CompTIA DataSys+ Certification Exam Questions and Answers
A DBA is reviewing the following logs to determine the current data backup plan for a primary data server:
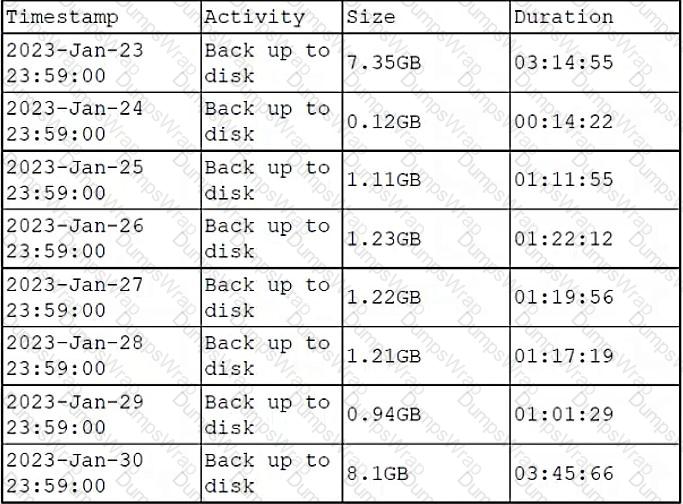
Which of the following best describes this backup plan?
Options:
Monthly full, daily differential
Daily differential
Daily full
Weekly full, daily incremental
Answer:
DExplanation:
The backup plan that best describes the logs is weekly full, daily incremental. This means that a full backup of the entire database is performed once a week, and then only the changes made since the last backup are backed up every day. This can be inferred from the logs by looking at the size and duration of the backups. The full backups are larger and take longer than the incremental backups, and they occur every seven days. The other backup plans do not match the pattern of the logs. References: CompTIA DataSys+ Course Outline, Domain 5.0 Business Continuity, Objective 5.2 Given a scenario, implement backup and restoration of database management systems.
Which of the following is most likely to prevent tampering with server hardware that houses data?
Options:
Biometric locks
Strong password policy
Network firewall
Surveillance cameras
Answer:
AExplanation:
The option that is most likely to prevent tampering with server hardware that houses data is biometric locks. Biometric locks are devices that use biological characteristics, such as fingerprints, facial recognition, iris scan, etc., to control access to a physical location or resource. Biometric locks help prevent tampering with server hardware that houses data by restricting unauthorized entry or theft of the hardware by intruders or attackers. Biometric locks also provide higher security and convenience than other types of locks, such as keys or passwords, which can be lost, stolen, or forgotten. The other options are either not related or not effective for this purpose. For example, a strong password policy is a set of rules or standards for creating and managing passwords for user accounts or systems; a network firewall is a device or software that controls the incoming and outgoing traffic on a network based on a set of rules or policies; surveillance cameras are devices that capture and record video footage of a physical location or resource. References: CompTIA DataSys+ Course Outline, Domain 4.0 Data and Database Security, Objective 4.2 Given a scenario, implement security controls for databases.
Which of the following is part of logical database infrastructure security?
Options:
Surveillance
Biometric access
Perimeter network
Cooling system
Answer:
CExplanation:
The option that is part of logical database infrastructure security is perimeter network. Perimeter network, also known as DMZ (Demilitarized Zone), is a network segment that lies between an internal network and an external network, such as the internet. Perimeter network provides an additional layer of security for the internal network by isolating and protecting the servers or services that are exposed to the external network, such as web servers, email servers, database servers, etc. Perimeter network also helps prevent unauthorized access or attacks from the external network to the internal network by using firewalls, routers, proxies, etc. The other options are either part of physical database infrastructure security or not related to database infrastructure security at all. For example, surveillance is a method of monitoring and recording physical activities or events in a location or resource; biometric access is a device that uses biological characteristics to control access to a physical location or resource; cooling system is a device or system that regulates the temperature and humidity of a location or resource. References: CompTIA DataSys+ Course Outline, Domain 4.0 Data and Database Security, Objective 4.1 Given a scenario, implement database infrastructure security.
A database administrator needs a tool to document and explain the relationships between data in an organization's database. Which of the following is the best tool to accomplish this task?
Options:
Text editor
UML editor
Word processor
SQL query
Answer:
BExplanation:
The best tool for the database administrator to document and explain the relationships between data in an organization’s database is a UML editor. A UML editor is a software application that allows users to create, edit, and visualize diagrams using the Unified Modeling Language (UML). UML is a standard language for modeling software systems and their components, such as classes, objects, relationships, behaviors, etc. UML can also be used to document and explain the relationships between data in an organization’s database by creating entity relationship diagrams (ERDs), which are graphical representations of the entities (tables), attributes (columns), and relationships (constraints) in a database. A UML editor can help the administrator to document and explain the relationships between data by providing features such as drag-and-drop, templates, symbols, validation, etc. The other options are either not suitable or not optimal for this task. For example, a text editor is a software application that allows users to create and edit plain text files; a word processor is a software application that allows users to create and edit text documents; an SQL query is a statement that performs an operation on a database using Structured Query Language (SQL). References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.2 Given a scenario, create database objects using scripting and programming languages.
A developer is designing a table that does not have repeated values. Which of the following indexes should the developer use to prevent duplicate values from being inserted?
