HCIE-Datacom V1.0 Questions and Answers
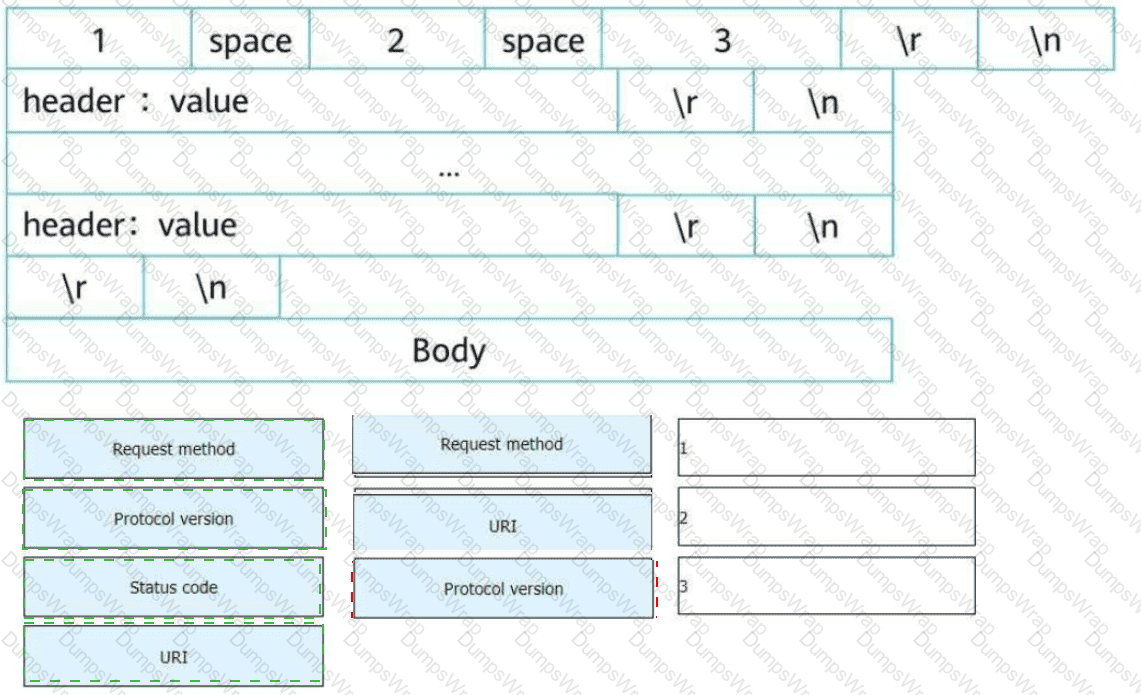
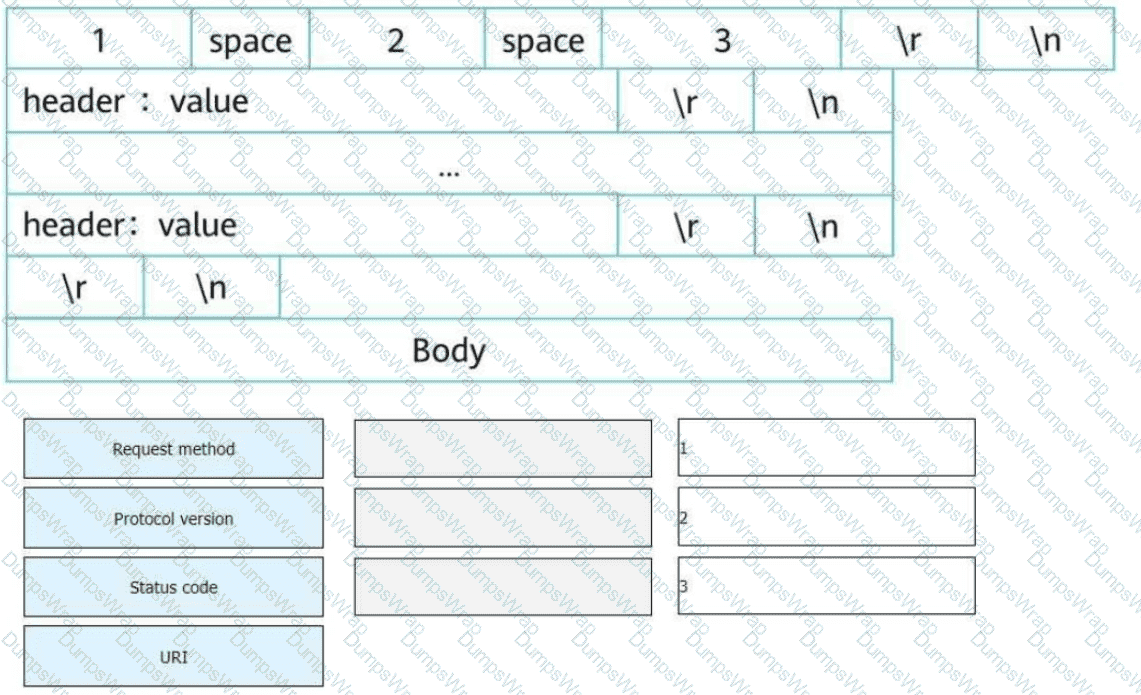
An HTTP request line consists of three fields. Select the fields to form a complete HTTP request message.
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following fields is not carried in BGP EVPN Type 2 routes?
