AWS Certified Developer - Associate Questions and Answers
A financial services company builds a credit card transaction processing application that uses an Amazon API Gateway HTTP API and AWS Lambda functions. The application logs all requests and request parameters to Amazon CloudWatch. The application makes the logs accessible to developer AWS accounts and a separate fraud detection AWS account by using a cross-account IAM role .
The company requires that only the fraud detection account be able to view customer credit card numbers that are associated with the transactions. Developers at the company must not be able to use the credit card numbers for testing or debugging.
The developers create the following data protection policy document snippet:
{
" Name " : " data-protection-policy " ,
" Description " : " Credit card redaction " ,
" Version " : " 2021-06-01 " ,
" Statement " : [{
" Sid " : " redact-policy " ,
" DataIdentifier " : [
" arn:aws:dataprotection::aws:data-identifier/CreditCardNumber "
],
" Operation " : {
" Deidentify " : {
" MaskConfig " : {}
}
}
}]
}
Which combination of actions must the developers take to comply with the new policy? (Select TWO.)
A developer needs to give a new application the ability to retrieve configuration data.
The application must be able to retrieve new configuration data values without the need to redeploy the application code. If the application becomes unhealthy because of a bad configuration change, the developer must be able to automatically revert the configuration change to the previous value.
A developer manages a website that distributes its content by using Amazon CloudFront. The website ' s static artifacts are stored in an Amazon S3 bucket.
The developer deploys some changes and can see the new artifacts in the S3 bucket. However, the changes do not appear on the webpage that the CloudFront distribution delivers.
How should the developer resolve this issue?
A developer writes an AWS Lambda function that processes new object uploads to an Amazon S3 bucket. The Lambda function runs for approximately 30 seconds. The function runs as expected under normal load conditions. Other Lambda functions in the AWS account also run as expected. Occasionally, up to 500 new objects are written to the bucket every minute. Each new object write invokes the processing Lambda function during the high-volume periods through an event. The developer must ensure that the processing function will continue to run as expected during the high-volume periods. Which solution will meet this requirement?
A developer has created a data collection application that uses Amazon API Gateway, AWS Lambda, and Amazon S3. The application ' s users periodically upload data files and wait for the validation status to be reflected on a processing dashboard. The validation process is complex and time-consuming for large files.
Some users are uploading dozens of large files and have to wait and refresh the processing dashboard to see if the files have been validated. The developer must refactor the application to immediately update the validation result on the user’s dashboard without reloading the full dashboard.
What is the MOST operationally efficient solution that meets these requirements?
A developer is migrating an application to Amazon Elastic Kubernetes Service (Amazon EKS). The developer migrates the application to Amazon Elastic Container Registry (Amazon ECR) with an EKS cluster.
As part of the application migration to a new backend, the developer creates a new AWS account. The developer makes configuration changes to the application to point the application to the new AWS account and to use new backend resources. The developer successfully tests the changes within the application by deploying the pipeline.
The Docker image build and the pipeline deployment are successful, but the application is still connecting to the old backend. The developer finds that the application ' s configuration is still referencing the original EKS cluster and not referencing the new backend resources.
Which reason can explain why the application is not connecting to the new resources?
A developer creates a static website for their department The developer deploys the static assets for the website to an Amazon S3 bucket and serves the assets with Amazon CloudFront The developer uses origin access control (OAC) on the CloudFront distribution to access the S3 bucket
The developer notices users can access the root URL and specific pages but cannot access directories without specifying a file name. For example, /products/index.html works, but /products returns an error The developer needs to enable accessing directories without specifying a file name without exposing the S3 bucket publicly.
Which solution will meet these requirements ' ?
A developer is testing a Python application that is deployed on AWS Elastic Beanstalk. The application is using the Boto3 library to send events to an Amazon SQS queue. An external tool consumes the events.
During the tests, a ThrottlingException error occurs at irregular intervals.
What should the developer do to resolve this error?
A developer is trying to make API calls using the AWS SDK. The IAM user credentials used by the application require multi-factor authentication for all API calls.
Which method should the developer use to access the multi-factor authentication-protected API?
A company has an analytics application that uses an AWS Lambda function to process transaction data asynchronously A developer notices that asynchronous invocations of the Lambda function sometimes fail When failed Lambda function invocations occur, the developer wants to invoke a second Lambda function to handle errors and log details.
Which solution will meet these requirements?
A company is working on a new serverless application. A developer needs to find an automated way to deploy AWS Lambda functions and the dependent Infrastructure with minimum coding effort. The application also needs to be reliable.
Which method will meet these requirements with the LEAST operational overhead?
An application reads data from an Amazon Aurora global database with clusters in two AWS Regions. Database credentials are stored in AWS Secrets Manager in the primary Region and are rotated regularly.
The application must be able to run in both Regions and remain highly available .
Which combination of actions will meet these requirements? (Select TWO.)
A developer created an AWS Lambda function that accesses resources in a VPC. The Lambda function polls an Amazon Simple Queue Service (Amazon SOS) queue for new messages through a VPC endpoint. Then the function calculates a rolling average of the numeric values that are contained in the messages. After initial tests of the Lambda function, the developer found that the value of the rolling average that the function returned was not accurate.
How can the developer ensure that the function calculates an accurate rolling average?
A developer has an application that is composed of many different AWS Lambda functions. The Lambda functions all use some of the same dependencies. To avoid security issues the developer is constantly updating the dependencies of all of the Lambda functions. The result is duplicated effort to reach function.
How can the developer keep the dependencies of the Lambda functions up to date with the LEAST additional complexity?
A company runs a critical application on AWS. The application uses credentials to access an Amazon RDS database.
As part of a risk assessment to analyze security vulnerabilities, the company found that database credentials are not frequently rotated. A developer needs to implement a solution that securely stores and rotates the credentials. The solution must not expose the credentials to anyone who should not have access to the credentials.
Which solution will meet these requirements?
A company stores data in an Amazon S3 bucket. The data is updated multiple times every day from an application that runs on a server in the company’s on-premises data center. The company enables S3 Versioning on the S3 bucket. After some time, the company observes multiple versions of the same objects in the S3 bucket. The company needs the S3 bucket to keep the current version of each object and the version immediately previous to the current version. Which solution will meet these requirements?
A software company is launching a multimedia application. The application will allow guest users to access sample content before the users decide if they want to create an account to gain full access. The company wants to implement an authentication process that can identify users who have already created an account. The company also needs to keep track of the number of guest users who eventually create an account.
Which combination of steps will meet these requirements? {Select TWO.)
A developer has been asked to create an AWS Lambda function that is invoked any time updates are made to items in an Amazon DynamoDB table. The function has been created and appropriate permissions have been added to the Lambda execution role Amazon DynamoDB streams have been enabled for the table, but the function 15 still not being invoked.
Which option would enable DynamoDB table updates to invoke the Lambda function?
A developer must cache dependent artifacts from Maven Central, a public package repository, as part of an application ' s build pipeline. The build pipeline has an AWS CodeArtifact repository where artifacts of the build are published. The developer needs a solution that requires minimum changes to the build pipeline.
Which solution meets these requirements?
A company operates a media streaming platform that delivers on-demand video content to users from around the world. User requests flow through an Amazon CloudFront distribution, an Amazon API Gateway REST API, AWS Lambda functions, and Amazon DynamoDB tables.
Some users have reported intermittent buffering issues and delays when users try to start a video stream. The company needs to investigate the issues to discover the underlying cause.
