Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator Questions and Answers
You have configured the performance SLA with the probe mode as Prefer Passive.
What are two observable impacts of this configuration? (Choose two.)
Options:
FortiGate can offload the traffic that is subject to passive monitoring to hardware.
FortiGate passively monitors the member if ICMP traffic is passing through the member.
During passive monitoring, the SLA performance rule cannot detect dead members.
After FortiGate switches to active mode, the SLA performance rule falls back to passive monitoring after 3 minutes.
FortiGate passively monitors the member if TCP traffic is passing through the member.
Answer:
C, EExplanation:
In theSD-WAN 7.6 Core Administratorcurriculum, the "Prefer Passive" probe mode is a hybrid monitoring strategy designed to minimize the overhead of synthetic traffic (probes) while maintaining link health visibility. According to theFortiOS 7.6 Administration Guideand theSD-WAN Study Guide, the behavior and impacts are as follows:
TCP Traffic Requirement (Option E):Passive monitoring relies on the FortiGate’s ability to inspect actual user traffic to calculate health metrics such as Latency, Jitter, and Packet Loss. Specifically, it usesTCP traffic(by analyzing TCP sequence numbers and timestamps to calculate Round Trip Time - RTT). If user traffic is flowing through the member interface, the FortiGate uses those real-world sessions for SLA calculations instead of sending its own probes.
Inability to Detect Dead Members (Option C):A significant limitation of passive monitoring is that it cannot distinguish between a "dead" link and an "idle" link. If there is no traffic, the passive monitor has no data to analyze. Consequently, while in passive mode, the SD-WAN enginecannot detect a dead member. To mitigate this, "Prefer Passive" includes a fail-safe: if no traffic is detected for a specific period (typically3 minutes), the FortiGate will automatically switch toActive mode(sending ICMP/TCP pings) to verify if the link is actually alive.
Why other options are incorrect:
Option A:Passive monitoring generallydisables hardware offloading (ASIC)for the monitored traffic. This is because the CPU must inspect every packet header to calculate performance metrics; if the traffic were offloaded to the Network Processor (NP), the CPU would not see the packets, rendering passive monitoring impossible.
Option B:While active probes often use ICMP,passive monitoringis specifically designed forTCP trafficbecause the TCP protocol's ACK structure allows for accurate RTT and loss calculation without synthetic packets.
Option D:The "3-minute" timer is actually the trigger to switchfrom passive to activewhen traffic is absent, not the fallback timer to return to passive. The fallback to passive happens as soon as valid TCP traffic is detected again.
According to theFortiSASE 7.6 Administration Guideand theFCP - FortiSASE 24/25 Administratorstudy materials, FortiSASE supports three primary external (remote) authentication sources to verify the identity of remote users (SIA and SPA users). These sources allow organizations to leverage their existing identity infrastructure for seamless onboarding and policy enforcement:
Security Assertion Markup Language (SAML) (Option A):This is the most common and recommended method for modern SASE deployments. FortiSASE acts as aSAML Service Provider (SP)and integrates withIdentity Providers (IdP)such as Microsoft Entra ID (formerly Azure AD), Okta, or FortiAuthenticator. This enables Single Sign-On (SSO) and Multi-Factor Authentication (MFA).
Lightweight Directory Access Protocol (LDAP) (Option C):FortiSASE can connect to on-premises or cloud-based LDAP servers (such as Windows Active Directory). This allows the administrator to map existing AD groups to FortiSASE user groups for granular security policy application.
Remote Authentication Dial-in User Service (RADIUS) (Option E):RADIUS is supported for organizations that use centralized authentication servers or traditional MFA solutions (like RSA SecurID). FortiSASE can query a RADIUS server to validate user credentials before granting access to the SASE tunnel.
Why other options are incorrect:
OpenID Connect (OIDC) (Option B):While OIDC is a modern authentication protocol similar to SAML, FortiSASE's primary integration for external Identity Providers is currently standardized onSAML 2.0.