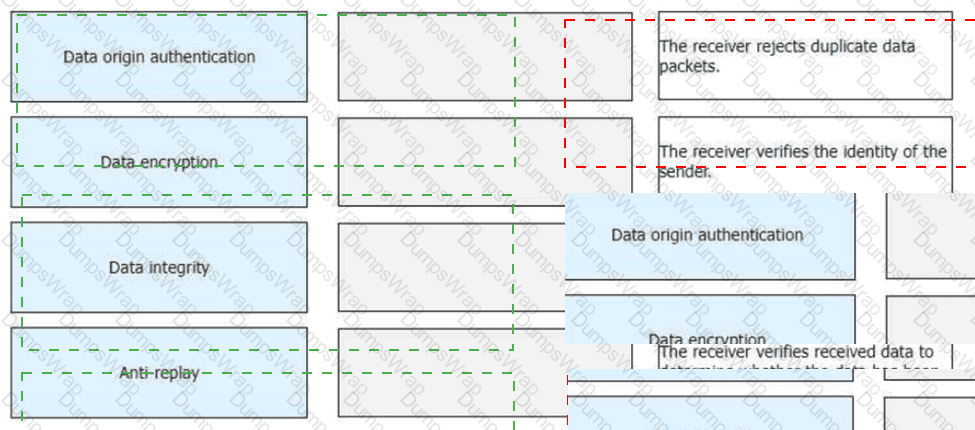
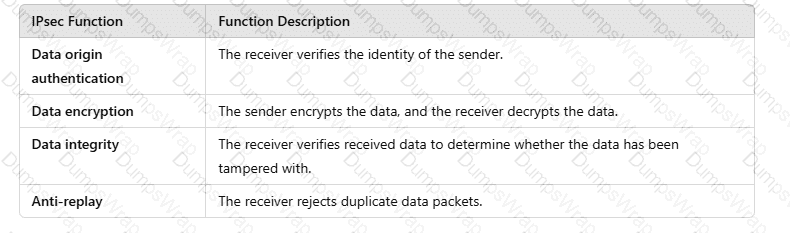
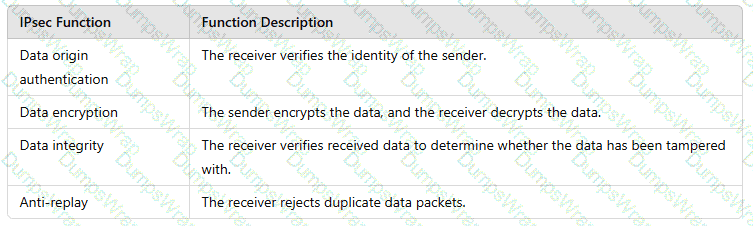
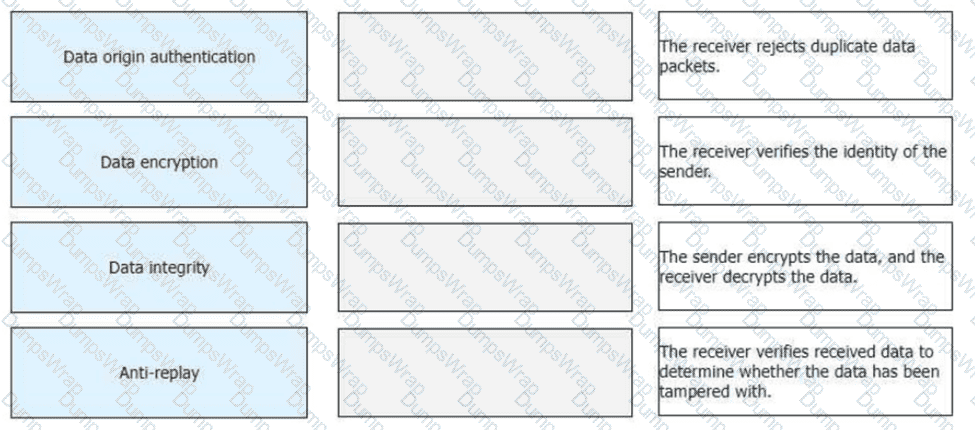
Drag the IPsec functions on the left to the corresponding function description on the right.
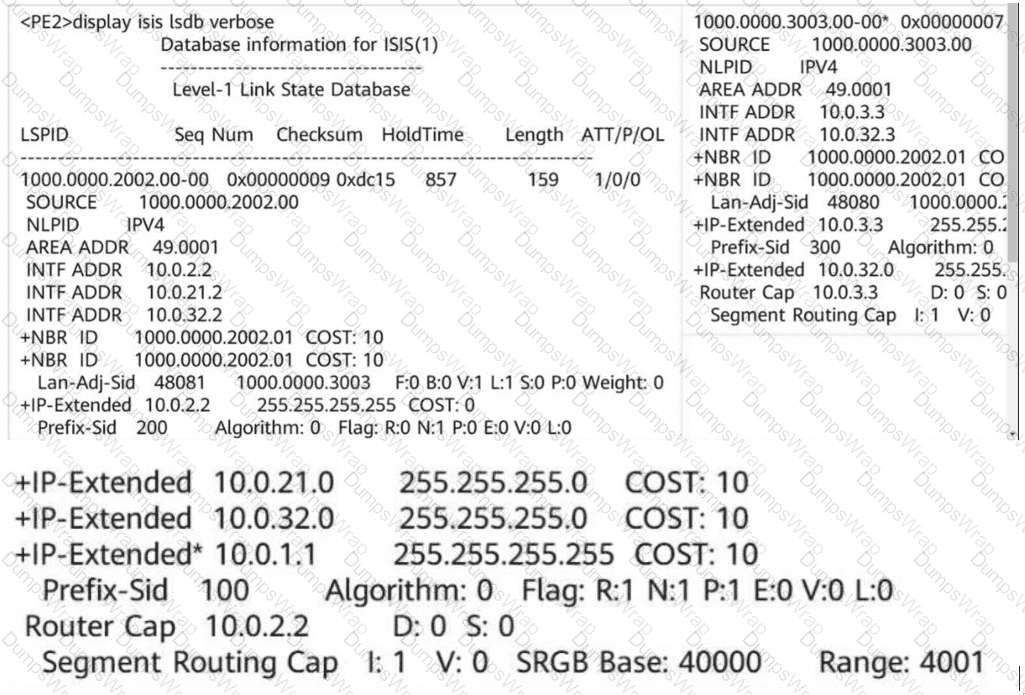
Refer to the output information of a device below. According to the information, which of the following MPLS labels is carried in a data packet forwarded by the device to 10.0.1.1?
When you configure a virtualized campus network on iMaster NCE-Campus, Fit APs can immediately go online after you add them to iMaster NCE-Campus.