Options:
Unique
Single column
Implicit
Composite
Answer:
AExplanation:
The index that the developer should use to prevent duplicate values from being inserted is unique. A unique index is a type of index that enforces the uniqueness of the values in one or more columns of a table. A unique index ensures that no two rows in the table have the same value or combination of values in the indexed columns. A unique index helps to maintain data integrity and avoid data duplication or inconsistency. The other options are either not related or not effective for this purpose. For example, a single column index is a type of index that involves only one column of a table, but it does not prevent duplicate values unless it is also unique; an implicit index is a type of index that is automatically created by the database system when a constraint or a primary key is defined on a column or columns of a table, but it does not prevent duplicate values unless it is also unique; a composite index is a type of index that involves two or more columns of a table, but it does not prevent duplicate values unless it is also unique. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.2 Given a scenario, execute database tasks using scripting and programming languages.
A database is configured to use undo management with temporary undo enabled. An UPDATE is run on the table.
Which of the following describes where the undo is stored?
Options:
In the system global area
In the undo
In the SYSAUX
In the temporary
Answer:
DExplanation:
The correct answer is D. When undo management with temporary undo is enabled, the undo data is stored in the temporary tablespace instead of the undo tablespace. The temporary tablespace is a tablespace that stores temporary data such as sort results or intermediate query results. The undo data is the data that records the changes made by transactions on the database. Undo data is used to roll back transactions in case of errors or failures, or to provide read consistency for concurrent queries. By storing undo data in the temporary tablespace, the database can reduce the space consumption and contention in the undo tablespace, and improve performance and scalability. The other options are either incorrect or irrelevant for this question. For example, the system global area is a memory area that stores information shared by all sessions connected to an instance; the undo tablespace is a tablespace that stores undo data by default; the SYSAUX tablespace is a tablespace that stores auxiliary information for various database features. References: CompTIA DataSys+ Course Outline, Domain 3.0 Database Management and Maintenance, Objective 3.1 Given a scenario, perform common database maintenance tasks.
Which of the following would a database administrator monitor to gauge server health? (Choose two.)
Options:
CPU usage
Memory usage
Transaction logs
Network sniffer
Domain controllers
Firewall traffic
Answer:
A, BExplanation:
The two factors that the database administrator should monitor to gauge server health are CPU usage and memory usage. CPU usage is the percentage of time that the processor (CPU) of the server is busy executing instructions or processes. CPU usage indicates how much workload the server can handle and how fast it can process requests. High CPU usage may affect the performance or availability of the server and cause delays or errors. Memory usage is the amount of physical memory (RAM) or virtual memory (swap space) that the server uses to store data or run applications. Memory usage indicates how much space the server has to store temporary or intermediate data or results. High memory usage may affect the performance or availability of the server and cause swapping or paging. The other options are either not relevant or not direct indicators of server health. For example, transaction logs are files that record the changes made by transactions on the database; network sniffer is a tool that captures and analyzes network traffic; domain controllers are servers that manage user authentication and authorization in a network; firewall traffic is the amount of data that passes through a firewall device or software. References: CompTIA DataSys+ Course Outline, Domain 3.0 Database Management and Maintenance, Objective 3.2 Given a scenario, monitor database performance.
(An analyst in the United States configured a database server so it could be accessed remotely by users in Brazil and Canada. Users in Brazil can connect to the server, but users in Canada cannot connect to the server. Which of the following is the reason for the issue?)
Options:
The perimeter network is rejecting remote connections.
The rule set was configured to allow specific IP addresses.
The firewall was configured to deny all connections.
The server port security is disabled.
Answer:
BExplanation:
The correct answer is B. The rule set was configured to allow specific IP addresses. CompTIA DataSys+ materials emphasize the importance of network security controls, particularly firewall rules and access control lists (ACLs), in regulating remote database access. In this scenario, the database server is reachable by users in Brazil but not by users in Canada, which strongly indicates that access is being selectively permitted rather than globally blocked.
Firewall rule sets are often configured using IP-based allowlists, where only approved IP addresses or IP ranges are permitted to establish a connection. If the analyst allowed the IP address range associated with Brazil but did not include the IP range used by Canadian users, connections from Canada would fail while Brazilian users would still have access. This behavior aligns precisely with selective rule-based access control, a common best practice highlighted in DataSys+ for reducing attack surfaces.
Option A is incorrect because if the perimeter network were rejecting remote connections entirely, users in Brazil would also be unable to connect. Option C is incorrect for the same reason: a firewall rule denying all connections would block access from all locations, not just Canada. Option D, server port security being disabled, would typically prevent all inbound connections to the database service, again affecting all users regardless of geography.
CompTIA DataSys+ stresses that troubleshooting connectivity issues requires identifying whether failures are global or location-specific. Location-specific failures are most commonly caused by misconfigured firewall rules, IP filtering, or regional access restrictions. In database environments that support remote access, DBAs must ensure that firewall rules are consistently applied to all authorized networks.
Therefore, the most accurate and verified explanation is that the rule set was configured to allow specific IP addresses, and the Canadian users’ IP range was not included. This makes option B the correct answer.
(Analysts are writing complex queries across live tables for a database administrator. Which of the following is the best solution for the analysts to implement in order to improve user performance?)
Options:
Creating views to support repeat queries
Removing data redundancy
Modifying the data in the table
Deleting records from the table
Answer:
AExplanation:
The correct answer is A. Creating views to support repeat queries. CompTIA DataSys+ emphasizes that views are an effective way to improve performance, usability, and consistency when users frequently run complex queries against live production tables. A view is a virtual table based on a predefined SQL query that presents data in a simplified and reusable format without physically storing the data.
