Microsoft Security Compliance and Identity Fundamentals Questions and Answers
Select the answer that correctly completes the sentence.
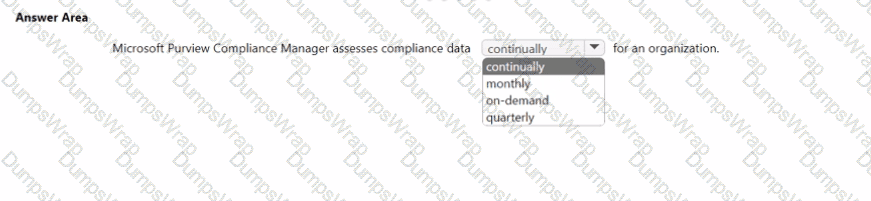
Options:
Answer:
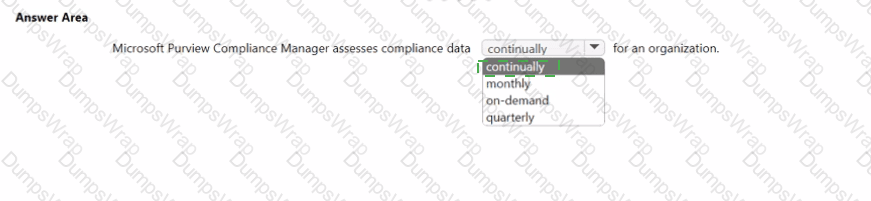
Explanation:
Microsoft Purview Compliance Manager is designed to give organizations a continuous view of their compliance posture. In Microsoft’s Security, Compliance, and Identity guidance, Compliance Manager is described as a capability that assesses your compliance posture against regulatory standards and data protection baselines and updates the compliance score as you implement or fail controls. The platform aggregates signals from assessments, controls, and improvement actions, then recalculates your compliance score as evidence is collected and actions are marked complete or tested. Because these evaluations are tied to live improvement actions and mapped controls (such as access, data protection, and governance controls), your organization’s status isn’t limited to a fixed reporting cycle; rather, it reflects ongoing progress and gaps across supported regulations and standards.
SCI study materials also emphasize that the score is not a one-time audit: it’s a running indicator of risk reduction and control implementation. As you address recommendations, add or update evidence, or connect automated tests where available, the score and related dashboards refresh to show the latest compliance state. This makes Compliance Manager suitable for continuous assessment, enabling organizations to monitor posture, prioritize work, and demonstrate incremental improvements over time—hence, it assesses compliance data continually for an organization.
Which two Azure resources can a network security group (NSG) be associated with? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
Options:
a network interface
an Azure App Service web app
a virtual network
a virtual network subnet
a resource group
Answer:
A, DExplanation:
You can use an Azure network security group to filter network traffic to and from Azure resources in an Azure virtual network. A network security group contains security rules that allow or deny inbound network traffic to, or outbound network traffic from, several types of Azure resources.
Match the types of compliance score actions to the appropriate tasks.
To answer. drag the appropriate action type from the column on the left to its task on the right. Each type may be used once. more than once, or not at all.
NOTE: Each correct match is worth one point.
