CyberArk CDE-CPC Recertification Questions and Answers
Which deployment criteria influences the CyberArk-provided hardening methods that need to be applied to CPM and PSM components?
You want to improve performance on the CPM by restricting accounts for the CYBRWINDAD platform to only the WINDEMEA and WINDEMEA_ADMIN Safes. How do you set this in CyberArk?
What is a requirement when installing the PSM on multiple Privileged Cloud Connector servers?
After the session has ended, where is the default final recording storage located?
Which statements accurately describe the process of LDAP integration with CyberArk Privilege Cloud Standard? (Choose two.)
What is the recommended method to enable load balancing and failover of the CyberArk Identity Connector?
Your customer is using Privilege Cloud Shared Services. What is the correct CyberArk Vault address for this customer?
You have been tasked with deploying a Privilege Cloud PSM for SSH connector When the initial installation has successfully completed, you create and permission several maintenance users to be used for administering the connector.
Which configuration file must be updated to define these maintenance users?
You plan to install the Privilege Cloud Connector on Windows Server 2019 and must leverage your existing RDS Per-user licenses for PSM connections. What must you do?
An end user (external user account) has been removed from the Users tab in CyberArk Identity Administration and tries to log in to the CyberArk Privilege Cloud portal using the correct credentials. What will happen?
Which method can be used to directly authenticate users to PSM for SSH? (Choose three.)
Your customer recently merged with a smaller organization. The customer's connector has no network connectivity to the smaller organization's infrastructure. You need to map LDAP users from both your customer and the smaller organization. How is this achieved?
A CyberArk Privileged Cloud Shared Services customer asks you how to find recent failed login events for all users. Where can you do this without generating reports?
Which tool configures the user object that will be used during the installation of the PSM for SSH component?
Before installing the Privilege Cloud Connector using Connector Management, which network rules should be in place?
What is determined by the MaxConcurrentConnections setting within a platform?
Which group has only View Audit and View Safe permissions?
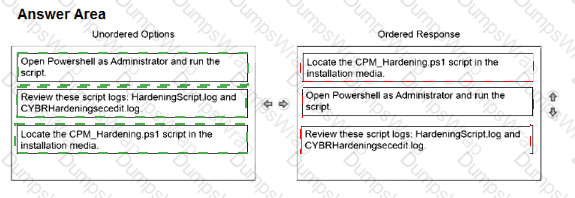
Arrange the steps to complete CPM Hardening for out-of-Domain deployment in the correct sequence.
You need to map an enterprise’s Active Directory to Privilege Cloud Shared Services to enable users to log in to CyberArk through their LDAP credentials. What do you need to accomplish this? (Choose two.)
Which actions must be performed when manually hardening a SUSE server with PSM for SSH? (Choose two.)
Which statements are correct regarding LDAP integration in Privilege Cloud Shared Services? (Choose two.)
To disable the PSM default Support for Browser Sessions, which option should be set to 'No* before running Hardening?
You want to enforce Multi-Factor Authentication (MFA) for all Privilege Cloud Shared Services users and require them to set up an MFA factor. How should you accomplish this?
You are designing a CyberArk Privilege Cloud environment for a new customer with three data center locations: one in London, one in New York, and one in Singapore. The customer wants to reduce the amount of traffic on their dedicated network links between each data center. Which design should you consider to manage their credentials?
Which prerequisites are required for installing PSM for SSH (Unix Connector)? (Choose two.)
When installing the PSM and CPM components on the same Privilege Cloud Connector, what should you consider when hardening?
You are deploying a CyberArk Identity Connector to integrate Privilege Cloud Shared Services with an Active Directory environment. Which requirement must be met?
The Secure Tunnel component of CyberArk Privilege Cloud connects to which services in the CyberArk Privilege Cloud? (Choose two.)
Which external-facing IP addresses need to be provided to CyberArk when configuring Privilege Cloud so that they can be allowlisted?