When analysts run complex queries directly against live tables, it can increase CPU usage, I/O operations, and locking contention, potentially impacting other users and critical workloads. By creating views, the database administrator can encapsulate complex joins, filters, and aggregations into a single logical object. Analysts can then query the view instead of repeatedly executing expensive SQL statements. This reduces query complexity, improves readability, and can lead to more predictable performance. DataSys+ highlights views as a best practice for supporting reporting and analytical workloads while minimizing disruption to transactional systems.
Option B, removing data redundancy, is related to normalization and data integrity, not query performance optimization for analysts. Option C, modifying the data in the table, risks data integrity issues and does not address performance concerns. Option D, deleting records from the table, may reduce table size but is not an appropriate or safe method for improving user query performance and can result in data loss.
CompTIA DataSys+ also notes that views can enhance security by limiting analysts’ access to only the required columns or rows, further protecting live data. In some implementations, indexed or materialized views can offer additional performance benefits for repeated queries.
Therefore, the best solution to improve analyst performance when running complex, repeat queries on live tables is creating views to support repeat queries, making option A the correct and fully verified answer.
Which of the following is the deployment phase in which a DBA ensures the most recent patches are applied to the new database?
Options:
Importing
Upgrading
Provisioning
Modifying
Answer:
BExplanation:
The deployment phase in which a DBA ensures the most recent patches are applied to the new database is upgrading. Upgrading is a process that updates an existing database system or software to a newer version or release that may include new features, enhancements, bug fixes, security patches, etc. Upgrading helps improve the performance, functionality, compatibility, and security of the database system or software. Upgrading can be done manually or automatically using tools or scripts provided by the vendor or developer. Upgrading can also involve testing, backup, migration, or rollback procedures to ensure the quality and reliability of the new version or release. The other options are either different deployment phases or not related to deployment at all. For example, importing is a process that transfers data from one source to another using files or formats; provisioning is a process that allocates resources such as servers, storage, network, etc., for a system or software; modifying is a process that changes existing data or objects in a database using commands or scripts. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.3 Given a scenario, update database systems.
Which of the following is recommended in order to provide encrypted data communication pathways for information as it is transmitted over a network?
Options:
TCP/IP
NFS
SMB
TLS
Answer:
DExplanation:
The option that is recommended in order to provide encrypted data communication pathways for information as it is transmitted over a network is TLS. TLS, or Transport Layer Security, is a protocol that provides secure communication over the internet by encrypting the data using cryptographic algorithms and keys. TLS also provides authentication and integrity by verifying the identity of the parties involved and ensuring that the data has not been altered or tampered with. TLS can be used to protect various types of data, such as web traffic, email, instant messaging, voice over IP, etc. The other options are either not related or not sufficient for this purpose. For example, TCP/IP, or Transmission Control Protocol/Internet Protocol, is a set of protocols that defines how data is transmitted and routed over the internet, but does not provide encryption or security; NFS, or Network File System, is a protocol that allows users to access and share files over a network, but does not provide encryption or security; SMB, or Server Message Block, is a protocol that allows users to access and share files, printers, and other resources over a network, but does not provide encryption or security. References: CompTIA DataSys+ Course Outline, Domain 4.0 Data and Database Security, Objective 4.2 Given a scenario, implement security controls for databases.
A company needs to prepare a document that establishes the responsibilities, metrics, penalties, and other generalities that a provider would have to fulfill for customers to use its platforms.
Which of the following documents meets these requirements?
Options:
DOU
SLA
MOU
SOW
Answer:
BExplanation:
The document that meets these requirements is an SLA. An SLA, or Service Level Agreement, is a contract between a service provider and a customer that defines the scope, quality, and terms of the service delivery. An SLA typically includes the responsibilities, metrics, penalties, and other generalities that a provider would have to fulfill for customers to use its platforms. An SLA also establishes the expectations and obligations of both parties, as well as the methods for measuring and monitoring the service performance. The other options are either different types of documents or not related to service delivery. For example, a DOU, or Data Use Agreement, is a document that governs the sharing and use of data between parties; an MOU, or Memorandum of Understanding, is a document that expresses a mutual agreement or intention between parties; a SOW, or Statement of Work, is a document that describes the specific tasks and deliverables of a project or contract. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.4 Given a scenario, implement service level agreements.
Which of the following is a reason to create a stored procedure?
Options:
To minimize storage space
To improve performance
To bypass case sensitivity requirements
To give control of the query logic to the user
Answer:
BExplanation:
A reason to create a stored procedure is to improve performance. A stored procedure is a set of SQL statements or commands that are stored and compiled in the database server, and can be executed by name or by a trigger. A stored procedure can improve performance by reducing the network traffic between the client and the server, as only the name or the parameters of the stored procedure need to be sent, rather than the entire SQL code. A stored procedure can also improve performance by reusing the same execution plan, as the stored procedure is compiled only once and cached in the server memory. The other options are either not true or not relevant for this purpose. For example, a stored procedure does not necessarily minimize storage space, as it still occupies space in the database server; a stored procedure does not bypass case sensitivity requirements, as it still follows the rules of the database system; a stored procedure does not give control of the query logic to the user, as it is defined and maintained by the database administrator or developer. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.2 Given a scenario, create database objects using scripting and programming languages.
A database administrator needs to provide access to data from two different tables to multiple group users in order to facilitate ongoing reporting. However, some columns in each table are restricted, and users should not be able to see the values in these columns.
Which of the following is the best action for the administrator to take?
Options:
Create a stored procedure.
Create a view.
Create a csv export.
Create a trigger.