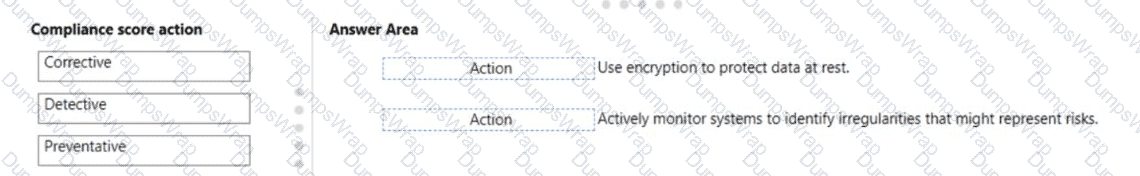
Options:
Answer:
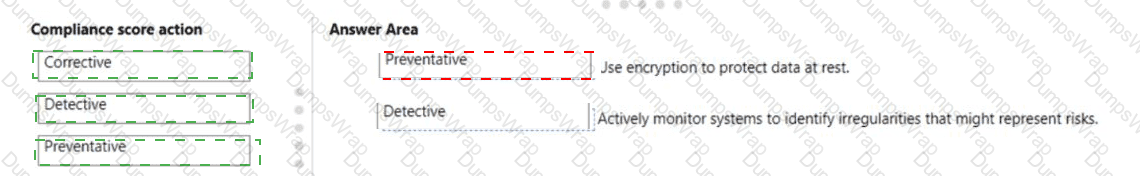
Explanation:
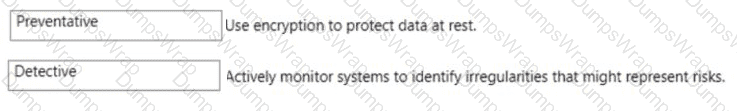
In Microsoft Purview Compliance Manager, improvement actions are categorized by control type to reflect how they reduce risk and contribute to your compliance score. Microsoft’s SCI guidance explains that preventative controls are safeguards that “prevent a security or compliance incident from occurring by enforcing protections in advance (for example, enforcing encryption of data at rest and in transit, access restrictions, and configuration baselines).” This directly aligns with the task “Use encryption to protect data at rest”, which is a classic prevention mechanism intended to stop unauthorized disclosure before it can happen.
The guidance also states that detective controls are measures that “identify, log, and surface anomalous or non-compliant activities so they can be investigated and addressed (for example, continuous monitoring, alerting, audit logging, and analytics).” This maps to “Actively monitor systems to identify irregularities that might represent risks”, because the goal is to detect suspicious behavior or drift as it occurs.
By comparison, corrective controls are used to “remediate issues and restore a desired state after a problem is discovered (for example, patching, incident response, or configuration correction).” No corrective action is described in the two listed tasks, so Corrective is not selected. This mapping reflects how Compliance Manager classifies actions that contribute points to the compliance score based on their risk-reducing impact.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
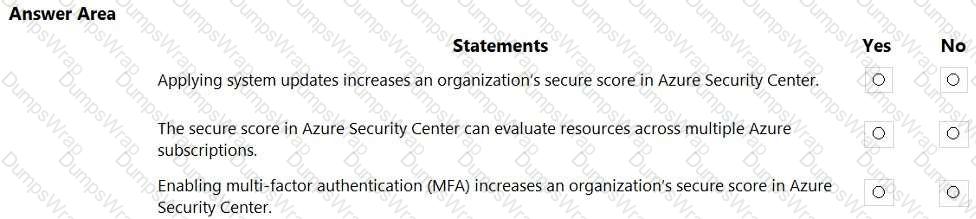
Options:
Answer:
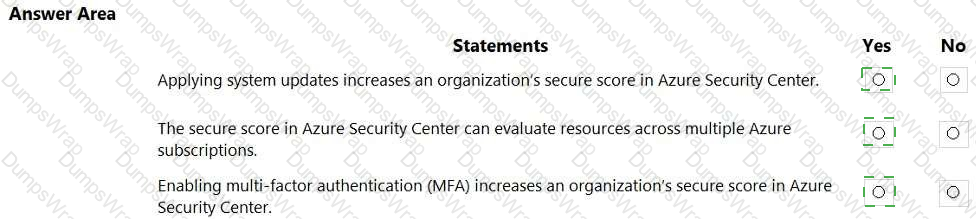
Explanation:
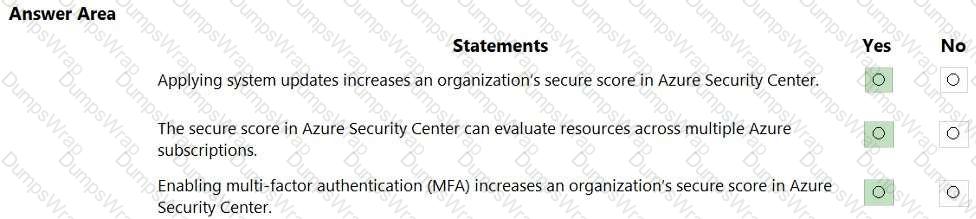
In Microsoft Defender for Cloud (formerly Azure Security Center), Secure score is defined as “a measurement of an organization’s security posture; the higher the score, the lower the identified risk.” Microsoft states that Defender for Cloud provides security recommendations that “help you harden your resources and increase your secure score.” Among these recommendations is “Apply system updates” for virtual machines—Microsoft describes it as ensuring that “machines should have the latest security updates installed”, and completing this action adds points to your secure score because it remediates a vulnerability class (missing patches).