Which solution will meet this requirement?
A company maintains an application responsible for processing several thousand external callbacks each day. The company’s system administrators want to know how many callbacks are being received on a rolling basis, and they want this data available for 10 days.
The company also wants the ability to issue automated alerts if the number of callbacks exceeds the defined thresholds.
What is the MOST cost-effective way to address the need to track and alert on these statistics?
A developer wants to store information about movies. Each movie has a title, release year, and genre. The movie information also can include additional properties about the cast and production crew. This additional information is inconsistent across movies. For example, one movie might have an assistant director, and another movie might have an animal trainer.
The developer needs to implement a solution to support the following use cases:
For a given title and release year, get all details about the movie that has that title and release year.
For a given title, get all details about all movies that have that title.
For a given genre, get all details about all movies in that genre.
Which data store configuration will meet these requirements?
A developer is using an AWS account to build an application that stores files in an Amazon S3 bucket. Files must be encrypted at rest by AWS KMS keys. A second AWS account must have access to read files from the bucket.
The developer wants to minimize operational overhead for the application.
Which combination of solutions will meet these requirements? (Select TWO.)
A company uses Amazon API Gateway to expose a set of APIs to customers. The APIs have caching enabled in API Gateway. Customers need a way to invalidate the cache for each API when they test the API.
What should a developer do to give customers the ability to invalidate the API cache?
A cloud-based video surveillance company is developing an application that analyzes video files. After the application analyzes the files, the company can discard the files.
The company stores the files in an Amazon S3 bucket. The files are 1 GB in size on average. No file is larger than 2 GB. An AWS Lambda function will run one time for each video file that is processed. The processing is very I/O intensive, and the application must read each file multiple times.
Which solution will meet these requirements in the MOST performance-optimized way?
A company is using AWS SAM to develop a social media application. A developer needs a quick way to test AWS Lambda functions locally by using test event payloads. The developer needs the structure of these test event payloads to match the actual events that AWS services create.
Which solution will meet these requirements with the LEAST development effort?
A company runs an analytics application that creates daily reports. The company stores the reports in an Amazon S3 bucket that has versioning enabled. The application stores several drafts of each report every day as S3 object versions before submitting a final report for the day.
The company needs a solution to delete draft reports that are older than 1 year. The company accesses draft reports frequently for the first month. After 1 month, the company accesses draft reports rarely during the next 11 months. Draft reports must be accessible within minutes.
Which solution will meet these requirements MOST cost-effectively?
A company runs a batch processing application by using AWS Lambda functions and Amazon API Gateway APIs with deployment stages for development, user acceptance testing and production A development team needs to configure the APIs in the deployment stages to connect to third-party service endpoints.
Which solution will meet this requirement?
An application runs on multiple EC2 instances behind an ELB.
Where is the session data best written so that it can be served reliably across multiple requests?
A developer maintains a legacy ecommerce application that sends logs to an Amazon CloudWatch Logs log group. During an audit, the developer discovers that the application sends credit card numbers and credit card verification codes to the log group.
The developer needs a solution to give support staff the ability to view the logs. However, the support staff must not be able to view the sensitive credit card information. Application administrators must be able to view the logs and must have access to the sensitive credit card data. The developer cannot modify the application code.
Which solution will meet these requirements?
A company runs an application that currently uploads content to an unencrypted Amazon S3 bucket. The S3 bucket contains millions of objects that total more than 2 TB in size. A new company policy requires all data to be encrypted. The company creates an AWS KMS key to use for encryption.
Which solution will meet this requirement MOST cost-effectively?
An application interacts with Amazon Aurora to store and track customer information. The primary database is set up with multiple read replicas for improving the performance of the read queries. However, one of the Aurora replicas is receiving most or all of the traffic, while the other Aurora replica remains idle.
How can this issue be resolved?
An ecommerce application is running behind an Application Load Balancer. A developer observes some unexpected load on the application during non-peak hours. The developer wants to analyze patterns for the client IP addresses that use the application. Which HTTP header should the developer use for this analysis?
A company is using Amazon OpenSearch Service to implement an audit monitoring system. A developer needs to create an AWS Cloudformation custom resource that is associated with an AWS Lambda function to configure the OpenSearch Service domain. The Lambda function must access the OpenSearch Service domain by using Open Search Service internal master user credentials.
What is the MOST secure way to pass these credentials to the Lambdas function?
A developer is building a process flow that invokes two AWS Lambda functions. The Lambda functions write logs to Amazon CloudWatch. Each run of the process has a unique request ID that flows to both Lambda functions.
The developer encounters a failure in the process flow. The developer wants to use the request IDs to analyze the flow logs.
Which solution will meet these requirements with the LEAST development effort?
A developer needs to perform geographic load testing of an API. The developer must deploy resources to multiple AWS Regions to support the load testing of the API.
How can the developer meet these requirements without additional application code?
A company uses AWS Secrets Manager to store API keys for external REST services. The company uses an AWS Lambda function to rotate the API keys on a regular schedule.
Due to an error in the Lambda function, the API keys are successfully updated in AWS Secrets Manager but are not updated in the external REST services. Before investigating the root cause of the issue, the company wants to resume requests to the external REST services as quickly as possible.
Which solution will meet this requirement with the LEAST operational overhead ?
A company has a serverless application that uses an Amazon API Gateway API to invoke an AWS Lambda function. A developer creates a fix for a defect in the Lambda function code. The developer wants to deploy this fix to the production environment. To test the changes, the developer needs to send 10% of the live production traffic to the updated Lambda function version.
Options:
A developer has code that is stored in an Amazon S3 bucket. The code must be deployed as an AWS Lambda function across multiple accounts in the same AWS Region as the S3 bucket an AWS CloudPormation template that runs for each account will deploy the Lambda function.
What is the MOST secure way to allow CloudFormaton to access the Lambda Code in the S3 bucket?
A developer has an application that asynchronously invokes an AWS Lambda function. The developer wants to store messages that resulted in failed invocations of the Lambda function so that the application can retry the call later.
What should the developer do to accomplish this goal with the LEAST operational overhead?
A development team uses AWS CodeBuild as part of a CI/CD pipeline. The project includes hundreds of unit and integration tests, and total build time continues to increase. The team wants faster feedback and lower overall testing duration without managing additional infrastructure.
Which solution will meet these requirements with the LEAST operational overhead ?
Users of a web-based music application are experiencing latency issues on one of the application ' s most popular pages. A developer identifies that the issue is caused by the slow load time of specific widgets that rank and sort various songs and albums.
The developer needs to ensure that the widgets load more quickly by using built-in, in-memory ranking and sorting techniques. The developer must ensure that the data remains up to date.
Which solution will meet these requirements with the LEAST latency ?
A company stores data in an Amazon S3 bucket that is updated multiple times each day. S3 Versioning is enabled, and multiple versions of objects accumulate.
The company needs the bucket to retain only the current version and the immediately previous version of each object.
Which solution will meet these requirements?
An application routinely processes a large number of Amazon S3 GET requests each second. A developer wants to increase the number of requests that the application can handle in parallel.
What should the developer do to achieve this goal?
A developer is creating an AWS Lambda function that will connect to an Amazon RDS for MySQL instance. The developer wants to store the database credentials. The database credentials need to be encrypted and the database password needs to be automatically rotated.
Which solution will meet these requirements?
A developer has an application that makes batch requests directly to Amazon DynamoDB by using the BatchGetItem low-level API operation. The responses frequently return values in the UnprocessedKeys element.