Answer:
BExplanation:
The best action for the administrator to take is to create a view. A view is a virtual table that shows a subset of data from one or more tables. The administrator can use a view to provide access to data from two different tables to multiple group users without exposing the restricted columns. The view can also simplify the queries and improve the performance of the reporting process. The other options are either not suitable for this scenario or do not address the requirement of hiding some columns from users. For example, creating a stored procedure would require additional coding and execution, creating a csv export would create a static file that may not reflect the latest data changes, and creating a trigger would perform an action in response to an event rather than provide access to data. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.2 Given a scenario, create database objects using scripting and programming languages.
A database professional is considering denormalizing a database. Which of the following documents should be used to analyze the database's structure?
Options:
SOP
Data dictionaries
UML diaqrams
ERD
Answer:
DExplanation:
The document that should be used to analyze the database’s structure is an ERD. An ERD, or Entity Relationship Diagram, is a graphical representation of the entities (tables), attributes (columns), and relationships (constraints) in a database. An ERD helps to visualize the structure and design of the database, as well as the dependencies and associations among the tables. An ERD can also help to evaluate the level of normalization of the database, which is a process that organizes data into tables and columns to reduce redundancy and improve consistency. By using an ERD, a database professional can consider denormalizing a database, which is a process that introduces some redundancy or duplication of data to improve performance or simplify queries. The other options are either different types of documents or not related to the database’s structure. For example, an SOP, or Standard Operating Procedure, is a document that describes the steps and procedures for performing a specific task or operation; a data dictionary is a document that describes the metadata (information about data) of a database; a UML diagram is a graphical representation of a software system or its components using the Unified Modeling Language (UML). References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.2 Given a scenario, create database objects using scripting and programming languages.
Which of the following is a typical instruction that is found on a Linux command-line script and represents a system shell?
Options:
/bin/bash
#/bin/shell
>/bin/sh
#!/bin/bash
Answer:
DExplanation:
The instruction that is found on a Linux command-line script and represents a system shell is #!/bin/bash. This instruction is called a shebang or a hashbang, and it indicates the interpreter that should be used to execute the script. In this case, the interpreter is /bin/bash, which is the path to the bash shell, a common system shell for Linux. A system shell is a program that provides an interface for users to interact with the operating system, either through commands or scripts. A system shell can also perform various tasks, such as file management, process control, variable assignment, etc. The other options are either incorrect or not typical for this purpose. For example, /bin/bash is the path to the bash shell, but it does not indicate the interpreter for the script; #/bin/shell is not a valid shebang or a path to a system shell; >/bin/sh is a redirection operator followed by a path to a system shell, but it does not indicate the interpreter for the script. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.2 Given a scenario, create database objects using scripting and programming languages.
(Which of the following types of scripting can be executed on a web browser?)
Options:
Server-side
PowerShell
Client-side
Command-line
Answer:
CExplanation:
The correct answer is C. Client-side. CompTIA DataSys+ explains that client-side scripting refers to code that is executed directly within the user’s web browser, rather than on a backend server or operating system shell. The most common and widely recognized client-side scripting language is JavaScript, which runs natively in modern web browsers and is used to enhance interactivity, validate input, and dynamically update content on web pages.
Client-side scripts execute after a web page is delivered to the user’s browser. This allows for immediate feedback, such as form validation, dynamic content updates, and interactive user interfaces, without requiring a round trip to the server. DataSys+ highlights client-side scripting as an important concept when discussing web applications that interact with databases, particularly because improper client-side controls can introduce security risks if not reinforced by server-side validation.
Option A, server-side scripting, runs on the web server rather than in the browser. Examples include PHP, Python, Ruby, and server-side JavaScript (such as Node.js). These scripts handle tasks like database queries, authentication, and business logic and are never executed in the browser itself. Option B, PowerShell, is a scripting and automation language used primarily in Windows environments for system and database administration tasks and cannot run inside a web browser. Option D, command-line scripting, refers to scripts executed in a terminal or shell environment, not within a browser context.
CompTIA DataSys+ emphasizes the distinction between client-side and server-side execution models because of their impact on performance, security, and data handling. Understanding where code executes is critical for protecting databases from exposure and enforcing proper validation controls.
Therefore, the type of scripting that can be executed in a web browser is client-side scripting, making option C the correct and fully verified answer.
Which of the following computer services associates IP network addresses with text-based names in order to facilitate identification and connectivity?
Options:
LDAP
NTP
DHCP
IDNS
Answer:
DExplanation:
The computer service that associates IP network addresses with text-based names in order to facilitate identification and connectivity is IDNS. IDNS, or Internet Domain Name System (DNS), is a service that translates domain names into IP addresses and vice versa. Domain names are human-readable names that identify websites or devices on the internet, such as or IP addresses are numerical identifiers that locate websites or devices on the internet, such as 104.18.26.46 or 142.250.72.238. IDNS helps users to access websites or devices using domain names instead of IP addresses, which are easier to remember and type. IDNS also helps administrators to manage websites or devices using domain names instead of IP addresses, which are more flexible and scalable. The other options are either different computer services or not related to IP network addresses or text-based names at all. For example, LDAP, or Lightweight Directory Access Protocol, is a service that provides access to directory information such as users, groups, or devices on a network; NTP, or Network Time Protocol, is a service that synchronizes the clocks of computers or devices on a network; DHCP, or Dynamic Host Configuration Protocol, is a service that assigns IP addresses and other network configuration parameters to computers or devices on a network. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.1 Given a scenario, select an appropriate database deployment method.
(Which of the following best describes the function of a wildcard in the WHERE clause?)