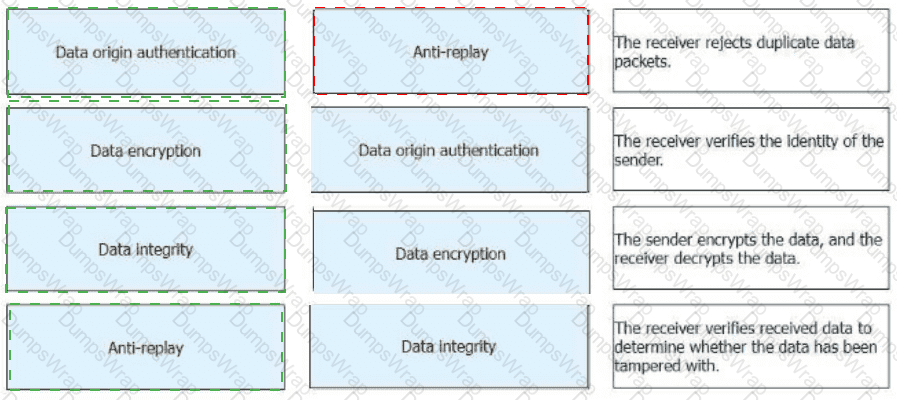
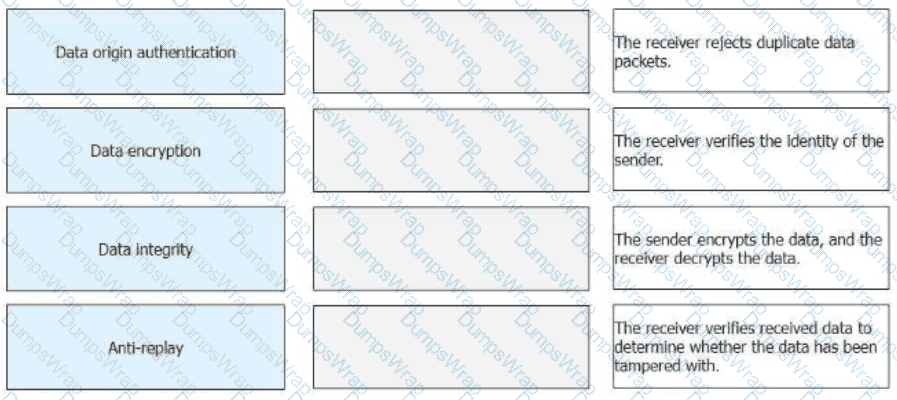
Drag the IPsec functions on the left to the corresponding function description on the right.
MPLS implements data forwarding based on two different planes. Which of the following statements regarding the forwarding mechanism are correct?
Which of the following statements about SR-MPLS Policy path planning are correct?
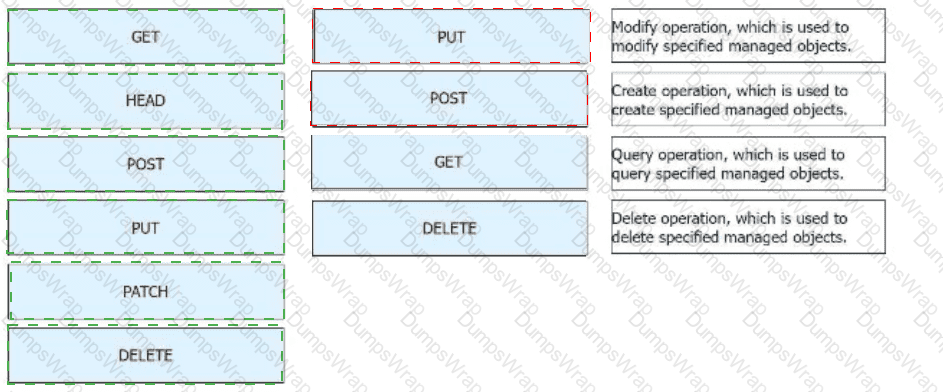
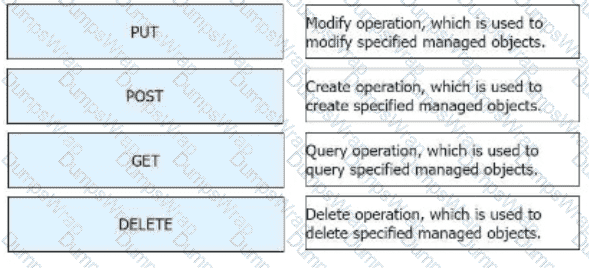
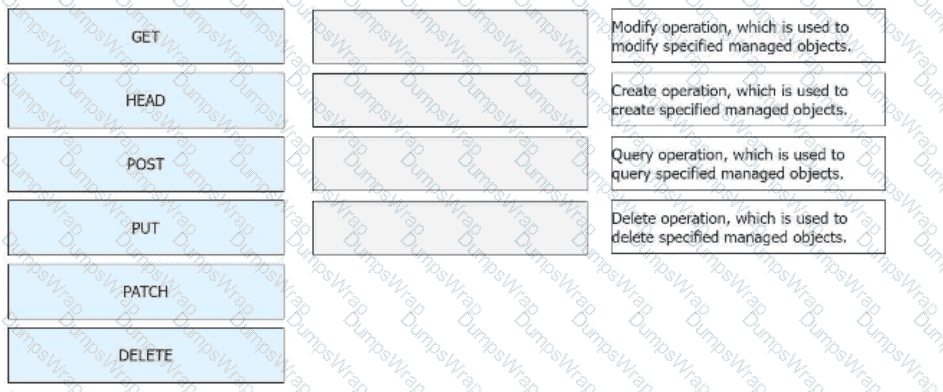
Huawei Open Programmability System (OPS) uses HTTP methods to access managed objects to manage network devices. Drag the HTTP methods to their corresponding functions.
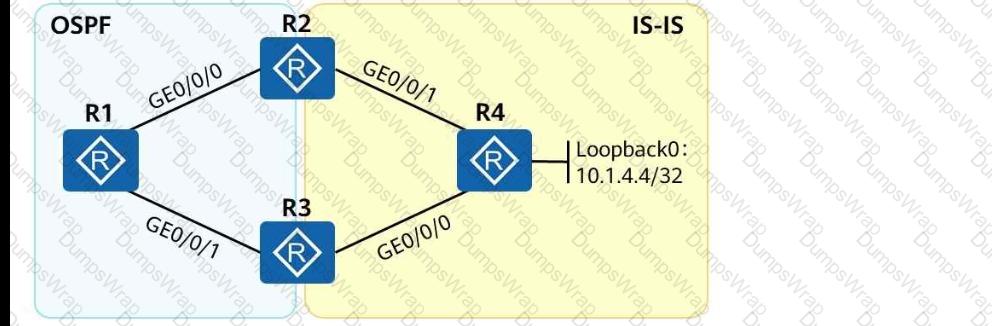
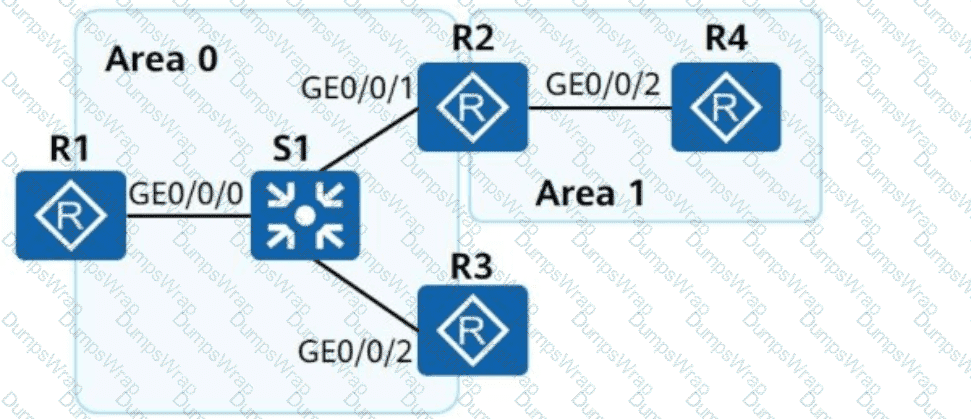
As shown in the following figure, an engineer tests network interconnection between two branches. To implement network interconnection, OSPF is deployed on R1, R2, and R3 of branch 1, and IS-IS is deployed on R2, R3, and R4 of branch 2. Which of the following operations needs to be performed to allow R1 to access R4 ' s loopback interface address?
