Fortinet NSE 6 - Network Security 7.6 Support Engineer Questions and Answers
Refer to the exhibit, which shows the output o! the BGP database.
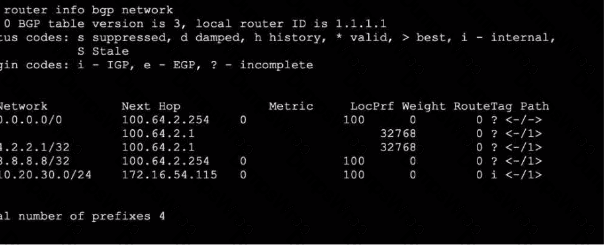
Which two statements are correct? (Choose two.)
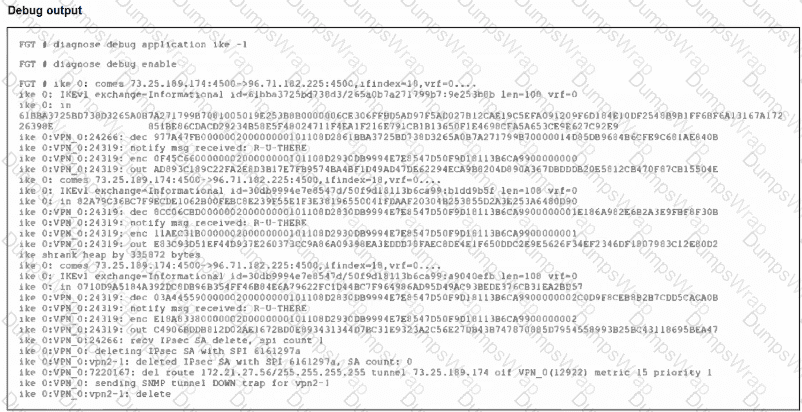
Refer to the exhibit, which contains partial output from an IKE real-time debug.
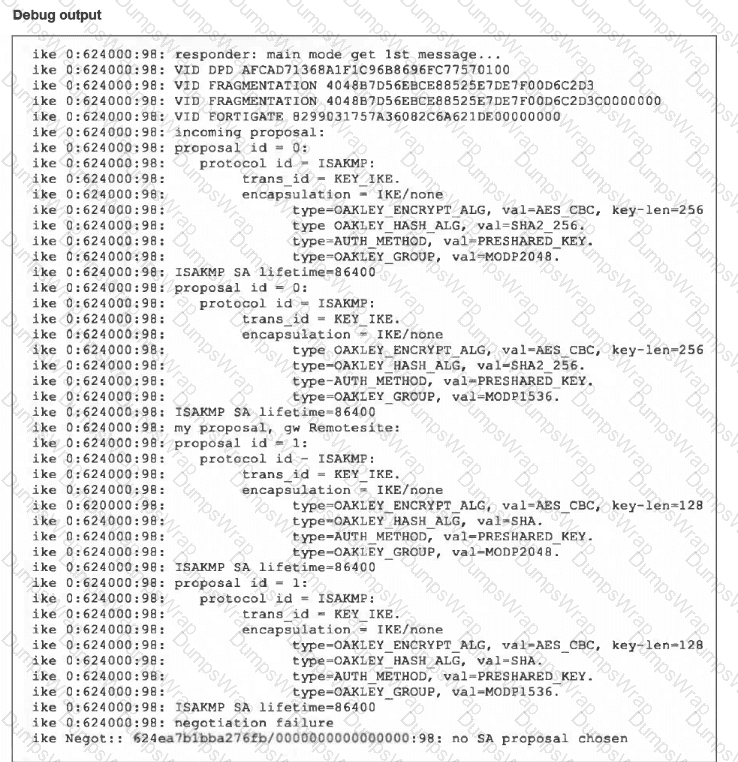
The administrator does not have access to the remote gateway.
Based on the debug output, which configuration change the administrator make to the local gateway to resolve the phase 1 negotiation error?