Which actions should the developer take to increase the resiliency of the application when the batch response includes values in UnprocessedKeys? (Choose two.)
A company has an existing application that has hardcoded database credentials A developer needs to modify the existing application The application is deployed in two AWS Regions with an active-passive failover configuration to meet company’s disaster recovery strategy
The developer needs a solution to store the credentials outside the code. The solution must comply With the company ' s disaster recovery strategy
Which solution Will meet these requirements in the MOST secure way?
A development team uses an Amazon DynamoDB table as a database for an application. The team notices errors and slowdowns in the application during peak usage hours. The slowdowns and errors occur during a surge of user logins. The application receives frequent write requests. Application logs indicate that write requests are being throttled.
The development team needs to reduce the application latency and resolve the throttling errors.
Which solutions will meet these requirements? (Select TWO.)
A company is developing a weather forecast application that displays forecasts for towns and cities in a single country for a specified date range. The application stores weather data in an Amazon DynamoDB table named Forecasts. The Forecasts table has attributes named CityId, Temperature, and ForecastDate. The company expects the application to be read-heavy and that the vast majority of reads will target the current day’s forecast for one of a small number of very large cities. The company needs to design a partition key configuration that will yield the most even distribution of read requests for the application ' s expected use case. Which solution will meet these requirements?
A developer is building a microservices-based application by using Python on AWS and several AWS services The developer must use AWS X-Ray The developer views the service map by using the console to view the service dependencies. During testing, the developer notices that some services are missing from the service map
What can the developer do to ensure that all services appear in the X-Ray service map?
A developer needs to store configuration variables for an application. The developer needs to set an expiration date and time for me configuration. The developer wants to receive notifications. Before the configuration expires. Which solution will meet these requirements with the LEAST operational overhead?
A company wants to make sure that only one user from its Admin group has the permanent right to delete an Amazon EC2 resource. There should be no changes in the existing policy under the Admin group. What should a developer use to meet these requirements?
A company uses more than 100 AWS Lambda functions to handle application services. One Lambda function is critical and must always run successfully. The company notices that occasionally, the critical Lambda function does not initiate. The company investigates the issue and discovers instances of the Lambda TooManyRequestsException: Rate Exceeded error in Amazon CloudWatch logs. Upon further review of the logs, the company notices that some of the non-critical functions run properly while the critical function fails. A developer must resolve the errors and ensure that the critical Lambda function runs successfully. Which solution will meet these requirements with the LEAST operational overhead?
A developer is building an application that processes a stream of user-supplied data. The data stream must be consumed by multiple Amazon EC2-based processing applications in parallel and in real time. Each processor must be able to resume without losing data if there is a service interruption. The application architect plans to add other processors in the near future and wants to minimize the amount of data duplication involved.
Which solution will satisfy these requirements?
A developer is creating a microservices application that runs across multiple compute environments. The application must securely access secrets that are stored in AWS Secrets Manager with minimal network latency. The developer wants a solution that reduces the number of direct calls to Secrets Manager and simplifies secrets management across environments. Which solution will meet these requirements with the LEAST operational overhead?
A company runs a serverless application on AWS. The application includes an AWS Lambda function. The Lambda function processes data and stores the data in an Amazon RDS for PostgreSQL database. A developer created user credentials in the database for the application.
The developer needs to use AWS Secrets Manager to manage the user credentials. The password must be rotated on a regular basis. The solution needs to ensure that there is high availability and no downtime for the application during secret rotation.
What should the developer do to meet these requirements?
A developer has a legacy application that is hosted on-premises. Other applications hosted on AWS depend on the on-premises application for proper functioning. In case of any application errors, the developer wants to be able to use Amazon CloudWatch to monitor and troubleshoot all applications from one place.
How can the developer accomplish this?
A developer must securely access a secret during a build process in an AWS CodeBuild project that has an IAM role. The secret must remain encrypted at rest and must be passed to the buildspec.yml file without appearing in the build logs. Which solution will meet these requirements with the LEAST operational overhead?
A company uses an AWS Lambda function to transfer files from an Amazon S3 bucket to the company ' s SFTP server. The Lambda function connects to the SFTP server by using credentials such as username and password. The company uses Lambda environment variables to store these credentials.
A developer needs to implement encrypted username and password credentials.
Which solution will meet these requirements?
In a move toward using microservices, a company’s management team has asked all development teams to build their services so that API requests depend only on that service’s data store. One team is building a Payments service which has its own database; the service needs data that originates in the Accounts database. Both are using Amazon DynamoDB.
What approach will result in the simplest, decoupled, and reliable method to get near-real time updates from the Accounts database?
A developer is using AWS Elastic Beanstalk to deploy an application. The application must be able to access API keys from a third-party service. Currently, the company stores the credentials to access the third-party service in the code bundle. The company must redeploy the code bundle when the credentials rotate. The developer wants to improve security and avoid redeployments. Which solution will meet these requirements with the LEAST operational overhead?
A company uses AWS CloudFormation to deploy an application that includes an Amazon API Gateway REST API integrated with AWS Lambda and Amazon DynamoDB. The application has three stages: development, testing, and production, each with its own DynamoDB table.
The company wants to deploy a new production release and route 20% of traffic to the new version while keeping 80% of traffic on the existing production version. The solution must minimize the number of errors that any single customer experiences.
Which approach should the developer take?
A developer is writing an application to analyze the traffic to a fleet of Amazon EC2 instances. The EC2 instances run behind a public Application Load Balancer (ALB). An HTTP server runs on each of the EC2 instances, logging all requests to a log file.
The developer wants to capture the client public IP addresses. The developer analyzes the log files and notices only the IP address of the ALB.
What must the developer do to capture the client public IP addresses in the log file?
An ecommerce company is using an AWS Lambda function behind Amazon API Gateway as its application tier. To process orders during checkout, the application calls a POST API from the frontend. The POST API invokes the Lambda function asynchronously. In rare situations, the application has not processed orders. The Lambda application logs show no errors or failures.
What should a developer do to solve this problem?
A company is creating an application that processes csv files from Amazon S3 A developer has created an S3 bucket The developer has also created an AWS Lambda function to process the csv files from the S3 bucket
Which combination of steps will invoke the Lambda function when a csv file is uploaded to Amazon S3? (Select TWO.)
A company has an Amazon API Gateway REST API that integrates with an AWS Lambda function. The API’s development stage references a Lambda development alias named dev.
A developer needs to make a production alias of the Lambda function named prod available through the API.
Which solution meets these requirements?
A developer needs to add additional monitoring to an application that runs in an Amazon ECS cluster. The solution must publish and store custom metrics for the application. The developer must be able to save metadata about the custom metrics and store data with a granularity of 1 second.
Which solution will meet these requirements?
A company has an application that runs on Amazon EC2 instances. The application needs to use dynamic feature flags that will be shared with other applications. The application must poll on an interval for new feature flag values. The values must be cached when they are retrieved.
Which solution will meet these requirements in the MOST operationally efficient way?
A developer is building an ecommerce application that uses AWS Lambda functions. Each Lambda function performs a specific step in a customer order workflow, such as order processing and inventory management. The developer must ensure that the Lambda functions run in a specific order.
Which solution will meet this requirement with the LEAST operational overhead?
A developer is troubleshooting an Amazon API Gateway API Clients are receiving HTTP 400 response errors when the clients try to access an endpoint of the API.
How can the developer determine the cause of these errors?
