CompTIA Cloud+ (V4) Questions and Answers
Which of the following types of storage provides the greatest performance advantage for a traditional relational database?
Department supervisors have requested a report that will help them understand the utilization of cloud resources, make decisions about budgeting for the following year, and reduce
costs. Which of the following are the most important requisite steps to create the report? (Select two).
A security analyst confirms a zero-day vulnerability was exploited by hackers who gained access to confidential customer data and installed ransomware on the server Which of the following steps should the security analyst take? (Select two).
An on-call cloud engineer receives a critical alert about an e-commerce web server being unresponsive. Which of the following steps should the engineer take first?
The company's IDS has reported an anomaly. The cloud engineer remotely accesses the cloud instance, runs a command, and receives the following information:
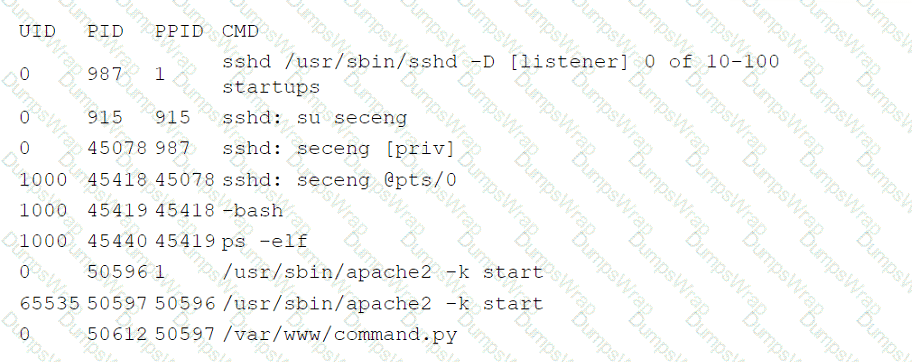
Which of the following is the most likely root cause of this anomaly?
An administrator attempts to use a script to deploy a cloud-based virtual machine with five data disks. After running the script, the administrator sees the following message:
ERROR: Response 403, storage API provisioning error.
Which of the following is the reason the deployment failed?
Which of the following is a direct effect of cloud migration on an enterprise?
Which of the following refers to the idea that data should stay within certain borders or territories?
Which of the following is the most cost-effective way to store data that is infrequently accessed?
A healthcare organization must follow strict compliance requirements to ensure that Pll is not leaked. The cloud administrator needs to ensure the cloud email system can support this requirement Which of the following should the organization enable?
Which of the following do developers use to keep track of changes made during software development projects?
A high-usage cloud resource needs to be monitored in real time on specific events to guarantee its availability. Which of the following actions should be used to meet this requirement?
A cloud security analyst is looking for existing security vulnerabilities on software applications. Which of the following describes this vulnerability management phase?
A user's assigned cloud credentials are locked, and the user is unable to access the project's application. The cloud administrator reviews the logs and notices several attempts to log in with the user's account were made to a different application after working hours. Which of the following is the best approach for the administrator to troubleshoot this issue?
A cloud developer needs to update a REST API endpoint to resolve a defect. When too many users attempt to call the API simultaneously, the following message is displayed:
Error: Request Timeout - Please Try Again Later
Which of the following concepts should the developer consider to resolve this error?
A write-intensive workload is having frequent performance issues. The workload is running on pay-as-you-go VMs. These VMs use SSDs and have appropriate CPU and RAM sizes. The workload writes millions of small files and has a one-year retention requirement. Which of the following actions should be taken?
A cloud solutions architect needs to design a solution that will collect a report and upload it to an object storage service every time a virtual machine is gracefully or non-gracefully
stopped. Which of the following will best satisfy this requirement?
A company has ten cloud engineers working on different manual cloud deployments. In the past, engineers have had difficulty keeping deployments consistent. Which of the following is the best method to address this issue?
A newly configured VM fails to run application updates despite having internet access. The updates download automatically from a third-party network. Given the following output:
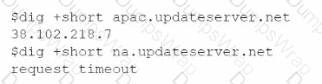
Which of the following troubleshooting steps would be best to take?
An organization is preparing for seasonal sales on its storefront web application. Which of the following approaches is best suited to meet this requirement with the minimal cost?
Which of the following Al/ML technologies consumes text input to discern tone?
A cloud networking engineer is troubleshooting the corporate office's network configuration. Employees in the IT and operations departments are unable to resolve IP addresses on all devices, and the IT department cannot establish a connection to other departments' subnets. The engineer identifies the following configuration currently in place to support the office network:
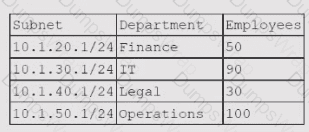
Each employee needs to connect to the network with a maximum of three hosts. Each subnet must be segregated, but the IT department must have the ability to communicate with all subnets. Which of the following meet the IP addressing and routing requirements? (Select two).
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
Given the following command:
Sdocker pull images.comptia.org/user1/myimage:latest
Which of the following correctly identifies images.comptia.org?
Five thousand employees always access the company's public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application Which of the following is the best configuration approach to resolve this issue?
A video surveillance system records road incidents and stores the videos locally before uploading them to the cloud and deleting them from local storage. Which of the following
best describes the nature of the local storage?
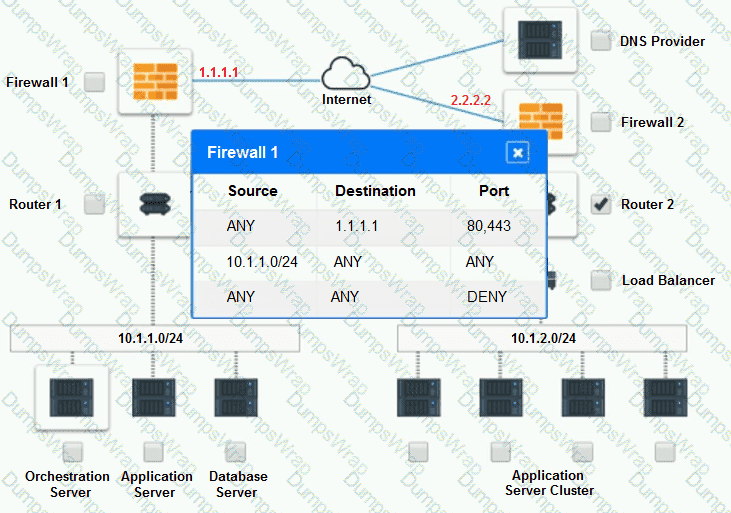
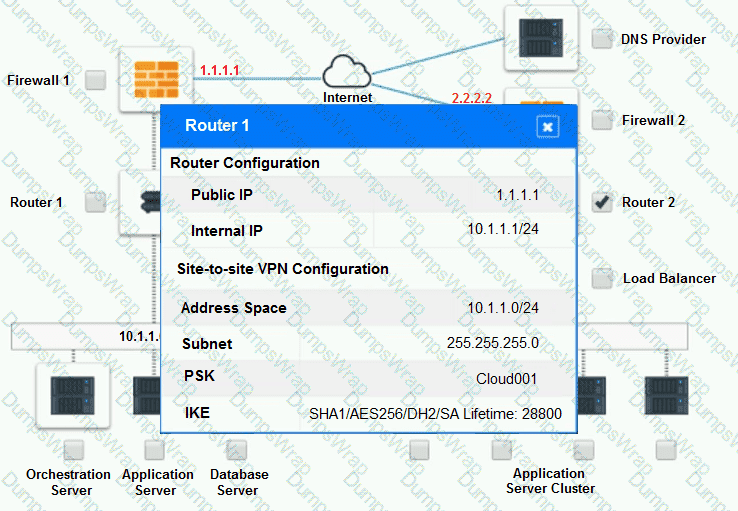
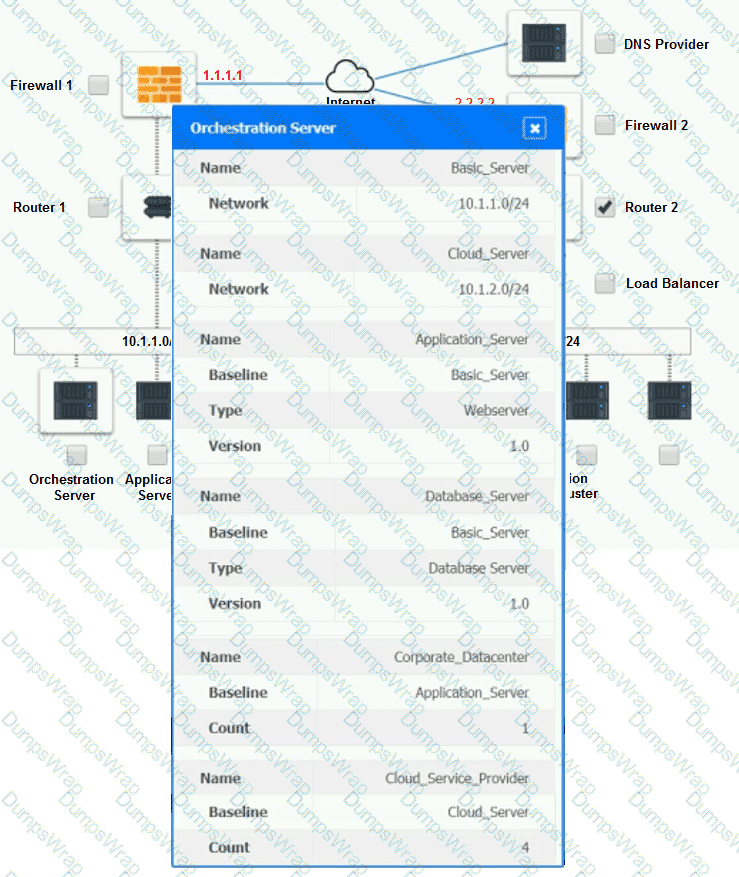
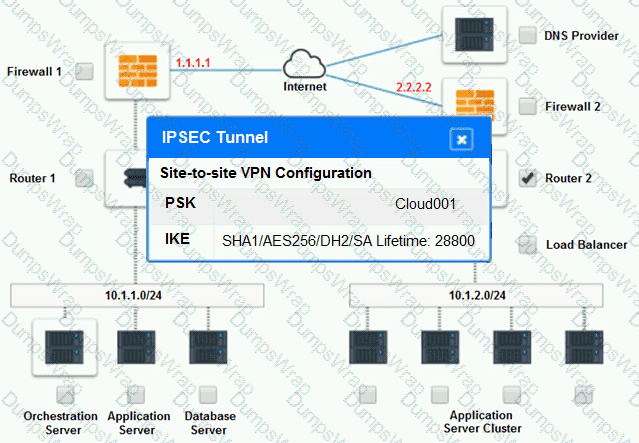
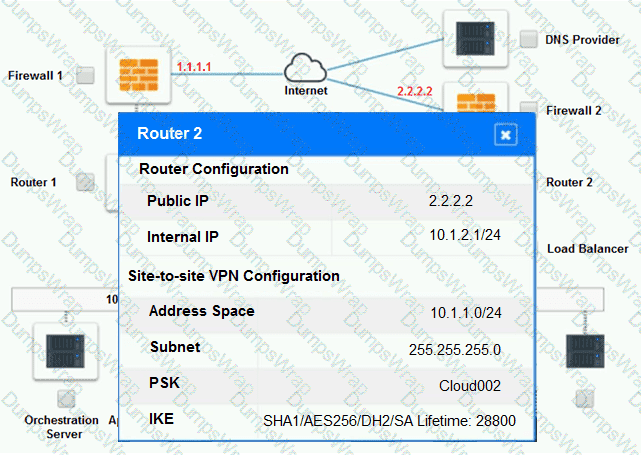
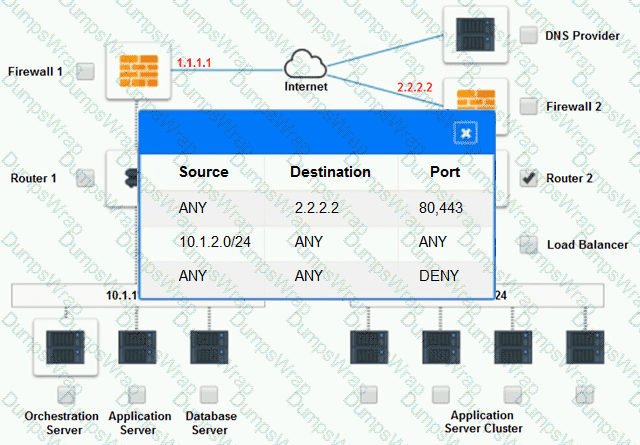
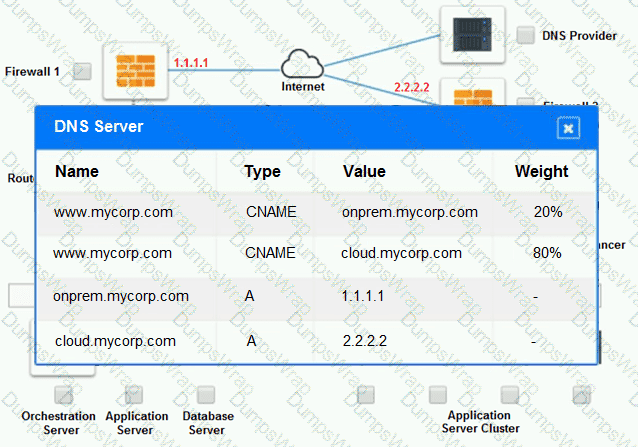
A company has decided to scale its e-commerce application from its corporate datacenter to a commercial cloud provider to meet an anticipated increase in demand during an upcoming holiday.
The majority of the application load takes place on the application server under normal conditions. For this reason, the company decides to deploy additional application servers into a commercial cloud provider using the on-premises orchestration engine that installs and configures common software and network configurations.
The remote computing environment is connected to the on-premises datacenter via a site-to-site IPSec tunnel. The external DNS provider has been configured to use weighted round-robin routing to load balance connections from the Internet.
During testing, the company discovers that only 20% of connections completed successfully.
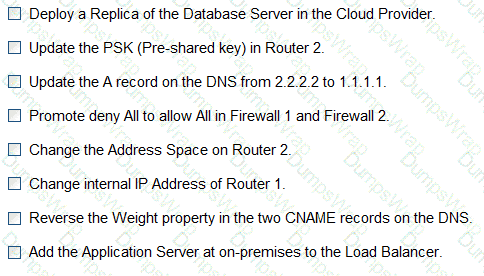
INSTRUCTIONS
Review the network architecture and supporting documents and fulfill these requirements:
Part 1:
 Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
Analyze the configuration of the following components: DNS, Firewall 1, Firewall 2, Router 1, Router 2, VPN and Orchestrator Server.
 Identify the problematic device(s).
Identify the problematic device(s).
Part 2:
 Identify the correct options to provide adequate configuration for hybrid cloud architecture.
Identify the correct options to provide adequate configuration for hybrid cloud architecture.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Part 1:
Cloud Hybrid Network Diagram
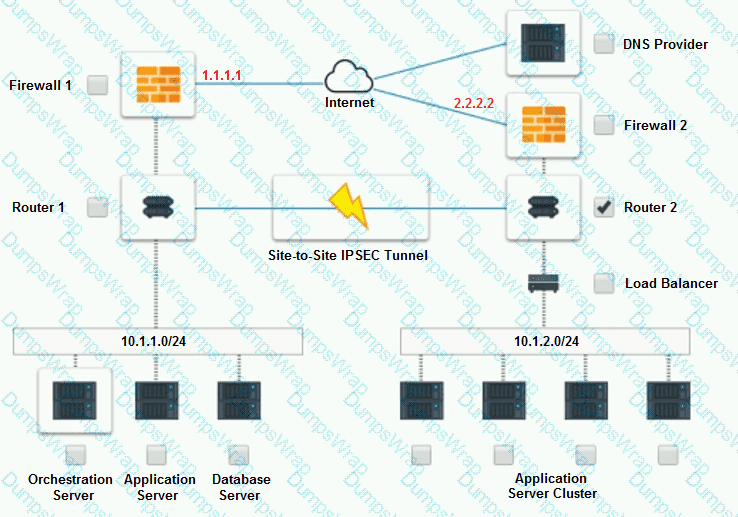
Part 2:
Only select a maximum of TWO options from the multiple choice question
Which of the following industry standards mentions that credit card data must not be exchanged or stored in cleartext?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
Which of the following application migration strategies will best suit a customer who wants to move a simple web application from an on-premises server to the cloud?