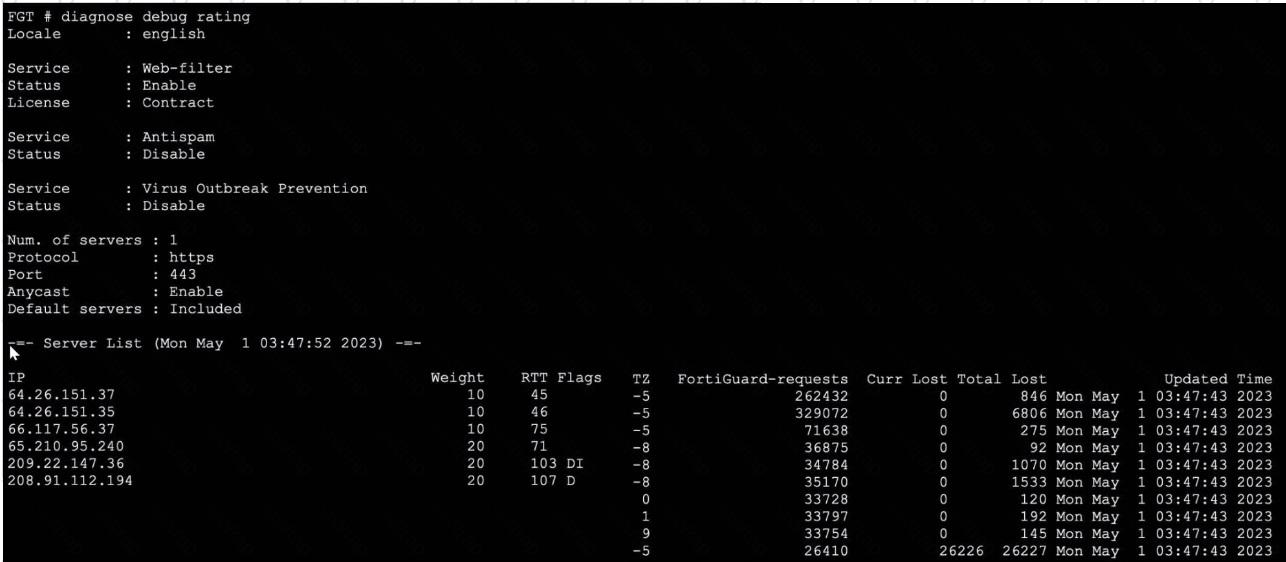
Refer to the exhibit.
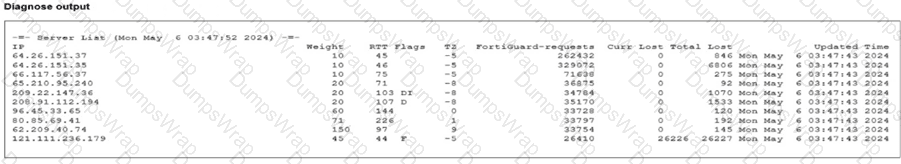
Partial output of command diagnose debug rating is shown. Which FDS server will the FortiGate algorithm choose?
Which statement about protocol options is true?
Refer to the exhibit, which shows the output of a BGP debug command.
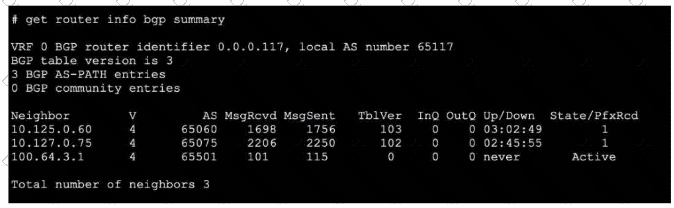
What can you conclude about the router in this scenario?
Refer to the exhibit.
The exhibit shows the output from using the command diagnose debug application samld -1 to diagnose a SAML connection.

Based on this output, what can you conclude?