Options:
An exact match is not possible in a CREATE statement.
An exact match is necessary in a SELECT statement.
An exact match is not possible in a SELECT statement.
An exact match is necessary in a CREATE statement.
Answer:
CExplanation:
The correct answer is C. An exact match is not possible in a SELECT statement. CompTIA DataSys+ documentation explains that wildcards are used in SQL primarily within the WHERE clause of a SELECT statement to enable pattern matching rather than exact value matching. Wildcards such as % and _ are commonly used with the LIKE operator to search for partial strings or variable patterns in character-based data.
In practical database usage, wildcards allow analysts and administrators to retrieve records when the full or exact value is unknown or unnecessary. For example, searching for all patient records with last names starting with “Mac%” or all email addresses ending in “@example.com” requires pattern-based matching. In these cases, an exact match is explicitly not required, which is the core purpose of wildcards in SQL queries.
Option A and D incorrectly reference the CREATE statement. Wildcards are not relevant to CREATE statements, which are used for defining database objects such as tables, indexes, or views. These statements require explicit definitions and do not support wildcard-based matching logic. Option B is also incorrect because a SELECT statement does not always require an exact match; this is precisely why wildcards exist and are heavily used in querying operations.
CompTIA DataSys+ emphasizes that understanding query flexibility is essential for data retrieval and reporting. Wildcards enhance query usability and efficiency by allowing broader result sets without complex logic or multiple conditions. They are particularly valuable in analytical, reporting, and troubleshooting scenarios where partial data exploration is required.
Therefore, the best description of the function of a wildcard in the WHERE clause is that it allows queries where an exact match is not required, making option C the correct and fully aligned answer according to CompTIA DataSys+ principles.
(A database administrator wants to create a database that does not have a predefined schema. Which of the following tools should the administrator use to create this type of database? Select two.)
Options:
PostgreSQL
MariaDB
MySQL
SQL Server
MongoDB
Cosmos
Answer:
E, FExplanation:
The correct answers are E. MongoDB and F. Cosmos. CompTIA DataSys+ clearly differentiates between relational databases, which require predefined schemas, and non-relational (NoSQL) databases, which support flexible or schema-less data models. A schema-less database allows data to be stored without enforcing a fixed table structure, making it ideal for rapidly changing data requirements, unstructured data, or applications with evolving schemas.
MongoDB is a document-oriented NoSQL database that stores data in flexible, JSON-like documents. Each document in a MongoDB collection can have a different structure, allowing developers to add or remove fields without modifying a predefined schema. DataSys+ highlights document stores like MongoDB as well-suited for modern applications that require agility, scalability, and the ability to handle semi-structured or unstructured data.
Cosmos (commonly referring to Azure Cosmos DB) is a globally distributed NoSQL database service that supports multiple data models, including core (SQL) API, MongoDB API, and other non-relational models. It is designed for high availability, horizontal scalability, and schema flexibility. DataSys+ includes cloud-based NoSQL platforms such as Cosmos as examples of databases that do not enforce rigid schemas.
Options A, B, C, and D—PostgreSQL, MariaDB, MySQL, and SQL Server—are all relational database management systems (RDBMS). These systems require predefined schemas with fixed table definitions, column data types, and constraints before data can be stored. While some relational systems support limited JSON storage, they are still fundamentally schema-based and do not meet the requirement described in the question.
CompTIA DataSys+ emphasizes selecting database technologies based on data structure and application needs. When schema flexibility is required, NoSQL solutions are preferred. Therefore, the tools best suited for creating a database without a predefined schema are MongoDB and Cosmos, making options E and F the correct and fully verified answers.
A database administrator would like to create a table named XYZ. Which of the following queries should the database administrator use to create the table?
A)
B)
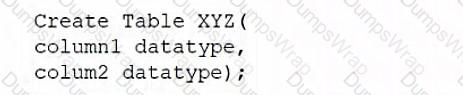
C)
D)
Options:
Option A
Option B
Option C
Option D
Answer:
BExplanation:
The query that the administrator should use to create the table is option B. This query uses the CREATE TABLE statement to define a new table named XYZ with three columns: ID, Name, and Age. Each column has a data type and a constraint, such as NOT NULL, PRIMARY KEY, or CHECK. The other options either have syntax errors, use incorrect keywords, or do not specify the table name or columns correctly. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.1 Given a scenario, identify and apply database structure types.
Which of the following is an advantage of creating indexes?
Options:
To help with space allocation
To provide quick and efficient access to data
To reduce memory
To update the query plan
Answer:
BExplanation:
The advantage of creating indexes is to provide quick and efficient access to data. An index is a data structure that stores the values of one or more columns of a table in a sorted order, along with pointers to the corresponding rows in the table. An index helps to speed up queries that search, filter, sort, or join data based on the indexed columns, as it reduces the number of disk accesses or scans required to locate the desired data. An index also helps to enforce uniqueness or referential integrity constraints on the indexed columns. The other options are either not true or not relevant for this purpose. For example, an index does not help with space allocation, as it consumes additional space in the database; an index does not reduce memory, as it may use memory for caching or buffering purposes; an index does not update the query plan, as it is an input or a factor for the query optimizer to generate the query plan. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.2 Given a scenario, execute database tasks using scripting and programming languages.
Which of the following is the best way to migrate a large data load from one table to another, considering total time and blocking?
Options:
Split the load size into many transactions.
Split the load size in half and run simultaneously.
Batch into small loads and run in parallel.
Batch large loads into one transaction.