A developer is investigating recent performance bottlenecks within a company ' s distributed web application that runs on various AWS services, including Amazon EC2 and Amazon DynamoDB.
How can the developer determine the length of time of the application ' s calls to the various downstream AWS services?
A developer has a financial application. The application uses AWS Secrets Manager to manage an Amazon RDS for PostgreSQL database ' s username and password. The developer needs to rotate the password while maintaining the application ' s high availability. Which solution will meet these requirements with LEAST development effort?
A developer is troubleshooting an application mat uses Amazon DynamoDB in the uswest-2 Region. The application is deployed to an Amazon EC2 instance. The application requires read-only permissions to a table that is named Cars The EC2 instance has an attached IAM role that contains the following IAM policy.
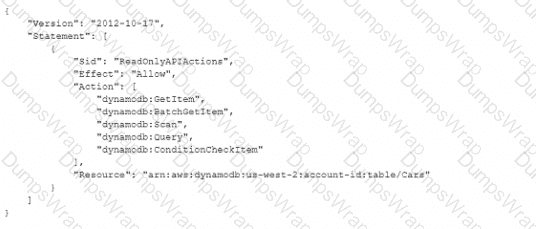
When the application tries to read from the Cars table, an Access Denied error occurs.
How can the developer resolve this error?
A company is planning to use AWS CodeDeploy to deploy an application to AWS Lambda. During the deployment of a new version of the application, the company initially must expose only 10% of live traffic to the new version of the deployed application. Then, every 10 minutes, the company must route another 10% of live traffic to the new version of the deployed application until all live traffic is routed to the new version.
Which CodeDeploy predefined configuration will meet these requirements?
A developer at a company recently created a serverless application to process and show data from business reports. The application ' s user interface (UI) allows users to select and start processing the files. The Ul displays a message when the result is available to view. The application uses AWS Step Functions with AWS Lambda functions to process the files. The developer used Amazon API Gateway and Lambda functions to create an API to support the UI.
The company ' s Ul team reports that the request to process a file is often returning timeout errors because of the see or complexity of the files. The Ul team wants the API to provide an immediate response so that the Ul can deploy a message while the files are being processed. The backend process that is invoked by the API needs to send an email message when the report processing is complete.
What should the developer do to configure the API to meet these requirements?
A developer is creating a simple proof-of-concept demo by using AWS CloudFormation and AWS Lambda functions The demo will use a CloudFormation template to deploy an existing Lambda function The Lambda function uses deployment packages and dependencies stored in Amazon S3 The developer defined anAWS Lambda Function resource in a CloudFormation template. The developer needs to add the S3 bucket to the CloudFormation template.
What should the developer do to meet these requirements with the LEAST development effort?
A company needs to distribute firmware updates to its customers around the world.
Which service will allow easy and secure control of the access to the downloads at the lowest cost?
A developer is building a new application on AWS. The application uses an AWS Lambda function that retrieves information from an Amazon DynamoDB table. The developer hardcoded the DynamoDB table name into the Lambda function code. The table name might change over time. The developer does not want to modify the Lambda code if the table name changes.
Which solution will meet these requirements MOST efficiently?
A developer is setting up infrastructure by using AWS Cloud Formation. If an error occurs when the resources described in the CloudFormation template are provisioned, successfully provisioned resources must be preserved. The developer must provision and update the CloudFormation stack by using the AWS CLI.
Which solution will meet these requirements?
A healthcare company discovers that one of the company ' s AWS Lambda functions is improperly sending customer personal health information (PHI) and personally identifiable information (PII) to an Amazon CloudWatch Logs log group.
The company needs a solution to automatically mask PHI and PII across all log events in the log group. The company must ensure that masked values cannot be accidentally revealed through CloudWatch Logs Insights queries or subscription filters. The solution must allow only specific security engineers to view the original unmasked values when required for investigations.
Which solution will meet these requirements?
A developer is creating an AWS Lambda function in VPC mode An Amazon S3 event will invoke the Lambda function when an object is uploaded into an S3 bucket The Lambda function will process the object and produce some analytic results that will be recorded into a file Each processed object will also generate a log entry that will be recorded into a file.
Other Lambda functions. AWS services, and on-premises resources must have access to the result files and log file. Each log entry must also be appended to the same shared log file. The developer needs a solution that can share files and append results into an existing file.
Which solution should the developer use to meet these requirements?
A developer is testing a RESTful application that is deployed by using Amazon API Gateway and AWS Lambda When the developer tests the user login by using credentials that are not valid, the developer receives an HTTP 405 METHOD_NOT_ALLOWED error The developer has verified that the test is sending the correct request for the resource
Which HTTP error should the application return in response to the request?
A company is developing a serverless application that requires storage of sensitive API keys as environment variables for various services. The application requires the automatic rotation of the encryption keys every year.
Which solution will meet these requirements with no development effort?
A developer is building an application that stores user activity data in an Amazon DynamoDB table. The developer is writing a new AWS Lambda function to process the activity data. The developer grants the IAM role that the function assumes permission to query the table. The developer must ensure that the function does not have access to personally identifiable information (PII) that is stored in some of the table item attributes.
Which solutions will meet these requirements? (Select TWO.)
A developer has created an AWS Lambda function to provide notification through Amazon Simple Notification Service (Amazon SNS) whenever a file is uploaded to Amazon S3 that is larger than 50 MB. The developer has deployed and tested the Lambda function by using the CLI. However, when the event notification is added to the S3 bucket and a 3.000 MB file is uploaded, the Lambda function does not launch.
Which of the following Is a possible reason for the Lambda function ' s inability to launch?
A developer is deploying an AWS Lambda function The developer wants the ability to return to older versions of the function quickly and seamlessly.
How can the developer achieve this goal with the LEAST operational overhead?
A developer maintains a serverless application that uses AWS Lambda to process financial transaction files uploaded to an Amazon S3 bucket. A Lambda function is scheduled to run once per hour to process the files.
As file uploads increase, the Lambda function occasionally exceeds the 15-minute execution limit . The developer must handle higher file volumes, reduce processing time, and prevent duplicate file processing .
Which solution will meet these requirements?
A company has a multi-node Windows legacy application that runs on premises. The application uses a network shared folder as a centralized configuration repository to store configuration files in .xml format. The company is migrating the application to Amazon EC2 instances. As part of the migration to AWS, a developer must identify a solution that provides high availability for the repository.
Which solution will meet this requirement MOST cost-effectively?
A developer is setting up a deployment pipeline. The pipeline includes an AWS CodeBuild build stage that requires access to a database to run integration tests. The developer is using a buildspec.yml file to configure the database connection. Company policy requires automatic rotation of all database credentials.
Which solution will handle the database credentials MOST securely?
A developer is working on an application that uses a microservices architecture. The developer needs to grant an AWS Lambda function access to make calls to an Amazon API Gateway HTTP API. The HTTP API requires authentication.
Which solution will meet these requirements?
A developer is creating an AWS Lambda function. The Lambda function needs an external library to connect to a third-party solution The external library is a collection of files with a total size of 100 MB The developer needs to make the external library available to the Lambda execution environment and reduce the Lambda package space
Which solution will meet these requirements with the LEAST operational overhead?
A company runs an ecommerce application on AWS. The application stores data in an Amazon Aurora database.
A developer is adding a caching layer to the application. The caching strategy must ensure that the application always uses the most recent value for each data item.
Which caching strategy will meet these requirements?
