Fortinet NSE 4 - FortiOS 7.2 Questions and Answers
Which two statements describe how the RPF check is used? (Choose two.)
7
Which two settings can be separately configured per VDOM on a FortiGate device? (Choose two.)
Which statement about video filtering on FortiGate is true?
32
When configuring a firewall virtual wire pair policy, which following statement is true?
109
Why does FortiGate keep TCP sessions in the session table for some seconds even after both sides
(client and server) have terminated the session?
Refer to the exhibits.
Exhibit A shows the application sensor configuration. Exhibit B shows the Excessive-Bandwidth and Apple filter details.
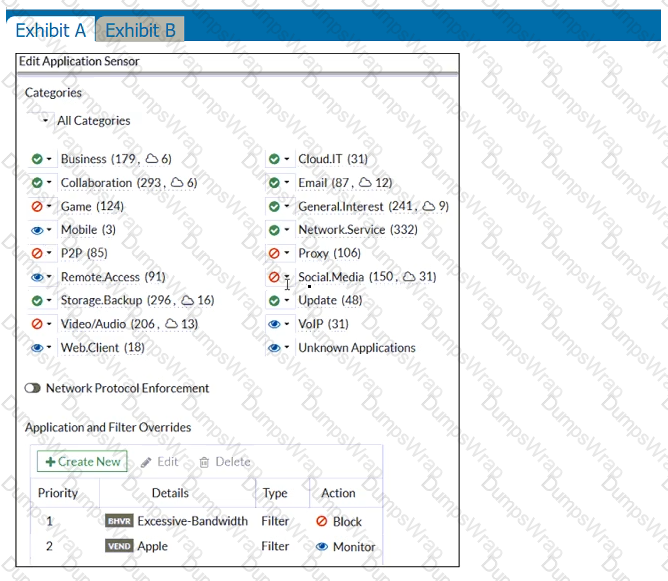
Based on the configuration, what will happen to Apple FaceTime if there are only a few calls originating or incoming?
An administrator wants to configure timeouts for users. Regardless of the userTMs behavior, the timer should start as soon as the user authenticates and expire after the configured value.
Which timeout option should be configured on FortiGate?
An administrator configures outgoing interface any in a firewall policy.
What is the result of the policy list view?
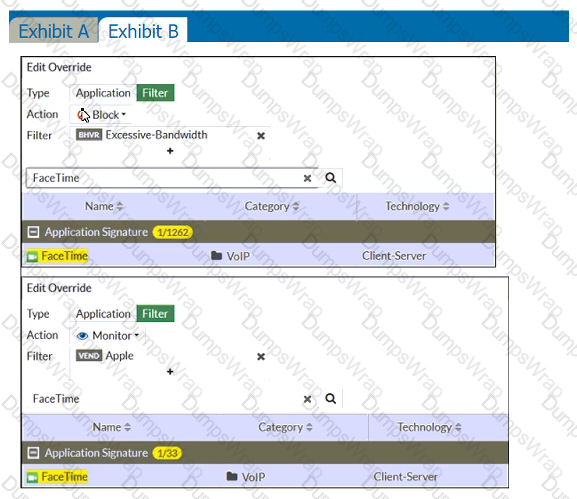
View the exhibit.
Which of the following statements are correct? (Choose two.)
By default, FortiGate is configured to use HTTPS when performing live web filtering with FortiGuard servers.
Which CLI command will cause FortiGate to use an unreliable protocol to communicate with FortiGuard servers for live web filtering?
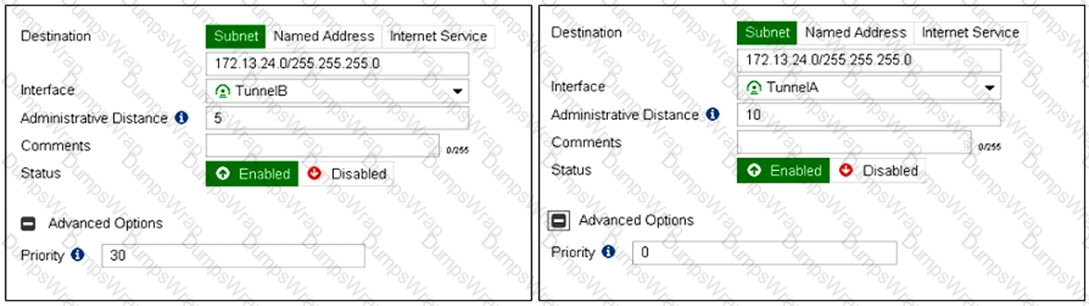
Refer to the exhibit showing a debug flow output.