Answer:
CExplanation:
The best way to migrate a large data load from one table to another, considering total time and blocking, is to batch into small loads and run in parallel. This means that the large data load is divided into smaller chunks that can be processed simultaneously by multiple threads or processes. This reduces the total time required for the migration and also minimizes the blocking of other operations on the tables involved. The other options are either less efficient or more prone to blocking. For example, splitting the load size into many transactions may increase the overhead and latency of each transaction; splitting the load size in half and running simultaneously may still cause blocking or contention; batching large loads into one transaction may take longer and lock the tables for longer periods. References: CompTIA DataSys+ Course Outline, Domain 3.0 Database Management and Maintenance, Objective 3.3 Given a scenario, migrate data between databases.
An automated script is using common passwords to gain access to a remote system. Which of the following attacks is being performed?
Options:
DoS
Brute-force
SQL injection
Phishing
Answer:
BExplanation:
The attack that is being performed is brute-force. A brute-force attack is a type of attack that tries to guess a password or a key by systematically trying all possible combinations of characters or values until the correct one is found. A brute-force attack can use common passwords, such as “123456”, “password”, or “qwerty”, as well as dictionaries, word lists, or patterns to speed up the process. A brute-force attack can target a remote system, such as a web server, an email account, or a network device, and gain unauthorized access to its data or resources. The other options are either different types of attacks or not related to password guessing. For example, a DoS, or Denial-of-Service, attack is a type of attack that floods a system with requests or traffic to overwhelm its capacity and prevent legitimate users from accessing it; an SQL injection attack is a type of attack that inserts malicious SQL statements into an input field or parameter of a web application to manipulate or compromise the underlying database; a phishing attack is a type of attack that sends fraudulent emails or messages that appear to come from a trusted source to trick users into revealing their personal or financial information. References: CompTIA DataSys+ Course Outline, Domain 4.0 Data and Database Security, Objective 4.4 Given a scenario, identify common types of attacks against databases.
Which of the following best describes a collection of data that shares the same properties or attributes?
Options:
Relation set
ER model
Entity set
Tuples
Answer:
CExplanation:
The option that best describes a collection of data that shares the same properties or attributes is entity set. An entity set is a term used in the entity-relationship (ER) model, which is a conceptual model for designing and representing databases. An entity set is a collection of entities that have the same type or characteristics, such as students, courses, products, etc. An entity is an object or thing that can be identified and distinguished from others, such as a specific student, course, product, etc. An entity set can have one or more attributes that describe the properties or features of the entities, such as name, age, price, etc. An entity set can also have one or more relationships with other entity sets that define how the entities are associated or connected, such as enrolled, taught by, purchased by, etc. The other options are either different terms or not related to the ER model at all. For example, relation set is a term used in the relational model, which is a logical model for implementing and manipulating databases; ER model is a term used to refer to the entity-relationship model itself; tuples are rows or records in a table or relation. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.1 Given a scenario, identify common database types.
A database administrator is conducting a stress test and providing feedback to a team that is developing an application that uses the Entity Framework. Which of the following explains the approach the administrator should use when conducting the stress test?
Options:
Capture business logic, check the performance of codes, and report findings.
Check the clustered and non-clustered indexes, and report findings.
Review application tables and columns, and report findings.
Write queries directly into the database and report findings.
Answer:
AExplanation:
The approach that the administrator should use when conducting the stress test is to capture business logic, check the performance of codes, and report findings. This will help the administrator to evaluate how well the application handles high volumes of data and transactions, identify any bottlenecks or errors in the code, and provide feedback to the development team on how to improve the application’s efficiency and reliability. The other options are either too narrow or too broad in scope, and do not address the specific needs of an application that uses the Entity Framework. References: CompTIA DataSys+ Course Outline, Domain 4.0 Data and Database Security, Objective 4.3 Given a scenario, monitor database performance and security.
A database administrator set up a connection for a SQL Server instance for a new user, but the administrator is unable to connect using the user's workstation. Which of the following is the most likely cause of the issue?
Options:
The SQL Server codes are performing badly.
The SQL Server has not been tested properly.
The SQL Server ports to the main machine are closed.
The SQL Server has many concurrent users.
Answer:
CExplanation:
The most likely cause of the issue is that the SQL Server ports to the main machine are closed. SQL Server uses TCP/IP ports to communicate with clients and other servers. If these ports are blocked by a firewall or other network device, the connection will fail. The administrator should check the port configuration on both the server and the user’s workstation, and make sure that they are open and match the expected values. The other options are either unlikely or unrelated to the issue. For example, the SQL Server codes performing badly or having many concurrent users may affect the performance or availability of the server, but not prevent the connection entirely; the SQL Server not being tested properly may cause errors or bugs in the functionality or security of the server, but not affect the connection unless there is a configuration problem. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.3 Given a scenario, troubleshoot common database deployment issues.
(Which of the following statements is TRUNCATE an example of?)
Options:
DDL statement
DCL statement
MCL statement
DML statement
Answer:
AExplanation:
The correct answer is A. DDL statement. CompTIA DataSys+ clearly classifies the TRUNCATE statement as a Data Definition Language (DDL) operation because it affects the structure and allocation of database objects rather than manipulating individual rows in a transactional manner.
TRUNCATE is used to quickly remove all rows from a table while preserving the table structure itself. Unlike DELETE, which is a Data Manipulation Language (DML) statement that removes rows one by one and can be rolled back in many database systems, TRUNCATE operates by deallocating data pages. This makes it significantly faster and more efficient for clearing large tables, but also more destructive in nature. DataSys+ emphasizes that DDL operations are typically auto-committed, meaning they cannot be rolled back once executed in most implementations.