Defender for Cloud also supports wide scope evaluation: you can “view and manage the secure score across subscriptions and management groups,” allowing organizations with multiple Azure subscriptions to see an aggregated and per-scope score and track improvement actions consistently.
Identity protections are part of Defender for Cloud’s recommendations as well. Under the Azure Security Benchmark controls, Defender for Cloud includes the recommendation that “MFA should be enabled on accounts with owner permissions on your subscription.” Implementing this MFA control earns secure-score points because it mitigates high-impact identity risks.
Therefore, applying system updates (Yes), evaluating across multiple subscriptions (Yes), and enabling MFA (Yes) all increase or contribute to an organization’s secure score in Azure Security Center/Defender for Cloud.
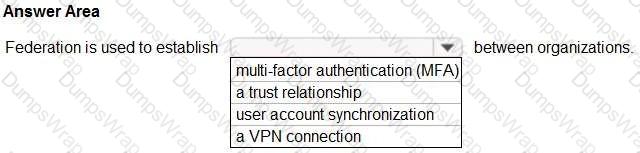
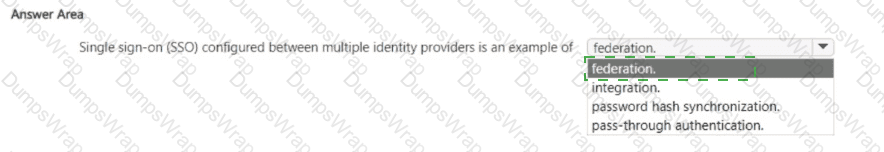
Select The answer that correctly completes the sentence.
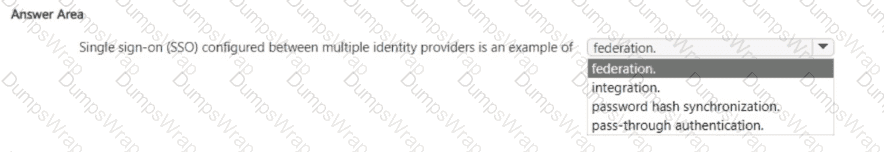
Options:
Answer:
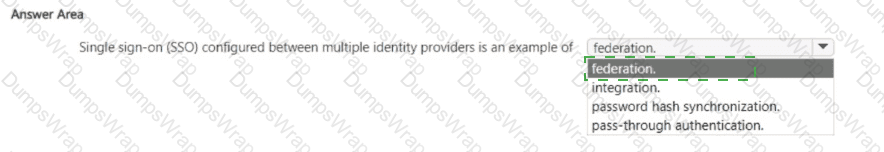
Explanation:

In Microsoft identity and access management terminology, federation refers to the establishment of a trust relationship between identity providers, which enables single sign-on (SSO) across different organizations or platforms.