What two conclusions can you make from the debug flow output? (Choose two.)
An administrator is configuring an IPsec VPN between site A and site B. The Remote Gateway setting in both sites has been configured as Static IP Address. For site A, the local quick mode selector is 192. 168. 1.0/24 and the remote quick mode selector is 192. 168.2.0/24.
Which subnet must the administrator configure for the local quick mode selector for site B?
An administrator needs to increase network bandwidth and provide redundancy.
What interface type must the administrator select to bind multiple FortiGate interfaces?
Which scanning technique on FortiGate can be enabled only on the CLI?
Which statement about video filtering on FortiGate is true?
18
If the Issuer and Subject values are the same in a digital certificate, which type of entity was the certificate issued to?
Which two types of traffic are managed only by the management VDOM? (Choose two.)
Which statement is correct regarding the use of application control for inspecting web applications?
Which two statements about FortiGate FSSO agentless polling mode are true? (Choose two.)
An administrator has configured a strict RPF check on FortiGate. Which statement is true about the strict RPF check?
What is the effect of enabling auto-negotiate on the phase 2 configuration of an IPsec tunnel?
20
Which two statements are true about the RPF check? (Choose two.)
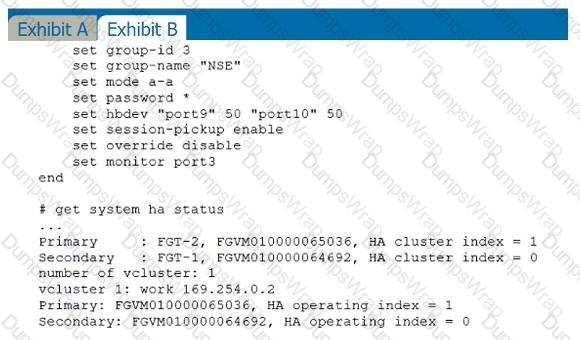
Refer to the exhibit.
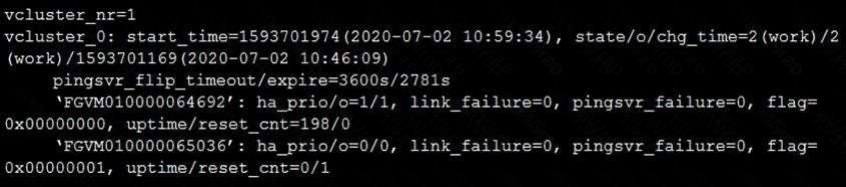
The exhibit displays the output of the CLI command: diagnose sys ha dump-by vcluster.
Which two statements are true? (Choose two.)
Refer to the exhibit.
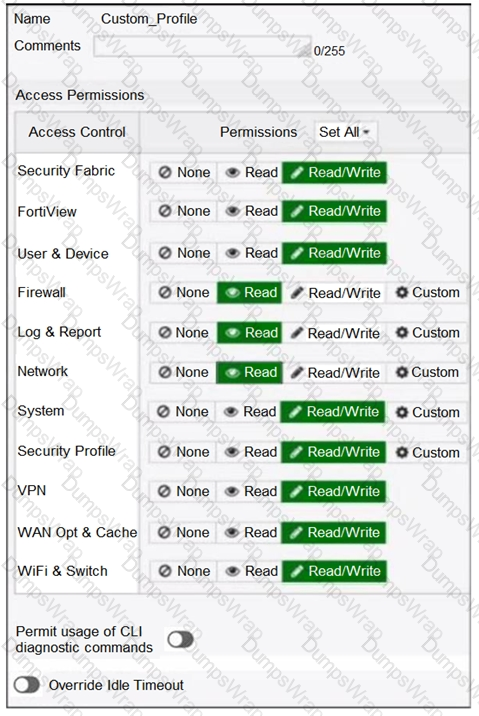
Based on the administrator profile settings, what permissions must the administrator set to run the diagnose firewall auth list CLI command on FortiGate?
Examine this PAC file configuration.
Which of the following statements are true? (Choose two.)
Which statement about the deployment of the Security Fabric in a multi-VDOM environment is true?
What is the limitation of using a URL list and application control on the same firewall policy, in NGFW policy-based mode?