Option D, DML, is incorrect because DML statements (such as SELECT, INSERT, UPDATE, and DELETE) work at the row level and are designed for routine data manipulation within existing structures. TRUNCATE does not qualify because it bypasses row-level logging and transactional controls. Option B, DCL (Data Control Language), is used for permission and access management (e.g., GRANT, REVOKE) and has no role in data removal. Option C, MCL, is not a recognized SQL command category and is therefore invalid.
CompTIA DataSys+ materials stress the importance of understanding SQL command categories, particularly the risks associated with DDL statements. Because TRUNCATE is fast, non-transactional, and irreversible in most cases, it should be used cautiously and typically only by administrators. Its classification as DDL is essential knowledge for exam objectives related to database operations, data safety, and change management.
Therefore, the correct and verified classification of TRUNCATE is DDL, making option A the correct answer.
Which of the following commands is part of DDL?
Options:
UPDATE
GRANT
CREATE
INSERT
Answer:
CExplanation:
The command that is part of DDL is CREATE. CREATE is a SQL command that belongs to the category of DDL, or Data Definition Language. DDL is a subset of SQL commands that are used to define or modify the structure or schema of a database, such as tables, columns, constraints, indexes, views, etc. CREATE is a DDL command that is used to create a new object in a database, such as a table, column, constraint, index, view, etc. For example, the following statement uses the CREATE command to create a new table called employee with four columns:
CREATE TABLE employee (
emp_id INT PRIMARY KEY,
emp_name VARCHAR(50) NOT NULL,
emp_dept VARCHAR(20),
emp_salary DECIMAL(10,2)
);
Copy
The other options are either part of different categories of SQL commands or not SQL commands at all. For example, UPDATE is a SQL command that belongs to the category of DML, or Data Manipulation Language. DML is a subset of SQL commands that are used to manipulate or modify the data or content of a database, such as inserting, updating, deleting, or selecting data. GRANT is a SQL command that belongs to the category of DCL, or Data Control Language. DCL is a subset of SQL commands that are used to control or manage the access or permissions of users or roles on a database, such as granting or revoking privileges or roles. INSERT is a SQL command that belongs to the category of DML, or Data Manipulation Language. INSERT is a DML command that is used to insert new data into a table. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.2 Given a scenario, execute database tasks using scripting and programming languages.
Which of the following can be used to protect physical database appliances from damage in a server room? (Choose two.)
Options:
Biometric access systems
Database control systems
Fire suppression systems
Camera systems
Key card systems
Cooling systems
Answer:
C, FExplanation:
The two options that can be used to protect physical database appliances from damage in a server room are fire suppression systems and cooling systems. Fire suppression systems are systems that detect and extinguish fires in a server room using water, gas, foam, or other agents. Fire suppression systems help prevent damage to physical database appliances caused by fire hazards such as overheating, electrical faults, or flammable materials. Cooling systems are systems that regulate the temperature and humidity in a server room using fans, air conditioners, chillers, or other devices. Cooling systems help prevent damage to physical database appliances caused by excessive heat or moisture that may affect their performance or lifespan. The other options are either not related or not effective for this purpose. For example, biometric access systems, camera systems, and key card systems are systems that control the access to a server room using fingerprints, facial recognition, video surveillance, or magnetic cards; these systems help prevent unauthorized entry or theft of physical database appliances, but not damage caused by environmental factors; database control systems are systems that manage the functionality and security of databases using software tools or commands; these systems help protect logical database appliances from errors or attacks, but not physical damage caused by environmental factors. References: CompTIA DataSys+ Course Outline, Domain 5.0 Business Continuity, Objective 5.4 Given a scenario, implement disaster recovery methods.
Which of the following have data manipulation and procedural scripting power? (Choose two.)
Options:
PQL
PL/SQL
Advanced
SQL
SQL
T-SQL
Answer:
B, FExplanation:
The two options that have data manipulation and procedural scripting power are PL/SQL and T-SQL. PL/SQL, or Procedural Language/Structured Query Language, is an extension of SQL that adds procedural features to SQL for Oracle databases. PL/SQL allows users to create and execute stored procedures, functions, triggers, packages, etc., using variables, loops, conditions, exceptions, etc., in addition to SQL commands. PL/SQL helps improve the performance, functionality, modularity, and security of SQL queries and applications. T-SQL, or Transact-SQL, is an extension of SQL that adds procedural features to SQL for Microsoft SQL Server databases. T-SQL allows users to create and execute stored procedures, functions, triggers, etc., using variables, loops, conditions, exceptions, etc., in addition to SQL commands. T-SQL helps improve the performance, functionality, modularity, and security of SQL queries and applications. The other options are either not related or not having both data manipulation and procedural scripting power. For example, PQL, or Power Query Language, is a data analysis and transformation language for Microsoft Power BI and Excel; Advanced SQL is a term that refers to the advanced features or techniques of SQL, such as subqueries, joins, aggregations, etc.; SQL, or Structured Query Language, is a standard language for manipulating and querying data in relational databases, but it does not have procedural features. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.2 Given a scenario, execute database tasks using scripting and programming languages.
Which of the following tools is used for natively running a Linux system in Windows?