According to the Microsoft Security, Compliance, and Identity (SCI) learning path, particularly in the SC-900 and SC-300 certifications, the following definition is provided:
“Federation is a means of establishing trust between two identity systems. This trust allows users from one domain to access resources in another domain without needing to authenticate again, typically using SAML, WS-Federation, or OAuth protocols.”
This concept is essential in cross-organization SSO scenarios, such as enabling users from one enterprise (or identity provider) to authenticate with services hosted in another, using existing credentials.
SCI documentation further states:
“Single sign-on (SSO) between multiple identity providers is enabled through federation protocols, which delegate authentication and allow token-based identity propagation across systems.”
The other options are not accurate in this context:
Integration is a vague term and not specific to SSO configuration.
Password hash synchronization and pass-through authentication are Azure AD authentication methods used for hybrid identity with on-premises AD, not for federating with external identity providers.
✅ Therefore, SSO configured between multiple identity providers is best classified as an example of federation.
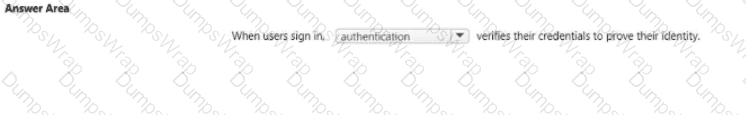
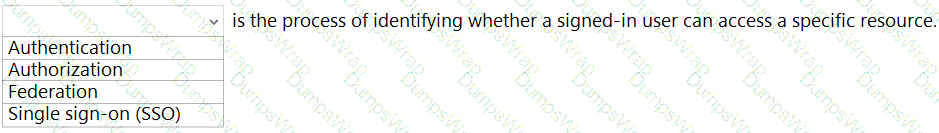
Select the answer that correctly completes the sentence.
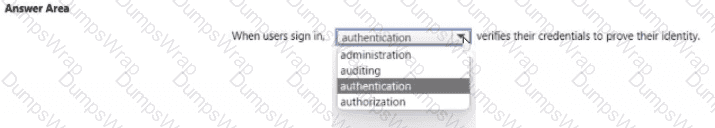
Options:
Answer:

Explanation:
In Microsoft identity terminology, authentication is the step that proves who the user is when they attempt to sign in. Microsoft Learn defines it plainly: “Authentication is the process of proving the identity of a user, device, or service.” By contrast, “Authorization is the process of determining what a user, device, or service can do.” During sign-in to Microsoft Entra ID (formerly Azure AD), “the identity provider validates credentials and, upon successful authentication, issues tokens that applications use to grant access.” Microsoft further explains the available methods: “Microsoft Entra ID supports multiple authentication methods, including passwords, multi-factor authentication, FIDO2 security keys, certificate-based authentication, and federated authentication.”
Auditing and administration are not the mechanisms that verify identity at sign-in. Auditing “records security-relevant events for investigation and compliance,” while administration “refers to configuring and managing identities, access policies, and settings.” Therefore, in the sentence “When users sign in, _____ verifies their credentials to prove their identity,” the correct completion is authentication, because it is the control that validates the user’s credentials and establishes identity before any authorization decisions are made.
Select the answer that correctly completes the sentence.
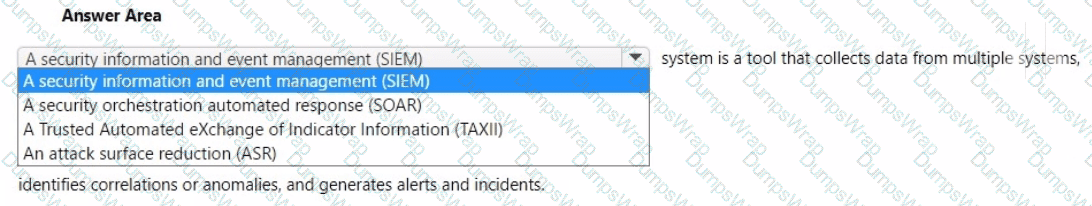
Options:
Answer:

Explanation:
A Security Information and Event Management (SIEM) system is designed to collect and aggregate security data from multiple sources—such as servers, devices, applications, and security appliances—across an organization. It then analyzes the data for anomalies, correlations, and patterns that could indicate potential threats or breaches.
