Fortinet NSE 6 - OT Security 7.6 Architect Questions and Answers
Refer to the exhibit.
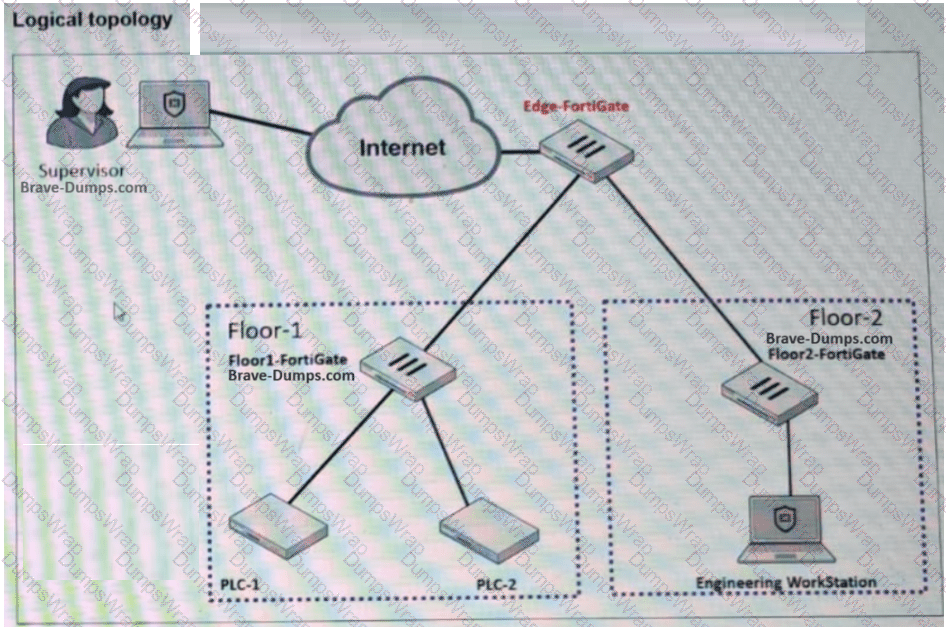
A partial OT network is shown. You want to provide the supervisor with secure remote access. Which two features can you implement on Edge-FortiGate ? (Choose two answers)
According to the IEC 62443 standard, your security level is 4 . What is your OT environment defending against? (Choose one answer)
Refer to the exhibit.
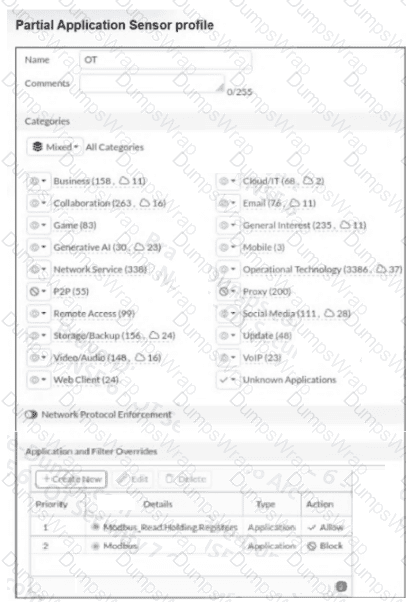
A partial Application Sensor profile is shown. When you apply this profile in firewall policy, which two statements are correct? (Choose two answers)
You would like to customize your current FortiAnalyzer report to provide a better risk assessment of your OT network. Which two options can you use to enhance your report? (Choose two answers)
Refer to the exhibit.
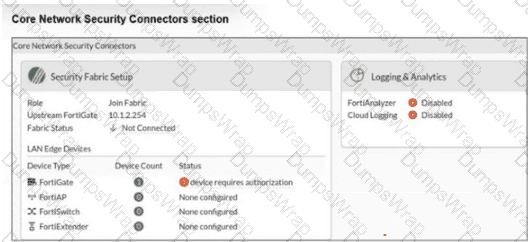
The Core Network Security Connectors page of the FortiGate-2 device is shown. Which statement is correct? (Choose one answer)
Refer to the exhibit.
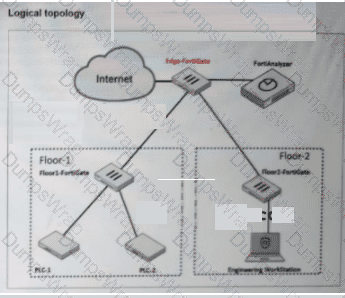
A partial OT network is shown. You want to configure an automated alert sent by FortiAnalyzer when an attack occurs on a FortiGate device. Which two configurations must you implement? (Choose two answers)
Refer to the exhibit.