A developer wants to deploy a new version of an AWS Elastic Beanstalk application. During deployment, the application must maintain full capacity and avoid service interruption. Additionally, the developer must minimize the cost of additional resources that support the deployment.
Which deployment method should the developer use to meet these requirements?
A developer is designing a serverless application that customers use to select seats for a concert venue. Customers send the ticket requests to an Amazon API Gateway API with an AWS Lambda function that acknowledges the order and generates an order ID. The application includes two additional Lambda functions: one for inventory management and one for payment processing. These two Lambda functions run in parallel and write the order to an Amazon DynamoDB table.
The application must provide seats to customers according to the following requirements. If a seat is accidentally sold more than once, the first order that the application received must get the seat. In these cases, the application must process the payment for only the first order. However, if the first order is rejected during payment processing, the second order must get the seat. In these cases, the application must process the payment for the second order.
Which solution will meet these requirements?
A developer is integrating Amazon ElastiCache in an application. The cache will store data from a database. The cached data must populate real-time dashboards. Which caching strategy will meet these requirements?
A company wants to ensure that only one user from its Admin group has the permanent right to delete an Amazon EC2 resource. The company must not modify the existing Admin group policy .
What should a developer use to meet these requirements?
A developer is working on an AWS Lambda function that accesses Amazon DynamoDB. The Lambda function must retrieve an item and update some of its attributes, or create the item if it does not exist. The Lambda function has access to the primary key.
Which IAM permissions should the developer request for the Lambda function to achieve this functionality?
A)
B)
C)
D)
A company ' s development team uses an SSH key pair to copy files among a large fleet of development servers. The SSH key pair has been compromised. A developer has generated a replacement key pair. The company has deployed the AWS Systems Manager Agent (SSM Agent) and the Amazon CloudWatch agent on all of the development servers.
The developer needs a solution to distribute the new key to all the Linux servers.
Which solution will meet these requirements in the MOST operationally efficient way?
A developer is writing a web application that will run on AWS Lambda. The application will give users the ability to log in to view private documents. All pages in the application must be designed to match the company ' s branding.
How can the developer host the sign-in pages with the LEAST amount of custom code?
A developer is building an application that needs to store an API key. An AWS Lambda function needs to use the API key. The developer ' s company requires secrets to be encrypted at rest by an AWS KMS key. The company must control key rotation.
Which solutions will meet these requirements? (Select TWO.)
A company is building a content authoring application. The application has multiple user groups, such as content creator, reviewer, approver, and administrator. The company needs to assign users fine-grained permissions for specific parts of the application.
The company needs a solution to configure, maintain, and analyze user permissions. The company wants a solution that can be easily adapted to work with newer applications in the future. The company must use a third-party OpenID Connect (OIDC) identity provider (IdP) to authenticate users.
An ecommerce company is developing a serverless application to track user activities. The company needs to track each type of activity with a timestamp and a unique product ID. The company also must track actions that are associated with each activity, such as product views, shopping cart actions, purchases, and checkout processes.
The company is planning a marketing campaign based on each user ' s activity. A developer needs to implement a partitioning strategy for an Amazon DynamoDB table to meet the data storage and access requirements for the application. The strategy must maximize provisioned throughput efficiency while minimizing the risk of throttling.
Which solution will meet these requirements?
A developer is building an application that processes a stream of user-supplied data. The data stream must be consumed by multiple Amazon EC2 based processing applications in parallel and in real time. Each processor must be able to resume without losing data if there is a service interruption. The application architect plans to add other processors in the near future, and wants to minimize the amount of data duplication involved.
Which solution will satisfy these requirements?
A company has a web application that contains an Amazon API Gateway REST API. A developer has created an AWS CloudFormation template for the initial deployment of the application. The developer has deployed the application successfully as part of an AWS CodePipeline continuous integration and continuous delivery (CI/CD) process. All resources and methods are available through the deployed stage endpoint.
The CloudFormation template contains the following resource types:
• AWS::ApiGateway::RestApi
• AWS::ApiGateway::Resource
• AWS::ApiGateway::Method
• AWS:ApiGateway::Stage
• AWS::ApiGateway:;Deployment
The developer adds a new resource to the REST API with additional methods and redeploys the template. CloudFormation reports that the deployment is successful and that the stack is in the UPDATE_COMPLETE state. However, calls to all new methods are returning 404 (Not Found) errors.
What should the developer do to make the new methods available?
A company is building a micro services app1 cation that consists of many AWS Lambda functions. The development team wants to use AWS Serverless Application Model (AWS SAM) templates to automatically test the Lambda functions. The development team plans to test a small percentage of traffic that is directed to new updates before the team commits to a full deployment of the application.
Which combination of steps will meet these requirements in the MOST operationally efficient way? (Select TWO.)
An application uses an Amazon API Gateway API that is integrated with an AWS Lambda function. Specific API requests are returning the HTTP 504 (Gateway Timeout) error message. The Lambda function is configured with a 20-second timeout. The API Gateway integration is configured with a 15-second timeout and a rate of 10 requests every second. There are no errors in the logs for the Lambda function. Which solution will prevent the HTTP 504 error responses?
A company is building a serverless application that uses AWS Lambda functions. The company needs to create a set of test events to test Lambda functions in a development environment. The test events will be created once and then will be used by all the developers in an 1AM developer group. The test events must be editable by any of the 1AM users in the 1AM developer group.
Which solution will meet these requirements?
A development team is using an Amazon SNS topic as part of an application. The development team is using an AWS SDK to send messages to the SNS topic. The SNS topic sends an email message to a specific person when each message arrives in the topic.
The development team wants a solution to invoke a specific AWS Lambda function if a message that arrives in the topic contains the word “Important” in the title attribute of the JSON message. The solution must not require any changes to the application code.
Which solution will meet these requirements?
A developer has built an application that inserts data into an Amazon DynamoDB table. The table is configured to use provisioned capacity. The application is deployed on a burstable nano Amazon EC2 instance. The application logs show that the application has been failing because of a ProvisionedThroughputExceededException error.
Which actions should the developer take to resolve this issue? (Select TWO.)
A company wants to automate part of its deployment process. A developer needs to automate the process of checking for and deleting unused resources that supported previously deployed stacks but that are no longer used.
The company has a central application that uses the AWS Cloud Development Kit (AWS CDK) to manage all deployment stacks. The stacks are spread out across multiple accounts. The developer’s solution must integrate as seamlessly as possible within the current deployment process.
Which solution will meet these requirements with the LEAST amount of configuration?
A company built an online event platform For each event the company organizes quizzes and generates leaderboards that are based on the quiz scores. The company stores the leaderboard data in Amazon DynamoDB and retains the data for 30 days after an event is complete The company then uses a scheduled job to delete the old leaderboard data
The DynamoDB table is configured with a fixed write capacity. During the months when many events occur, the DynamoDB write API requests are throttled when the scheduled delete job runs.
A developer must create a long-term solution that deletes the old leaderboard data and optimizes write throughput
Which solution meets these requirements?
A developer is storing sensitive data generated by an application in Amazon S3. The developer wants to encrypt the data at rest. A company policy requires an audit trail of when the AWS Key Management Service (AWS KMS) key was used and by whom.
Which encryption option will meet these requirements?
A company is using AWS CloudFormation to deploy a two-tier application. The application will use Amazon RDS as its backend database. The company wants a solution that will randomly generate the database password during deployment. The solution also must automatically rotate the database password without requiring changes to the application.
What is the MOST operationally efficient solution that meets these requirements ' ?