From the SCI certification learning paths, especially SC-200 (Microsoft Security Operations Analyst), Microsoft defines SIEM as follows:
“SIEM tools collect and analyze activity from multiple resources across your IT infrastructure. Microsoft Sentinel is Microsoft’s cloud-native SIEM that provides intelligent security analytics and threat intelligence to help detect and respond to security threats.”
A SIEM system:
Ingests large volumes of data (logs, events).
Uses built-in rules, AI, and analytics to identify threats.
Correlates alerts from various sources to form incidents.
Generates alerts and dashboards for security analysts.
Microsoft Sentinel, as Microsoft’s SIEM solution, embodies all of these capabilities.
Other options in the dropdown (incorrect for this context):
SOAR is focused on automating responses after SIEM alerts.
TAXII is a threat intel transport protocol, not a detection system.
ASR (Attack Surface Reduction) refers to endpoint hardening, not centralized event analysis.
✅ Therefore, the correct and Microsoft-verified term is: A security information and event management (SIEM).
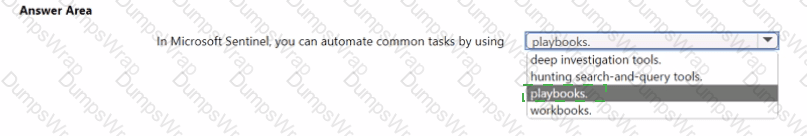
Select the answer that correctly completes the sentence.

Options:
Answer:

Explanation:
Which two types of resources can be protected by using Azure Firewall? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Options:
Azure virtual machines
Azure Active Directory (Azure AD) users
Microsoft Exchange Online inboxes
Azure virtual networks
Microsoft SharePoint Online sites
Answer:
A, DExplanation:
Azure Firewall is a managed, cloud-based network security service designed to secure traffic inside and across Azure Virtual Networks. Microsoft describes Azure Firewall as a stateful firewall that “protects Azure Virtual Network resources” by enforcing network and application rules, central logging, and threat intelligence–based filtering. Because it is deployed into a VNet/subnet (often as the hub in a hub-and-spoke), it directly governs East/West and North/South flows to workloads such as Azure virtual machines and platform services reachable through the VNet, using DNAT/SNAT and rule collections. Microsoft guidance highlights capabilities to “centrally create, enforce, and log application and network connectivity policies across subscriptions and virtual networks,” and to filter traffic for peered VNets, branch connections (VPN/ExpressRoute), and internet traffic. These capabilities explicitly map to protecting Azure virtual networks and the VMs and subnets inside them. In contrast, Azure AD users, Exchange Online inboxes, and SharePoint Online sites are SaaS/identity resources protected by Microsoft Entra controls, Exchange/SharePoint security, and Purview/Defender for Office 365—not by a VNet firewall. Therefore, the Azure Firewall–protectable resource types among the options are Azure virtual machines and Azure virtual networks.
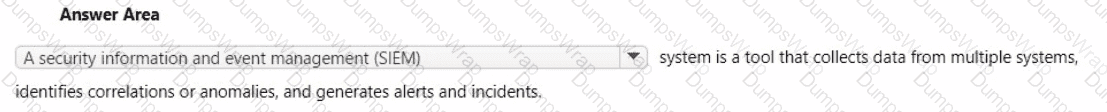
Select the answer that correctly completes the sentence.
