CompTIA A+ Core 2 (2026 Exam Update) Questions and Answers
A technician is unable to join a computer to the Windows domain. However, the computer can ping the domain controller by IP address. Which of the following is the most likely reason?
A senior administrator asks a help desk technician to run a set of commands on a remote network switch. After running the commands, the technician needs to collect the output and provide it to the administrator. Which of the following should the technician use to fulfill the administrator ' s request?
A support technician must install software that allows a user to deliver a project status presentation to external stakeholders. Which of the following software types should the technician install?
A desktop technician is mapping a remote Windows share \\WinNAS\shared as local drive Z:. Which command should the technician run?
After a recent system update, a user ' s Windows 11 computer begins to experience slower boot times. The user notices additional icons are in the system tray. Which of the following should a technician do first to resolve the issue?
A technician needs to configure settings for password complexity and failed log-in attempts before a user is locked out. These settings cannot be changed by standard users. Which of the following MMC snap-ins should the technician use?
A malicious actor uses multiple endpoints to target a single endpoint. Which of the following describes this threat?
The battery on a user’s smartphone discharges quickly when the user travels. The smartphone was replaced two weeks ago. Which of the following should a technician do first?
Users are reporting that an unsecured network is broadcasting with the same name as the normal wireless network. They are able to access the internet but cannot connect to the file share servers. Which of the following best describes this issue?
A user reports that their computer is running extremely slowly. They are also often redirected to unknown websites when attempting to access internal applications. The computer ' s antivirus software is outdated, and the user cannot access certain security-related settings. A network administrator confirms that all other workstations are operating normally, and network diagnostics show no issues. Which of the following should the administrator do next to troubleshoot these issues?
A help desk technician recently installed an SSH client on a workstation in order to access remote servers. What does this enable?
After a technician upgrades the RAM on a user ' s workstation, the system shows a “No boot device found” message. Which of the following is most likely the cause?