VLAN-based MAC address flapping detection is configured. If MAC address flapping occurs, actions to be taken on an interface can be configured as required. Which of the following actions cannot be configured?
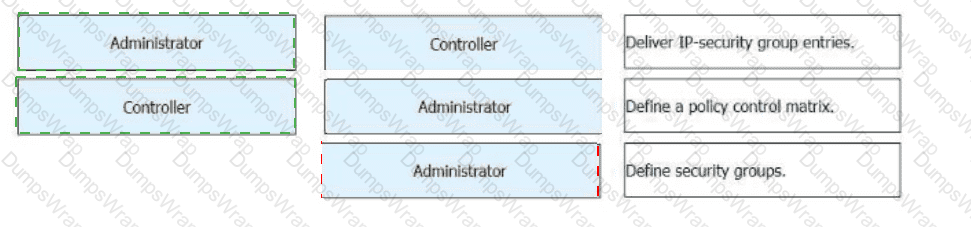
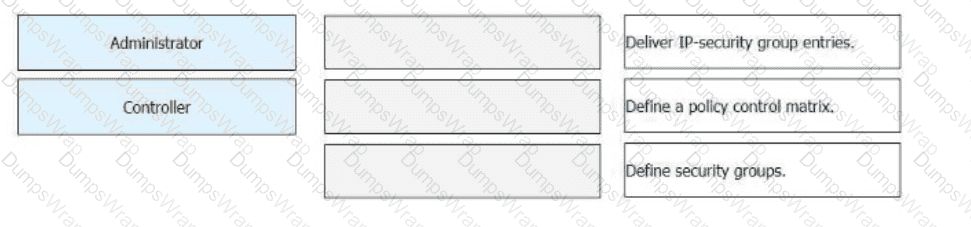
Free mobility is deployed on a campus network through iMaster NCE-Campus. During this deployment, which of the following steps are performed by administrators and which are automatically performed by iMaster NCE-Campus? Drag the administrators and iMaster NCE-Campus icons on the left to the corresponding steps on the right.
Which of the following statements about SR-MPLS characteristics are correct? (Select all that apply)
An LSR (Label Switching Router) supports various label retention modes. Which of the following statements regarding the liberal mode are correct?
As shown in the figure, what is known about the default routes on R4?
Routing Table on R4:
< R4 > display ip routing-table protocol isis
Destination/Mask Proto Pre Cost Flags NextHop Interface
0.0.0.0/0 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
172.16.1.2/32 ISIS-L1 15 10 D 10.1.24.1 GigabitEthernet0/0/1
172.16.1.3/32 ISIS-L1 15 10 D 10.1.34.1 GigabitEthernet0/0/0
Which of the following operations is not involved in the middle phase of a migration?
In SRv6, each time a packet passes through an SRv6 endpoint node, the Segments Left field value decrements by 1, and the IPv6 DA changes.
An SR-MPLS Policy needs to divert service traffic to a tunnel for forwarding. If traffic from various services is destined for the same address, which of the following traffic diversion modes is recommended to ensure the quality of each service?
As shown in the figure, when PE1 receives an ARP request packet, it forwards the packet to PE4. The packet then carries two labels. The label value 201 is carried by the EVPN Type ____ route. (Enter only digits.)
Which of the following commands needs to be run in the BGP view to enable a VPN instance to advertise IP routes to the BGP-EVPN address family?
Network Quality Analysis (NQA) is a real-time network performance detection and measurement technology. It monitors the performance of multiple protocols running on a network. Which of the following protocols can be monitored by NQA?
Which of the following statements about configuring user access authentication is incorrect?
OSPFv3 link LSAs are advertised in the entire area.
Which of the following types of LSAs does OSPF use to support SR-MPLS?
Which of the following issues do DiffServ model-based QoS have?
K company has two types of network services: UDP-based real-time video streaming services and TCP-based FTP download services. The company ' s network administrator often receives complaints that the FTP download speed is slow or unstable. What are the possible causes?
On a router, SRv6 is enabled, and the configurations shown below are performed. Which of the following statements about the configurations are correct?
[Router-segment-routing-ipv6] locator srv6_locator1 ipv6-prefix 2001:DB8:ABCD::/64 static 32
On a VXLAN-based virtualized network, if the fabric networking mode is centralized gateway networking, the gateway is located on the _____ device. (Capitalize the first letter.)
A network administrator needs to retrieve a token ID from iMaster NCE using the following Python code:
import requests
nbi_name = " demol3@north.com "
nbi_pwd = " qqcOVcVel@ "
host = " 139.9.213.72 "
port = " 18002 "
URI = " /controller/v2/tokens "
post_token_url = " " + host + " : " + port + URI
headers_post = { ' Content-Type ' : ' application/json ' , ' Accept ' : ' application/json ' }
r = requests.post(post_token_url, headers=headers_post, json={ " userName " : nbi_name, " password " : nbi_pwd}, verify=incorrect)
Which of the following statements is incorrect?
Which of the following statements is incorrect about the user authentication points on the network?
Refer to the following command output on the router R3. Which of the following statements are correct?
< R3 > display interface Tunnel
Tunnel0/0/0 current state : UP
Line protocol current state : UP
Last line protocol up time : 15:21:26 UTC-08:00
Description: HUAWEI, AR Series, Tunnel0/0/0 Interface
Route Port, The Maximum Transmit Unit is 1500
Internet Address is 20.1.1.2/24
Encapsulation is TUNNEL, loopback not set
Tunnel source 10.0.3.3 (LoopBack0), destination 10.0.1.1
Tunnel protocol/transport GRE/IP, key disabled
keepalive disabled
Checksumming of packets disabled
OSPF is a mature protocol and is unlikely to have route computation errors in a regular networking environment under correct configurations. Which of the following statements are correct about the possible causes preventing an OSPF neighbor relationship from entering Full state?