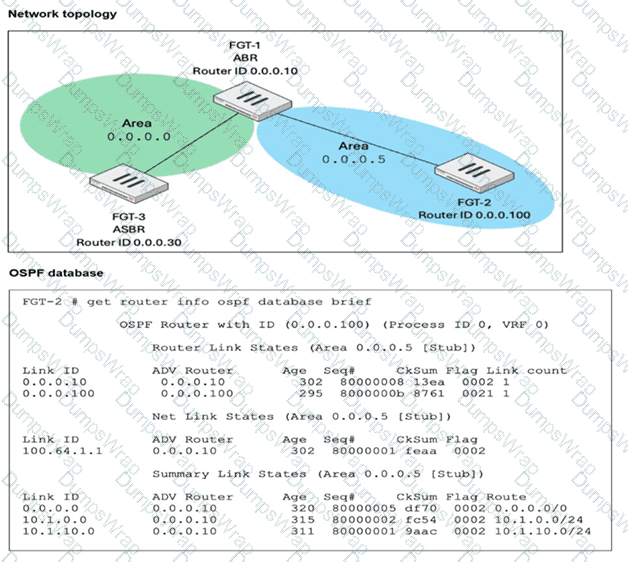
What are two reasons that an OSPF router does not have any type 5 tank-state advertisements (LSAs) In its link-stale database (LSD6)? (Choose two.)
Refer to the exhibit showing a debug output.
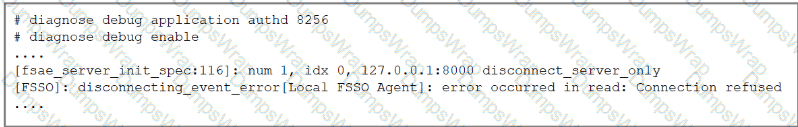
An administrator deployed FSSO in DC Agent Mode but FSSO is failing on FortiGate. Pinging FortiGate from where the collector agent is deployed is successful.
The administrator then produces the debug output shown in the exhibit.
What could be causing this error message?
Refer to the exhibit.
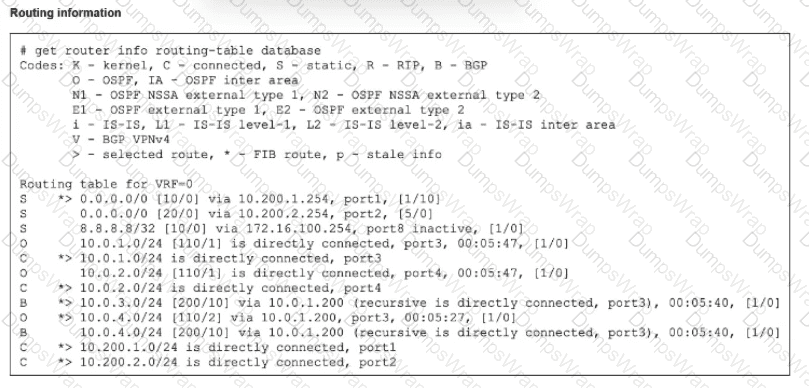
The modified output of live routing kemel is shown
Which two statements about the output are (rue? (Choose two.)
Refer to the exhibit.
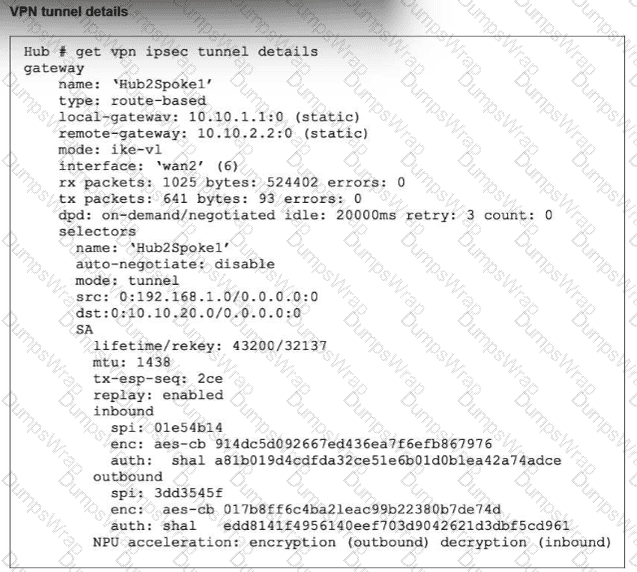
Partial output of the get vpn ipsec tunnel details command is shown. Based on the output, which two statements are correct? (Choose two.)
Which exchange lakes care of DoS protection in IKEv2?
Refer to the exhibit.