Which statements best describe auto discovery VPN (ADVPN). (Choose two.)
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 fails to come up. The administrator has also re-entered the pre-shared key on both FortiGate devices to make sure they match.
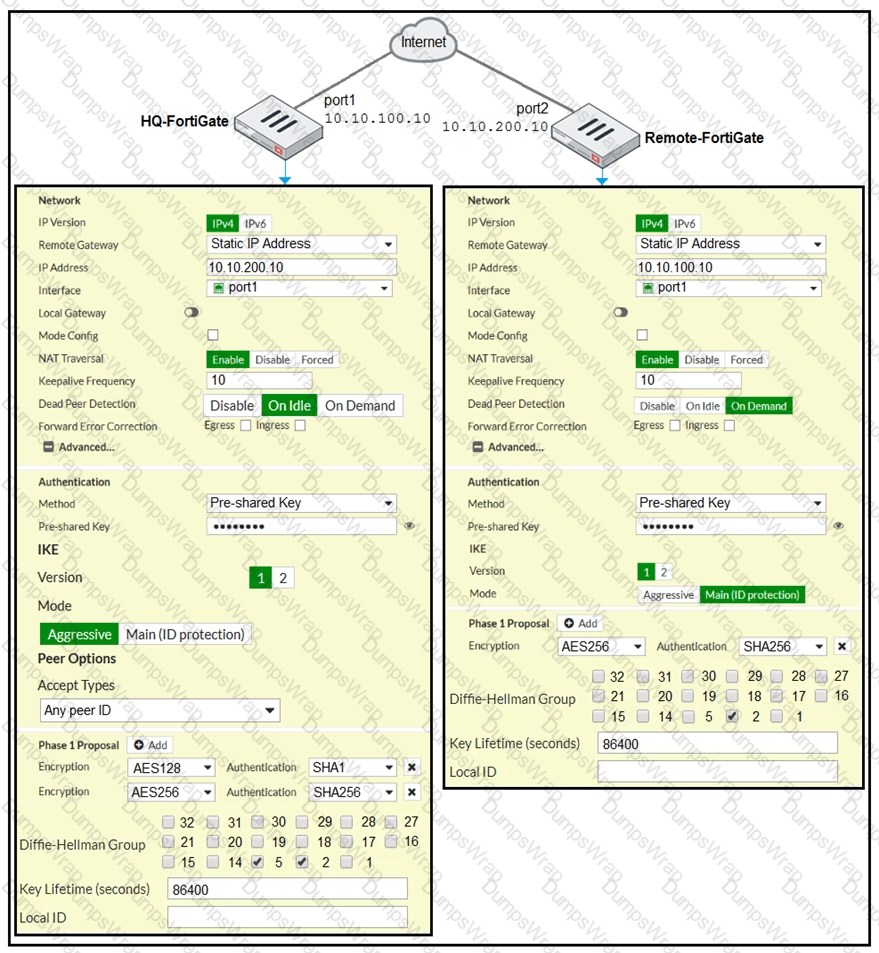
Based on the phase 1 configuration and the diagram shown in the exhibit, which two configuration changes will bring phase 1 up? (Choose two.)
An administrator must disable RPF check to investigate an issue.
Which method is best suited to disable RPF without affecting features like antivirus and intrusion prevention system?
Refer to the web filter raw logs.
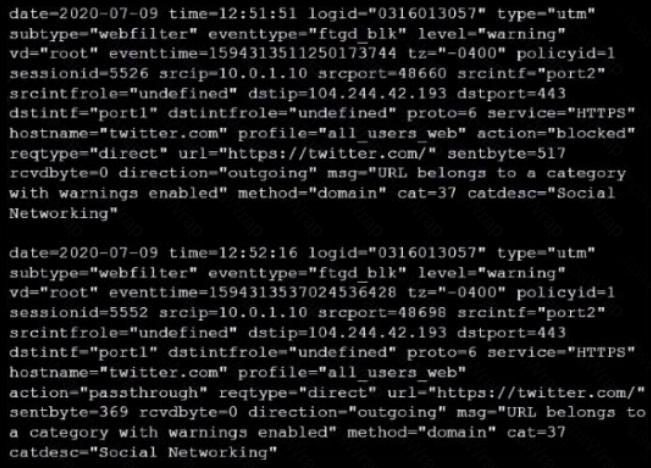
Based on the raw logs shown in the exhibit, which statement is correct?
Which two types of traffic are managed only by the management VDOM? (Choose two.)