TACACS+ (Option D):Terminal Access Controller Access-Control System Plus is primarily used foradministrative access(AAA) to network devices (like logging into a FortiGate CLI or FortiManager). It is not used for end-user VPN or SASE authentication in the Fortinet ecosystem.
The IT team is wondering whether they will need to continue using MDM tools for future FortiClient upgrades.
What options are available for handling future FortiClient upgrades?
Options:
Enable the Endpoint Upgrade feature on the FortiSASE portal.
FortiClient will need to be manually upgraded.
Perform onboarding for managed endpoint users with a newer FortiClient version.
A newer FortiClient version will be auto-upgraded on demand.
Answer:
AExplanation:
According to theFortiSASE 7.6 Feature Administration Guideand the latest updates to theNSE 5 SASEcurriculum, FortiSASE has introduced native lifecycle management for FortiClient agents to reduce the operational burden on IT teams who previously relied solely on third-party MDM (Mobile Device Management) or GPO (Group Policy Objects) for every update.
TheEndpoint Upgradefeature, found underSystem > Endpoint Upgradein the FortiSASE portal, allows administrators to perform the following:
Centralized Version Control: Administrators can see which versions are currently deployed and which "Recommended" versions are available from FortiGuard.
Scheduled Rollouts: You can choose to upgrade all endpoints or specific endpoint groups at a designated time, ensuring that upgrades do not disrupt business operations.
Status Monitoring: The portal provides a real-time dashboard showing the progress of the upgrade (e.g.,Downloading,Installing,Reboot Pending, orSuccess).
Manual vs. Managed: While MDM is still highly recommended for theinitial onboarding(the first time FortiClient is installed and connected to the SASE cloud), all subsequent upgrades can be handled natively by the FortiSASE portal.
Why other options are incorrect:
Option B: Manual upgrades are inefficient for large-scale deployments (~400 users in this scenario) and are not the intended "feature-rich" solution provided by FortiSASE.
Option C: "Onboarding" refers to the initial setup. Re-onboarding every time a version changes would be redundant and counterproductive.
Option D: While the system canmanagethe upgrade, it is not "auto-upgraded on demand" by the client itself without administrative configuration in the portal. The administrator must still define the target version and schedule.
Which three FortiSASE use cases are possible? (Choose three answers)
Options:
Secure Internet Access (SIA)
Secure SaaS Access (SSA)
Secure Private Access (SPA)
Secure VPN Access (SVA)
Secure Browser Access (SBA)
Answer:
A, B, CExplanation:
According to theFortiSASE 7.6 Architecture Guideand theFCP - FortiSASE 24/25 Administratorstudy materials, the FortiSASE solution is structured around three primary pillars or "use cases" that address the security requirements of a modern distributed workforce.
Secure Internet Access (SIA) (Option A): This use case focus on protecting remote users as they browse the public internet. It utilizes a full cloud-delivered security stack includingWeb Filtering,DNS Filtering,Anti-Malware, andIntrusion Prevention (IPS)to ensure that users are protected from web-based threats regardless of their physical location.
Secure SaaS Access (SSA) (Option B): This use case addresses the security of cloud-based applications (like Microsoft 365, Salesforce, and Dropbox). It leveragesInline-CASB (Cloud Access Security Broker)to identify and control "Shadow IT"—unauthorized cloud applications used by employees—and appliesData Loss Prevention (DLP)to prevent sensitive information from being leaked into unsanctioned SaaS platforms.
Secure Private Access (SPA) (Option C): This use case provides secure, granular access to private applications hosted in on-premises data centers or private clouds. It can be achieved through two main methods:ZTNA (Zero Trust Network Access), which provides session-specific access based on identity and device posture, or throughSD-WAN integration, where the FortiSASE cloud acts as a spoke connecting to a corporate SD-WAN Hub.
