Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator Questions and Answers
Refer to the exhibit, which shows the ADVPN network topology and partial BGP configuration.
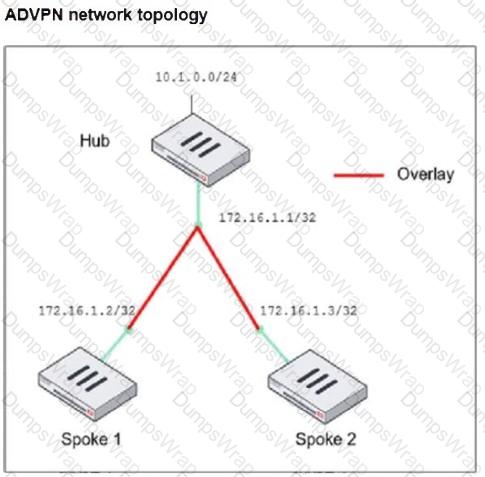
Which two parameters must an administrator configure in the config neighbor range for spokes shown in the exhibit? (Choose two.)
Which two recommendations prevent invalid paths when using zero phase 2 selectors?
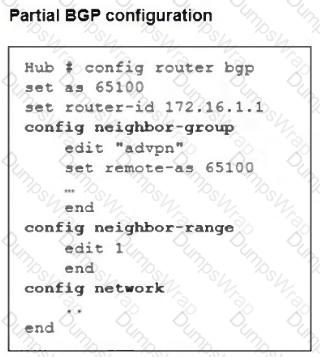
Refer to the exhibit.
A pre-run CLI template that is used in zero-touch provisioning (ZTP) and low-touch provisioning (LTP) with FortiManager is shown.
The template is not assigned even though the configuration has already been installed on FortiGate.
What is true about this scenario?
Refer to the exhibit, which shows a partial troubleshooting command output.
An administrator is extensively using IPsec on FortiGate. Many tunnels show information similar to the output shown in the exhibit.
What can the administrator conclude?
Which two statements about the LAN interface connection are correct?
Refer to the exhibit.
A LAN interface connected from FortiGate to two FortiSwitch devices is shown.
Which two statements about the LAN interface connection shown in the exhibit are correct? (Choose two.)
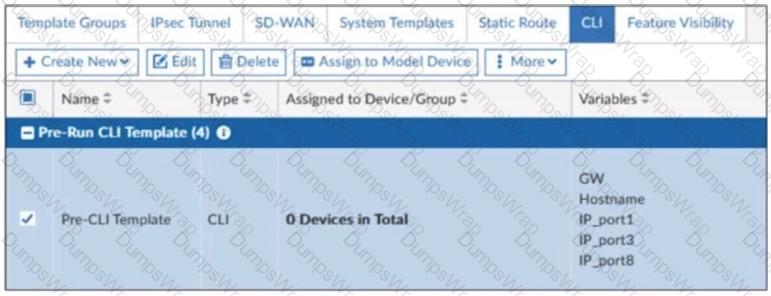
Refer to the exhibits.
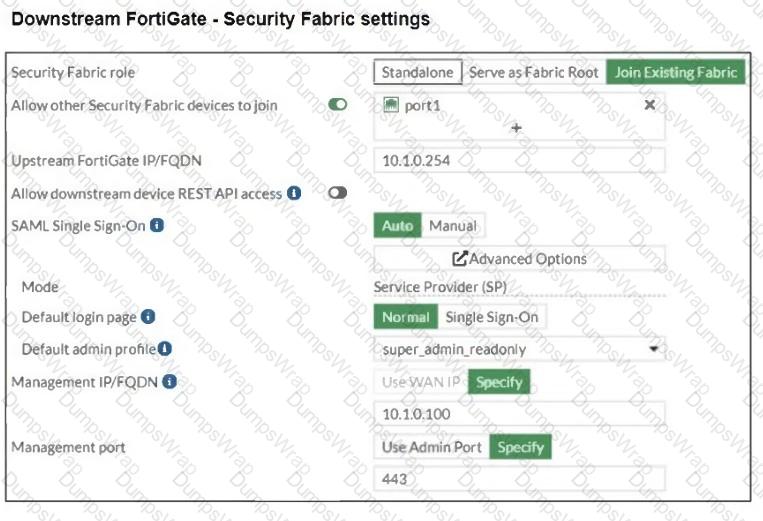
The Administrators section of a root FortiGate device and the Security Fabric Settings section of a downstream FortiGate device are shown.
When prompted to sign in with Security Fabric in the downstream FortiGate device, a user enters the AdminSSO credentials.
What is the next status for the user?
Refer to the exhibits. The exhibits show a network topology, a firewall policy, and an SSL/SSH inspection profile configuration.