An endpoint ' s screensaver no longer activates automatically. The global security policy states that the screensaver should activate after the endpoint has been idle for an hour. Which of the following commands should the technician run on the endpoint to investigate this issue?
A customer wants to format an external hard drive to work on both Windows and macOS. Which of the following filesystems is the best to use?
Technicians are failing to document user contact information, device asset tags, and a clear description of each issue in the ticketing system. Which of the following should a help desk management team implement for technicians to use on every call?
A customer must access the contents of the AppData folder, which is in the local user profile. Which of the following should a technician configure so the customer can easily navigate to this location?
Which of the following file types would a desktop support technician most likely use to automate tasks for a Windows user log-in?
Which of the following file systems allows macOS to write data?
An international traveler is concerned about others accessing the contents of their smartphone if it is lost or stolen. The traveler has enabled biometrics. Which of the following additional security measures further reduces the risk of unauthorized data access?
Which of the following filesystems is a successor to NTFS?
Which of the following helps to maintain integrity during a forensic investigation?
Which of the following describes an attack in which an attacker sets up a rogue AP that tricks users into connecting to the rogue AP instead of the legitimate network?
Which of the following is the best way to distribute custom images to 800 devices that include four device vendor classes with two types of user groups?
After completing malware removal steps, what is the next step the technician should take?
An end user is unable to access the intranet. A technician needs to confirm whether the Windows web server is online and functioning. Which of the following default remote access technologies would the technician most likely use to remotely connect to the server?
A user is working from home and is unable to access work files on a company laptop. Which of the following should a technician configure to fix the network access issue?
After using a third-party disk optimization software package, a technician restarts a laptop and receives the message “No operating system found.” The technician verifies that the BIOS properly recognizes the SSD. Which of the following should the technician do next?