A developer has created a large AWS Lambda function. Deployment of the function Is failing because of an InvalidParameterValueException error. The error message indicates that the unzipped size of the function exceeds the maximum supported value.
Which actions can the developer take to resolve this error? (Select TWO.)
A developer is building an application to process a stream of customer orders. The application sends processed orders to an Amazon Aurora MySQL database. The application needs to process the orders in batches.
The developer needs to configure a workflow that ensures each record is processed before the application sends each order to the database.
Options:
A developer is updating several AWS Lambda functions and notices that all the Lambda functions share the same custom libraries. The developer wants to centralize all the libraries, update the libraries in a convenient way, and keep the libraries versioned.
Which solution will meet these requirements with the LEAST development effort?
A developer is migrating some features from a legacy monolithic application to use AWS Lambda functions instead. The application currently stores data in an Amazon Aurora DB cluster that runs in private subnets in a VPC. The AWS account has one VPC deployed. The Lambda functions and the DB cluster are deployed in the same AWS Region in the same AWS account.
The developer needs to ensure that the Lambda functions can securely access the DB cluster without crossing the public internet.
Which solution will meet these requirements?
A company receives food orders from multiple partners. The company has a microservices application that uses Amazon API Gateway APIs with AWS Lambda integration. Each partner sends orders by calling a customized API that is exposed through API Gateway. The API call invokes a shared Lambda function to process the orders.
Partners need to be notified after the Lambda function processes the orders. Each partner must receive updates for only the partner ' s own orders. The company wants to add new partners in the future with the fewest code changes possible.
Which solution will meet these requirements in the MOST scalable way?
A company has a web application that runs on Amazon EC2 instances with a custom Amazon Machine Image (AMI) The company uses AWS CloudFormation to provision the application The application runs in the us-east-1 Region, and the company needs to deploy the application to the us-west-1 Region
An attempt to create the AWS CloudFormation stack in us-west-1 fails. An error message states that the AMI ID does not exist. A developer must resolve this error with a solution that uses the least amount of operational overhead
Which solution meets these requirements?
A developer supports an application that accesses data in an Amazon DynamoDB table. One of the item attributes is expirationDate in the timestamp format. The application uses this attribute to find items, archive them, and remove them from the table based on the timestamp value
The application will be decommissioned soon, and the developer must find another way to implement this functionality. The developer needs a solution that will require the least amount of code to write.
Which solution will meet these requirements?
A developer is migrating a containerized application from an on-premises environment to an Amazon ECS cluster.
In the on-premises environment, the container uses a Docker file to store the application. Service dependency configurations such as databases, caches, and storage volumes are stored in a docker-compose.yml file.
Both files are located at the top level of the code base that the developer needs to containerize. When the developer deploys the code to Amazon ECS, the instructions from the Docker file are carried out. However, none of the configurations from docker-compose.yml are applied.
The developer needs to resolve the error and ensure the configurations are applied.
A developer is deploying an AWS Lambda function that writes to Amazon DynamoDB. Amazon CloudWatch metrics for the Lambda function show that errors have occurred during some invocations of the function. However, there are no entries available in the CloudWatch Logs for the function. The source code for the function shows that the function writes log data before saving data. What should the developer do to address the missing CloudWatch log entries for the Lambda function?
An application uses an Amazon EC2 Auto Scaling group. A developer notices that EC2 instances are taking a long time to become available during scale-out events. The UserData script is taking a long time to run.
The developer must implement a solution to decrease the time that elapses before an EC2 instance becomes available. The solution must make the most recent version of the application available at all times and must apply all available security updates. The solution also must minimize the number of images that are created. The images must be validated.
Which combination of steps should the developer take to meet these requirements? (Choose two.)
A company runs an application on AWS. The application stores data in an Amazon DynamoDB table. Some queries are taking a long time to run. These slow queries involve an attribute that is not the table ' s partition key or sort key. The amount of data that the application stores in the DynamoDB table is expected to increase significantly. A developer must increase the performance of the queries. Which solution will meet these requirements?
An ecommerce company has an integration with a payment processing service that publishes messages about payment activities to an Amazon SNS topic. A developer is building an AWS Lambda function to process payment refunds from the SNS topic. The Lambda function must process only messages related to refunds. Which solution will meet this requirement in the MOST operationally efficient way?
A developer is testing an AWS Lambda function by using the AWS SAM local CLI. The application that is implemented by the Lambda function makes several AWS API calls by using the AWS SDK. The developer wants to allow the function to make AWS API calls in a test AWS account from the developer’s laptop.
What should the developer do to meet these requirements?
A company operates on-premises data centers that run an image processing service composed of containerized applications on Kubernetes clusters . All applications share access to a common NFS file system for data storage.
The company is running out of NFS capacity and must migrate to AWS quickly. The Kubernetes clusters must be highly available on AWS.
Which combination of actions will meet these requirements? (Select TWO.)
Users are reporting errors in an application. The application consists of several micro services that are deployed on Amazon Elastic Container Serves (Amazon ECS) with AWS Fargate.
When combination of steps should a developer take to fix the errors? (Select TWO)
A company is creating a new application that gives users the ability to upload and share short video files. The average size of the video files is 10 MB. After a user uploads a file, a message needs to be placed into an Amazon Simple Queue Service (Amazon SQS) queue so the file can be processed. The files need to be accessible for processing within 5 minutes.
Which solution will meet these requirements MOST cost-effectively?
A developer is building two microservices that use an Amazon SQS queue to communicate. The messages that the microservices send to one another contain sensitive information. The developer must ensure the messages are stored and are encrypted at rest.
Which solution will meet these requirements?
A company notices that credentials that the company uses to connect to an external software as a service (SaaS) vendor are stored in a configuration file as plaintext.
The developer needs to secure the API credentials and enforce automatic credentials rotation on a quarterly basis.
Which solution will meet these requirements MOST securely?
A company runs applications on Amazon EKS containers. The company sends application logs from the containers to an Amazon CloudWatch Logs log group. The company needs to process log data in real time based on a specific error in the application logs. Which combination of steps will meet these requirements? (Select TWO.)
A company uses AWS CloudFormation to deploy an application that uses an Amazon API Gateway REST API with AWS Lambda function integration. The application uses Amazon DynamoDB for data persistence. The application has three stages: development, testing, and production. Each stage uses its own DynamoDB table. The company has encountered unexpected issues when promoting changes to the production stage. A developer needs to route 20% of the traffic to the new production stage API with the next production release. The developer needs to route the remaining 80% of the traffic to the existing production stage. The solution must minimize the number of errors that any single customer experiences. Which approach should the developer take to meet these requirements?
A developer maintains an Amazon API Gateway REST API. Customers use the API through a frontend UI and Amazon Cognito authentication.
The developer has a new version of the API that contains new endpoints and backward-incompatible interface changes. The developer needs to provide beta access to other developers on the team without affecting customers.
Which solution will meet these requirements with the LEAST operational overhead?
A developer is implementing a serverless application by using AWS CloudFormation to provision Amazon S3 web hosting. Amazon API Gateway, and AWS Lambda functions. The Lambda function source code is zipped and uploaded to an S3 bucket. The S3 object key of the zipped source code is specified in the Lambda resource in the CloudFormation template.
The developer notices that there are no changes in the Lambda function every time the CloudFormation stack is updated.
How can the developer resolve this issue?
A company has developed a new serverless application using AWS Lambda functions that will be deployed using the AWS Serverless Application Model (AWS SAM) CLI.