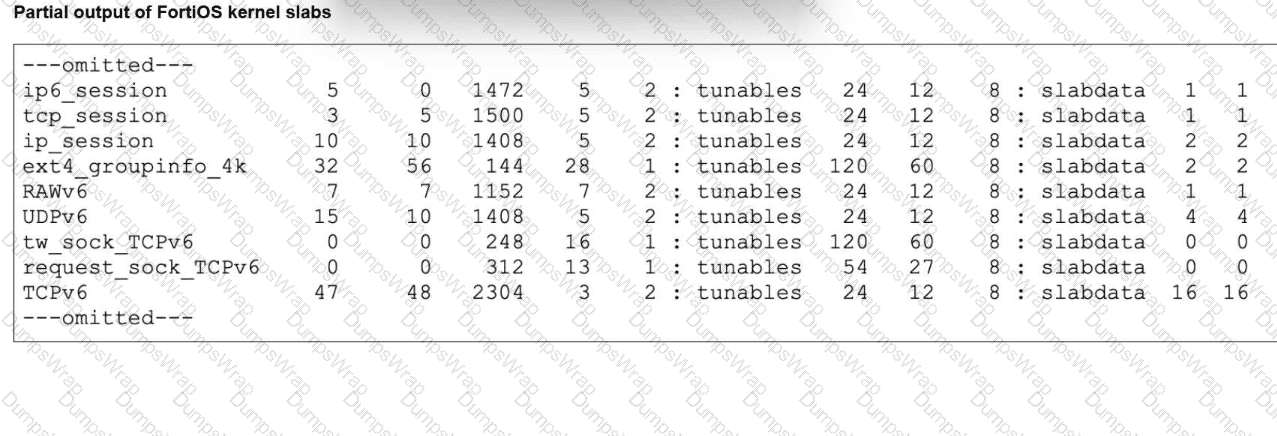
The partial output of FortiOS kernel slabs is shown. Which statement about total slab size is true?
Refer to the exhibit, which shows a partial output of a real-time LDAP debug.
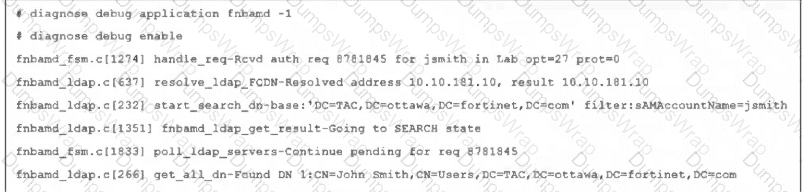
What two conclusions can you draw from the output? (Choose two.)
Refer to the exhibit.
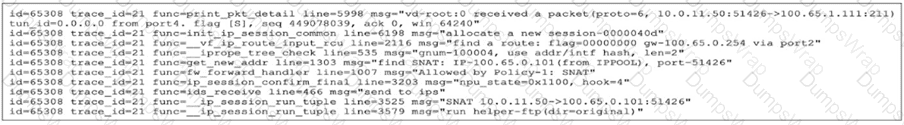
An administrator has configured a firewall policy to use proxy-based inspection mode. What could explain the messages observed in the debug flow output?
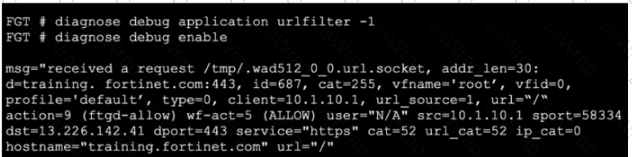
Refer to the exhibit, which shows the output of a real-time debug. Which statement about this output is true? (Choose one answer)
What are two functions of automation stitches? (Choose two.)
Refer to the exhibit, which shows one way communication of the downstream FortiGate with the upstream FortiGate within a Security Fabric.
What three actions must you take to ensure successful communication? (Choose three.)
Refer to the exhibit.