The following figure shows the inter-AS MPLS VPN Option B solution. If ASBR-PE1 and ASBR-PE2 only transmit VPNv4 routes, you can run the following command on ASBR-PE1:
[ASBR-PE1-bgp-af-vpnv4] undo peer 10.0.34.4 enable
On a CloudCampus virtualized campus network, which of the following modes can be used by a fabric to connect to external networks?
Which of the following statements is incorrect about intranet security design for a large or medium-sized virtualized campus network?
Huawei Open Programmability System (OPS) uses HTTP methods to access managed objects to manage network devices. To facilitate script compilation, Huawei OPS provides the Python script template. In the Python script template, what are the contents of the Content-type and Accept fields in the header of an HTTP request packet?
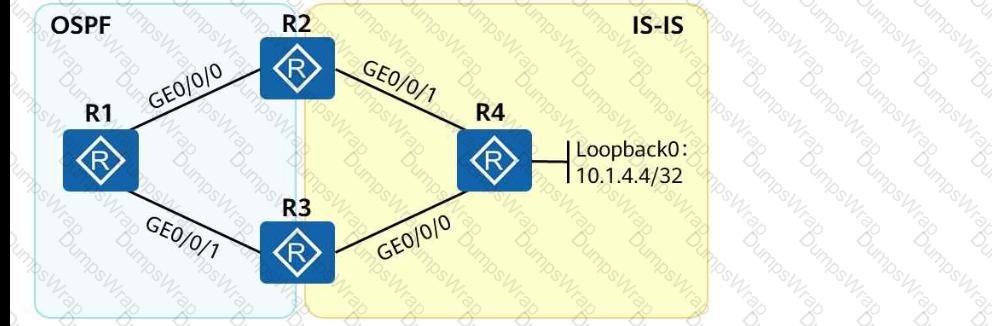
As shown in the following figure, an engineer tests network interconnection between two branches. To implement network interconnection, OSPF is deployed on R1, R2, and R3 of branch 1, and IS-IS is deployed on R2, R3, and R4 of branch 2. Which of the following operations needs to be performed to allow R1 to access R4 ' s loopback interface address?
When an SSH client logs in to an SSH server that is configured only with username and password authentication in SSH mode, the key exchange phase is not involved (no key is generated).
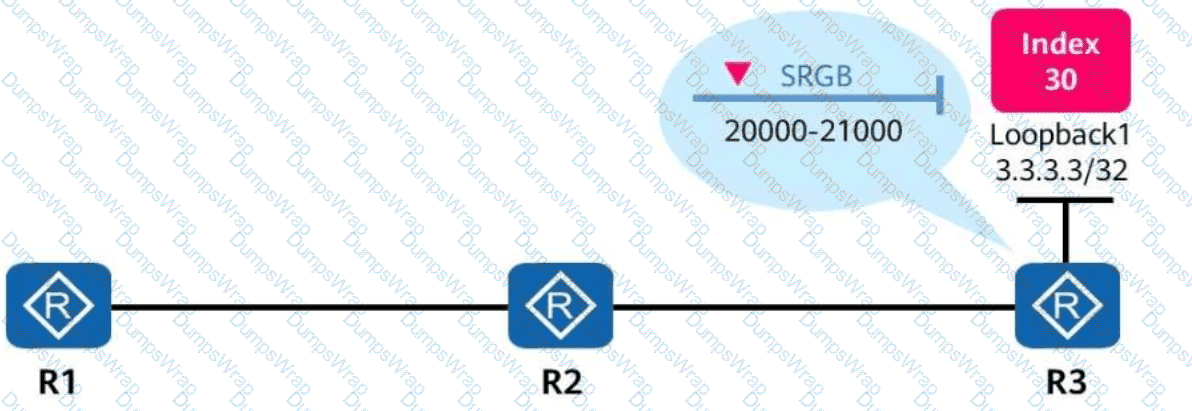
In the figure, SR-MPLS is enabled on R1, R2, and R3. The SRGB (Segment Routing Global Block) range on R3 is from 20000 to 21000, and the prefix SID index configured on the loopback1 interface of R3 is 30.
In this case, the MPLS label corresponding to the loopback1 interface of R3 is _____.
(Enter an Arabic numeral without symbols.)
The NETCONF content layer contains device configuration data.
Which of the following statements are correct about the following NETCONF configuration?
< ?xml version= " 1.0 " encoding= " UTF-8 " ? >
< rpc xmlns= " urn:ietf:params:xrnl:ns:netconf:base:1.0 " message-id= " 801 " >
< edit-config >
< target >
< running/ >
< /target >
< default-operation > merge < /default-operation >
< error-option > rollback-on-error < /error-option >
< config xmlns:xc= " urn:ietf:params:xml:ns:netconf:base:1.0 " >
< vlan xmlns= " " >
< vlans >
< vlan >
< vlanId > 10 < /vlanId >
< protocolVlans >
< protocolVlan xc:operation= " merge " >
< protocolIndex > 0 < /protocolIndex >
< /protocolVlan >
< /protocolVlans >
< /vlan >
< /vlans >
< /vlan >
< /config >
< /edit-config >
< /rpc >
Which of the following statements about OPS (Open Programmability System) application scenarios is incorrect?
Congestion management technology can be used to discard data packets in the buffer queue to prevent the buffer queue from being exhausted.
Which of the following statements about IPSG is incorrect?
In a scenario where a VXLAN tunnel is dynamically established through BGP EVPN, which of the following statements about symmetric IRB forwarding are correct?
NETCONF provides a set of mechanisms for managing network devices. What layers can NETCONF be conceptually partitioned into?