After a user installs a mobile application from an advertisement, the phone ' s battery dies a few hours later and becomes hot to touch, even when not in use. Which of the following should a technician do first?
A customer laptop has been shutting down unexpectedly. The customer explains that a blue screen appears just before the laptop turns off, but the screen disappears too quickly to see anything. Which of the following tools should a technician use to find details about the error?
A user needs to install and uninstall software on their Windows laptop but does not need to manage user accounts. The company follows least-privilege principles. Which of the following account types meets these requirements?
A company wants to perform an in-place upgrade of operating systems on all workstations. All types of removable storage are disabled for security reasons. Which of the following is the best way to upgrade while keeping security settings in place?
A technician must install a legacy business application on a new computer. The new computer does not meet the application ' s requirements. Which of the following steps should the technician take to ensure the application installs and runs correctly?
A user requires a temporary computer to perform duties. Which of the following is a way to leave minimal user data on the computer?
A town clerk wants to work from home and access documents on a town hall server. What should a technician set up?
Which of the following are system folders on macOS? (Select two)
A technician is assisting a user who is growing increasingly frustrated because an application continuously crashes. The technician must coordinate with another department to resolve the issue. Which of the following actions should the technician take to effectively and professionally communicate with the user?
Which of the following allows users to prevent malware installation and the disclosure of sensitive information?
An administrator must rename the administrator account on a Windows desktop. Which tool is best for this?
A customer is unable to open some files on their system. Each time the customer attempts to open a file, the customer receives a message that the file is encrypted. Which of the following best describes this issue?
Which of the following is found in an MSDS sheet for a battery backup?
A customer’s laptop will not turn on. The customer is distraught and panicking because the laptop contains family pictures that can never be replaced. Which of the following communication techniques is most important for the technician to demonstrate in this situation?