A cloud administrator is building a company-standard VM image, which will be based on a public image. Which of the following should the administrator implement to secure the image?
A cloud engineer is exploring options to reduce the management overhead of the servers and network. Which of the following cloud service models should the engineer implement?
Which of the following is a customer be responsible for in a provider-managed database service? (Select two).
A cloud infrastructure administrator updated the IP tables to block incoming connections and outgoing responses to 104.225.110.203. Which of the following vulnerability management steps is this an example of?
A government agency in the public sector is considering a migration from on premises to the cloud. Which of the following are the most important considerations for this cloud migration? (Select two).
A security analyst reviews the daily logs and notices the following suspicious activity:
The analyst investigates the firewall logs and identities the following:
Which of the following steps should the security analyst take next to resolve this issue? (Select two).
A cloud security analyst is investigating the impact of a recent cyberattack. The analyst is reviewing the following information:
Web server access log:
104.210.233.225 - - [21/10/2022:11:17: 40] "POST /uploadfile.html?f=myfile.php" 200 1638674
45.32.10.66 - - [21/10/2022:11:19:12] "GET /welcome.html" 200 5812
104.210.233.225 - - [21/10/2022:11:21:19] "GET / .. / .. / .. / .. /conf/server.xml HTTP/1.1" 200 74458
45.32.10.66 - - [21/10/22:11:22:32] "GET /admin.html HTTP/1.1" 200 9518
Web application firewall log:
"2022/10/21 11:17:33" "10.25.2.35" "104. 210.233.225" "userl" "File transfer completed successfully."
"2022/10/21 11:21:05" "10. 25.2. 35" "104. 210.233.225" "userl" "Accessed application page."
"2022/10/21 11:22:13" "10.25.2.35" "45. 32. 10. 66" "user2" "Accessing admin page. "
Which of the following has occurred?
A DevOps engineer is performing maintenance on the mail servers for a company's web application. Part of this maintenance includes checking core operating system updates. The servers are currently running version 3.2 of the operating system. The engineer has two update options—one to version 4.1 and the other to version 3.7. Both versions are fully supported by the operating system manufacturer. Which of the following best describes the action the engineer should take?
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
An e-commerce store is preparing for an annual holiday sale. Previously, this sale has increased the number of transactions between two and ten times the normal level of
transactions. A cloud administrator wants to implement a process to scale the web server seamlessly. The goal is to automate changes only when necessary and with minimal cost.