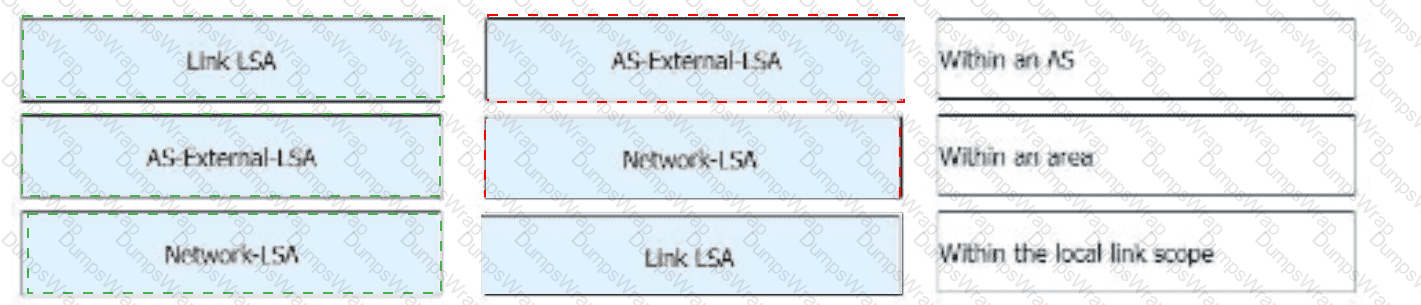
In OSPFv3, which of the following LSAs can be flooded within an area?
Which of the following statements is incorrect about intranet security design for a large or medium-sized virtualized campus network?
An Ethernet Segment Identifier (ESI) is 10 bytes long and unique on the entire network.
On traditional campus networks, network admission control (NAC), VLAN, and ACL technologies are used to control users ' network access rights. This results in heavy network O & M workload. Which of the following improvements does the free mobility solution of iMaster NCE-Campus make to traditional campus networks in terms of policy management and control?
BGP EVPN can be used as the VXLAN control plane protocol to completely prevent traffic flooding, such as broadcast ARP packets, on the VXLAN network.
gRPC (Google Remote Procedure Call) is a language-neutral, platform-neutral, and open-source remote RPC system that supports unary RPCs and streaming RPCs.
Which of the following service methods are NOT supported by gRPC?
Which of the following is the drop probability of packets exceeding the upper threshold in WRED?
On the campus network shown, IPv6 is deployed for service tests. Four routers are deployed on the network, and these routers use OSPFv3 for network connectivity. Which of the following statements about LSAs generated by the OSPFv3 network is incorrect?
In an MPLS VPN network, two-layer MPLS labels are added into data packets before they are transmitted over the public network. Which of the following statements regarding data packet processing are correct?
Which of the following commands are mandatory for configuring an OSPF-based SR-MPLS TE tunnel? (Select All that Apply)
O & M personnel for a large-scale event center receive feedback about Wi-Fi access failures. iMaster NCE-CampusInsight provides the function for personnel to view packet exchange processes and locate the root cause. It is found that IP addresses in the DHCP address pool are exhausted, preventing IP addresses from being assigned to mobile terminals. Which of the following functions is used by O & M personnel in this scenario?
Which of the following protocols is used in the Huawei SD-WAN Solution to report device performance data?
Which of the following statements is incorrect about MP-BGP?
In the firewall hot standby scenario, which of the following status information can be backed up between the active and standby firewalls?
Man-in-the-middle attacks (MITM) or IP/MAC Spoofing attacks are common on intranets and can cause information leakage.
Which configuration method can prevent these attacks?
In DU label advertisement mode, if the liberal label retention mode is used, the device reserves labels received from all the LDP peers regardless of whether the LDP peer is the optimal next hop for reaching the destination network.
A carrier ' s home broadband service requires a maximum downstream bandwidth of 100 Mbit/s during off-peak hours and a guaranteed downstream bandwidth of 50 Mbit/s during peak hours. The home broadband service includes the home IP phone service and the home Internet access service. Which of the following configurations best meets the service requirement?
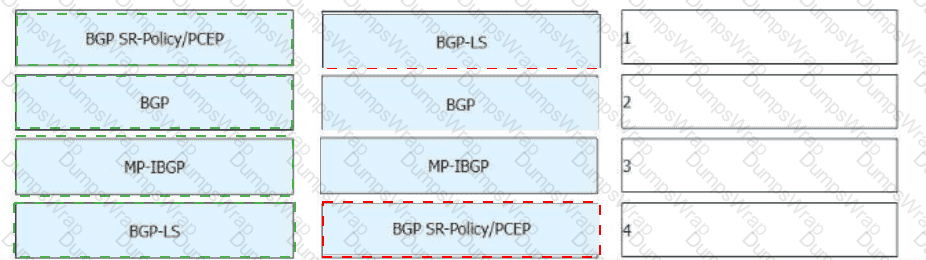
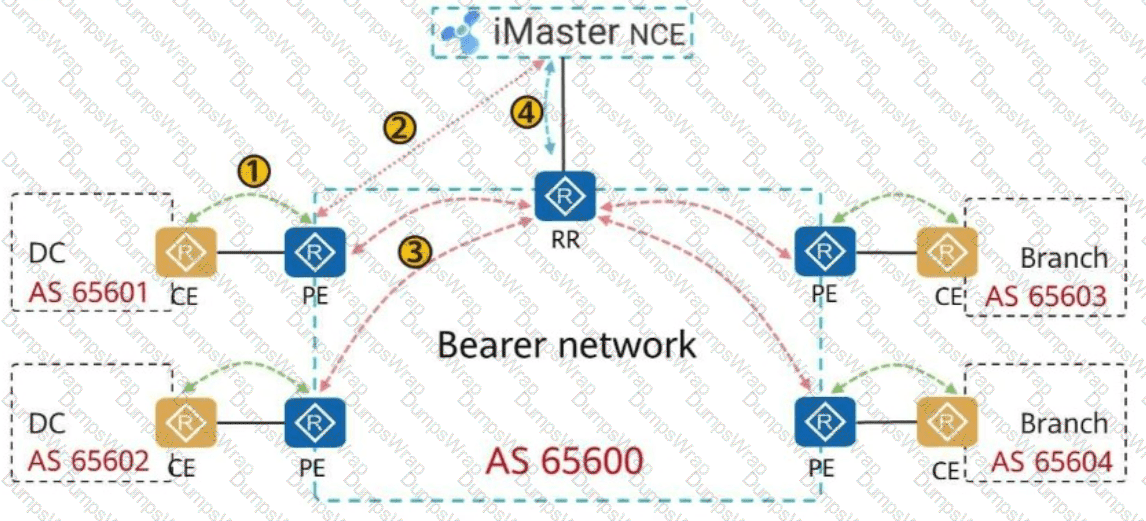
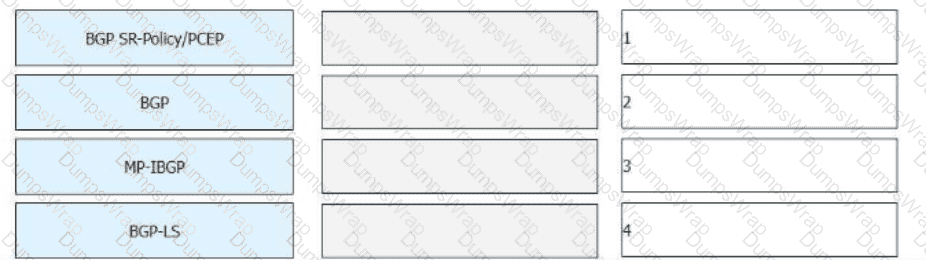
On the bearer WAN shown in the figure, SR (Segment Routing) is deployed, and the controller is used to compute paths. Drag network technologies on the left to the corresponding application locations on the right.