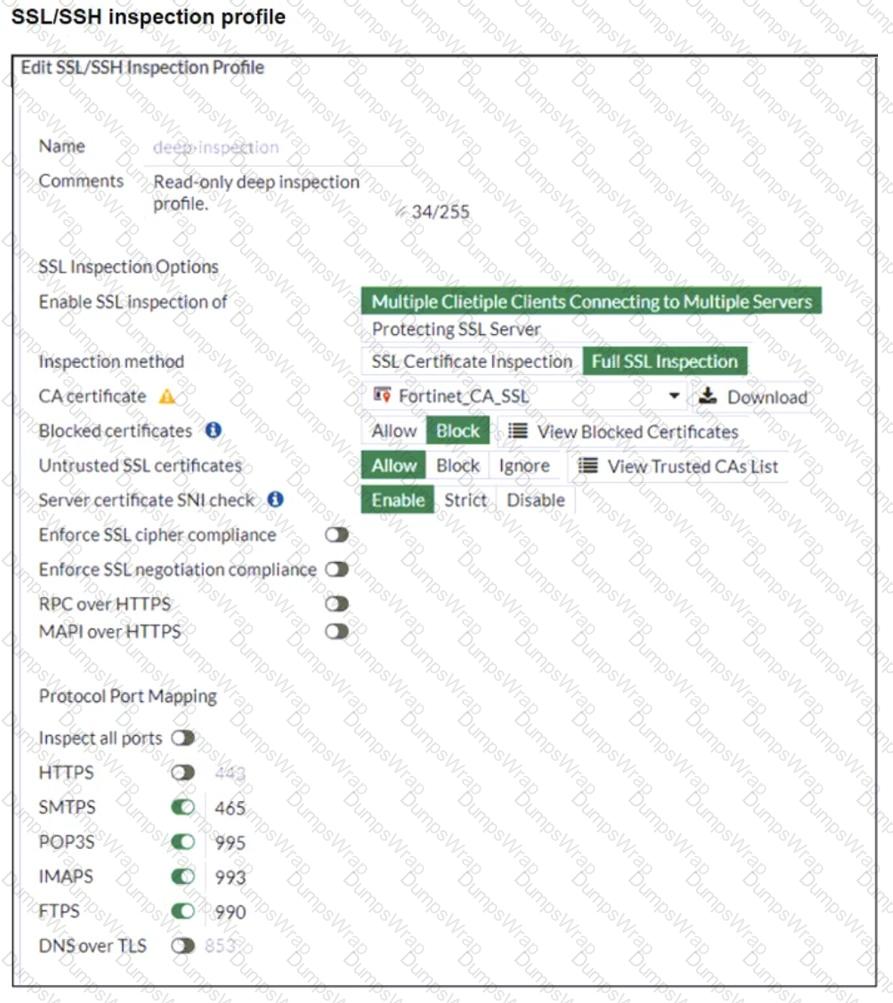
Why is FortiGate unable to detect HTTPS attacks on firewall policy ID 3 targeting the Linux server?
Refer to the exhibit.
The routing tables of FortiGate_A and FortiGate_B are shown. FortiGate_A and FortiGate_B are in the same autonomous system.
The administrator wants to dynamically add only route 172.16.1.248/30 on FortiGate_A.
What must the administrator configure?
How can FortiGate analyze HTTPS traffic on non-standard port 8443?
Which two features can you use to segment an enterprise network?
Refer to the exhibits.
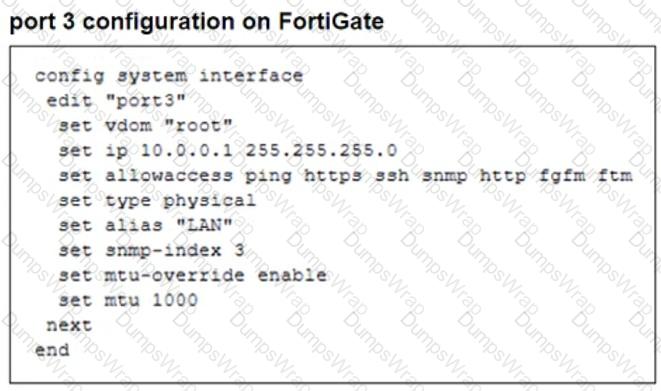
The configuration of a user ' s Windows PC, which has a default MTU of 1500 bytes, along with FortiGate interfaces set to an MTU of 1000 bytes, and the results of PC1 pinging server 172.16.0.254 are shown.
Why is the user in Windows PC1 unable to ping server 172.16.0.254 and is seeing the message: Packet needs to be fragmented but DF set?
The IT department discovered during the last network migration that all zero phase selectors in phase 2 IPsec configurations impacted network operations.
What are two valid approaches to prevent this during future migrations? (Choose two.)
An administrator is setting up an ADVPN configuration and wants to ensure that peer IDs are not exposed during VPN establishment.
Which protocol can the administrator use to enhance security?
How can you ensure the corporate FortiGate learns the 192.168.1.0/24 network?
Refer to the exhibit, which shows an enterprise network connected to an internet service provider.
The administrator must configure the BGP section of FortiGate A to give internet access to the enterprise network.
