Designing Cisco Security Infrastructure (300-745 SDSI) v1.0 Questions and Answers
A technology company has many remote workers who access corporate resources from various locations. The company must ensure that security policies are managed and enforced directly on endpoints, and endpoints are protected from threats regardless of location. Which firewall architecture meets the requirements?
A developer company recently implemented a testing environment based on Linux operating system. The company needs a technology solution that produces tracing and filtering capabilities in the Linux kernel. Which technology meets these requirements without modifying the kernel source code?
An agricultural company wants to enhance the cybersecurity posture by implementing a defense-in-depth strategy to protect against polymorphic malware threats. Currently, the company’s security infrastructure relies solely on a stateful traditional edge firewall that does not provide adequate protection against malware variants. Which technology must be added to the company’s security architecture to achieve the goal?
Which tool is used by a SOC analyst to quarantine an endpoint?
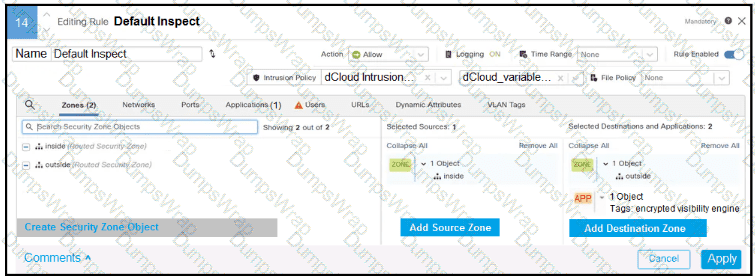
Refer to the exhibit.
In addition to SSL decryption, which firewall feature allows malware to be blocked?
An employee of a pharmaceutical company accidentally checked in code that contains AWS secret keys to a public GitHub repository, which exposes production resources to attackers. Which mitigation strategy must a security engineer recommend to prevent future reoccurrence?
A software development company relies on GitHub for managing the source code and is committed to maintaining application security. The company must ensure that known software vulnerabilities are not introduced to the application. The company needs a capability within GitHub that can analyze semantic versioning and flag any software components that pose security risks. Which GitHub feature must be used?
A security engineer on an application design team must choose a framework of attack patterns to evaluate during threat modeling. Which framework provides the common set of attacks?
A telecommunications company recently introduced a hybrid working model. Based on the new policy, employees can work remotely for 2 days per week if corporate equipment is used. The IT department is preparing corporate laptops to support users during the remote working days. Which solution must the IT department implement that provides secure connectivity to corporate resources and protects sensitive corporate data even if a laptop is stolen?
A product manager is focused on maintaining the security integrity of a microservice-based application as new features are developed and integrated. To ensure that known software vulnerabilities are not introduced into the product, it is crucial to implement a robust application security technique. The technique must be applied during the build phase of the software development lifecycle, which allows the team to proactively identify and address vulnerability risks before deployment. Which application security technique must be applied to accomplish the goal?
The network security team of a private university is conducting a comprehensive audit to evaluate the security posture across the network infrastructure. During the review, the security team found that a trusted vendor disclosed serious vulnerabilities identified in a product that plays a crucial role in the university’s CI/CD pipeline. The security team must act promptly to mitigate the potential risks posed by these vulnerabilities. Which action must the security team take first in response to the disclosure?
A company recently discovered that a former employee, who left to join a competitor, continued to access and exfiltrate sensitive data over several weeks after leaving. The breach highlighted vulnerabilities in the organization’s data security and access management practices. To prevent such incidents in the future, the organization must adopt measures that detect and restrict unauthorized data access and transfer. Which mitigation strategy must be implemented to address the issue?
What is a use for AI in securing network infrastructure?
A retail company is facing a series of cyberattacks targeting web servers, which results in disruptions to online services. Upon investigation, the security team identified that these attacks involved invalid HTTP request headers, which were used to exploit vulnerabilities in the web application. To safeguard the company websites against similar threats in the future, the security team must deploy a security solution specifically designed to detect and block such malicious web traffic. Which security product must be used to protect the websites from similar attacks?
A manufacturing company implemented IoT devices throughout their smart factory and needs a security solution that meets these requirements:
Protect IoT devices from network-based attacks.
Visibility into communication patterns.
Anomaly detection for IoT traffic.
Which firewall technology or feature should be recommended?
A manufacturing company experienced a security breach that resulted in sales data being compromised. An engineer participating in the investigation must identify who logged into the sales system during the affected period. Which approach must be used to gather the information?
An IT company experienced the spread of malicious content between user endpoints, which impacted business critical resources. The company wants to implement a solution to control communication between individual endpoints on the network. Which approach achieves the goal?