Refer to the exhibit.
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 status is up, but phase 2 fails to come up.
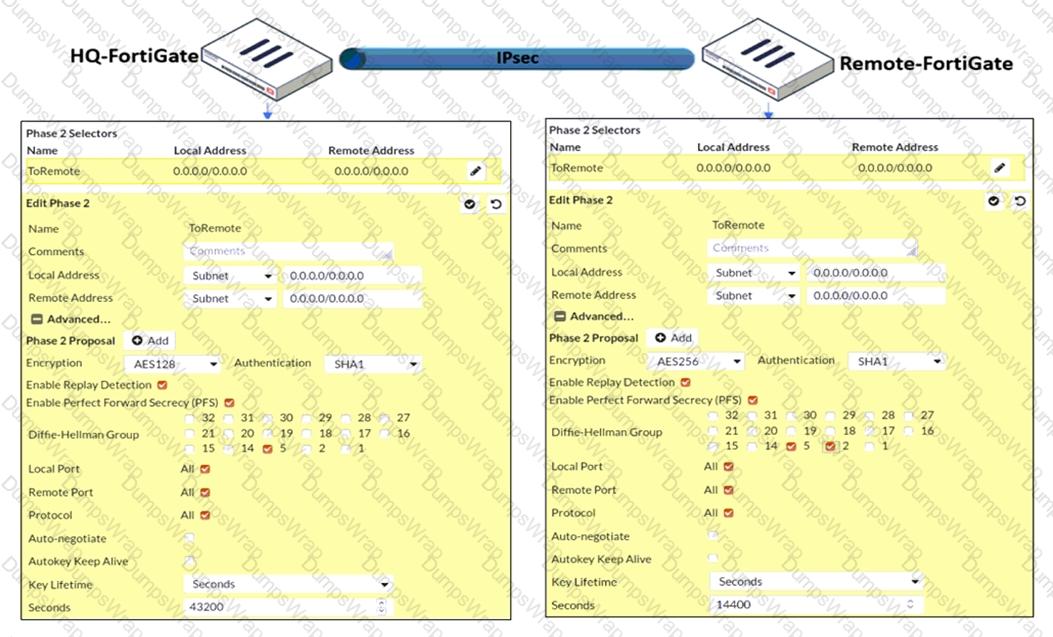
Based on the phase 2 configuration shown in the exhibit, which configuration change will bring phase 2 up?
Which of the following SD-WAN load balancing method use interface weight value to distribute traffic? (Choose two.)
Refer to the exhibits.
Exhibit A shows a topology for a FortiGate HA cluster that performs proxy-based inspection on traffic. Exhibit B shows the HA configuration and the partial output of the get system ha status command.
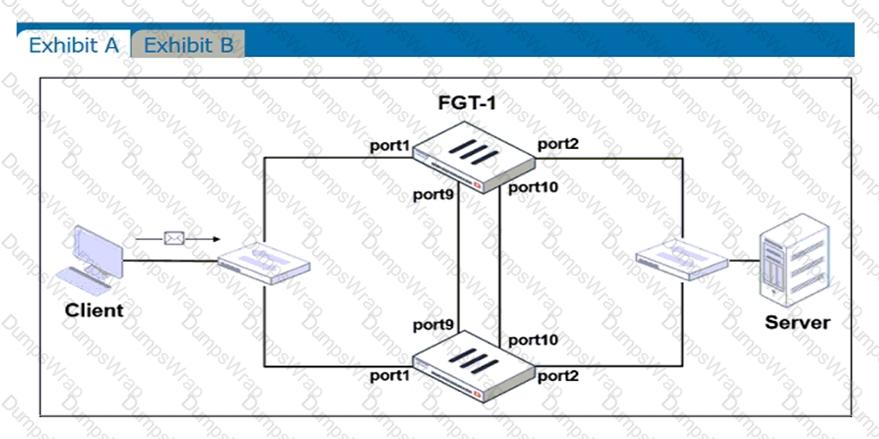
Based on the exhibits, which two statements about the traffic passing through the cluster are true? (Choose two.)
Refer to the exhibit.