Options:
WSL
[Remote Desktop Protocol
SSH
ITelnet
Answer:
AExplanation:
The tool that is used for natively running a Linux system in Windows is WSL. WSL, or Windows Subsystem for Linux, is a feature that allows users to run a Linux system natively on Windows 10 or Windows Server. WSL enables users to install and use various Linux distributions, such as Ubuntu, Debian, Fedora, etc., and run Linux commands, tools, applications, etc., without requiring a virtual machine or a dual-boot setup. WSL also provides users with interoperability and integration between Linux and Windows, such as file system access, network communication, process management, etc. WSL is useful for users who want to use Linux features or functionalities on Windows, such as development, testing, scripting, etc. The other options are either different tools or not related to running a Linux system in Windows at all. For example, Remote Desktop Protocol (RDP) is a protocol that allows users to remotely access and control another computer or device over a network; SSH, or Secure Shell, is a protocol that allows users to securely connect and communicate with another computer or device over a network; Telnet is a protocol that allows users to interact with another computer or device over a network using a text-based interface. References: CompTIA DataSys+ Course Outline, Domain 2.0 Database Deployment, Objective 2.2 Given a scenario, create database objects using scripting and programming languages.
Which of the following constraints is used to enforce referential integrity?
Options:
Surrogate key
Foreign key
Unique key
Primary key
Answer:
BExplanation:
The constraint that is used to enforce referential integrity is foreign key. A foreign key is a column or a set of columns in a table that references the primary key of another table. A primary key is a column or a set of columns in a table that uniquely identifies each row in the table. Referential integrity is a rule that ensures that the values in the foreign key column match the values in the primary key column of the referenced table. Referential integrity helps maintain the consistency and accuracy of the data across related tables. The other options are either different types of constraints or not related to referential integrity at all. For example, a surrogate key is a column that is artificially generated to serve as a primary key, such as an auto-increment number or a GUID (Globally Unique Identifier); a unique key is a column or a set of columns in a table that uniquely identifies each row in the table, but it can have null values unlike a primary key; there is no such constraint as TID. References: CompTIA DataSys+ Course Outline, Domain 1.0 Database Fundamentals, Objective 1.2 Given a scenario, execute database tasks using scripting and programming languages.
(Which of the following are ORM tools? Select two.)
Options:
PL/SQL
XML
Entity Framework
T-SQL
Hibernate
PHP
Answer:
C, EExplanation:
The correct answers are C. Entity Framework and E. Hibernate. CompTIA DataSys+ defines Object-Relational Mapping (ORM) tools as software frameworks that allow developers to interact with relational databases using object-oriented programming concepts instead of writing raw SQL queries. ORM tools map database tables to application objects, rows to object instances, and columns to object attributes, simplifying database access and improving developer productivity.
Entity Framework is a widely used ORM tool in the Microsoft ecosystem, commonly paired with .NET applications. It enables developers to define data models in code and allows the framework to automatically generate SQL queries, manage relationships, and handle CRUD (Create, Read, Update, Delete) operations. DataSys+ highlights ORM tools like Entity Framework as a way to reduce repetitive SQL coding while maintaining consistency and abstraction between application logic and the database layer.
Hibernate is a popular ORM framework used primarily in Java-based applications. Similar to Entity Framework, Hibernate manages database interactions by mapping Java objects to relational database structures. It handles SQL generation, transaction management, and caching, making it a core example of an ORM solution referenced in DataSys+ learning objectives.
Option A, PL/SQL, and option D, T-SQL, are procedural SQL languages, not ORM tools. They are used to write stored procedures, functions, and scripts that execute directly within the database. Option B, XML, is a data format used for data representation and exchange, not for object-relational mapping. Option F, PHP, is a general-purpose programming language that can use ORM tools but is not itself an ORM framework.
CompTIA DataSys+ emphasizes understanding the distinction between database languages, programming languages, and abstraction frameworks like ORMs. Entity Framework and Hibernate clearly fit the definition of ORM tools by bridging object-oriented applications and relational databases.
Therefore, the correct and fully verified answers are C and E.
(A company’s database was hacked. A security officer conducted an audit and discovered that an attacker used a rainbow table to break into one of the user accounts to access the database. Which of the following is the best immediate response to this attack?)
Options:
Security and awareness training
Implementation of security policies and procedures
Strong passwords
Password hash salting
Answer:
DExplanation:
The correct answer is D. Password hash salting. According to CompTIA DataSys+ objectives, rainbow table attacks specifically target hashed passwords by using precomputed hash values to quickly reverse weak or unsalted hashes back into their original plaintext passwords. If an attacker successfully used a rainbow table, it strongly indicates that the database stored password hashes without proper salting or used weak hashing algorithms.
Password salting is a defensive technique where a unique random value (the salt) is added to each password before hashing. This ensures that even if two users have the same password, their resulting hashes are different. More importantly, salting renders rainbow tables ineffective because the attacker would need to generate a separate rainbow table for every possible salt value, which is computationally impractical. DataSys+ highlights salting as a critical immediate control to protect stored credentials once a password compromise is identified.
Option C, strong passwords, is a preventative control but not the best immediate response. Even strong passwords can be compromised if hashes are unsalted and exposed. Option A, security and awareness training, addresses user behavior but does not mitigate the technical weakness exploited in this attack. Option B, implementing security policies and procedures, is important for long-term governance but does not directly stop rainbow table attacks against existing password hashes.
CompTIA DataSys+ emphasizes that when credential storage mechanisms are compromised, administrators must prioritize cryptographic protections at the database level. This includes salting, using strong hashing algorithms, and forcing credential resets. Among the options provided, password hash salting is the most direct and effective response to prevent the same attack vector from succeeding again.
Therefore, the best immediate response is D. Password hash salting, making it the verified and correct answer aligned with CompTIA DataSys+ guidance.