Which of the following scaling approaches should the administrator use?
A company has one cloud-based web server that is prone to downtime during maintenance. Which ot the following should the cloud engineer add to ensure high availability?
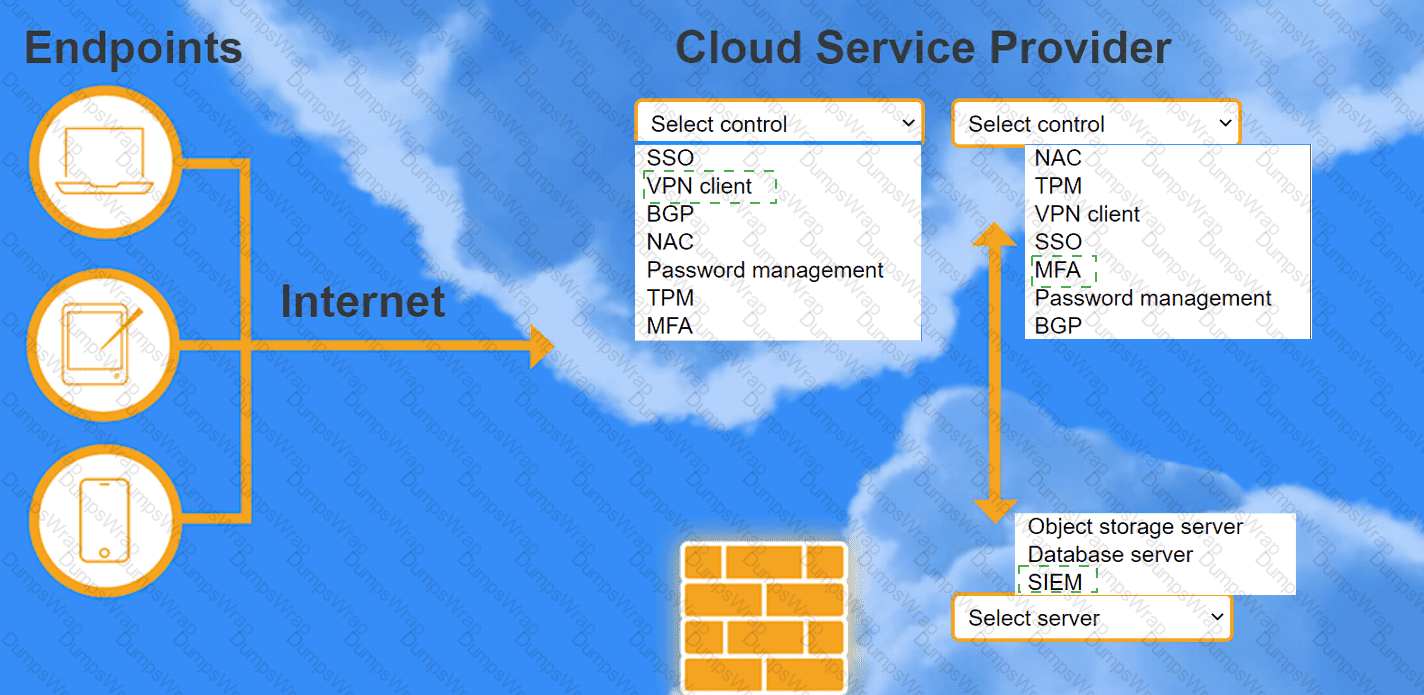
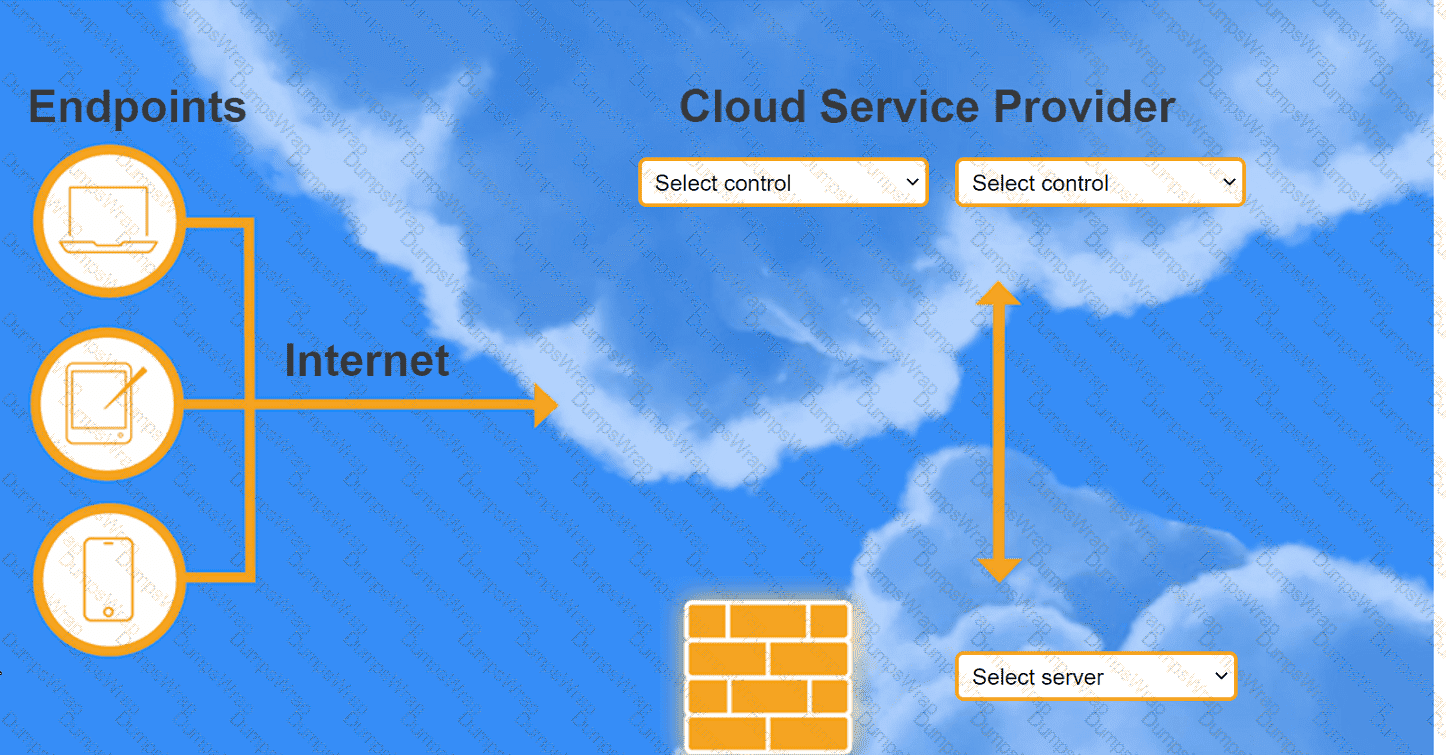
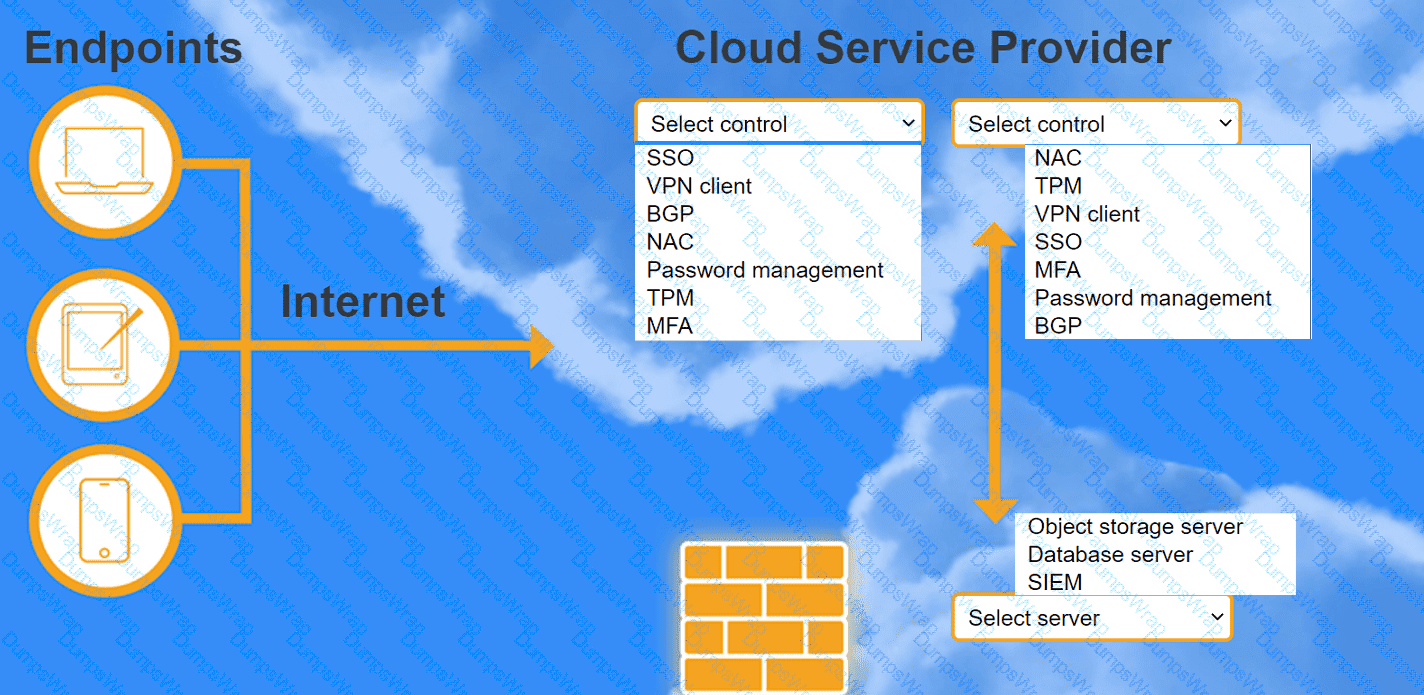
A highly regulated business is required to work remotely, and the risk tolerance is very low. You are tasked with providing an identity solution to the company cloud that includes the following:
secure connectivity that minimizes user login
tracks user activity and monitors for anomalous activity
requires secondary authentication
INSTRUCTIONS
Select controls and servers for the proper control points.
A cloud solution needs to be replaced without interruptions. The replacement process can be completed in phases, but the cost should be kept as low as possible. Which of the
following is the best strategy to implement?
Which of the transfer when comparing a multiregional to a single-region cloud platform design?
A cloud consultant needs to modernize a legacy application that can no longer address user demand and is expensive to maintain. Which of the following is the best migration
strategy?
A security team recently hired multiple interns who all need the same level of access. Which of the following controls should the security team implement to provide access to the
cloud environment with the least amount of overhead?
A cloud security analyst is concerned about security vulnerabilities in publicly available container images. Which of the following is the most appropriate action for the analyst to
recommend?
A company has ten cloud engineers working on different manual cloud deployments. In the past, engineers have had difficulty keeping deployments consistent. Which of the following is the best method to address this issue?
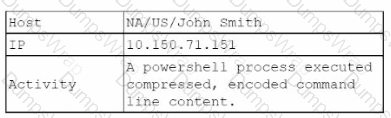
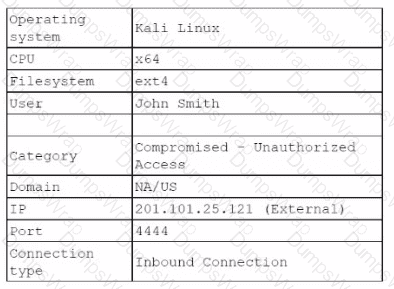
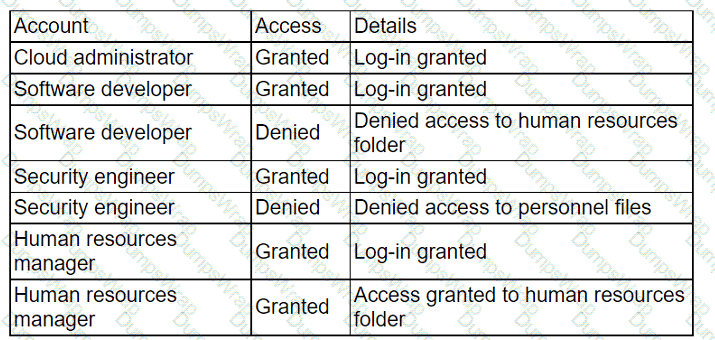
An administrator received a report that company data has been compromised. The compromise occurred on a holiday, and no one in the organization was working. While reviewing
the logs from the holiday, the administrator noted the following details:
The most appropriate action for the cloud security analyst to recommend is using CIS-hardened images. These images are pre-configured by the Center for Internet Security to provide security benchmark standards that help in mitigating vulnerabilities in publicly available container images. References: CompTIA Cloud+ Study Guide (Exam CV0-004) - Chapter on Cloud Security Posture
Which of the following accounts should the administrator disable to prevent a further breach?
Which of the following network protocols is generally used in a NAS environment?