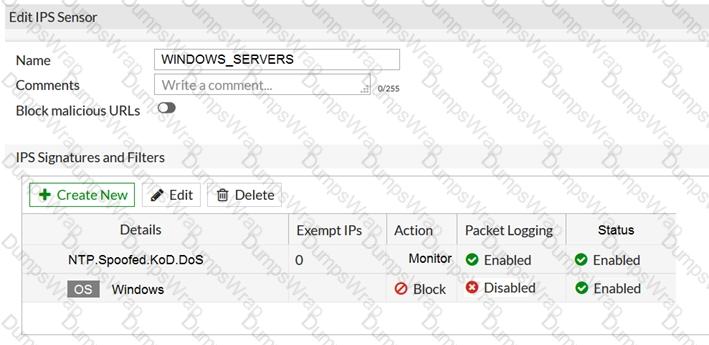
The exhibit shows the IPS sensor configuration.
If traffic matches this IPS sensor, which two actions is the sensor expected to take? (Choose two.)
Which statement correctly describes the use of reliable logging on FortiGate?
17
In consolidated firewall policies, IPv4 and IPv6 policies are combined in a single consolidated policy. Instead of separate policies. Which three statements are true about consolidated IPv4 and IPv6 policy configuration? (Choose three.)
85
Which statement regarding the firewall policy authentication timeout is true?
87
Which of the following are valid actions for FortiGuard category based filter in a web filter profile ui proxy-based inspection mode? (Choose two.)
Refer to the exhibits.
Exhibit A shows a network diagram. Exhibit B shows the firewall policy configuration and a VIP object configuration.
The WAN (port1) interface has the IP address 10.200.1.1/24.
The LAN (port3) interface has the IP address 10.0.1.254/24.
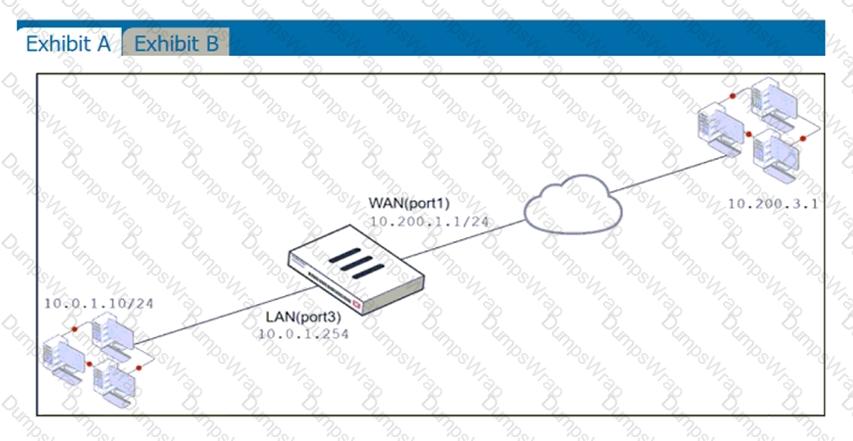
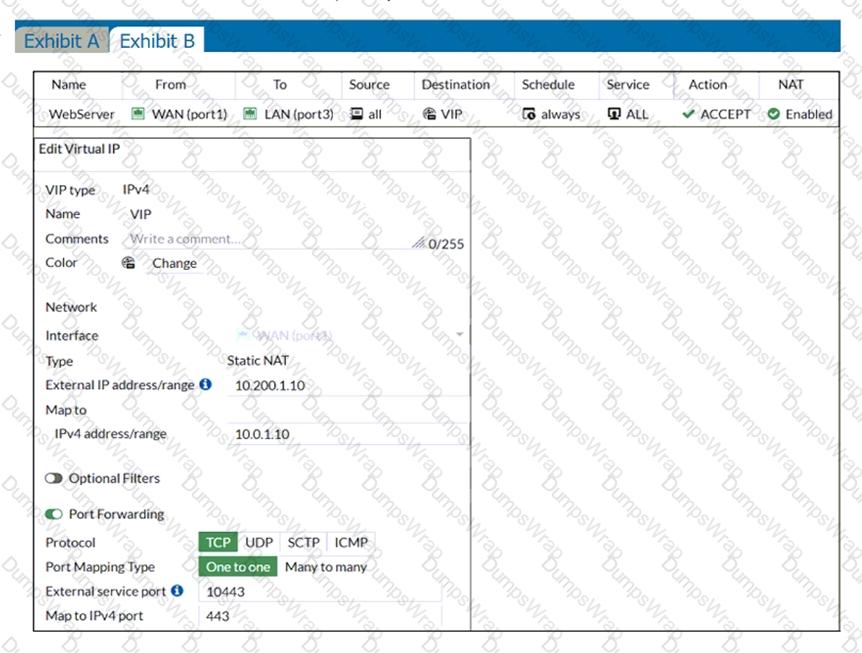
If the host 10.200.3.1 sends a TCP SYN packet on port 10443 to 10.200.1.10, what will the source address, destination address, and destination port of the packet be, after FortiGate forwards the packet to the destination?