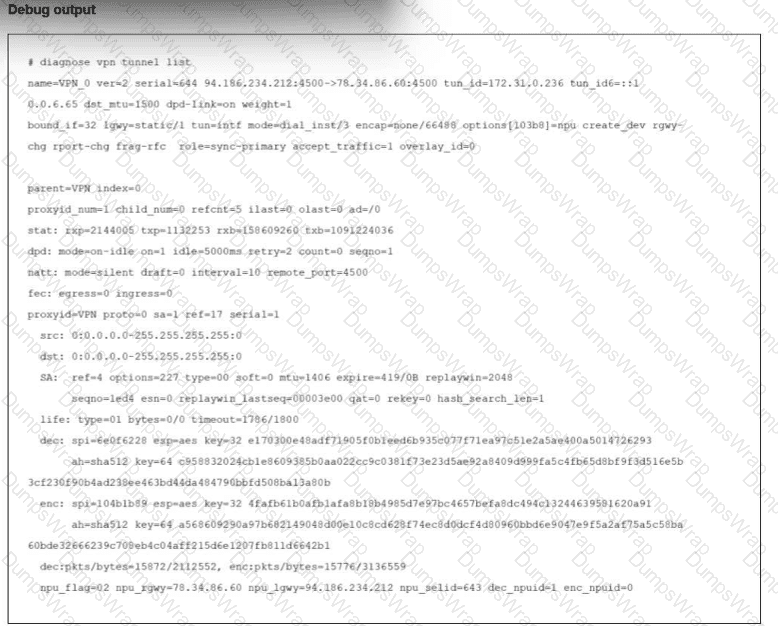
The output of the command diagnose vpn tunnel list is shown.
Reviewing the debug command, what is the current status of the traffic flowing through the tunnel?
Exhibit.
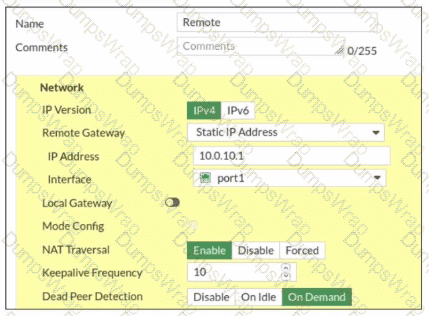
Refer to the exhibit, which contains a screenshot of some phase 1 settings.
The VPN is not up. To diagnose the issue, the administrator enters the following CLI commands on an SSH session on FortiGate:
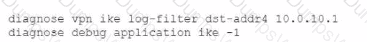
However, the IKE real-time debug does not show any output. Why?
Refer to the exhibit, which shows the output of a policy route table entry.
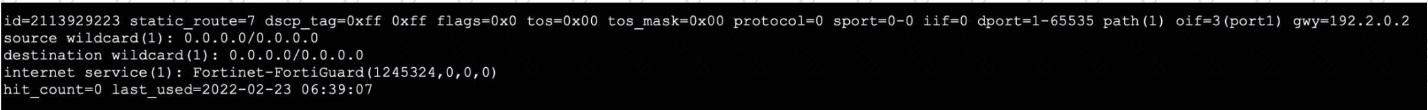
Which type of policy route does the output show?
Which two statements about an auxiliary session ate true? (Choose two.)
While troubleshooting a FortiGate web filter issue, users report that they cannot access any websites, even though those sites are not explicitly blocked by any web filter profiles that are applied to firewall policies.
What are the three most likely reasons for this behavior? (Choose three answers)
Which Iwo troubleshooting steps should you perform lf you encounter issues with intermittent web filter behavior? (Choose two.)
Refer to the exhibit, which shows partial outputs from two routing debug commands.
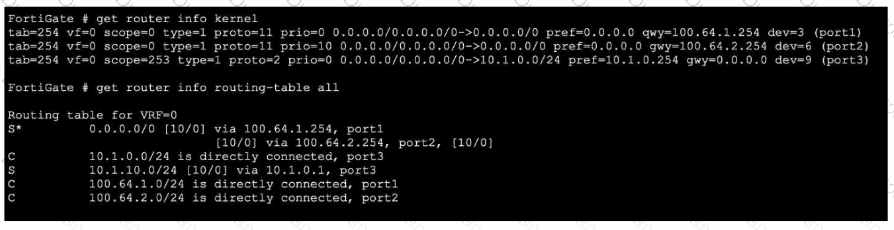
Which change must an administrator make on FortiGate to route web traffic from internal users to the internet, using ECMP?
Refer to the exhibit.