Which step should the developer complete prior to deploying the application?
A developer owns and supports an application that has database credentials stored in environment variables for AWS Lambda functions. The developer needs an alternate storage method for the credentials instead of using plaintext environment variables. Which solution will handle the credentials MOST securely?
A company created an application to consume and process data. The application uses Amazon SQS and AWS Lambda functions. The application is currently working as expected, but it occasionally receives several messages that it cannot process properly. The company needs to clear these messages to prevent the queue from becoming blocked. A developer must implement a solution that makes queue processing always operational. The solution must give the company the ability to defer the messages with errors and save these messages for further analysis. What is the MOST operationally efficient solution that meets these requirements?
A developer is building two microservices that communicate by using an Amazon SQS queue. The messages exchanged between the microservices contain sensitive information . The developer must ensure that the messages are encrypted at rest .
Which solution will meet these requirements?
A developer is building an image-processing application that includes an AWS Lambda function. The Lambda function moves images from one AWS service to another AWS service for image processing. For images that are larger than 2 MB, the Lambda function returns the following error: " Task timed out after 3.01 seconds. "
The developer needs to resolve the error without modifying the Lambda function code.
Which solution will meet these requirements?
A developer is designing a new feature for an existing application. The new feature uses an AWS Lambda function. The developer wants to test the Lambda function safely in a development AWS account and a testing AWS account before deploying the function into a production AWS account. The developer must roll back the function if issues are found. Which solution will meet these requirements with the LEAST operational overhead?
An online food company provides an Amazon API Gateway HTTP API 1o receive orders for partners. The API is integrated with an AWS Lambda function. The Lambda function stores the orders in an Amazon DynamoDB table.
The company expects to onboard additional partners Some to me panthers require additional Lambda function to receive orders. The company has created an Amazon S3 bucket. The company needs 10 store all orders and updates m the S3 bucket for future analysis
How can the developer ensure that an orders and updates are stored to Amazon S3 with the LEAST development effort?
An application stores user data in Amazon S3 buckets in multiple AWS Regions. A developer needs to implement a solution that analyzes the user data in the S3 buckets to find sensitive information. The analysis findings from all the S3 buckets must be available in the eu-west-2 Region.
Which solution will meet these requirements with the LEAST development effort?
A developer needs to set up an API to provide access to an application and its resources. The developer has a TLS certificate. The developer must have the ability to change the default base URL of the API to a custom domain name. The API users are distributed globally. The solution must minimize API latency.
A company is developing a set of AWS Lambda functions to process data. The Lambda functions need to use a common third-party library as a dependency. The library is frequently updated with new features and bug fixes. The company wants to ensure that the Lambda functions always use the latest version of the library.
Which solution will meet these requirements in the MOST operationally efficient way?
A developer is creating an application that will give users the ability to store photos from their cellphones in the cloud. The application needs to support tens of thousands of users. The application uses an Amazon API Gateway REST API that is integrated with AWS Lambda functions to process the photos. The application stores details about the photos in Amazon DynamoDB.
Users need to create an account to access the application. In the application, users must be able to upload photos and retrieve previously uploaded photos. The photos will range in size from 300 KB to 5 MB.
Which solution will meet these requirements with the LEAST operational overhead?
A developer is creating an AWS Lambda function that needs credentials to connect to an Amazon RDS for MySQL database. An Amazon S3 bucket currently stores the credentials. The developer needs to improve the existing solution by implementing credential rotation and secure storage. The developer also needs to provide integration with the Lambda function.
Which solution should the developer use to store and retrieve the credentials with the LEAST management overhead?
A developer is storing JSON files in an Amazon S3 bucket. The developer wants to securely share an object with a specific group of people.
How can the developer securely provide temporary access to the objects that are stored in the S3 bucket?
An application development team decides to use AWS X-Ray to monitor application code to analyze performance and perform root cause analysis.
What does the team need to do to begin using X-Ray? (Select TWO.)
A developer is modifying a large-scale IoT application that stores device telemetry data in an Amazon DynamoDB table. The telemetry data is valuable only for a limited time, but the application stores the data indefinitely. Data storage is slowing the application down. The developer needs a solution to improve the performance of the application.
Which solution will meet this requirement in the MOST operationally efficient way?
A company has an application that consists of different microservices that run inside an AWS account. The microservices are running in containers inside a single VPC. The number of microservices is constantly increasing. A developer must create a central logging solution for application logs.
Which solution will meet these requirements?
A developer must analyze performance issues with production-distributed applications written as AWS Lambda functions. These distributed Lambda applications invoke other components that make up me applications. How should the developer identify and troubleshoot the root cause of the performance issues in production?
A company is building an ecommerce application. The company stores the application ' s static content in an Amazon S3 bucket. The application stores data that includes personally identifiable information (PII). The application makes dynamic requests in JSON format through an Amazon CloudFront distribution to an Amazon API Gateway REST API. The REST API invokes an AWS Lambda function that stores and queries data in Amazon DynamoDB.
The company must ensure that all PII data is encrypted at rest in DynamoDB. The company must also protect specific data fields more granularly. The company must ensure that the specified fields are encrypted at the edge. The specified fields must remain encrypted throughout the full stack of the application.
Which solution will meet these requirements?
A company runs a web application on Amazon EC2 instances behind an Application Load Balancer. The application uses Amazon DynamoDB as its database. The company wants to ensure high performance for reads and writes.
Which solution will meet these requirements MOST cost-effectively?
A data visualization company wants to strengthen the security of its core applications The applications are deployed on AWS across its development staging, pre-production, and production environments. The company needs to encrypt all of its stored sensitive credentials The sensitive credentials need to be automatically rotated Aversion of the sensitive credentials need to be stored for each environment
Which solution will meet these requirements in the MOST operationally efficient way?
A developer updates an AWS Lambda function that an Amazon API Gateway API uses. The API is the backend for a web application.
The developer needs to test the updated Lambda function before deploying the Lambda function to production. The testing must not affect any production users of the web application.
Which solution will meet these requirements in the MOST operationally efficient way?
A company needs to deploy all its cloud resources by using AWS CloudFormation templates A developer must create an Amazon Simple Notification Service (Amazon SNS) automatic notification to help enforce this rule. The developer creates an SNS topic and subscribes the email address of the company ' s security team to the SNS topic.
The security team must receive a notification immediately if an 1AM role is created without the use of CloudFormation.
Which solution will meet this requirement?
A company is planning to securely manage one-time fixed license keys in AWS. The company ' s development team needs to access the license keys in automaton scripts that run in Amazon EC2 instances and in AWS CloudFormation stacks.
Which solution will meet these requirements MOST cost-effectively?
A company has an application that is based on Amazon EC2. The company provides API access to the application through Amazon API Gateway and uses Amazon DynamoDB to store the application ' s data. A developer is investigating performance issues that are affecting the application. During peak usage, the application is overwhelmed by a large number of identical data read requests that come through APIs. What is the MOST operationally efficient way for the developer to improve the application ' s performance?
A company is concerned that a malicious user could deploy unauthorized changes to the code for an AWS Lambda function. What can a developer do to ensure that only trusted code is deployed to Lambda?
A retail company runs a sales analytics application that uses an AWS Lambda function to process transaction data that is stored in Amazon DocumentDB. The application aggregates daily sales data across 500 stores and uses the data to generate reports for senior managers.
Application users report that the application is taking longer to generate reports and that their requests sometimes time out. A developer investigates and notices that the application ' s average response time for report generation has increased from 3 seconds to over 25 seconds.