An administrator wants to simplify remote access without asking users to provide user credentials.
Which access control method provides this solution?
27
Which feature in the Security Fabric takes one or more actions based on event triggers?
99
An administrator needs to configure VPN user access for multiple sites using the same soft FortiToken. Each site has a FortiGate VPN gateway. What must an administrator do to achieve this objective?
What are two features of collector agent advanced mode? (Choose two.)
Refer to the exhibit.
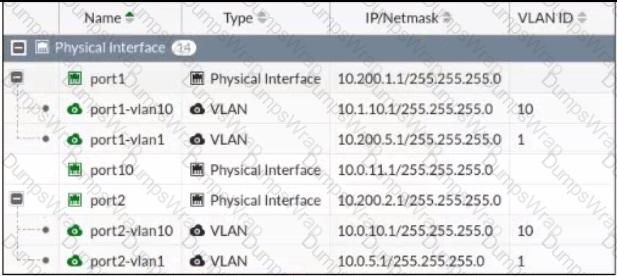
Given the interfaces shown in the exhibit. which two statements are true? (Choose two.)
Which two settings are required for SSL VPN to function between two FortiGate devices? (Choose two.)
Refer to the exhibit.
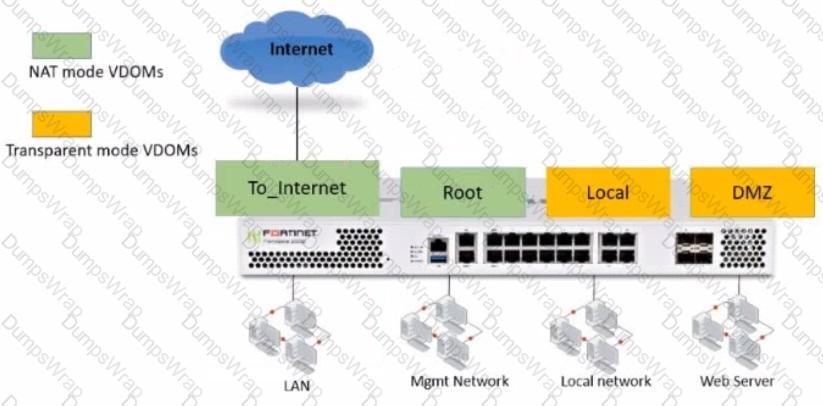
The Root and To_Internet VDOMs are configured in NAT mode. The DMZ and Local VDOMs are configured in transparent mode.
The Root VDOM is the management VDOM. The To_Internet VDOM allows LAN users to access the internet. The To_Internet VDOM is the only VDOM with internet access and is directly connected to ISP modem .
With this configuration, which statement is true?
What are two benefits of flow-based inspection compared to proxy-based inspection? (Choose two.)
Which two statements are correct regarding FortiGate FSSO agentless polling mode? (Choose two.)
Refer to the exhibit.
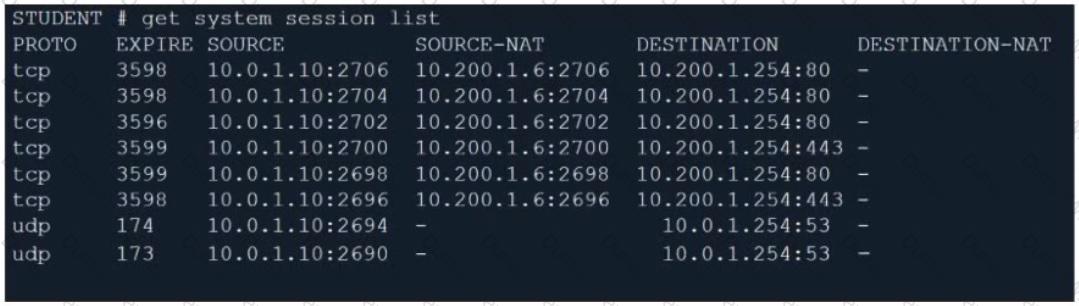
Which contains a session list output. Based on the information shown in the exhibit, which statement is true?