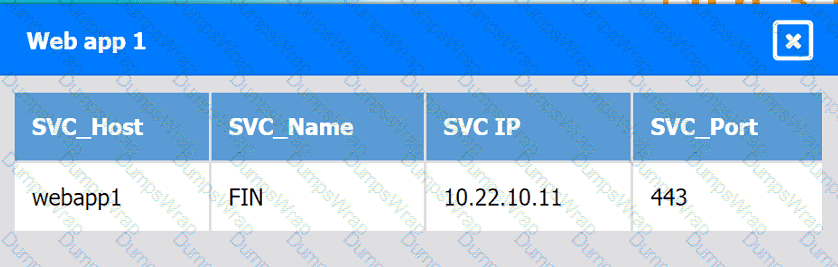
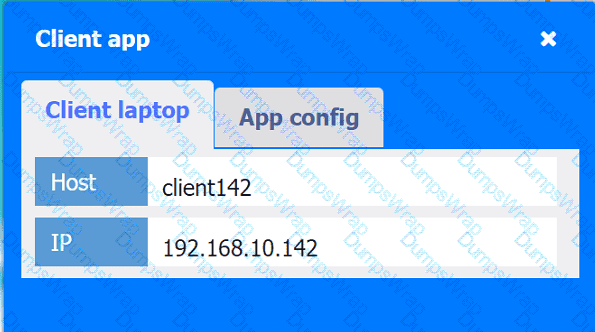
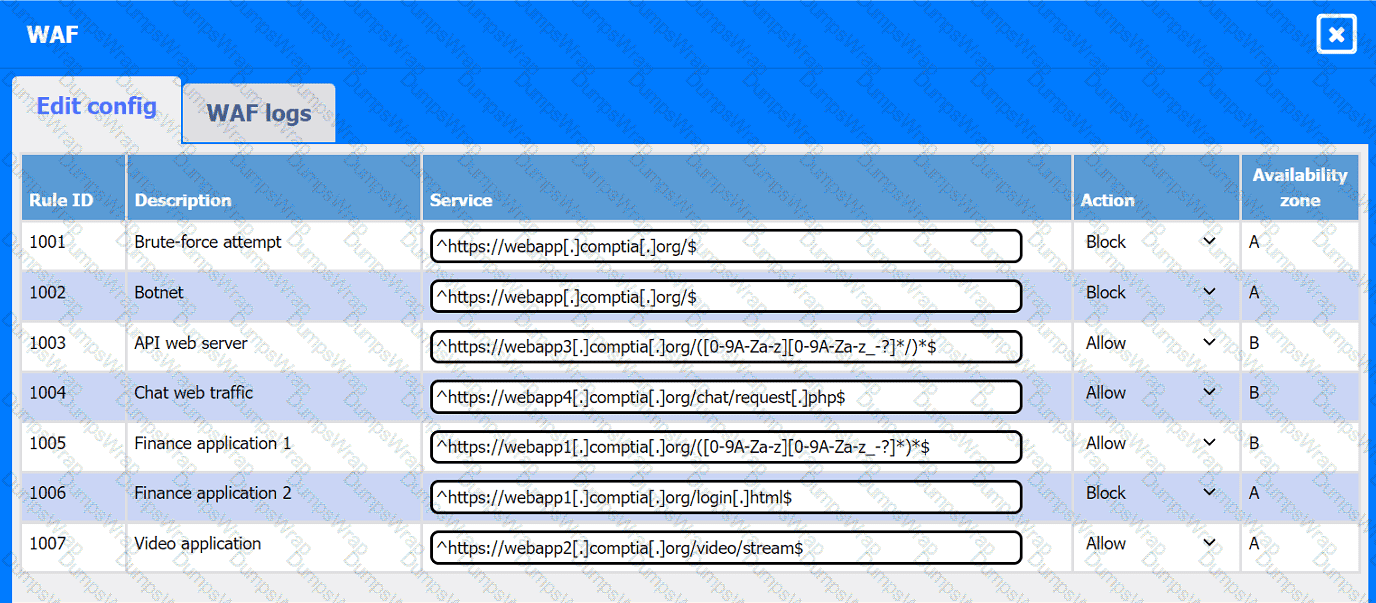
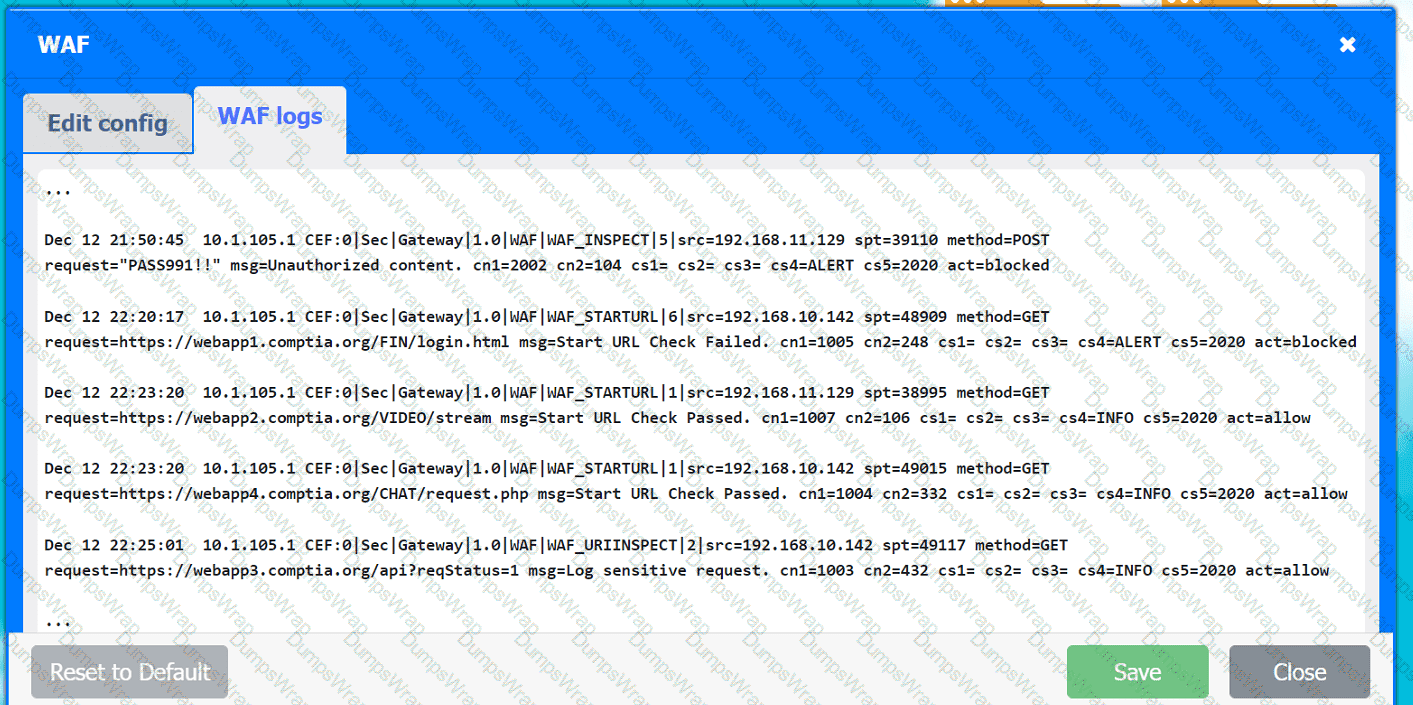
A company hosts various containerized applications for business uses. A client reports that one of its routine business applications fails to load the web-based login prompt hosted in the company cloud.