Why other options are incorrect:
Secure VPN Access (SVA) (Option D): While SASE uses VPN technology (SSL or IPsec) as a transport for the Endpoint mode, "SVA" is not a formal curriculum-defined use case. The SASE framework is intended to evolve beyond traditional "Secure VPN Access" into the SIA and SPA models.
Secure Browser Access (SBA) (Option E): Although FortiSASE offersRemote Browser Isolation (RBI), it is considered a feature or a component of the broaderSecure Internet Access (SIA)use case rather than a separate, standalone use case in the core administrator curriculum.
Which two statements about configuring a steering bypass destination in FortiSASE are correct? (Choose two.)
Options:
Subnet is the only destination type that supports the Apply condition
Apply condition allows split tunneling destinations to ae applied to On-net. off-net. or both types of endpoints
You can select from four destination types: Infrastructure, FQDN, Local Application, or Subnet
Apply condition can be set only to On-net or Off-net. but not both
Answer:
B, CExplanation:
According to theFortiSASE 7.6 Feature Administration Guide, steering bypass destinations (also known as split tunneling) allow administrators to optimize bandwidth by redirecting specific trusted traffic away from the SASE tunnel to the endpoint's local physical interface.
Destination Types (Option C): When creating a bypass destination, administrators can select from four distinct types:Infrastructure(pre-defined apps like Zoom/O365),FQDN(specific domains),Local Application(identifying processes on the laptop), orSubnet(specific IP ranges).
Apply Condition (Option B): The "Apply" condition is a flexible setting that allows the administrator to choose when the bypass is active. It can be applied to endpoints that areOn-net(inside the office),Off-net(remote), orBoth. This ensures that if a user is in the office, they don't use the SASE tunnel for local resources, but if they are home, they might still bypass high-bandwidth sites like YouTube to preserve tunnel capacity.
Why other options are incorrect:
Option A: Subnet is one of four types and is not the only type supporting these conditions.
Option D: The system explicitly supports "Both" to ensure consistency across network transitions.
Which three factors about SLA targets and SD-WAN rules should you consider when configuring SD-WAN rules? (Choose three answers)
Options:
When configuring an SD-WAN rule, you can select multiple SLA targets from different performance SLAs.
SLA targets are used only by SD-WAN rules that are configured with a Lowest Cost (SLA) strategy.
Member metrics are measured only if a rule uses the SLA target.
SD-WAN rules can use SLA targets to check whether the preferred members meet the SLA requirements.
When configuring an SD-WAN rule, you can select multiple SLA targets if they are from the same performance SLA.
Answer:
B, D, EExplanation:
According to theSD-WAN 7.6 Core Administratorstudy guide and theFortinet Document Library, the interaction between SD-WAN rules and SLA targets is governed by specific selection and measurement logic:
Usage by Strategy (Option B): SLA targets are fundamentally used by theLowest Cost (SLA)strategy to determine which links are currently healthy enough to be considered for traffic steering. While other strategies likeBest Qualityuse a "Measured SLA" to monitor metrics, they do not typically use the "Required SLA Target" to disqualify links unless specifically configured in a hybrid mode. In most curriculum contexts, the "Required SLA Target" field is specifically associated with the Lowest Cost and Maximize Bandwidth strategies.
SLA Compliance Checking (Option D): SD-WAN rules utilize SLA targets as a "pass/fail" gatekeeper. The engine checks if thepreferred membersmeet the defined SLA requirements (latency, jitter, or packet loss thresholds). If a preferred member fails the SLA, the rule will move to the next member in the priority list that does meet the SLA.
Single SLA Binding (Option E): When configuring an SD-WAN rule, the GUI and CLI allow you to selectmultiple SLA targets, but they must all belong to thesame Performance SLAprofile. You cannot mix and match targets from different health checks (e.g., Target 1 from "Google_HC" and Target 2 from "Amazon_HC") within a single SD-WAN rule.
Why other options are incorrect:
Option A: This is incorrect because a single SD-WAN rule can only be associated with one specific Performance SLA profile at a time; therefore, you cannot select targets fromdifferentSLAs.