An administrator received an email stating that the OS they are currently supporting will no longer be issued security updates and patches. Which of the following is most likely the reason the administrator received this message?
Which of the following must be followed during incident response to ensure the collected evidence is properly handled and accounted for?
A user takes an iOS-based smartphone to a repair shop due to performance issues. The technician observes:
Battery charge: 25%
Battery health: 90%
Hotspot: On
Used space: 63.76GB / 64GB
Which of the following is the most likely cause of the performance issue?
A technician needs to map a shared drive from a command-line interface. Which of the following commands should the technician use?
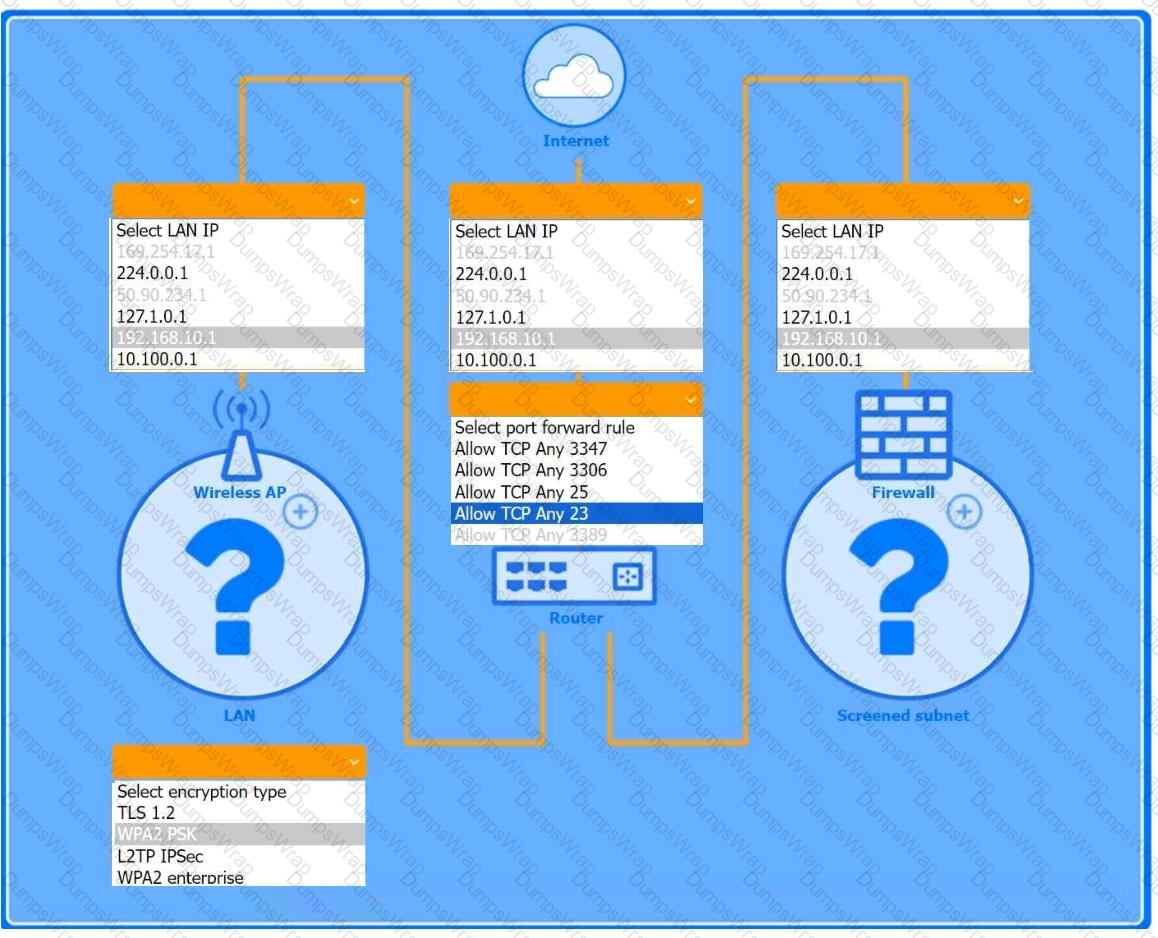
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
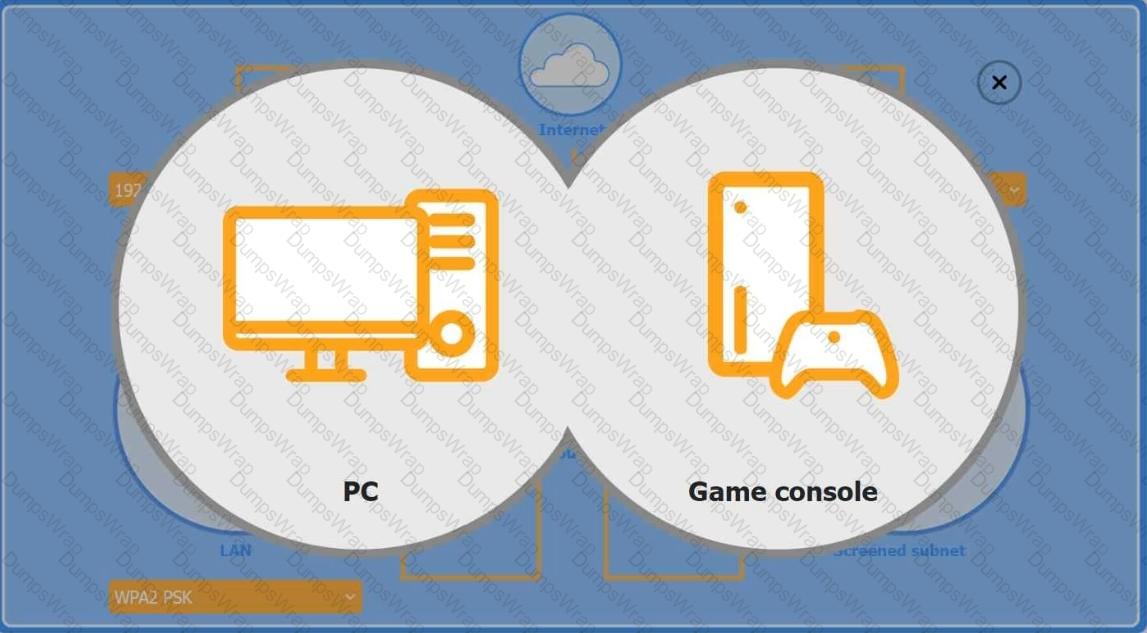
Firewall Screened Subnet
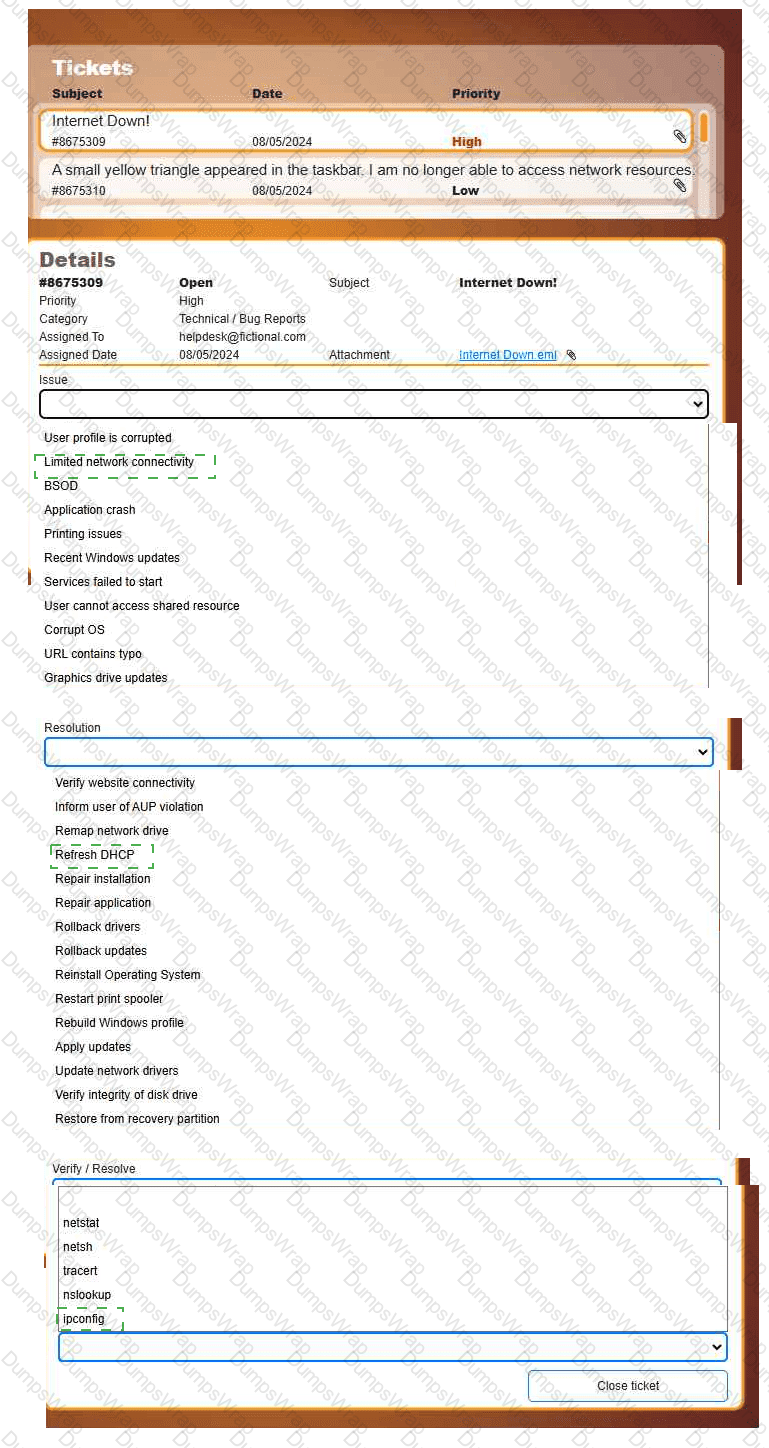
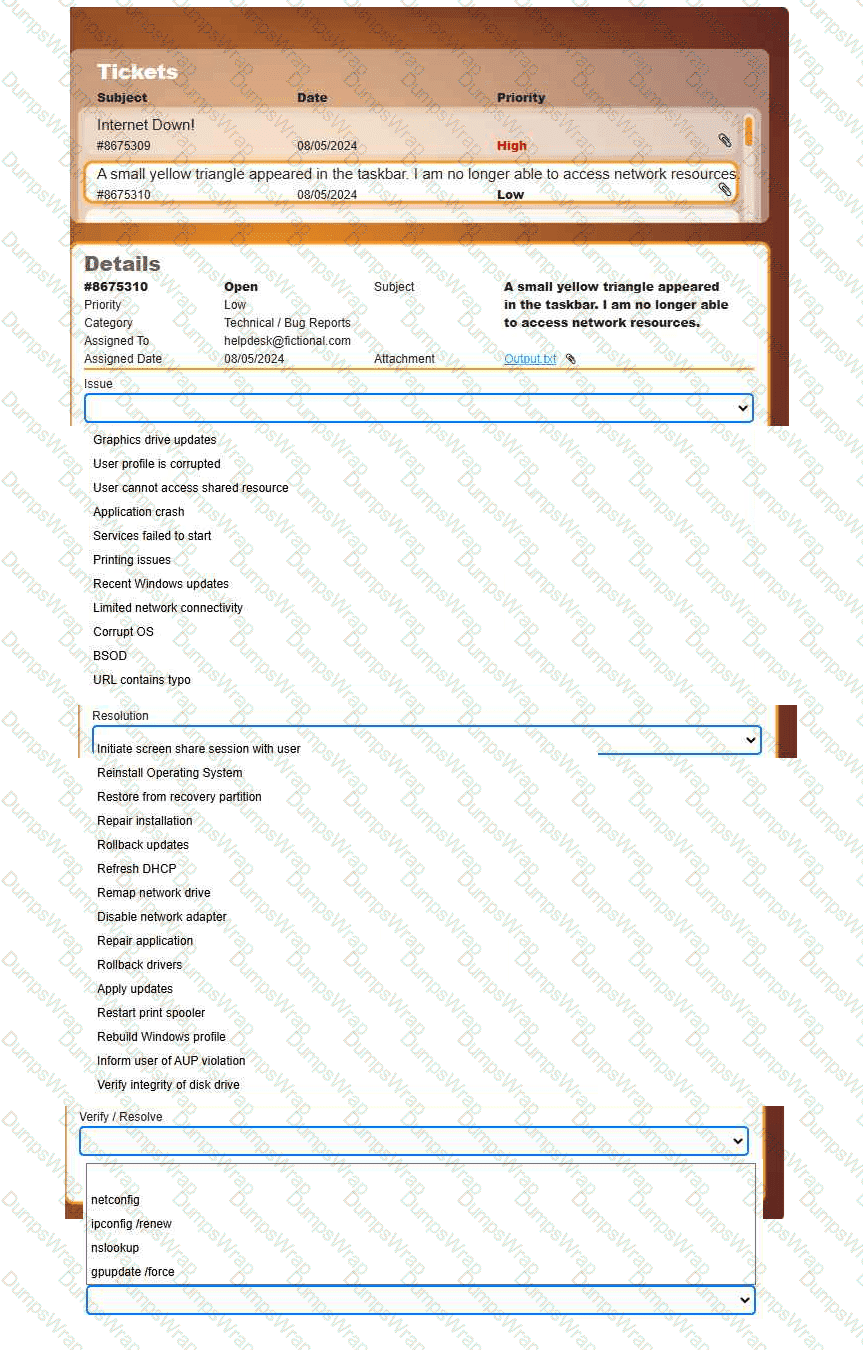
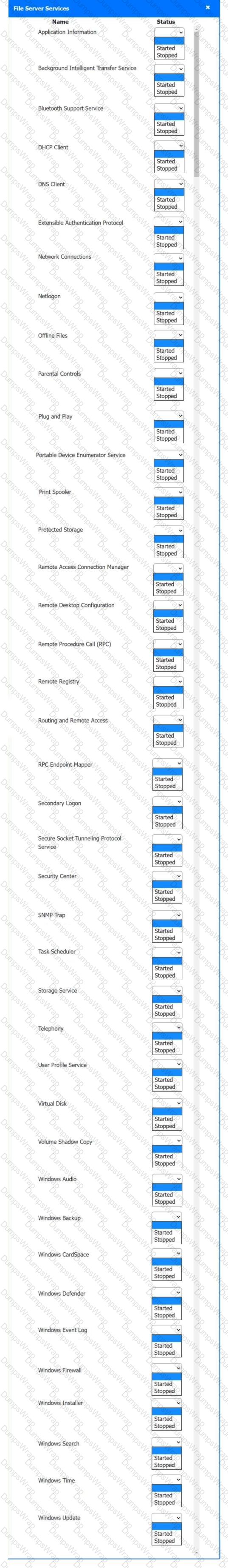
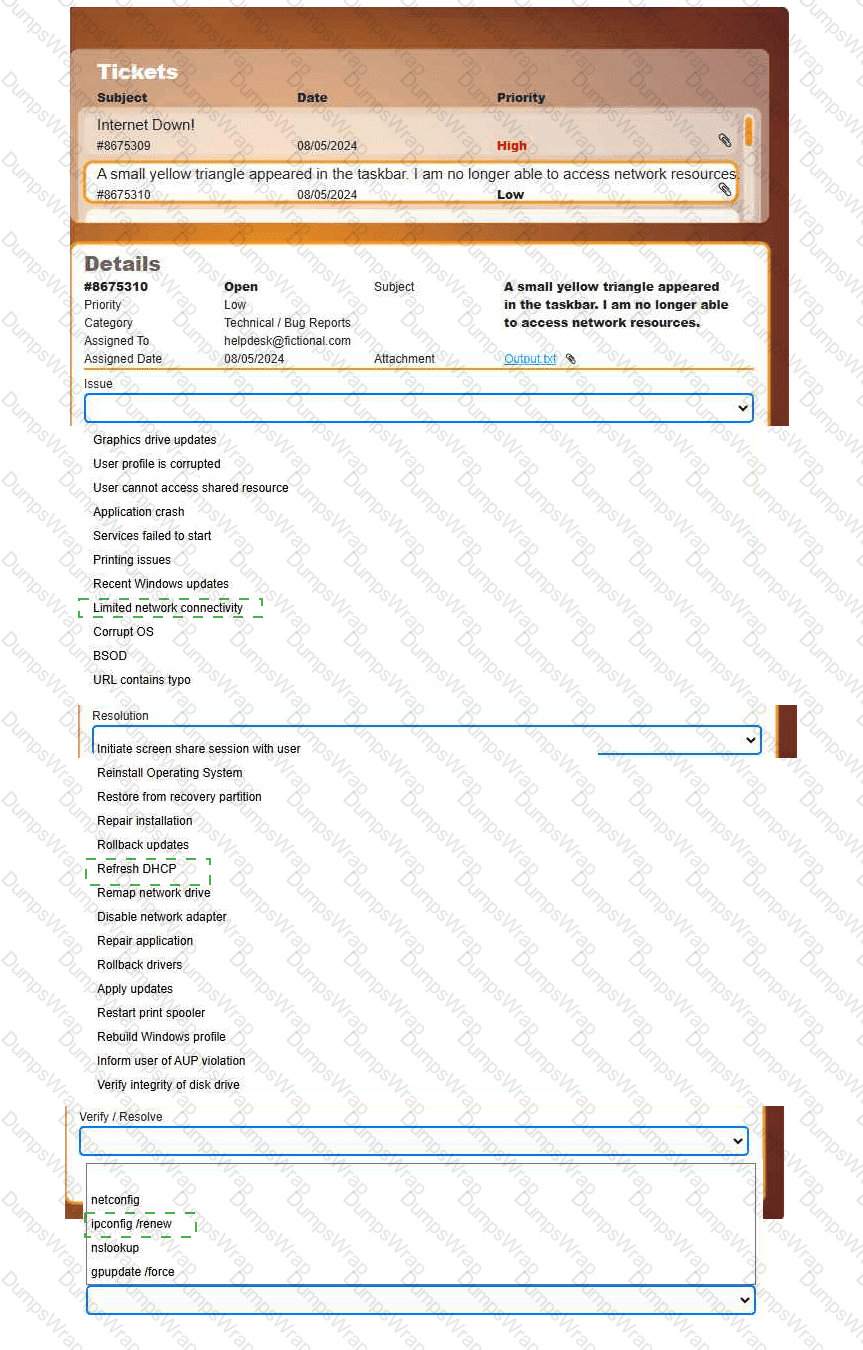
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
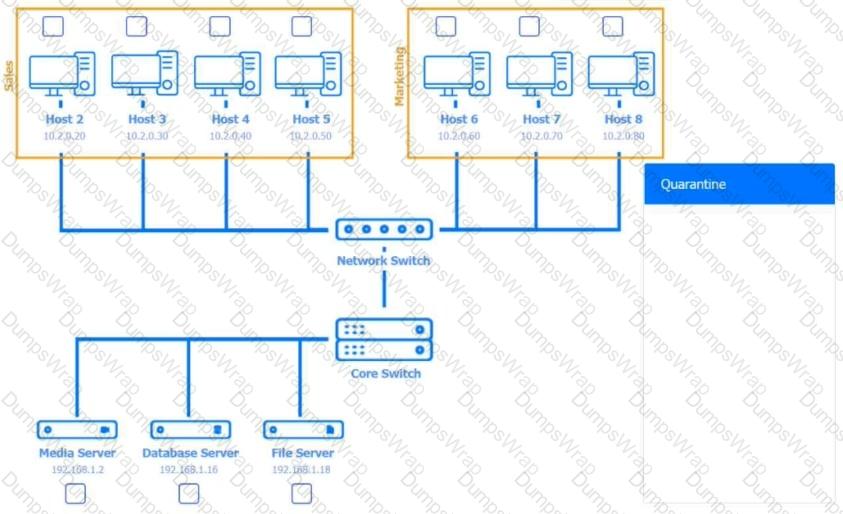
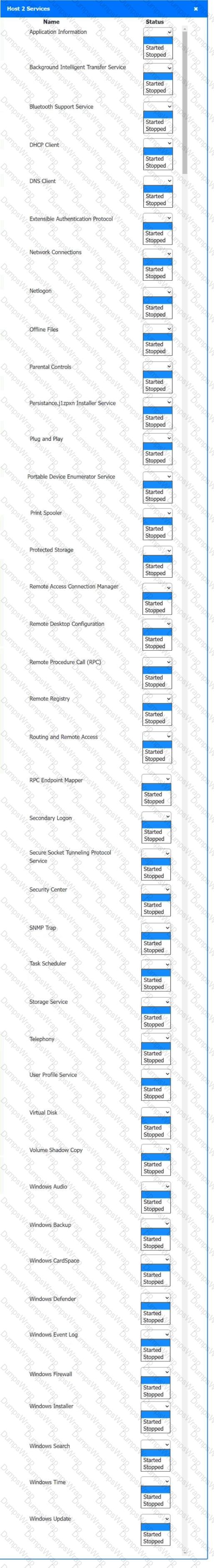