The developer needs to identify the application ' s performance bottlenecks.
Which solution will meet this requirement with the LEAST operational overhead?
A company runs an application as an Amazon ECS service on an AWS Fargate cluster. The company has configured the service to use the rolling update deployment type. The company set the minimum healthy percentage to 100% and set the maximum healthy percentage to 200%.
A developer observes that a new deployment of the ECS service is failing continuously. The developer must ensure that Amazon ECS restores the most recently completed service deployment when a new service deployment fails.
Which solution will meet this requirement?
A company is migrating legacy internal applications to AWS. Leadership wants to rewrite the internal employee directory to use native AWS services. A developer needs to create a solution for storing employee contact details and high-resolution photos for use with the new application.
Which solution will enable the search and retrieval of each employee ' s individual details and high-resolution photos using AWS APIs?
An AWS Lambda function requires read access to an Amazon S3 bucket and requires read/write access to an Amazon DynamoDB table. The correct IAM policy already exists.
What is the MOST secure way to grant the Lambda function access to the S3 bucket and the DynamoDB table?
A developer needs to deploy an application running on AWS Fargate using Amazon ECS The application has environment variables that must be passed to a container for the application to initialize.
How should the environment variables be passed to the container?
A developer is building an API to support a shopping cart application. The application ' s backend is an AWS Lambda function that integrates with Amazon API Gateway. The developer wants to have the ability to test new versions of the application in a development environment before pushing changes to production. The developer needs to test the application by using mock endpoints for external payment processor APIs. The tests must allow quality assurance (QA) testers to make calls against a separate development stage without impacting the production environment. When the tests are finished, the developer needs to publish new Lambda code safely and must have the option to perform rollbacks if issues occur. Which solution will meet these requirements in the MOST secure way?
A developer creates an AWS Lambda function to publish messages to an Amazon SNS topic. All message content must be encrypted in transit and at rest between AWS Lambda and Amazon SNS.
A portion of the Lambda execution role policy is shown:
" Effect " : " Allow " ,
" Action " : " sns:Publish " ,
" Resource " : " arn:aws:sns:us-east-1:1234567890:secure-topic "
Which combination of steps should the developer take to meet these requirements? (Select TWO.)
A developer is troubleshooting a three-tier application, which is deployed on Amazon EC2 instances. There is a connectivity problem between the application servers and the database servers.
Which AWS services or tools should be used to identify the faulty component? (Select TWO.)
A developer needs to use a code template to create an automated deployment of an application onto Amazon EC2 instances. The template must be configured to repeat deployment, installation, and updates of resources for the application. The template must be able to create identical environments and roll back to previous versions.
Which solution will meet these requirements?
A developer has written the following IAM policy to provide access to an Amazon S3 bucket:
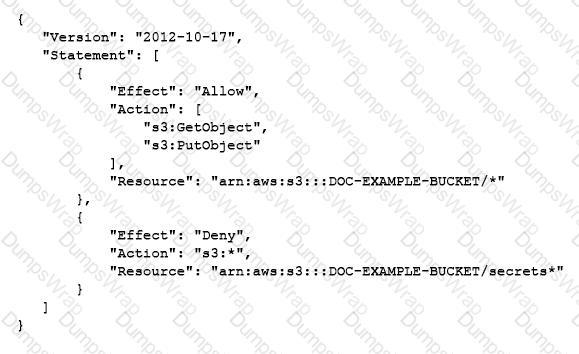
Which access does the policy allow regarding the s3:GetObject and s3:PutObject actions?
A developer is creating an Amazon DynamoDB table by using the AWS CLI The DynamoDB table must use server-side encryption with an AWS owned encryption key
How should the developer create the DynamoDB table to meet these requirements?
A developer needs to migrate an online retail application to AWS to handle an anticipated increase in traffic. The application currently runs on two servers: one server for the web application and another server for the database. The web server renders webpages and manages session state in memory. The database server hosts a MySQL database that contains order details. When traffic to the application is heavy, the memory usage for the web server approaches 100% and the application slows down considerably.
The developer has found that most of the memory increase and performance decrease is related to the load of managing additional user sessions. For the web server migration, the developer will use Amazon EC2 instances with an Auto Scaling group behind an Application Load Balancer.
Which additional set of changes should the developer make to the application to improve the application ' s performance?
A developer is testing an AWS Lambda function that has an event source of an Amazon SQS queue. The developer notices that some of the messages the Lambda function processes reappear in the queue while the messages are being processed. The developer must correct this behavior. Which solution will meet this requirement?
A developer is building an event-driven application that uses AWS Lambda functions and an Amazon SQS queue to handle Amazon S3 events and to perform additional processing. A parsing Lambda function implements business logic to parse each S3 event. The parsing function sends events on to an SQS queue. A processing Lambda function retrieves messages from the SQS queue and processes them.
During an isolated test, the developer observes that both Lambda functions work as expected for mock test events. However, when the test presents production S3 events to the functions, the developer observes that the number of messages in the SQS queue increases. The developer does not find any Amazon CloudWatch logs for the processing Lambda function when the processing function is presented with production S3 events. The developer does find logs for test events.
The developer must resolve these issues and ensure that the Lambda functions process production S3 events correctly.
Which solution will meet these requirements?
A developer creates an Amazon API Gateway REST API that has a usage plan. The REST API sits in front of an AWS Lambda function. The Lambda function calls a third-party fulfillment service that returns standard HTTP status codes. The developer enables API Gateway and Lambda logging in Amazon CloudWatch. CloudWatch metrics for API Gateway show the occurrence of 5XX errors but do not show the occurrence of 4XX errors. The Lambda execution log also states: “ERROR: Rate limit exceeded from fulfillment service.” The developer needs to resolve the errors. Which solution will meet these requirements?
A developer is creating an application that will store personal health information (PHI). The PHI needs to be encrypted at all times. An encrypted Amazon RDS for MySQL DB instance is storing the data. The developer wants to increase the performance of the application by caching frequently accessed data while adding the ability to sort or rank the cached datasets.
Which solution will meet these requirements?
A developer works in an environment with multiple AWS accounts that have AWS Lambda functions processing the same 100 KB payloads. The developer wants to centralize the point of origin of the payloads to one account and have all the Lambda functions be invoked whenever the initiating event occurs in the parent account.
How can the developer design the workflow in the MOST efficient way, so all the multi-account Lambda functions get invoked when the event occurs?
A healthcare company uses AWS Amplify to host a patient management system. The system uses Amazon API Gateway to expose RESTful APIs. The backend logic of the system is handled by AWS Lambda functions.
One of the Lambda functions receives patient data that includes personally identifiable information (PII). The Lambda function sends the patient data to an Amazon DynamoDB table. The company must encrypt all patient data at rest and in transit before the data is stored in DynamoDB.
A developer has created an AWS Lambda function that is written in Python. The Lambda function reads data from objects in Amazon S3 and writes data to an Amazon DynamoDB table. The function is successfully invoked from an S3 event notification when an object is created. However, the function fails when it attempts to write to the DynamoDB table.
What is the MOST likely cause of this issue?
An developer is building a serverless application by using the AWS Serverless Application Model (AWS SAM). The developer is currently testing the application in a development environment. When the application is nearly finsihed, the developer will need to set up additional testing and staging environments for a quality assurance team.
The developer wants to use a feature of the AWS SAM to set up deployments to multiple environments.
Which solution will meet these requirements with the LEAST development effort?