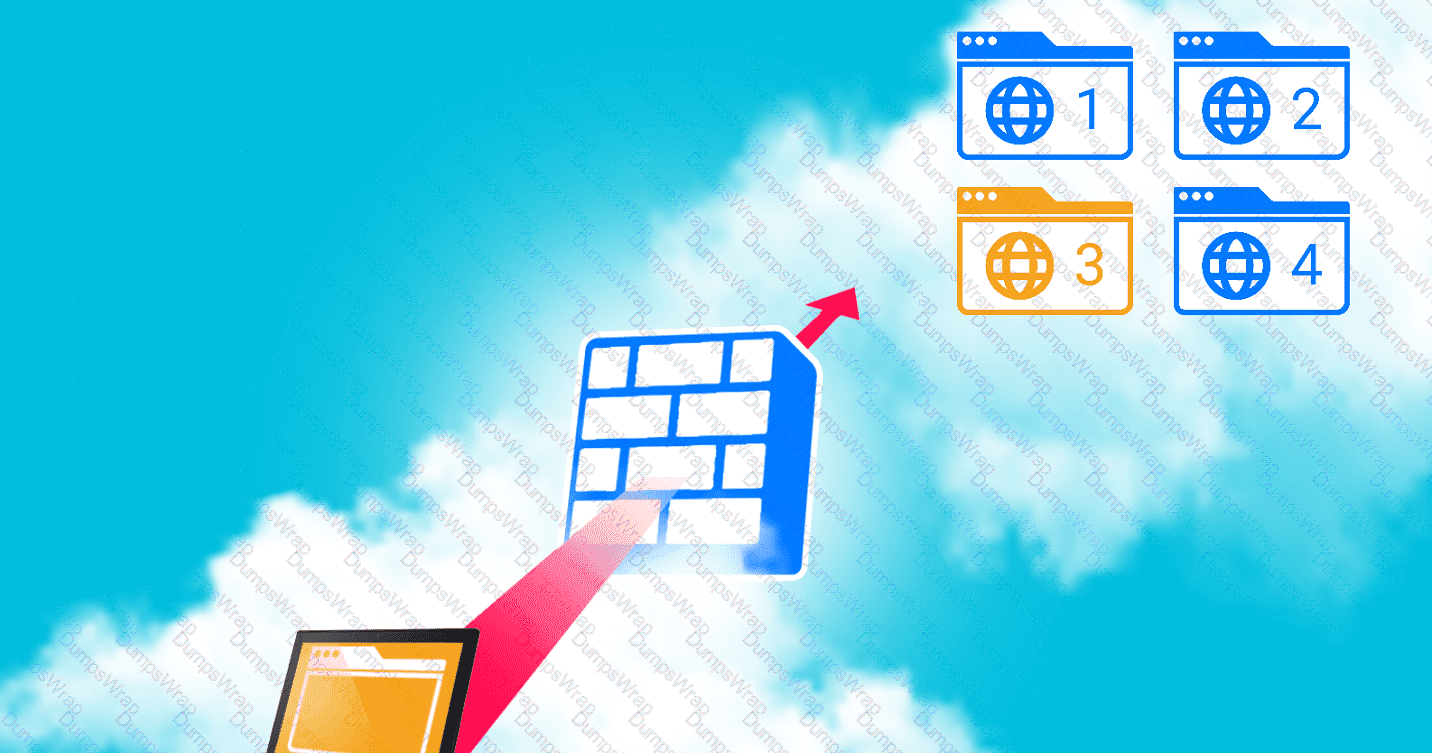
INSTRUCTIONS
Click on each device and resource. Review the configurations, logs, and characteristics of each node in the architecture to diagnose the issue. Then, make the necessary changes to the WAF configuration to remediate the issue.
Web app 1
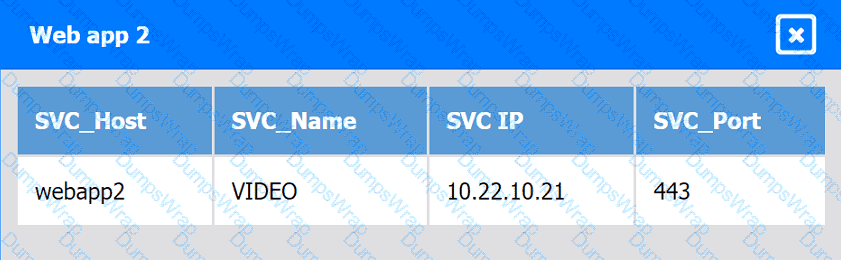
Web app 2
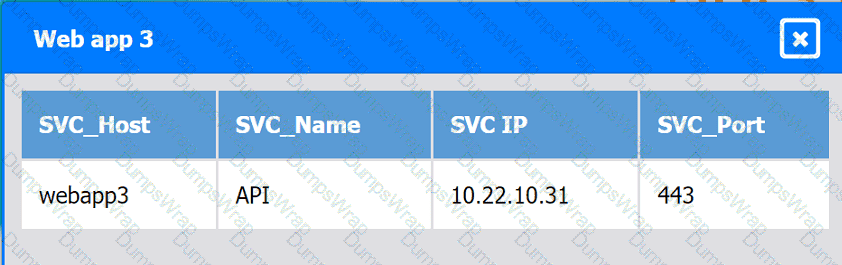
Web app 3
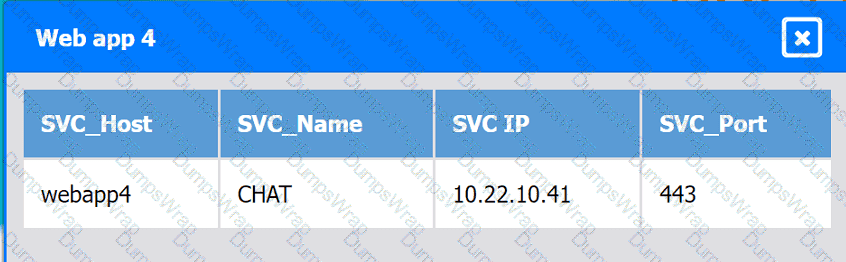
Web app 4
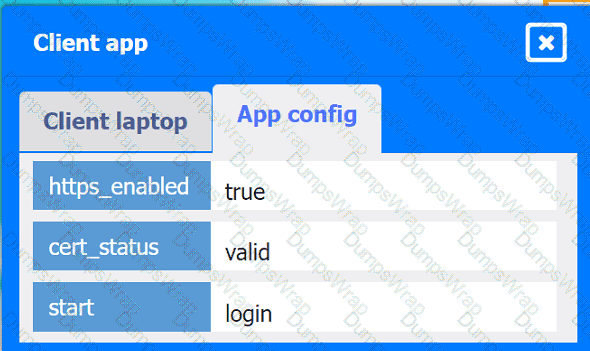
Client app
A company needs to deploy its own code directly in the cloud without provisioning additional infrastructure. Which of the following is the best cloud service model for the company to use?
A security engineer recently discovered a vulnerability in the operating system of the company VMs. The operations team reviews the issue and decides all VMs need to be updated
from version 3.4.0 to 3.5. Which of the following best describes the type of update that will be applied?
An organization is hosting a seminar with eight individuals who need to connect to their own dedicated VM. The technician used the following VM configurations:
IP address: DHCP
NIC: 1Gbps
Network: 10.1.10.0/29
Several users are unable to access their VMs. Which of the following best describes the reason?
An IT manager needs to deploy a cloud solution that meets the following requirements:
. Users must use two authentication methods to access resources.
· Each user must have 10GB of storage space by default.
Which of the following combinations should the manager use to provision these requirements?
An organization wants to ensure its data is protected in the event of a natural disaster. To support this effort, the company has rented a colocation space in another part of the
country. Which of the following disaster recovery practices can be used to best protect the data?
An organization's critical data was exfiltrated from a computer system in a cyberattack. A cloud analyst wants to identify the root cause and is reviewing the following security logs of
a software web application:
"2021/12/18 09:33:12" "10. 34. 32.18" "104. 224. 123. 119" "POST / login.php?u=administrator&p=or%201%20=1"
"2021/12/18 09:33:13" "10.34. 32.18" "104. 224. 123.119" "POST /login. php?u=administrator&p=%27%0A"
"2021/12/18 09:33:14" "10. 34. 32.18" "104. 224. 123. 119" "POST /login. php?u=administrator&p=%26"
"2021/12/18 09:33:17" "10.34. 32.18" "104. 224. 123.119" "POST / login.php?u=administrator&p=%3B"
"2021/12/18 09:33:12" "10.34. 32. 18" "104. 224. 123. 119" "POST / login. php?u=admin&p=or%201%20=1"
"2021/12/18 09:33:19" "10.34.32.18" "104. 224. 123.119" "POST / login. php?u=admin&p=%27%0A"
"2021/12/18 09:33:21" "10. 34. 32.18" "104.224. 123.119" "POST / login. php?u=admin&p=%26"
"2021/12/18 09:33:23" "10. 34. 32.18" "104. 224. 123.119" "POST / login. php?u=admin&p=%3B"
Which of the following types of attacks occurred?