Options:
Answer:
Explanation:
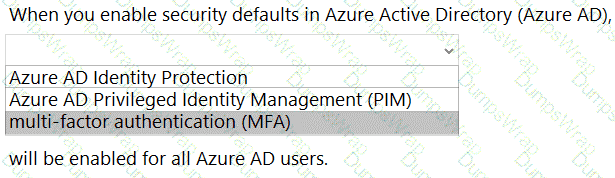
Microsoft states that Security defaults are baseline protections in Azure Active Directory (now Microsoft Entra ID) that “make it easier to help protect your organization from identity-related attacks.” One of the core behaviors is that security defaults “require all users to register for Azure AD Multi-Factor Authentication,” and enforce “multi-factor authentication for all users,” with special emphasis that “administrators are required to do multi-factor authentication.” Security defaults also “block legacy authentication” and add protections for privileged operations, but the universal control that applies to every user is MFA. Importantly, enabling security defaults does not turn on paid capabilities such as Azure AD Identity Protection or Privileged Identity Management (PIM); those are separate, premium features. The baseline is intentionally simple and tenant-wide: require MFA registration, challenge with MFA when risk or sensitive operations are detected, and reduce exposure by disabling legacy protocols. Therefore, when you enable security defaults, multi-factor authentication (MFA) will be enabled for all Azure AD users, aligning with Microsoft’s guidance that security defaults “help protect all organizations by requiring MFA and disabling legacy authentication.”
Select the answer that correctly completes the sentence.
Options:
Answer:

Explanation:
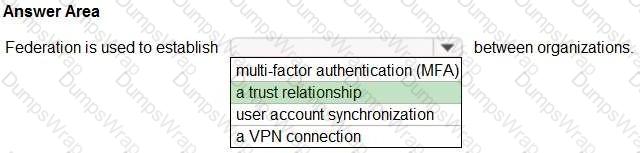
In Microsoft identity and access scenarios, federation is explicitly defined as a mechanism to create trust between autonomous organizations so that identities authenticated in one can be accepted by another. Microsoft describes this as: “Federation is a collection of domains that have established trust.” In a federation, “this trust relationship lets each organization accept the other’s user authentication” and enables access to resources without the need to duplicate user accounts or require separate credentials. Within Azure AD/Microsoft Entra and AD FS guidance, Microsoft further explains that federation enables “claims-based access across security boundaries” and “allows users to access applications in a partner organization using their existing credentials.” These statements underline that the purpose of federation is to establish a trust relationship across identity providers or directories, not to provide multi-factor authentication, synchronize accounts, or build network tunnels. MFA is an authentication strength that can be applied on top of federated sign-in, user account synchronization is handled by services like Microsoft Entra Connect (Azure AD Connect), and VPNs provide network connectivity, not identity trust. Therefore, the completion that aligns with Microsoft SCI documentation is that federation establishes a trust relationship between organizations.
What feature supports email as a method of authenticating users?
Options:
Microsoft Entra ID Protection
Microsoft Entra Multi-Factor Authentication (MFA)
self-service password reset (SSPR)
Microsoft Entra Password Protection
Answer:
CExplanation:
In Microsoft Entra ID (formerly Azure AD), self-service password reset (SSPR) is the feature that explicitly supports email as an authentication method when users need to verify their identity to reset or unlock their password.
According to Microsoft’s identity and access documentation and the SCI learning content, SSPR lets administrators choose which verification methods are available to users, such as mobile phone, office phone, mobile app, security questions, and email. When email is enabled, a verification code can be sent to a registered alternate email address. The user proves their identity by entering this code, which is treated as an authentication step in the SSPR process.
By contrast:
Microsoft Entra Multi-Factor Authentication (MFA) does not support email as an MFA method; it focuses on methods like authenticator apps, phone calls, and text messages.
Microsoft Entra ID Protection detects and responds to risky sign-ins and users but does not provide email-based authentication.
Microsoft Entra Password Protection deals with banned and compromised passwords, not with email verification.
Therefore, the only option in the list that uses email as a supported authentication method is self-service password reset (SSPR).
When you enable Azure AD Multi-Factor Authentication (MFA), how many factors are required for authentication?