Option C: This is incorrect because member metrics (latency, jitter, packet loss) are measured by thePerformance SLAprobes regardless of whether an SD-WAN rule is currently using that SLA target for steering decisions. Measurement is a function of the health-check, not the rule matching process.
Refer to the exhibits.
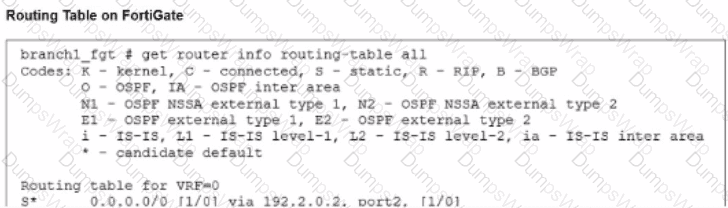
The administrator increases the member priority on port2 to 20. Upon configuration changes and the receipt of new packets, which two actions does FortiGate perform on existing sessions established over port2? (Choose two.)
Options:
FortiGate updates the gateway information of the sessions with SNAT so that they use port1 instead of port2.
FortiGate flags the SNAT session as dirty only if the administrator has assigned an IP pool to the firewall policies with NAT.
FortiGate routes only new sessions over port1.
FortiGate continues routing all existing sessions over port2.
FortiGate flags the sessions as dirty.
Answer:
A, EIn which order does a FortiGate device consider the following elements shown in the left column during the route lookup process?
Select the element in the left column, hold and drag it to a blank position in the column on the right. Place the four correct elements in order, placing the first element in the first position at the top of the column. Once you place an element, you can move it again if you want to change your answer before moving to the next question. You need to drop four elements in the work area.
Select and drag the screen divider to change the viewable area of the source and work areas.
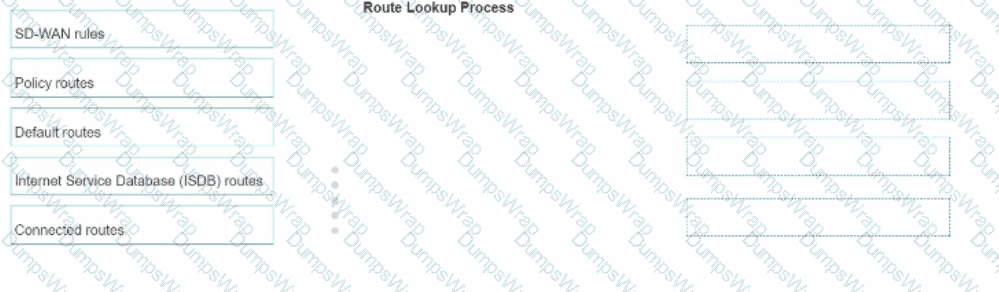
Options:
Answer:

Refer to the exhibit, which shows the SD-WAN rule status and configuration.