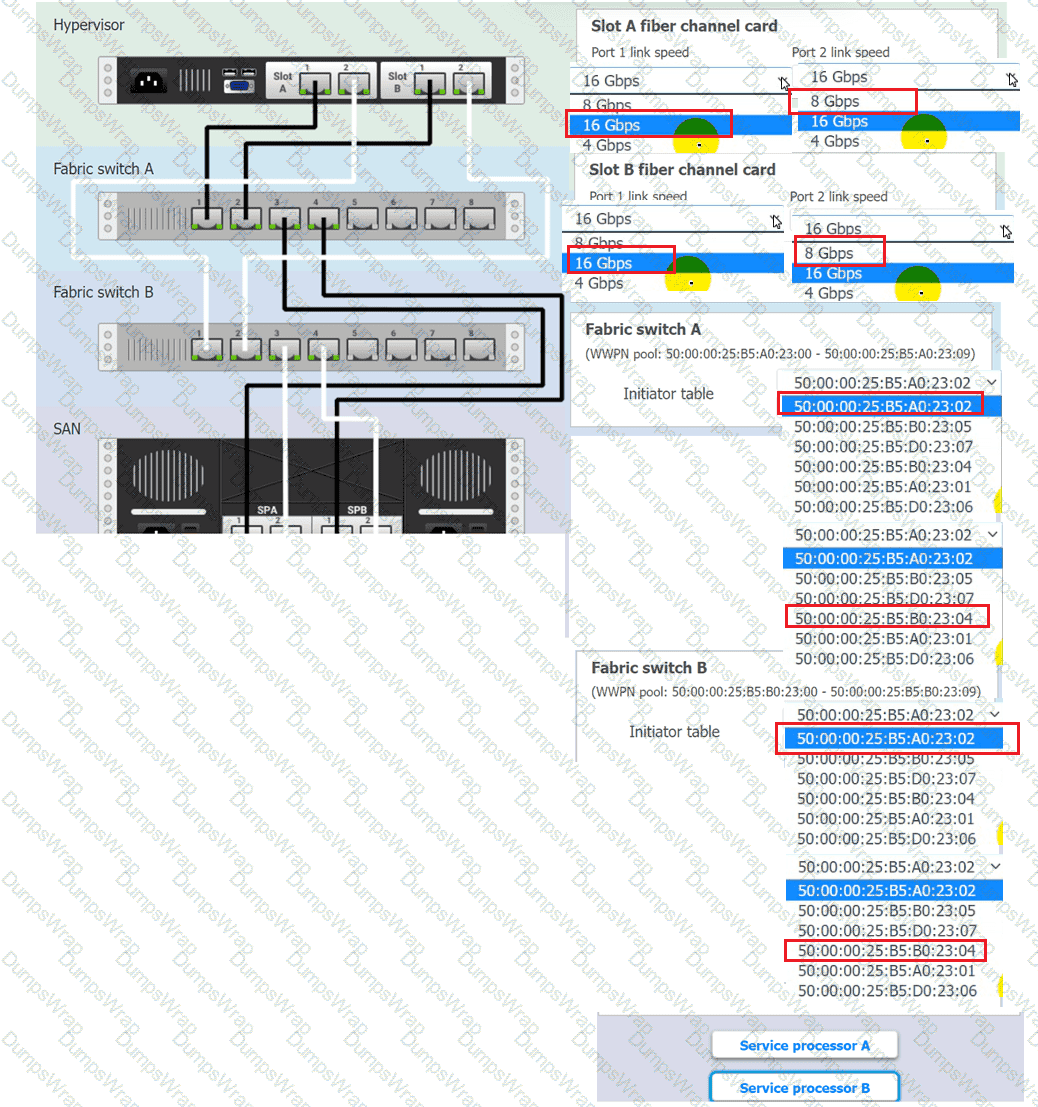
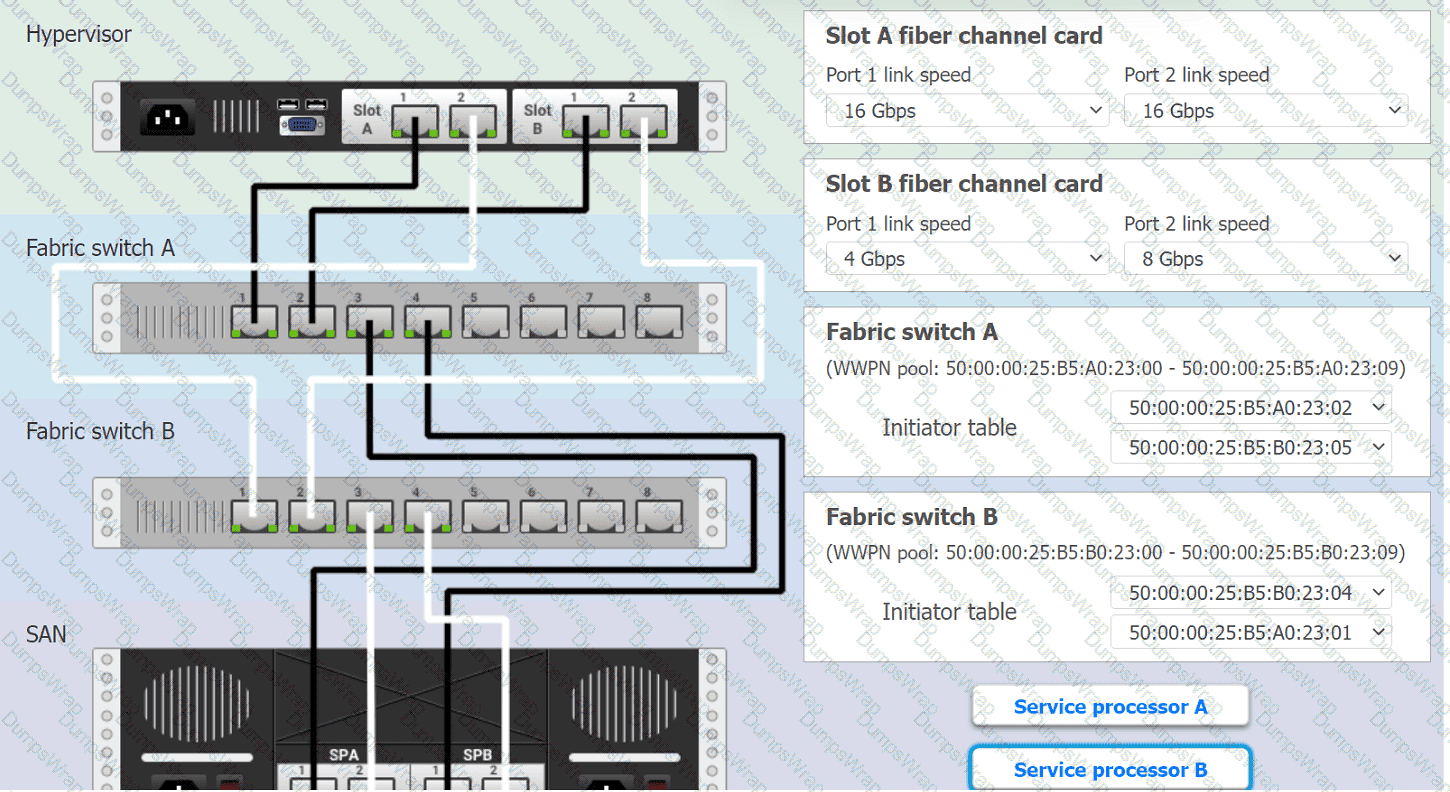
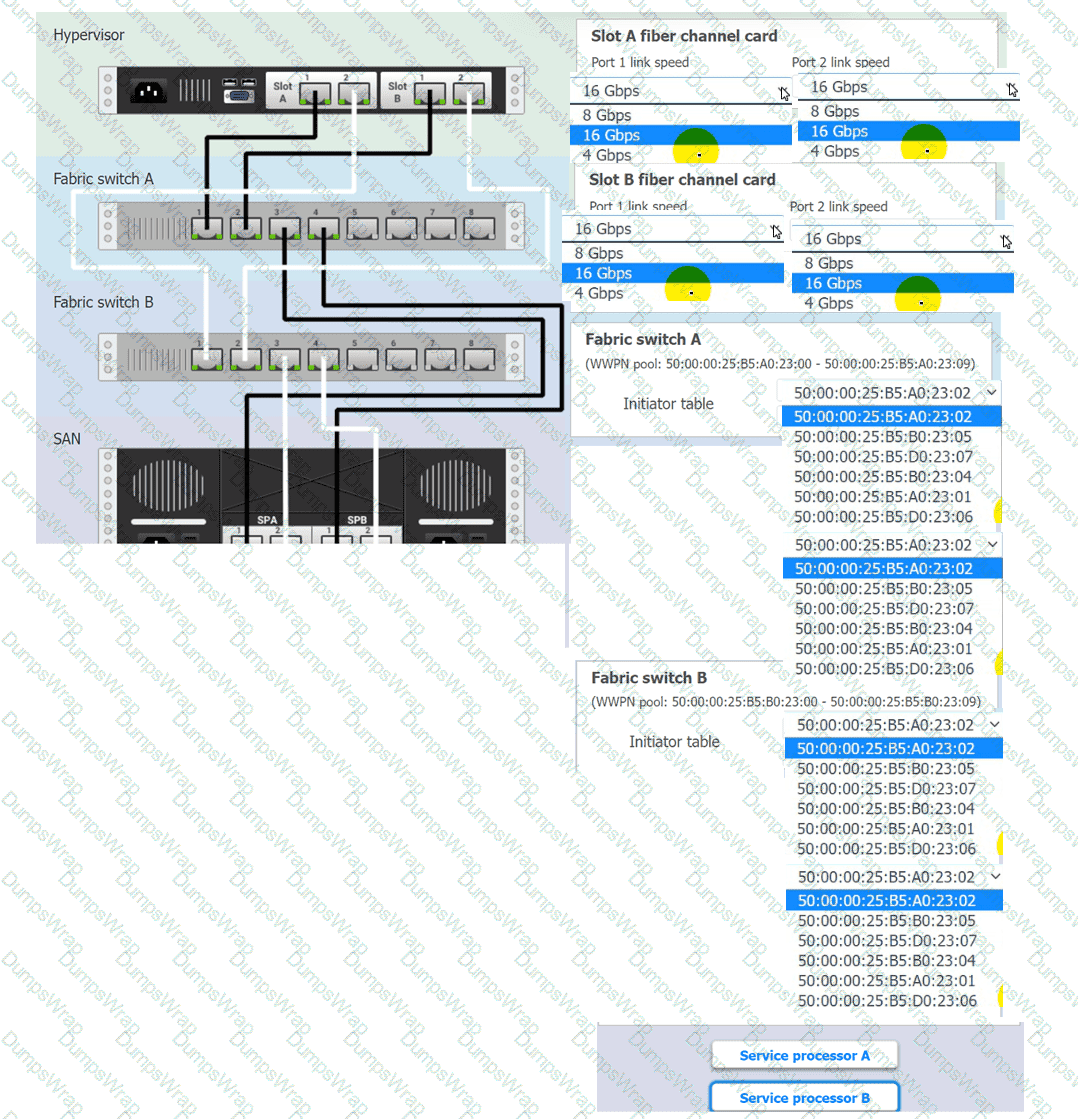
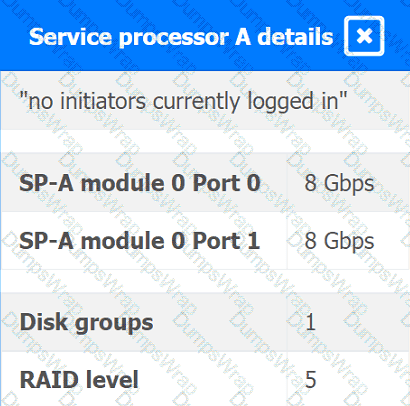
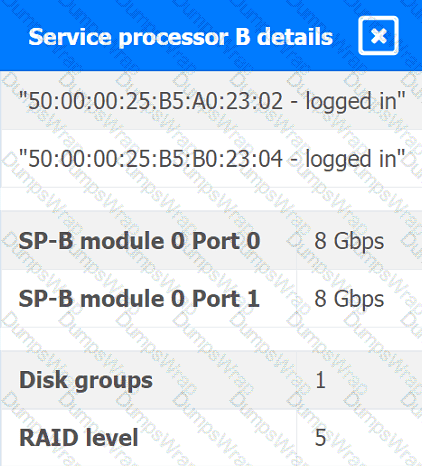
You are a cloud engineer working for a cloud service provider that is responsible for an
IaaS offering.
Your customer, who creates VMs and manages virtual storage, has noticed I/O bandwidth issues and low IOPS (under 9000).
Your manager wants you to verify the proper storage configuration as dictated by your service level agreement (SLA).
The SLA specifies:
. Each SFP on the hypervisor host must be set to the maximum link speed
allowed by the SAN array. . All SAN array disk groups must be configured in a RAID 5.
. The SAN array must be fully configured for redundant fabric paths. . IOPS should not fall below 14000
INSTRUCTIONS
Click on each service processor to review the displayed information. Then click on the drop-down menus to change the settings of each device as necessary to conform to the SLA requirements.
Which of the following should be used on containers to process data and keep the output in files for later review?
A cloud engineer is concerned about command-and-control (C2) communication leaving a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify this type of communication?
A bank informs an administrator that changes must be made to backups for long-term reporting purposes. Which of the following is the most important change the administrator
should make to satisfy these requirements?
A cloud engineer must find the root cause of a recent performance issue. Logs and metrics have been collected and are available. Which of the following is the best way to determine the source of the issue?
Which of the following interfaces is most commonly used for SSDs but not for HDDs?
An IT security team wants to ensure that the correct parties are informed when a specific user account is signed in. Which of the following would most likely allow an administrator to address this concern?
A cloud administrator wants to provision a host with two VMs. The VMs require the following:
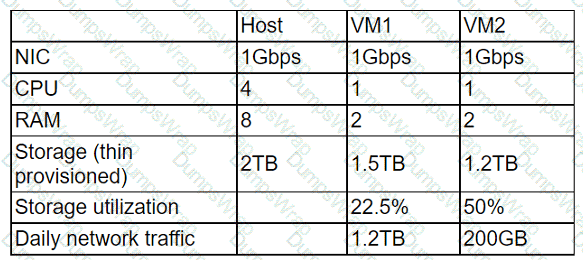
After configuring the servers, the administrator notices that during certain hours of the day, the performance heavily degrades. Which of the following is the best explanation?
Which of the following facilitates the continuous deployment of cloud applications without performing a clean install on each iteration?
A cloud engineer is deploying a cloud solution that will be used on premises with need-to-know access. Which of the following cloud deployment models best meets this
requirement?
A cloud engineer wants to implement a disaster recovery strategy that:
. Is cost-effective.