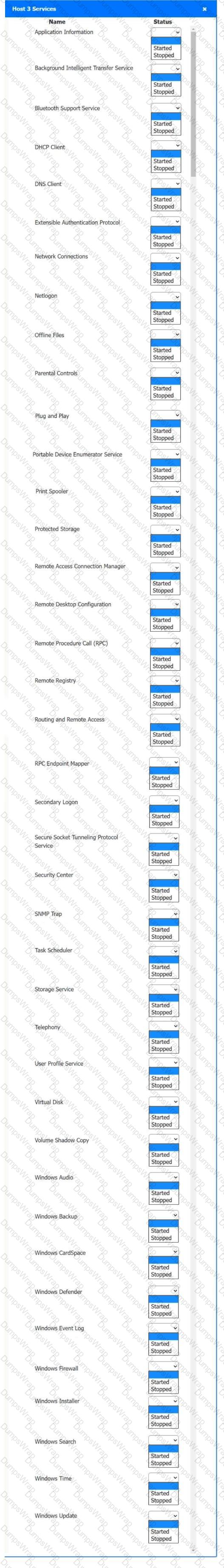
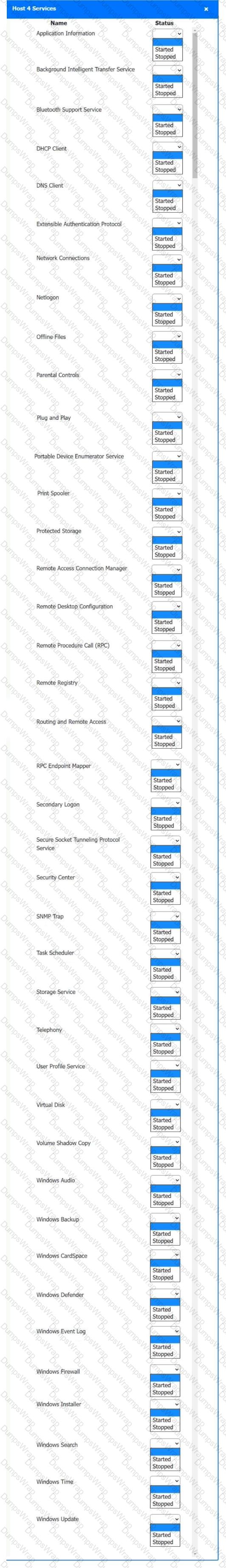
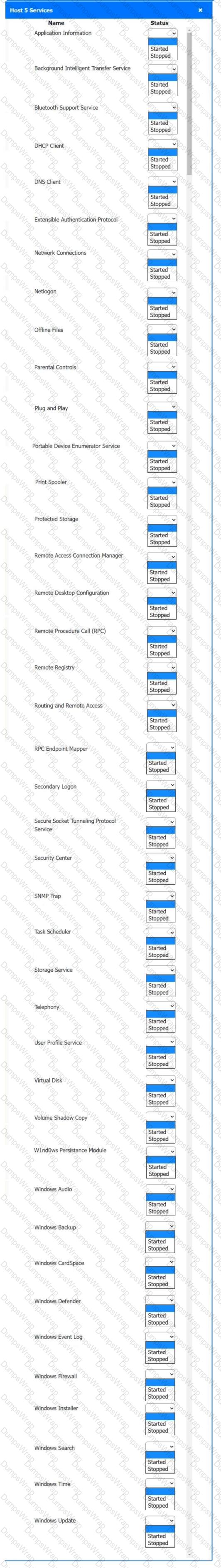
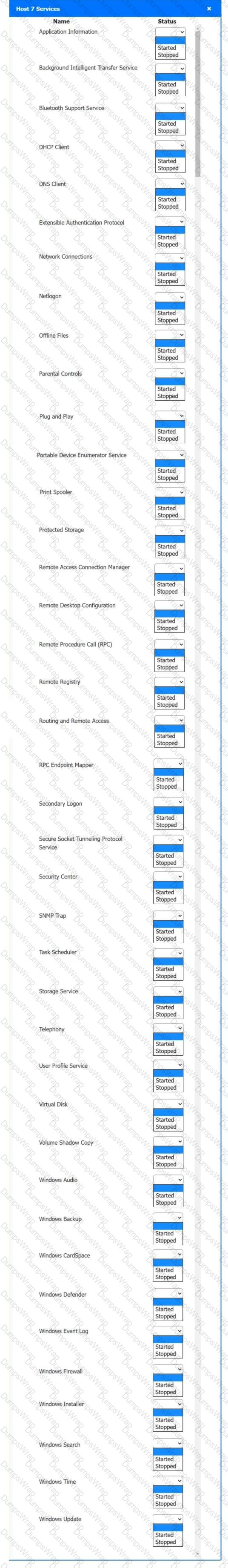
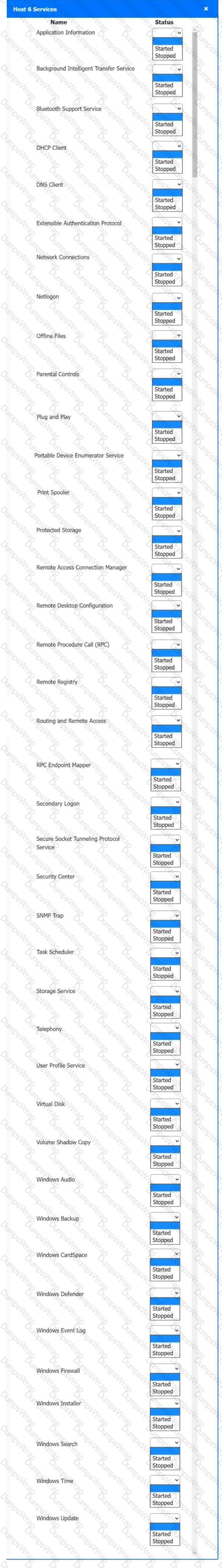
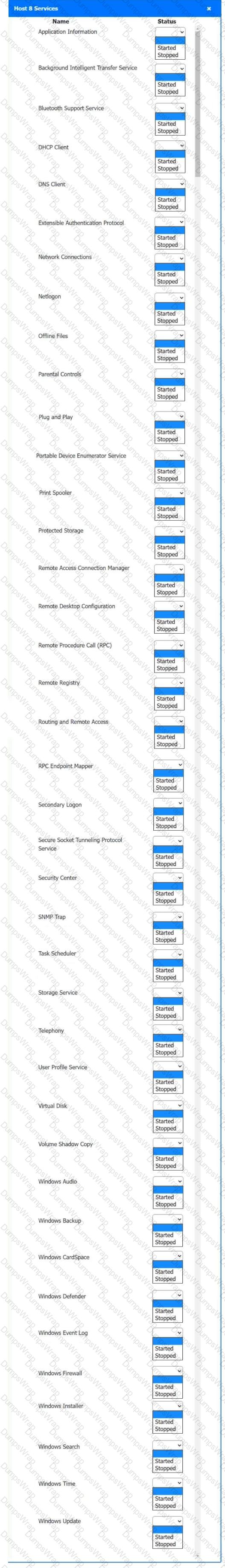
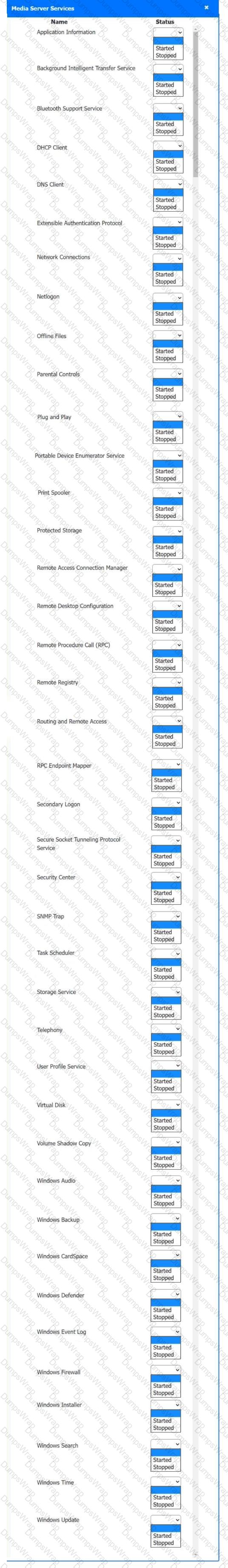
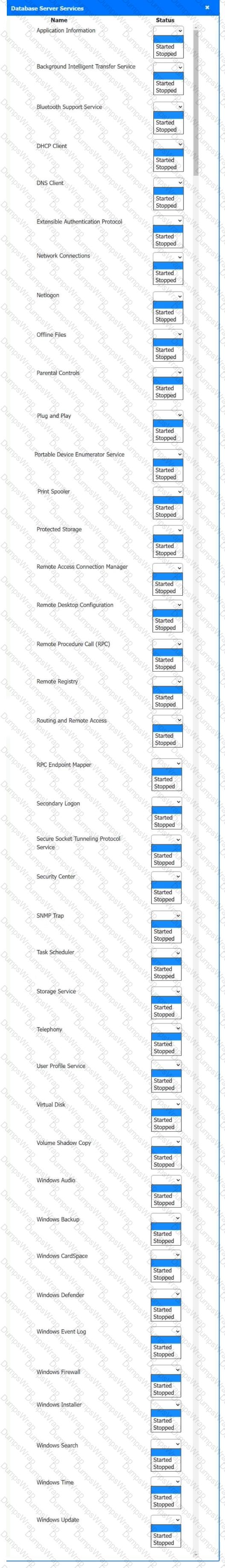
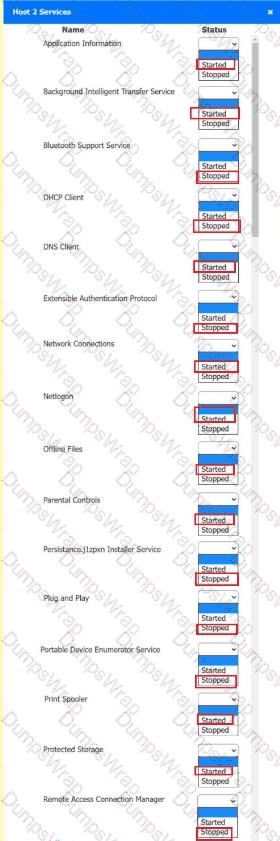
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
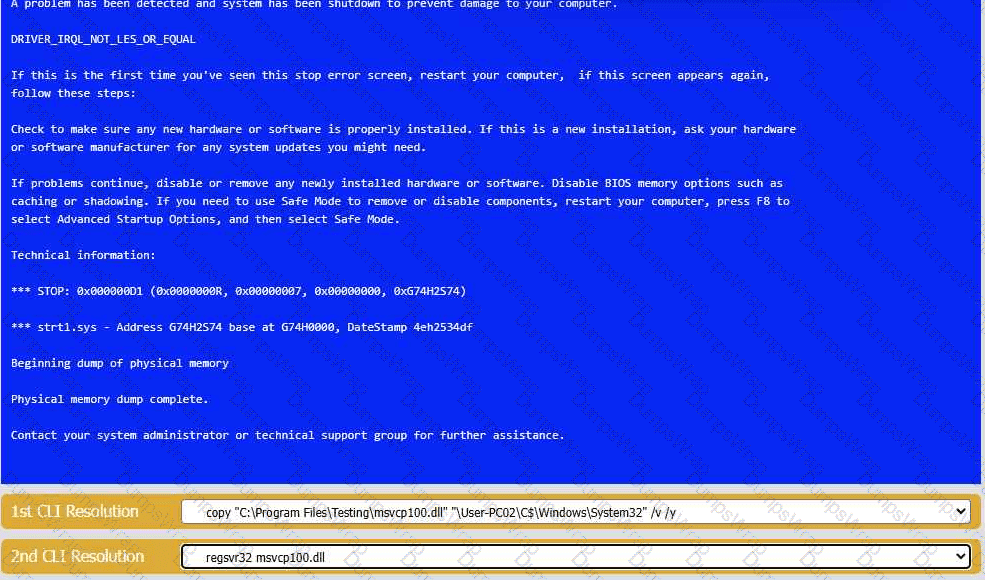
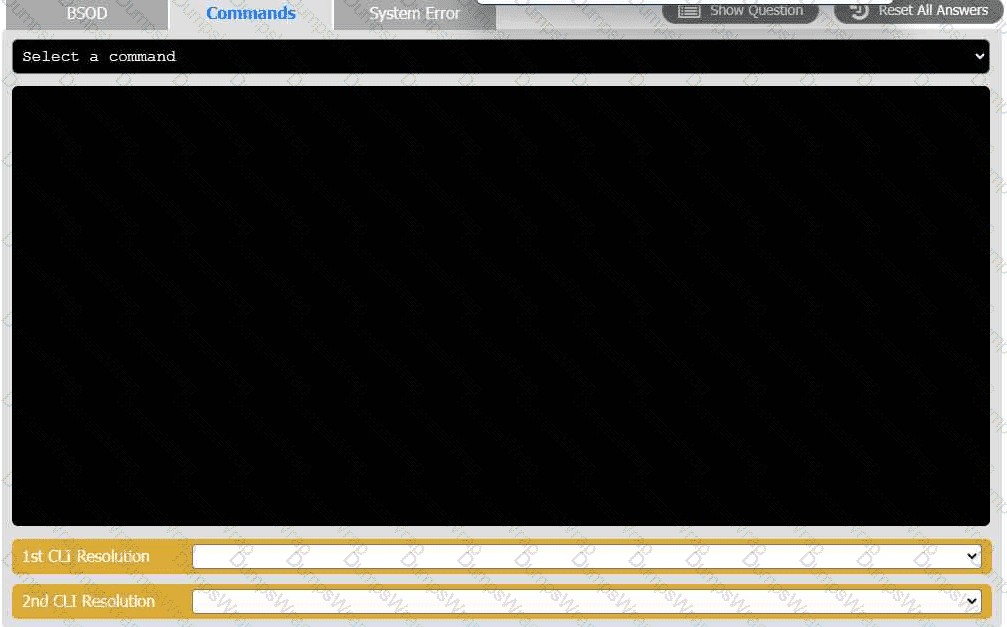
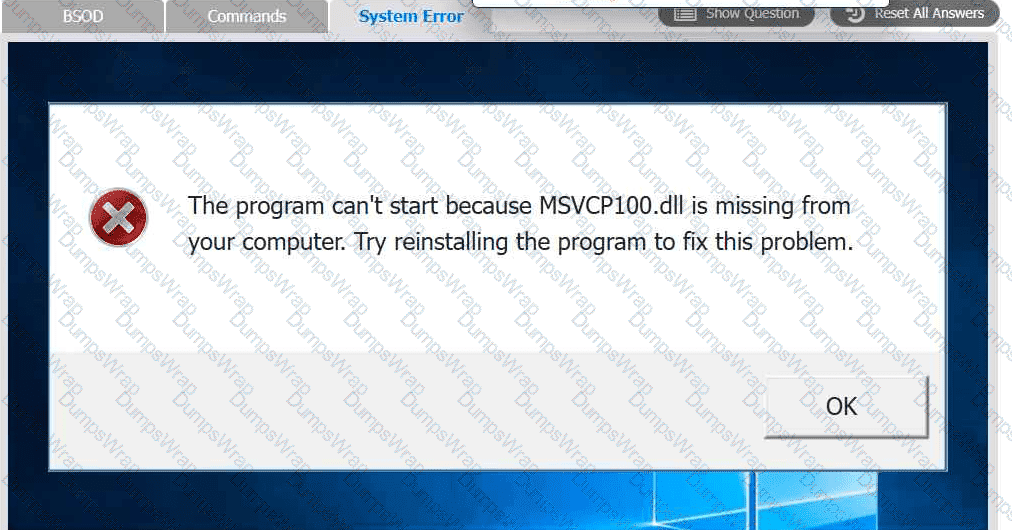
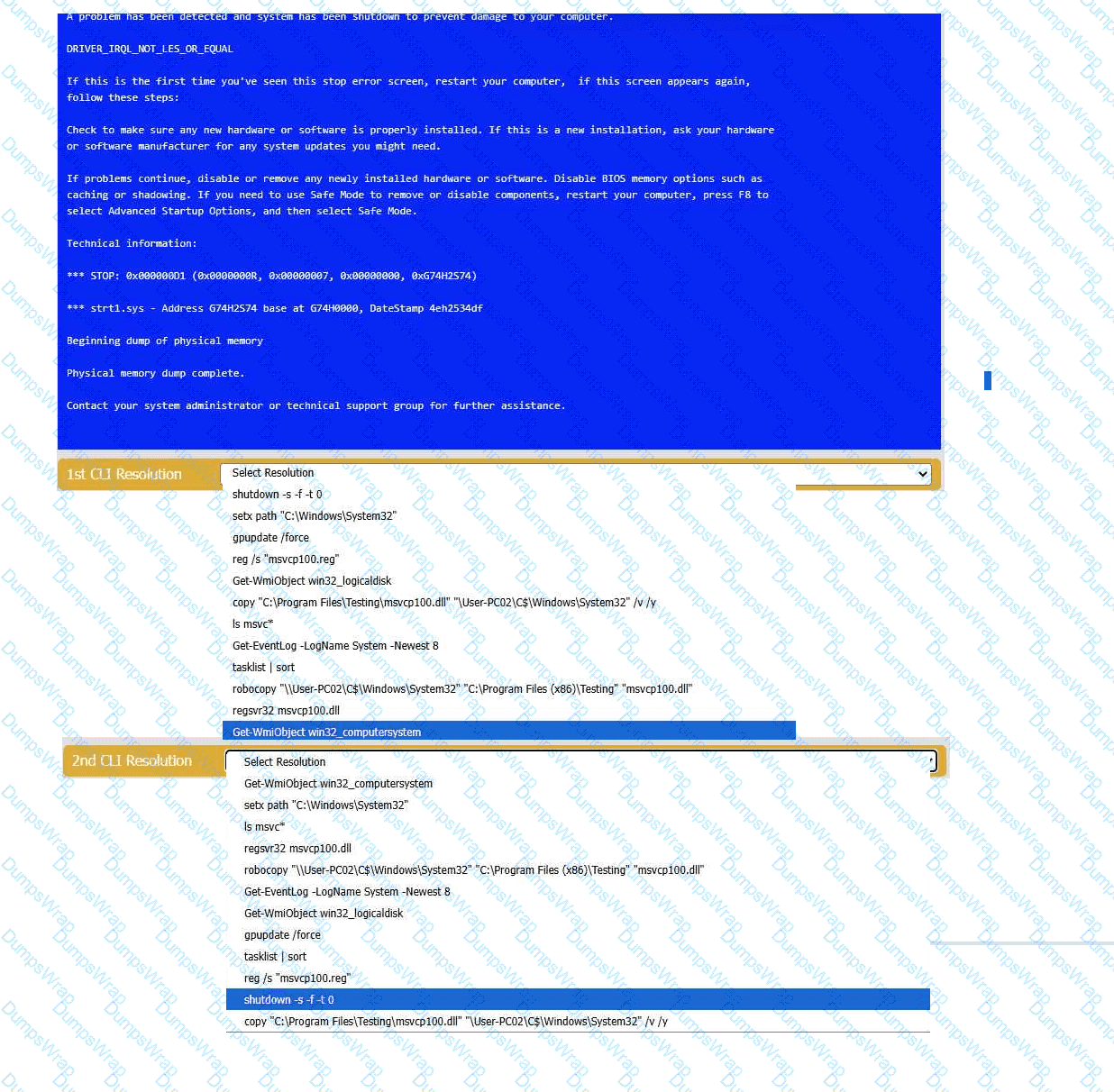
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
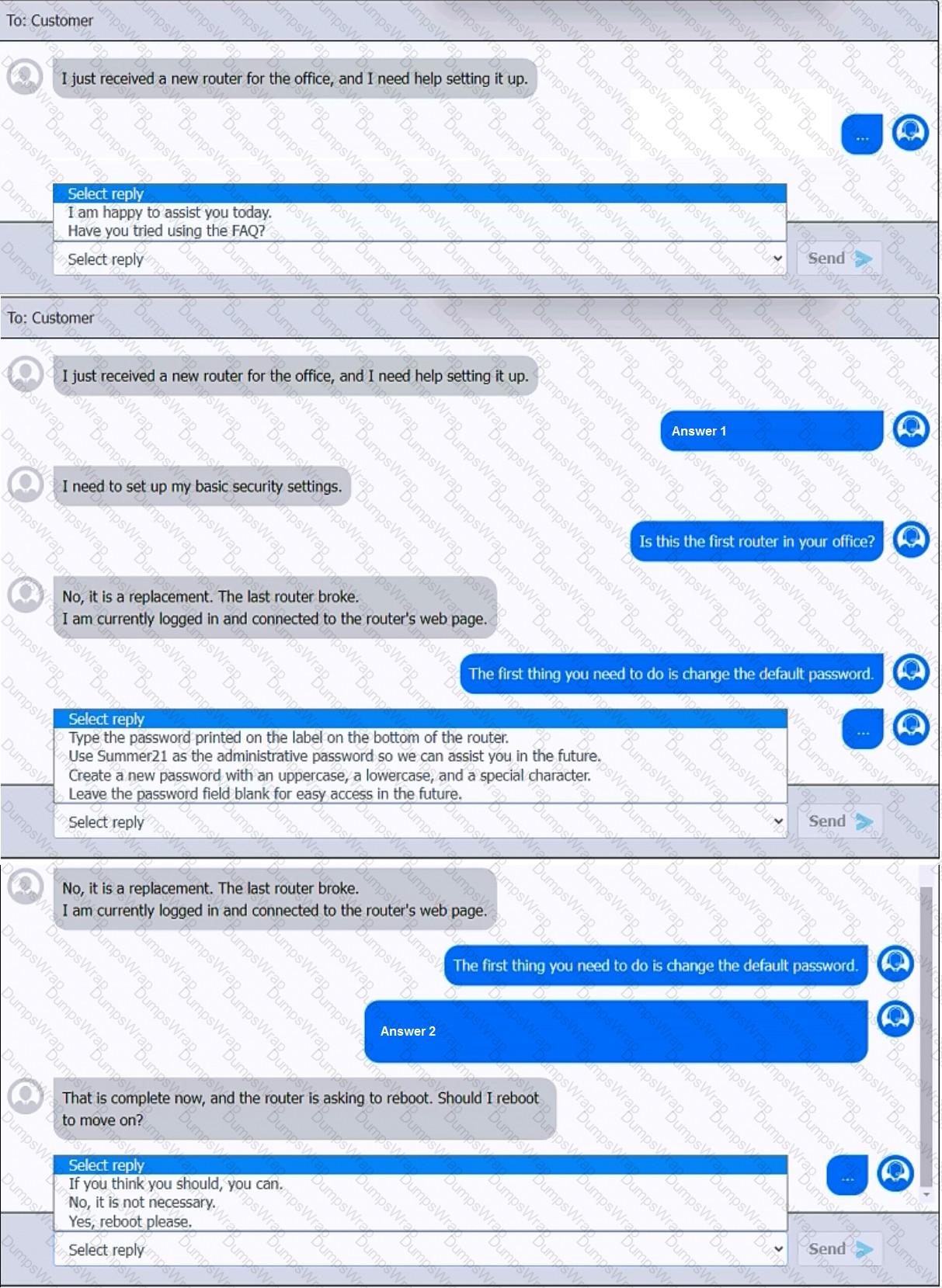
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
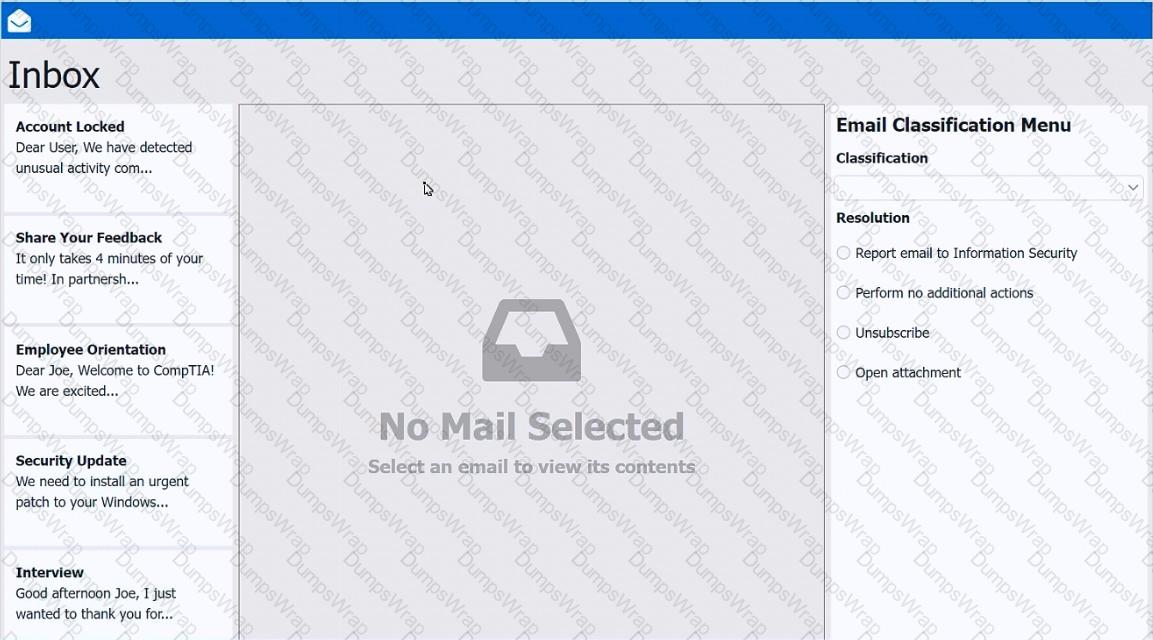
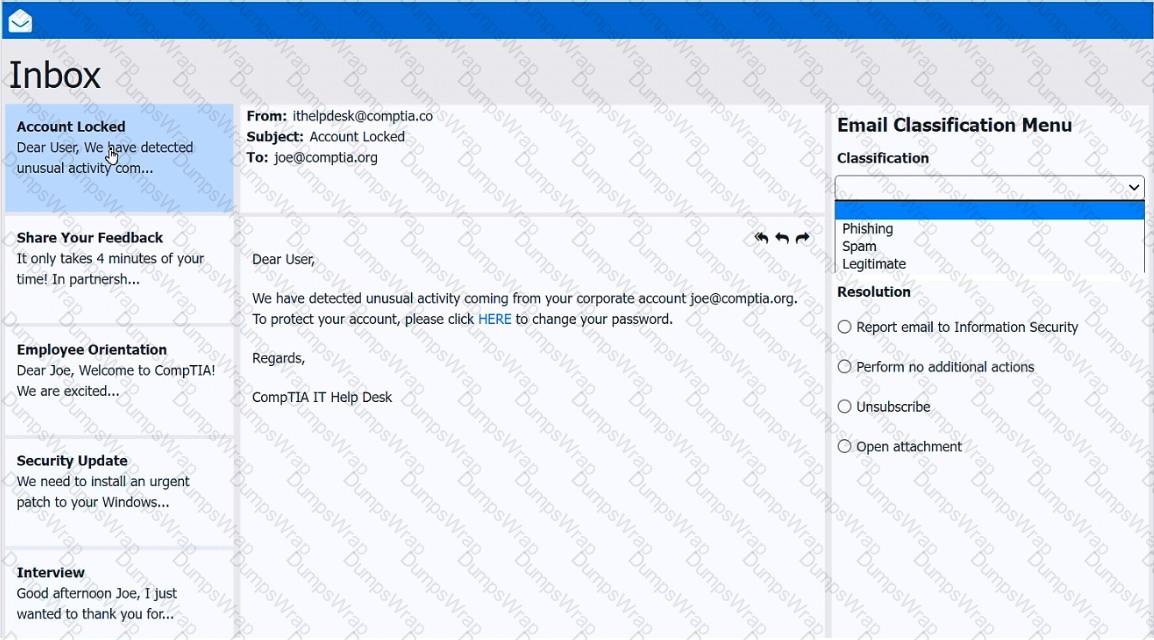
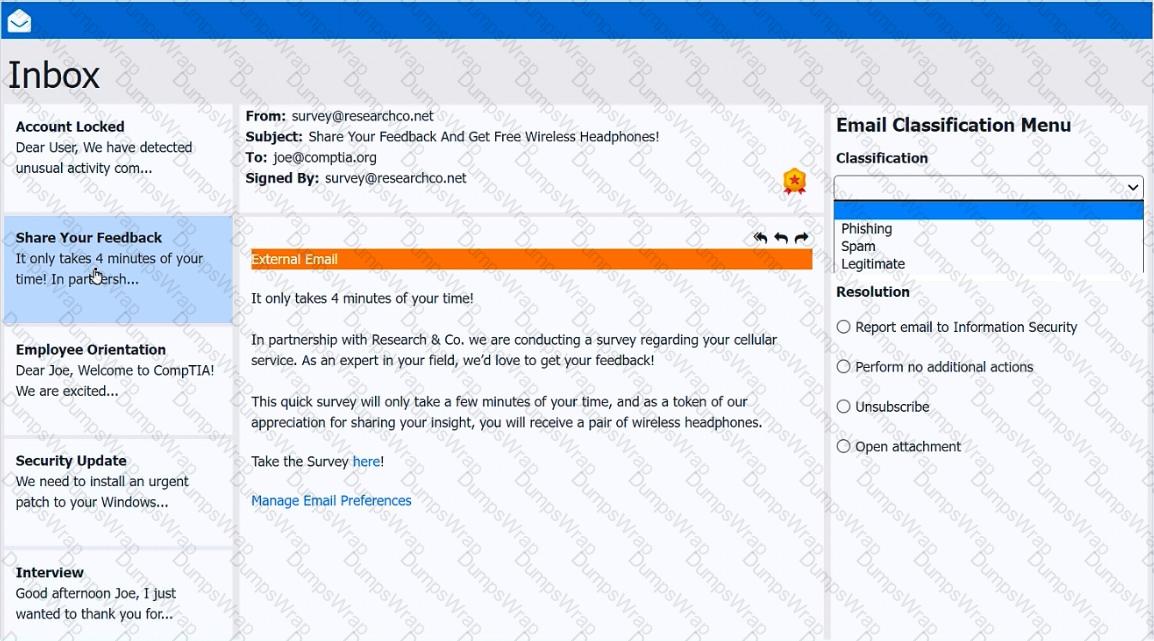
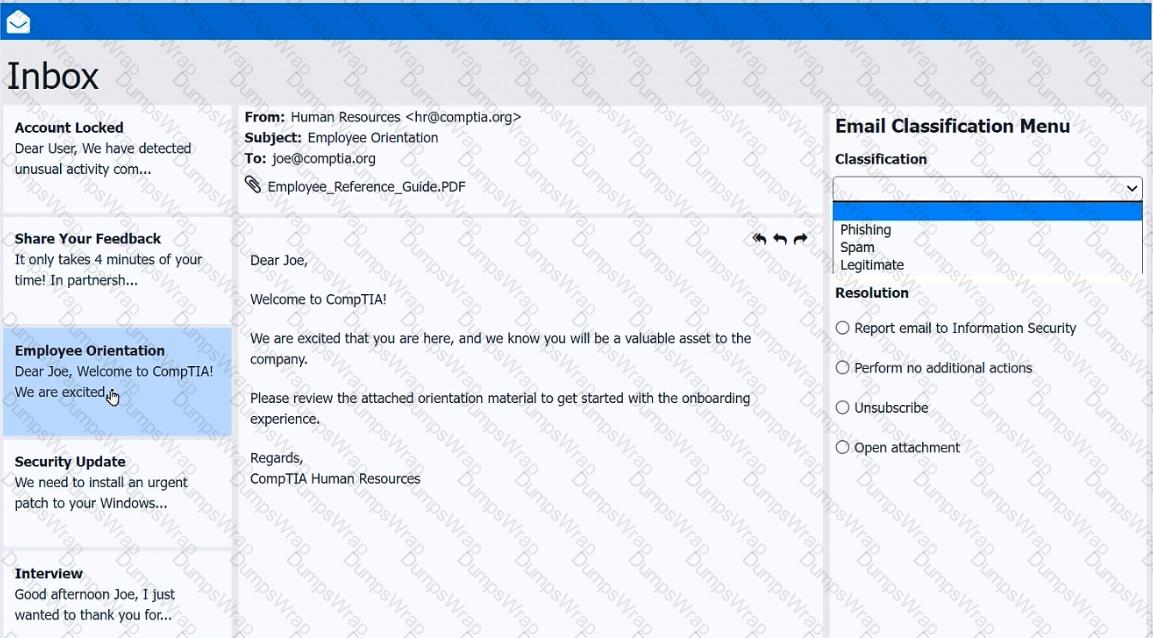
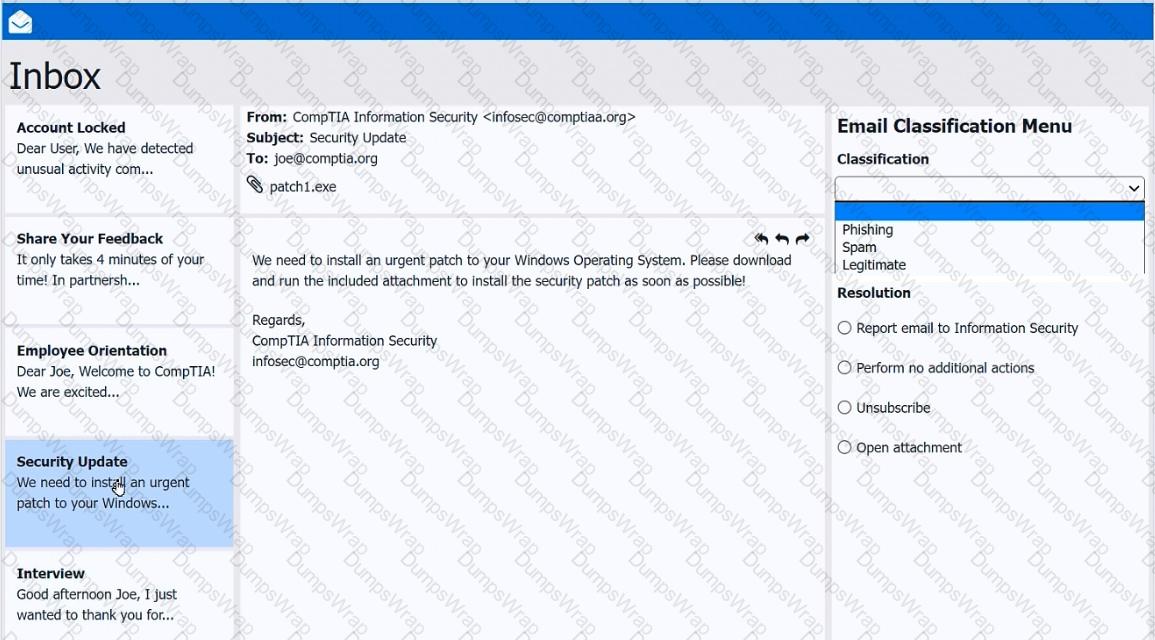
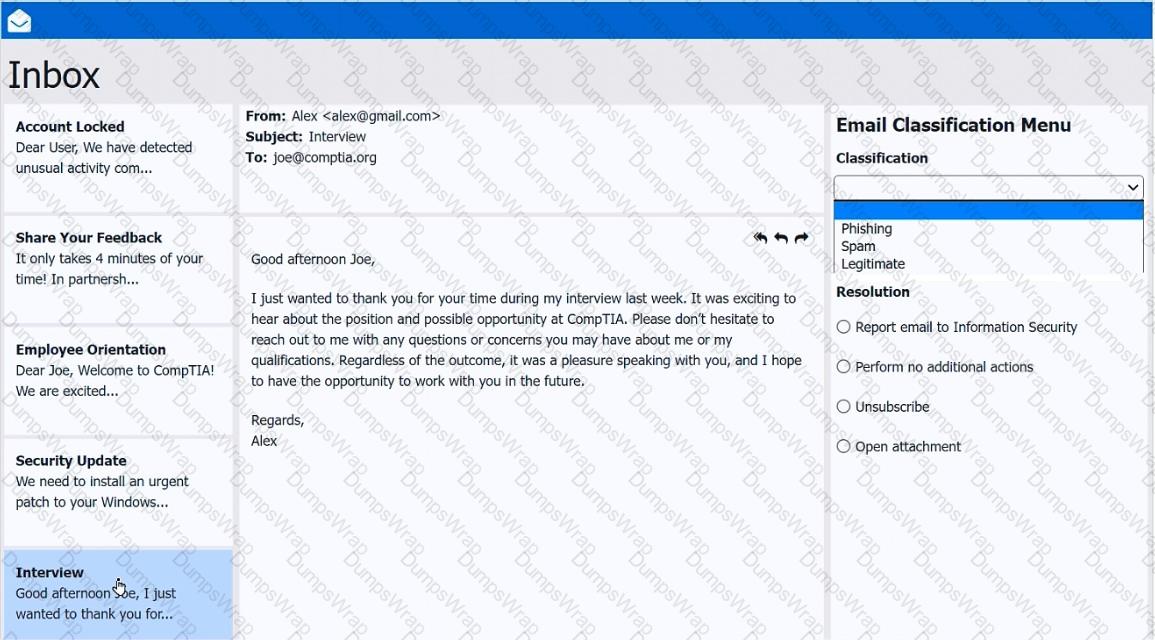
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
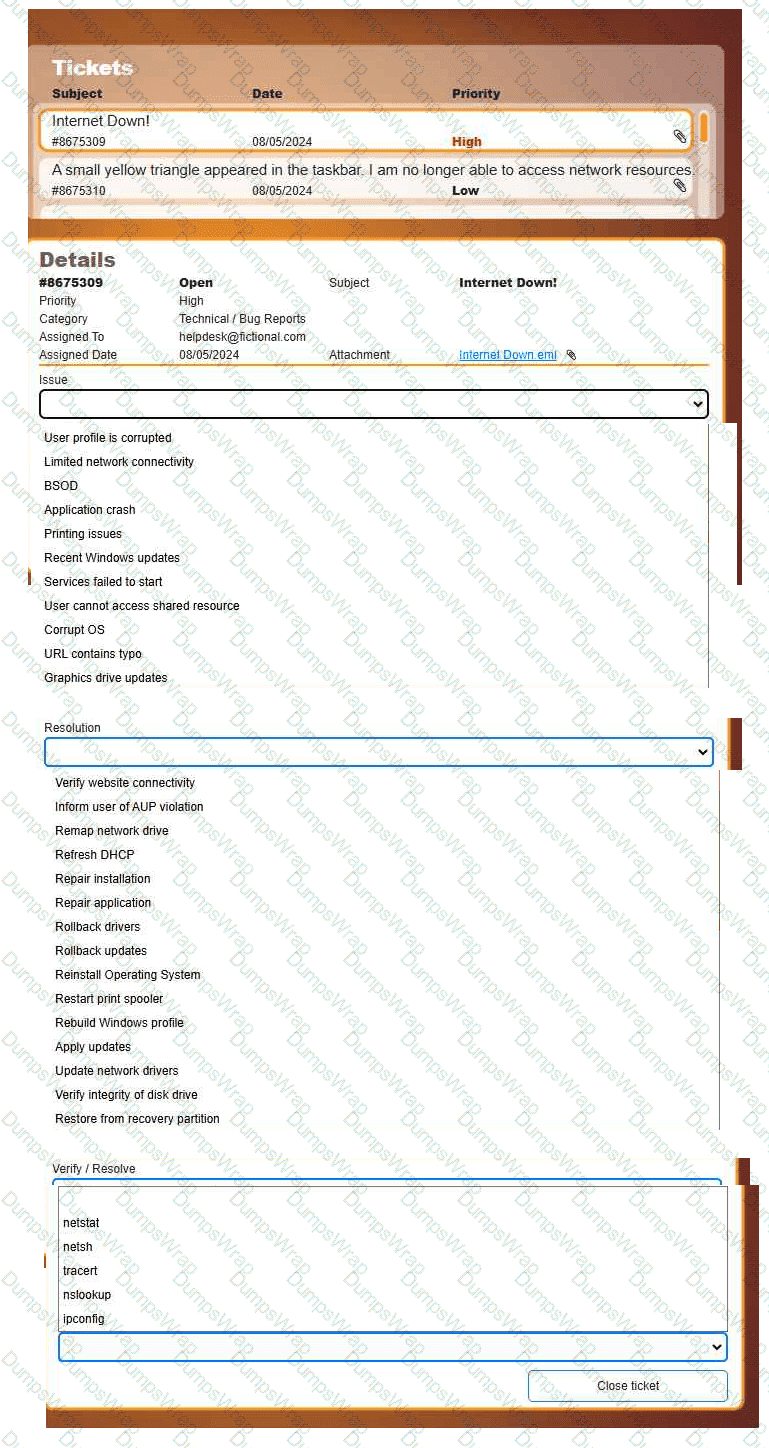
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.

 A screenshot of a computer AI-
A screenshot of a computer AI-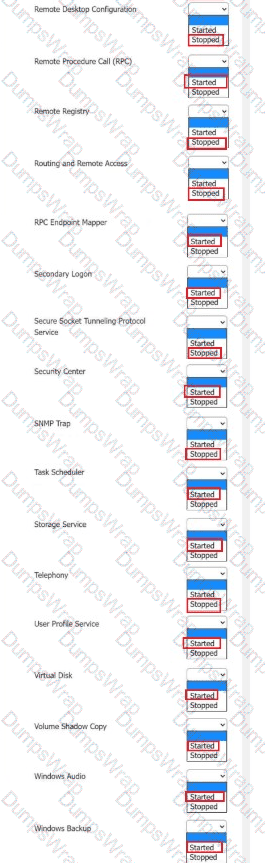 A screenshot of a computer AI-
A screenshot of a computer AI-