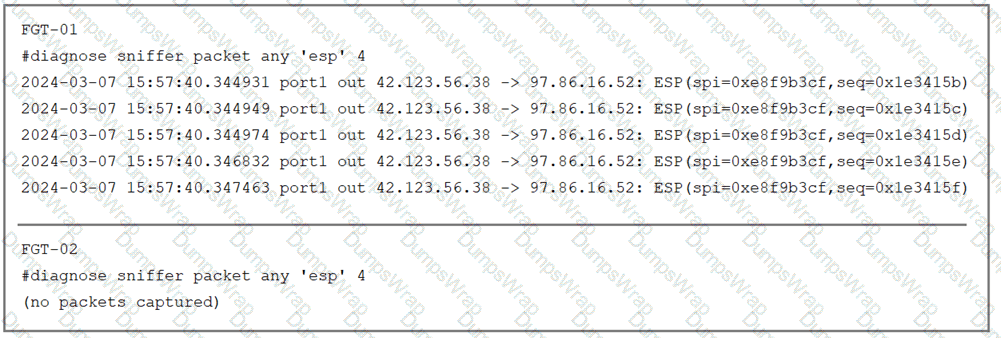
The sniffer log on two FortiGate devices are shown. Based on the information in the log, which two factors explain the output on FortiGate FGT-02? (Choose two answers)
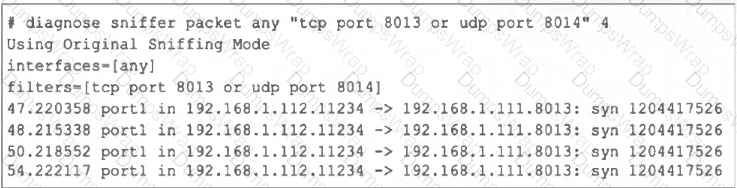
Refer to the exhibit, which shows the output of a diagnose command.
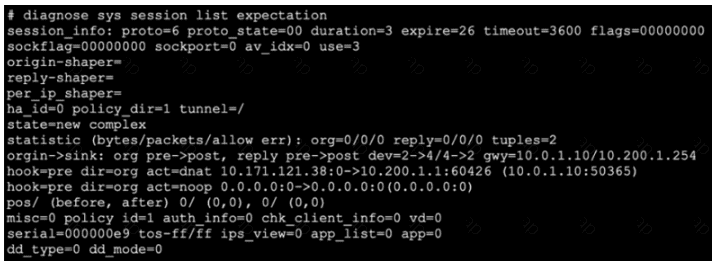
What two conclusions can you draw from the output shown in the exhibit? (Choose two answers)
What are two reasons you might see iprope_in check () check failed, drop when using the debug How? (Choose two.)
Exhibit.
Refer to the exhibit, which shows the output of a diagnose command.
What can you conclude about the debug output in this scenario?
Exhibit 1.
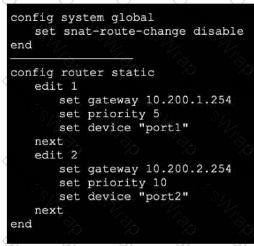
Exhibit 2.
Refer to the exhibits, which show the configuration on FortiGate and partial internet session information from a user on the internal network.
An administrator would like to lest session failover between the two service provider connections.
Which two changes must the administrator make to force this existing session to immediately start using the other interface? (Choose two.)
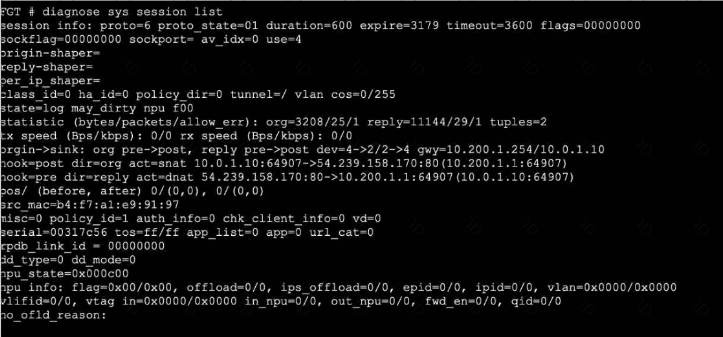
Refer to the exhibit.
An IPsec VPN tunnel is dropping, as shown by the debug output.
Analyzing the debug output, what could be causing the tunnel to go down?
Refer to the exhibit, which shows the partial output of a real-time OSPF debug.