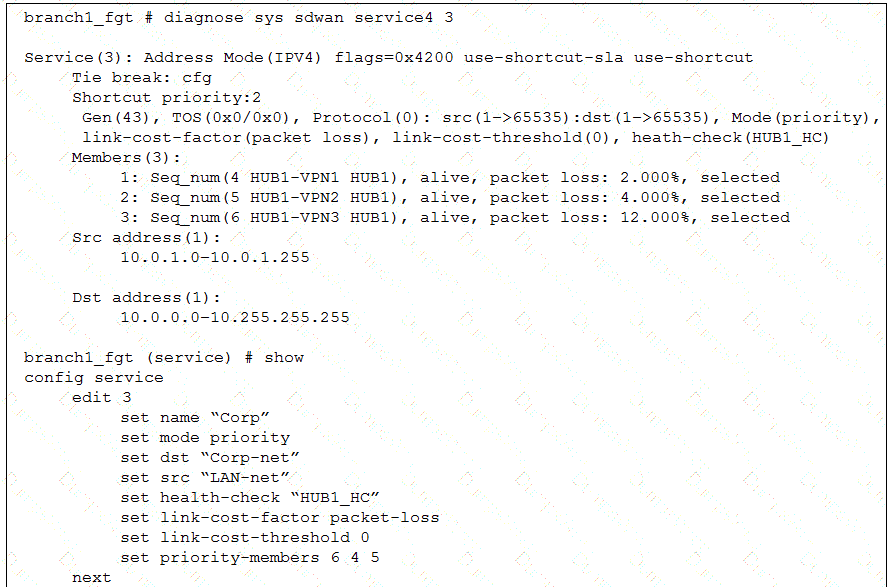
Based on the exhibit, which change in the measured packet loss will make HUB1-VPN3 the new preferred member? (Choose one answer)
Options:
When all three members have the same packet loss
When HUB1-VPN1 has 4% packet loss
When HUB1-VPN1 has 12% packet loss
When HUB1-VPN3 has 4% packet loss
Answer:
AExplanation:
According to theSD-WAN 7.6 Core Administratorstudy guide and theFortiOS 7.6 Administration Guide, the selection process for theBest Quality (priority)strategy depends on two primary factors: the measured link quality metric and the configured member priority order.
Based on the provided exhibit (image_b40dfc.png), we can determine the following:
Strategy and Metric: The rule is in Mode(priority) (Best Quality) using link-cost-factor(packet loss).
Strict Comparison: The link-cost-threshold is set to0. This means there is no "advantage" given to the current preferred link; the FortiGate performs a strict comparison where the link with the objectively best metric is chosen.
Tie-Breaker Logic: When multiple links have thesamepacket loss, the FortiGate uses theMember Priority Orderdefined in the rule (set priority-members 6 4 5) as the tie-breaker.
Member 6 (HUB1-VPN3)is the highest priority.
Member 4 (HUB1-VPN1)is the second priority.
Member 5 (HUB1-VPN2)is the lowest priority.
Current State: HUB1-VPN1 is currently selected because its packet loss (2.000%) is lower than HUB1-VPN2 (4.000%) and HUB1-VPN3 (12.000%). Even though HUB1-VPN3 has a higher configuration priority, its significantly higher packet loss prevents it from being chosen.
Evaluation of Options:
Option A (Verified): If all three members have thesame packet loss(e.g., they all show 2%), the quality metrics are equal. The SD-WAN engine then refers to the priority-members list. Since HUB1-VPN3 (Seq 6) is the first member in that list, it will immediately become the new preferred member.
Option B: If HUB1-VPN1 reaches 4%, it matches HUB1-VPN2 (4%). HUB1-VPN3 remains at 12%. The system will choose between VPN1 and VPN2. Since VPN1 (Seq 4) is higher in the priority list than VPN2 (Seq 5), HUB1-VPN1 stays preferred.
Option C: If HUB1-VPN1 reaches 12%, it matches HUB1-VPN3. However, HUB1-VPN2 is still better at4.000%. Therefore, HUB1-VPN2 would become the new preferred member, not HUB1-VPN3.
Option D: If HUB1-VPN3 drops to 4%, it matches HUB1-VPN2. However, HUB1-VPN1 is still the best link at2.000%, so it remains selected.
What is a key use case for FortiSASE Secure Internet Access (SIA) in an agentless deployment? (Choose one answer)
Options:
It provides secure web browsing by isolating browser sessions and enforcing data loss prevention for temporary employees.
It acts as a secure web gateway (SWG) distributing a PAC file for explicit web proxy use, securing HTTP and HTTPS traffic with a full security stack, and is ideal for unmanaged endpoints like contractors.
It distributes a PAC file to secure non-web traffic protocols and applies antivirus protection only for managed endpoints.
It requires FortiClient endpoints and supports ZTNA tags to secure all network traffic for unmanaged endpoints.