Which command must the administrator use to establish a connection with the internet service provider?
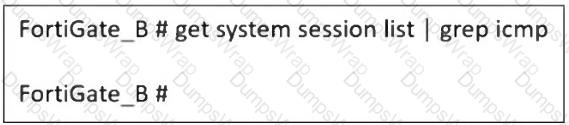
Why does FortiGate_B not show ICMP sessions when running: get system session list | grep icmp in an FGSP cluster?
Which two statements about IKEv2 are true if an administrator decides to implement IKEv2 in the VPN topology? (Choose two.)
You are using Virtual eXtensible LAN (VXLAN) extensively on FortiGate. Which specialized acceleration hardware must you use to improve FortiGate performance? (Choose one answer)
How does configuring tcp-mss-sender and tcp-mss-receiver affect TCP packets?
Refer to the exhibits.
The routing tables of FortiGate_A and FortiGate_B, and a network topology are shown.
Why does FortiGate_B have only one external route available to 100.75.5.1/32?
To secure your enterprise network traffic, which step does FortiGate perform first, when handling the first packets of a session? (Choose one answer)
Refer to the exhibit, which shows a command output.
FortiGate_A and FortiGate_B are members of an FGSP cluster in an enterprise network.
While testing the cluster using the ping command, the administrator monitors packet loss and found that the session output on FortiGate_B is as shown in the exhibit.
What could be the cause of this output on FortiGate_B?
Which two approaches facilitate efficient ADVPN deployment?
Which action should you take after applying a block-all IPS profile that caused applications to stop working?
Refer to the exhibit, which contains a partial command output.
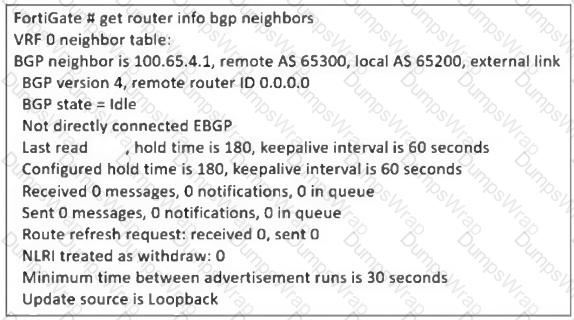
The administrator has configured BGP on FortiGate. The status of this new BGP configuration is shown in the exhibit.
What configuration must the administrator consider next?
Refer to the exhibit.
A FortiGate segmented into VDOMs is shown. You must ensure effective and accelerated internet access for all of the VDOMs in this enterprise network. How can you achieve this? (Choose one answer)
An administrator wants to scale the IBGP sessions and optimize the routing table in an IBGP network.
Which parameter should the administrator configure?
What is the initial step performed by FortiGate when handling the first packets of a session?
What must be done for RIP routes to propagate into OSPF?
Refer to the exhibit, which shows the FortiGuard Distribution Network of a FortiGate device.
FortiGuard Distribution Network on FortiGate
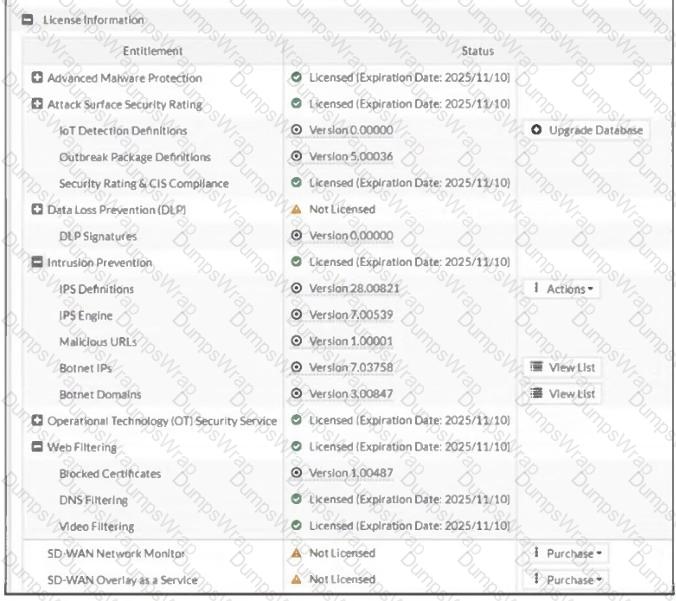
An administrator is trying to find the web filter database signature on FortiGate to resolve issues with websites not being filtered correctly in a flow-mode web filter profile.
Why is the web filter database version not visible on the GUI, such as with IPS definitions?
What does the command set forward-domain < domain_ID > in a transparent VDOM interface do?
A vulnerability scan report has revealed that a user has generated traffic to the website example.com (10.10.10.10) using a weak SSL/TLS version supported by the HTTPS web server.
What can the firewall administrator do to block all outdated SSL/TLS versions on any HTTPS web server to prevent possible attacks on user traffic?