HTTP/2 is a UDP-based low-delay Internet transport layer protocol.
The TTL field encapsulated in the MPLS label header can prevent infinite loops of MPLS packets. Which of the following statements regarding the TTL field are correct?
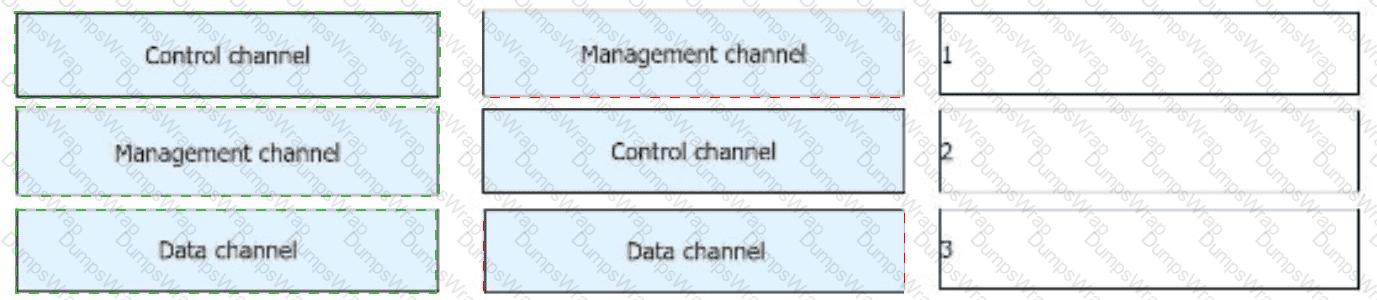
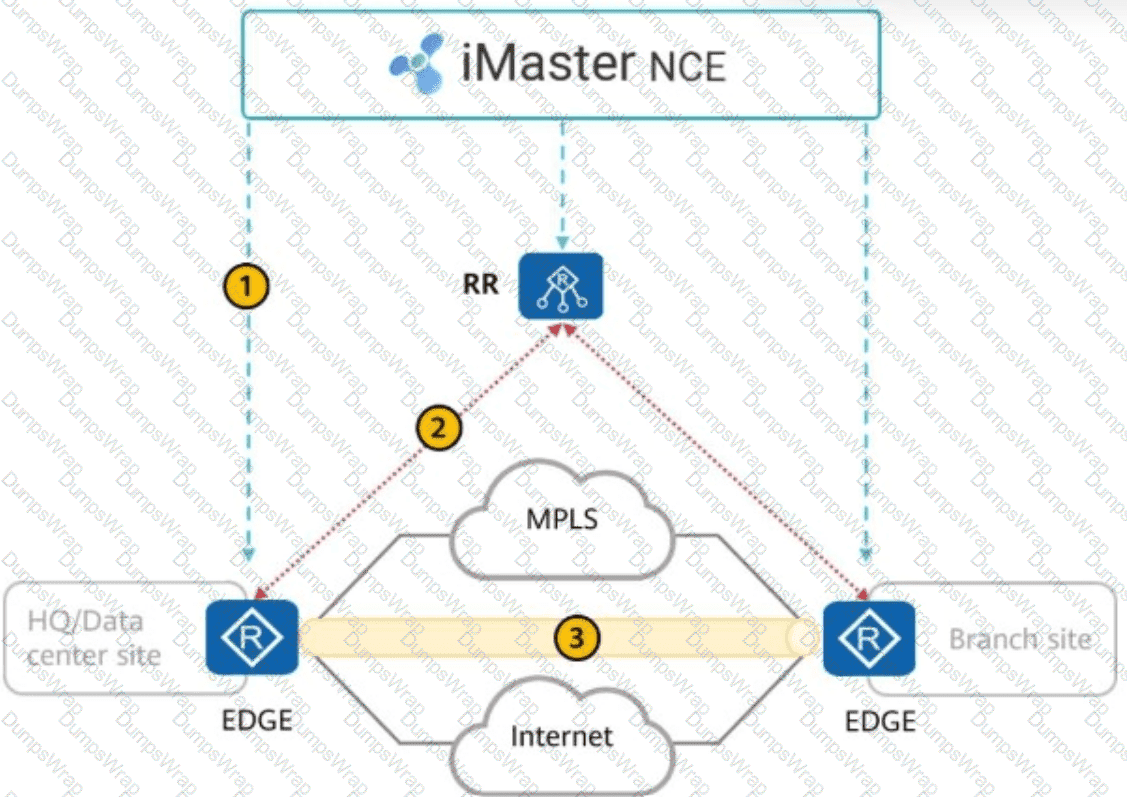
The Huawei SD-WAN solution has three types of channels. Drag the channel names to their corresponding callouts.
Which of the following statements about the multicast address used by OSPFv3 are correct?
When a client invokes the iMaster NCE-Campus RESTful API, it sends an HTTP request. The server then returns the status code 401. Which of the following errors has occurred?
Based on the configuration in the following figure, how many interfaces on R4 are advertised into IS-IS?
plaintext
CopyEdit
< R4 > display isis interface
Interface information for ISIS(1)
Interface Id IPV4.State IPV6.State MTU Type DIS
GE0/0/0 001 Up Down 1497 L1/L2 No/No
GE0/0/1 002 Up Down 1497 L1/L2 No/No
Loop0 001 Up Down 1500 L1/L2 -
IS-IS supports multi-instance and multi-process. Which of the following statements are correct about IS-IS multi-instance and multi-process?
Port isolation can be deployed on an Ethernet network to implement both Layer 2 communication and Layer 3 isolation, making the networking more flexible.
The Ingress VTEP performs both Layer 2 and Layer 3 table lookup for packet forwarding. The forwarding mode is ______ IRB forwarding. (Capitalize the first letter.)
There are multiple SR-MPLS TE tunnel protection mechanisms. FRR (Fast Reroute) constructs a virtual node to convert multiple identical route advertisement nodes into a single route advertisement node, and then computes the backup next hop of the virtual node based on the TI-LFA algorithm. In this way, traffic can be quickly switched when a fault occurs.