Options:
1
2
3
4
Answer:
BExplanation:
In Microsoft’s Security, Compliance, and Identity (SCI) learning content, Multi-Factor Authentication (MFA) is defined as requiring more than one verification method during sign-in. Microsoft states: “Multi-factor authentication (MFA) requires two or more verification methods” and Azure AD (Microsoft Entra ID) MFA “works by requiring two or more of the following: something you know (password), something you have (trusted device or token), something you are (biometrics).” The SCI fundamentals also explain that MFA strengthens authentication beyond a single password by combining distinct factor types, noting that “strong authentication uses at least two different factors to verify identity.”
When you enable Azure AD MFA, a user must successfully present two factors from those categories to complete the authentication—commonly a password (something you know) plus a second factor such as Microsoft Authenticator approval, a FIDO2 security key, SMS/voice code, or Windows Hello (something you have/are). This is the core of Azure AD’s risk-based and conditional access controls, which can require MFA based on conditions or risk signals. Therefore, the number of factors required after enabling Azure AD MFA is two, aligning with Microsoft’s definition and implementation of multi-factor authentication in Entra ID.
Select the answer that correctly completes the sentence.
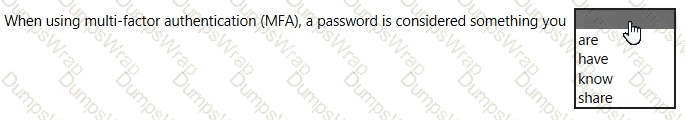
Options:
Answer:

Explanation:
In Microsoft’s Security, Compliance, and Identity guidance, multi-factor authentication (MFA) is based on combining independent categories of credentials to verify a user. Microsoft describes the three factor types as: something you know (knowledge), something you have (possession), and something you are (inherence). A password is explicitly categorized as “something you know,” because it relies on a secret the user memorizes and types during sign-in. MFA improves security by requiring two or more of these distinct factors—e.g., a password (know) plus a phone approval or hardware token (have), or a biometric like Windows Hello (are). Using factors from different categories mitigates common attacks such as password spray, credential stuffing, and phishing, because compromising one factor (for example, the password) does not grant access without the second, unrelated factor. Microsoft recommends enabling MFA broadly and pairing passwords with stronger possession or inherence methods to achieve a measurable reduction in account compromise risk. Therefore, in the MFA model used by Microsoft Entra ID (Azure AD), a password is considered something you know.
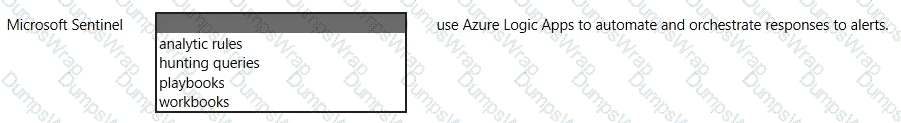
Select the answer that correctly completes the sentence.
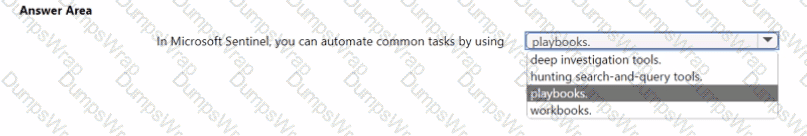
Options:
Answer:

Explanation:
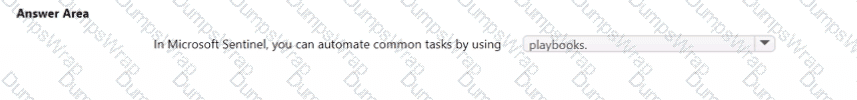
In Microsoft Sentinel, automation of routine or repetitive SOC tasks is delivered through playbooks. Microsoft’s Sentinel guidance defines playbooks as “collections of procedures that can be run from Microsoft Sentinel in response to an alert or incident.” They are “built on Azure Logic Apps” and enable teams to “automate and orchestrate responses to threats” such as enriching incidents, opening tickets, notifying responders, quarantining entities, or blocking indicators. The documentation further clarifies that automation rules can “trigger playbooks automatically based on analytics alerts or incident conditions,” allowing consistent, scalable actions without manual intervention. By contrast, workbooks provide “data visualization and reporting” for analysis; hunting search-and-query tools (built on KQL) are used to “proactively hunt for threats”; and deep investigation tools assist analysts during incident investigation. Therefore, when the goal is to automate common tasks—for example, sending incident notifications, enriching with threat intelligence, or creating tickets in ITSM—the correct capability in Microsoft Sentinel is playbooks, because they encapsulate repeatable response procedures and can be executed automatically via automation rules or manually from incidents, alerts, or entities.