. Reduces the amount of data loss in case of a disaster.
. Enables recovery with the least amount of downtime.
Which of the following disaster recovery strategies best describes what the cloud engineer wants to achieve?
A cloud engineer needs to integrate a new payment processor with an existing e-commerce website. Which of the following technologies is the best fit for this integration?
A software engineer at a cybersecurity company wants to access the cloud environment. Per company policy, the cloud environment should not be directly accessible via the internet. Which of the following options best describes how the software engineer can access the cloud resources?
A systems administrator is configuring backups on a VM and needs the process to run as quickly as possible, reducing the bandwidth on the network during all times from Monday through Saturday. In the event of data corruption, the management team expects the mean time to recovery to be as low as possible. Which of the following backup methods can the administrator use to accomplish these goals?
A cloud developer is creating a static website that customers will be accessing globally. Which of the following services will help reduce latency?
An organization uses a cloud provider’s specific features to host applications. The organization planned to move to another cloud provider due to rising costs, but moving was not technically feasible. Which of the following best describes this situation?
An IT manager is migrating the production environment to the cloud but needs to keep control of the operating systems, patches, and settings of all resources. Which of the following deployment models will best meet the requirements?
A developer is deploying a new version of a containerized application. The DevOps team wants:
• No disruption
• No performance degradation
* Cost-effective deployment
• Minimal deployment time
Which of the following is the best deployment strategy given the requirements?
A network administrator is budding a site-to-site VPN tunnel from the company's headquarters office 10 the company's public cloud development network. The network administrator confirms the following:
The VPN tunnel is established on the headquarter office firewall.
While inside the office, developers report that they cannot connect to the development network resources.
While outside the office on a client VPN, developers report that they can connect to the development network resources.
The office and the client VPN have different IP subnet ranges.
The firewall flow logs show VPN traffic is reaching the development network from the office.
Which of the following is the next step the next network administrator should take to troubleshoot the VPN tunnel?