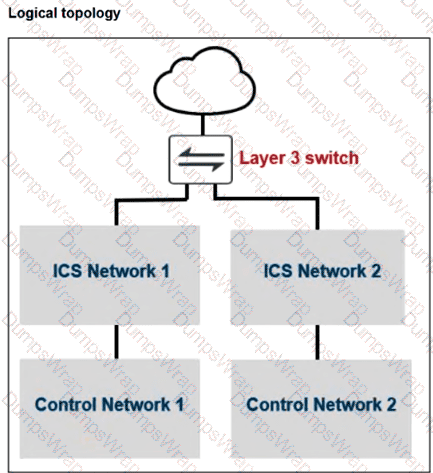
A partial OT network is shown. You must improve the security of this OT network and implement internal segmentation between network 1 and network 2. How can you achieve the segmentation? (Choose one answer)
For the installation of your first FortiGate device, you want to minimize the impact in your OT network. Therefore, you deploy it initially as an offline IDS. Which two statements about this deployment are correct? (Choose two answers)
During layer 2 polling , which two pieces of information are gathered by FortiNAC to identify a device? (Choose two answers)
What are two advantages provided by industrial Ethernet? (Choose two answers)
As the first step in your OT network protection plan, you must identify the OT protocols that the FortiGate device supports. Which two configurations must you implement on this FortiGate device? (Choose two answers)
You want to automate some tasks in your OT network. Which three configurations are directly available in a new basic event handler on FortiAnalyzer? (Choose three answers)
Refer to the exhibits.
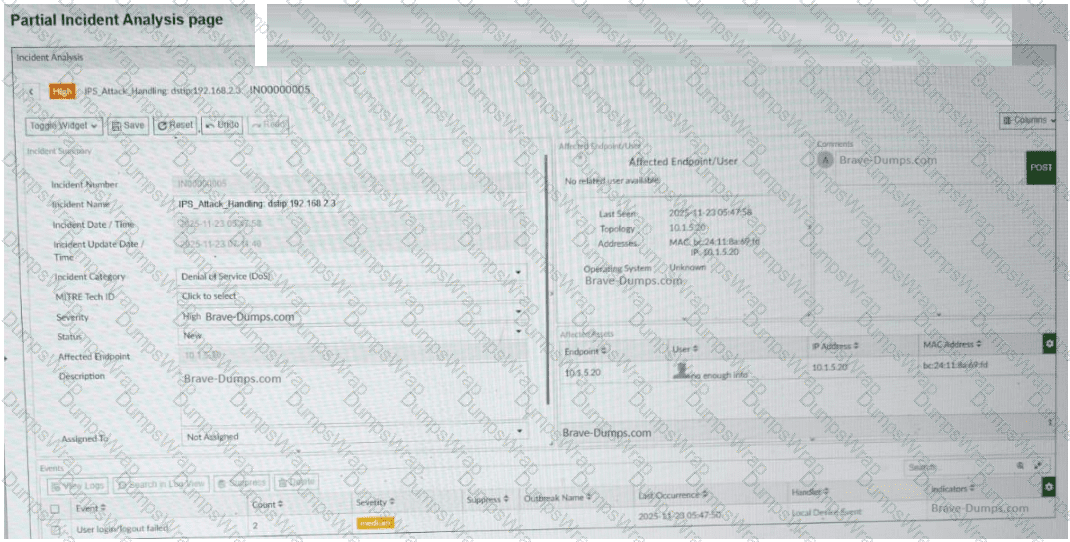
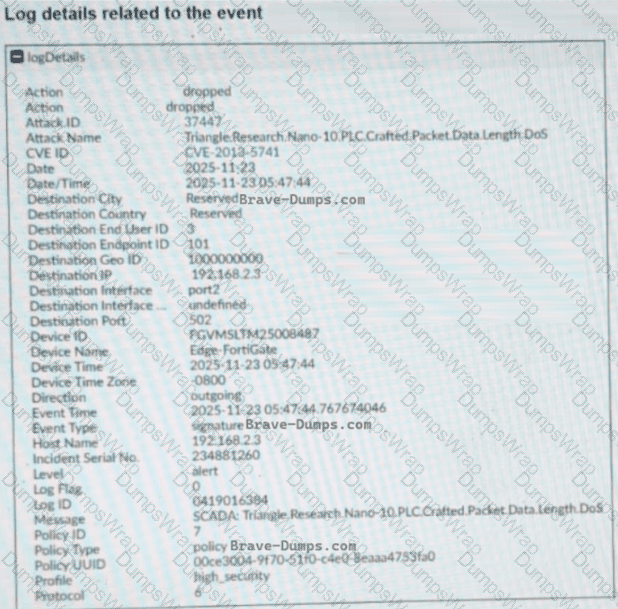
A partial Incident Analysis page and the log details related to the event are shown. An attack is reported on your OT network. You analyze the corresponding incident. Based on the information provided on the Incident Analysis page and the log details, which two statements are correct? (Choose two answers)