Answer:
BExplanation:
According to theFortiSASE 7.6 Administration Guideand theFCP - FortiSASE 24/25 Administratorcurriculum, the Agentless deployment mode—commonly referred to asSecure Web Gateway (SWG)mode—is a vital component of the Secure Internet Access (SIA) framework.
Deployment Mechanism: In an agentless deployment, FortiSASE functions as an explicit web proxy. This is achieved by distributing aPAC (Proxy Auto-Configuration) fileto the user's browser, which instructs the device to send its web traffic to the nearest FortiSASE Point of Presence (PoP).
Target Use Case: This mode is specifically designed forunmanaged endpoints, such as those used bycontractors, partners, or temporary workers, where the organization does not have the authority or capability to install the FortiClient agent.
Security Capabilities: Even without an agent, FortiSASE applies afull security stackto the redirected traffic. This includesWeb Filtering,Anti-Malware,SSL Inspection, andInline-CASBto secure HTTP and HTTPS sessions.
Protocol Limitations: Because it relies on proxy settings, this mode is limited to web protocols (HTTP/HTTPS) and does not inherently secure non-web traffic like ICMP, DNS, or custom TCP/UDP applications unless they are specifically proxied.
Why other options are incorrect:
Option A: While it provides secure browsing, session isolation (RBI) is a specific feature that can be used in either mode; the defining characteristic of the agentless use case is the proxy-based redirection for unmanaged devices.
Option C: A PAC file can only secure web traffic (protocols that support proxying), not non-web traffic protocols.
Option D: Agentless mode is the opposite of requiring FortiClient; ZTNA tags generally require the FortiClient agent to provide the necessary telemetry for tag evaluation.
You have a FortiGate configuration with three user-defined SD-WAN zones and one or two members in each of these zones. One SD-WAN member is no longer used in health-check and SD-WAN rules. This member is the only member of its zone. You want to delete it.
What happens if you delete the SD-WAN member from the FortiGate GUI?
Options:
FortiGate displays an error message. SD-WAN zones must contain at least one member.
FortiGate accepts the deletion and removes static routes as required.
FortiGate accepts the deletion with no further action.
FortiGate accepts the deletion and places the member in the default SD-WAN zone.
Answer:
BExplanation:
Questions no:9Verified Answer: B
Comprehensive and Detailed Explanation with all FortiSASE and SD-WAN 7.6 Core Administrator curriculum documents: According to theSD-WAN 7.6 Core Administratorstudy guide andFortiOS 7.6 Administration Guide, the behavior for deleting an SD-WAN member from the GUI when it is the only member in its zone is governed by the following operational logic:
Reference Checks: Before allowing the deletion of any SD-WAN member, FortiOS performs a "check for dependencies." If an interface is being used in an activePerformance SLAor anSD-WAN Rule, the GUI will typically prevent the deletion or gray out the option until those references are removed. However, the question specifies that this member isno longer usedin health-checks or rules.
Zone Integrity: Unlike some other network objects, an SD-WAN zone is permitted to exist without any members. When you delete the final member of a user-defined zone through the GUI, the zone itself remains in the configuration as an empty container.
Route Management: When an SD-WAN member is deleted, any static routes that were specifically tied to that interface's membership in the SD-WAN bundle are automatically updated or removed by the FortiGate to prevent routing loops or "black-holing" traffic. This is part of the automated cleanup process handled by the FortiOS management plane.
GUI vs. CLI: In the GUI, the process is streamlined to allow the removal of the member interface. Once the member is deleted, the interface returns to being a "regular" system interface and can be used for standard firewall policies or other functions.
Why other options are incorrect:
Option A: There is no requirement that a zone must contain at least one member; "empty" zones are valid configuration objects in FortiOS 7.6.
Option C: While the deletion is accepted, it is not with "no further action"—the system must still reconcile the routing table and interface status.
Option D: FortiGate does not automatically move deleted members into the default zone (virtual-wan-link). Once deleted, the interface is simply no longer an SD-WAN member.