What is the name of this protection mechanism?
To prevent hackers from attacking user devices or networks using MAC addresses, you can configure MAC addresses of untrusted users as blackhole MAC addresses to filter out such invalid MAC addresses. When receiving a packet whose source or destination MAC address is a blackhole MAC address on a device, the device discards the packet.
iMaster NCE-Campus provides the terminal identification function to display the terminal type, operating system, and manufacturer information.
Python Paramiko implements the SSH protocol. In the Python Paramiko module, which of the following classes is used to create SFTP sessions and perform remote file operations?
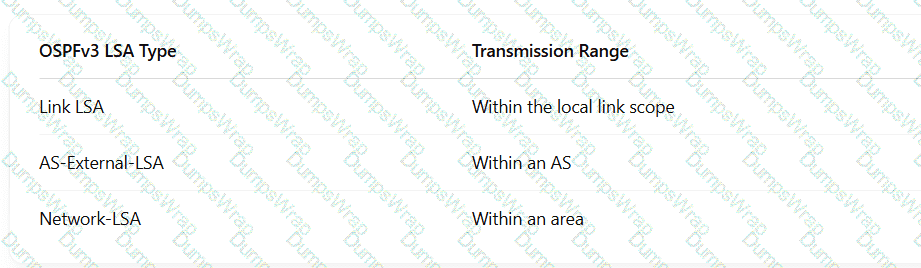
Drag the OSPFv3 LSAs to map them to their corresponding transmission ranges.

A network administrator runs the display telemetry destination command on a device to check information about a destination group that sampled data is sent to. The command output is as follows. Which of the following statements is incorrect?
[~CE-telemetry-sensor-group-Sensor1]display telemetry destination
Dest-name Dest-addr Dest-port State Vpn-name Protocol
Dest1 192.168.56.1 20000 RESOLVED - GRPC
The RR (Route Reflector) is critical to the Huawei SD-WAN Solution, and its deployment mode varies based on the scenario. In which of the following modes can an RR be deployed?
An SRv6 Policy can be either statically configured on a device or dynamically generated by the controller and then delivered to the device.
On a CloudCampus virtualized campus network, virtual networks are defined based on services. Each virtual network corresponds to a service, and isolation needs to be manually configured between virtual networks.
Which of the following parameters is not included in an IPsec security association (SA)?
In the following figure, a GRE tunnel is established between R1 and R2. If the command ping -a 10.1.1.1 10.3.1.1 is run on R1, which of the following statements is correct about the ICMP packet sent by GE0/0/1 of R1?
Portal authentication is recommended for scenarios with high mobility and numerous terminal types, such as shopping malls and supermarkets. MAC address authentication is recommended for dumb terminals that do not support Portal authentication, such as printers, fax machines, and IP phones.
When an NVE encapsulates a data frame into a VXLAN packet, information of which of the following protocols is encapsulated between the outer IP header and the VXLAN header?
Which of the following statements is correct about the differences between NSR and NSF?
For telemetry data push, data can be transferred between devices and collectors using the TLS protocol. TLS must be configured for data encryption if data is pushed based on gRPC.
A VGMP packet is encapsulated with a UDP header and a VGMP header. By default, a VGMP packet uses UDP port _____.
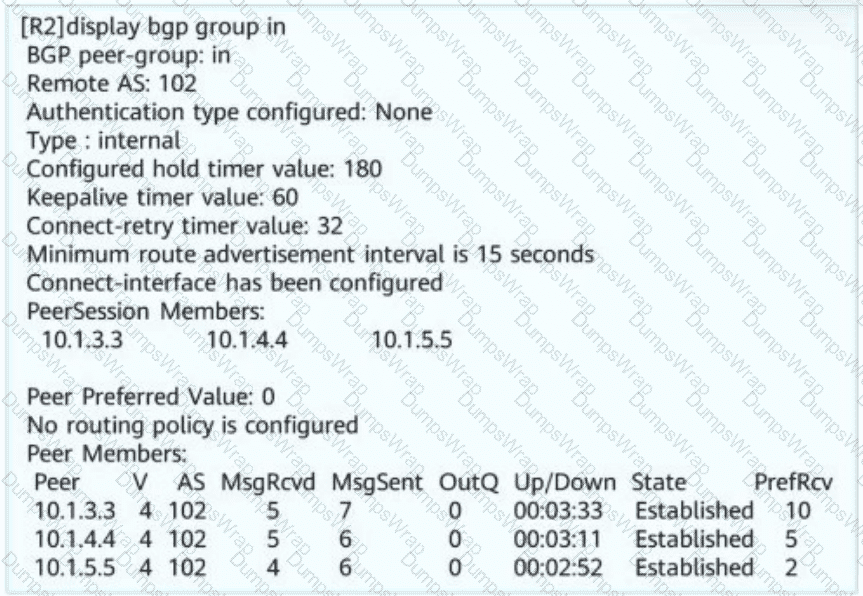
Network administrator A wants to view the BGP peer status of R2. The BGP peer status of R2 is shown in this figure. Obtain the following information: R2 resides in AS _____ (Enter only digits. Do not add punctuations or spaces.)
When MPLS/BGP IP VPN is deployed, which of the following statements is incorrect about BGP route exchange between PEs and CEs?
Based on the figure, which of the following statements are correct?
< R1 > tracert 172.17.1.5
1 10.1.12.2 40 ms 10 ms 10 ms
2 10.1.24.2 30 ms 20 ms 20 ms
3 10.1.34.1 20 ms 20 ms 20 ms
4 10.1.13.1 20 ms 20 ms 10 ms
5 10.1.12.2 20 ms 30 ms 20 ms
6 10.1.24.2 30 ms 30 ms 30 ms
7 10.1.34.1 50 ms 40 ms 40 ms
8 10.1.13.1 20 ms 30 ms 30 ms
Which of the following roles is NOT a core role in Huawei ' s Free Mobility solution?
Which of the following inter-AS MPLS L3VPN solutions need VPN user data packets to carry MPLS labels when being forwarded between ASs?
SSH connections are usually established based on TCP/IP connections. In specific cases, SSH connections can be established based on UDP connections.
Which of the following statements is incorrect about a BGP/MPLS IP VPN?
Huawei Open Programmability System (OPS) uses HTTP methods to access managed objects to manage network devices. HTTP is the most widely used network transmission protocol on the Internet. By default, the TCP port number _____ is used. (Fill in Arabic numerals.)