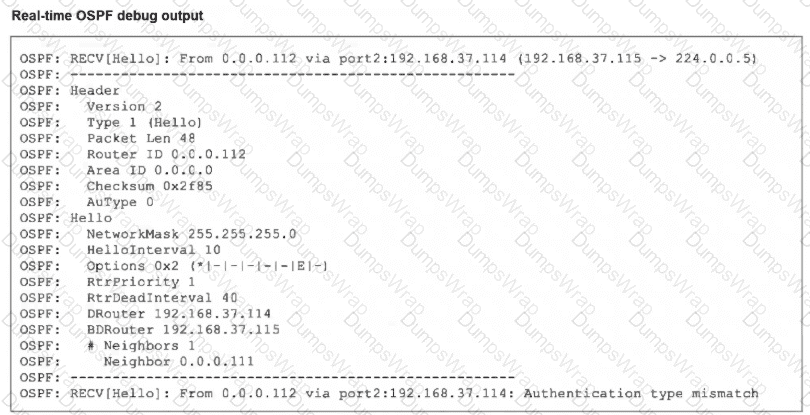
Why are the two FortiGate devices unable to form an adjacency?
Refer to the exhibit, which shows the output of get router info ospf neighbor.
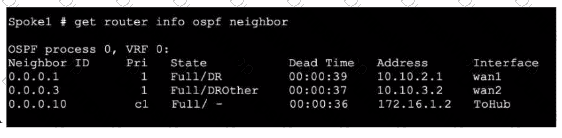
What can you conclude from the command output?
Refer to the exhibit.
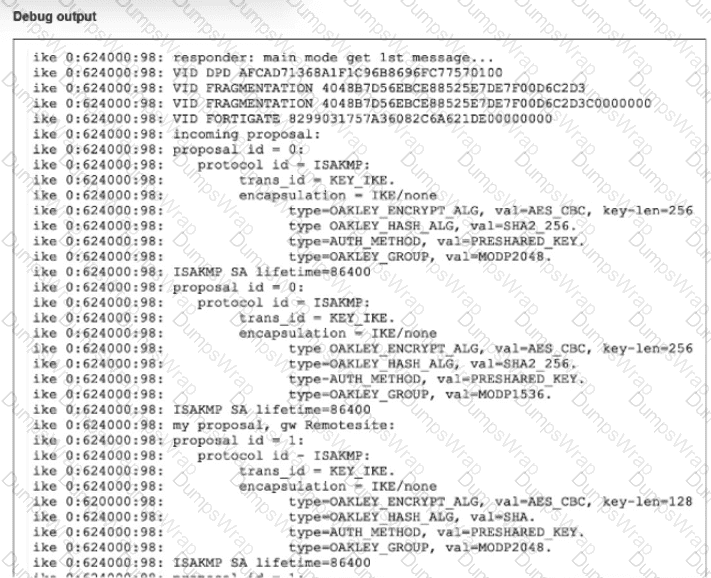
A partial output from an IKE real-time debug is shown
The administrator does not have access to (he remote gateway
Based on the debug output, which two conclusions can you draw? (Choose two.)
Which two protocol states indicate that traffic is bidirectional? (Choose two.)
Refer to the exhibit, which shows the port1 interface configuration on FortiGate and partial session information for ICMP traffic.

What happens to the session information if a routing change occurs that affects this session?
Consider the scenario where the server name indication (SNI) does not match either the common name (CN) or any of the subject alternative names (SAN) in the server certificate.
Which action will FortiGate take when using the default settings for SSL certificate inspection?
In the SAML negotiation process, which section does the Identity Provider (IdP) provide the SAML attributes utilized in the authentication process to the Service Provider (SP)?
Refer to the exhibit.
Partial output of diagnose sys session stat command is shown.
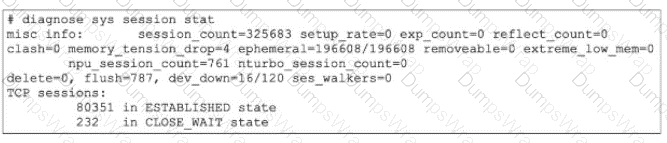
An administrator has noticed unusual behavior from FortiGate. It appears that sessions are randomly removed. Which two reasons could explain this? (Choose two.)
Which two statements about application-layer test commands are true? (Choose two answers)