Select the answer that correctly completes the sentence.

Options:
Answer:
Explanation:

In Microsoft’s official guidance, the Microsoft Cloud Adoption Framework for Azure (CAF) is described as the end-to-end approach that “provides best practices, documentation, and tools” to help organizations create and implement business and technology strategies for cloud adoption. The framework aggregates field experience from “Microsoft employees, partners, and customers” and offers prescriptive guidance across strategy, planning, readiness, governance, security, and management to ensure a secure and compliant Azure landing zone. Within SCI-aligned materials, CAF is highlighted as the authoritative body of guidance that helps organizations reduce risk by aligning cloud architecture, identity, security, and compliance controls with Zero Trust principles and regulatory needs. It enables teams to map security baselines, identity governance (e.g., using Microsoft Entra and Conditional Access), and compliance controls (e.g., data protection and regulatory mappings) into deployment blueprints and policy-driven guardrails.
By contrast, Azure Blueprints package artifacts (policies, RBAC, templates) for consistent deployments; Azure Policy enforces and audits configuration through policy definitions; and resource locks prevent accidental modification or deletion. While these are important technical controls, the statement in the question explicitly refers to a body of best practices and guidance that assists an Azure deployment end to end—this is precisely the role of the Microsoft Cloud Adoption Framework for Azure.
Select the answer that correctly completes the sentence.
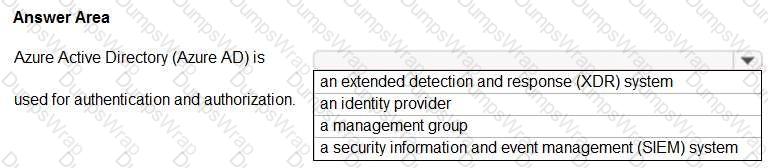
Options:
Answer:

Explanation:
Azure Active Directory (Azure AD) is a cloud-based user identity and authentication service. Reference:
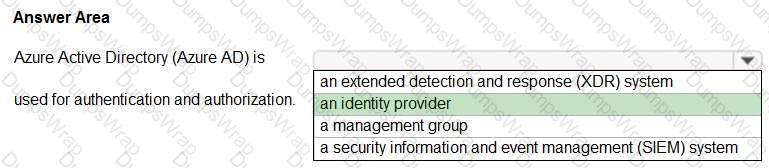
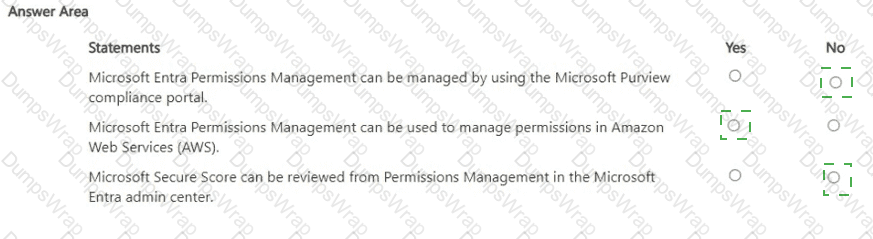
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
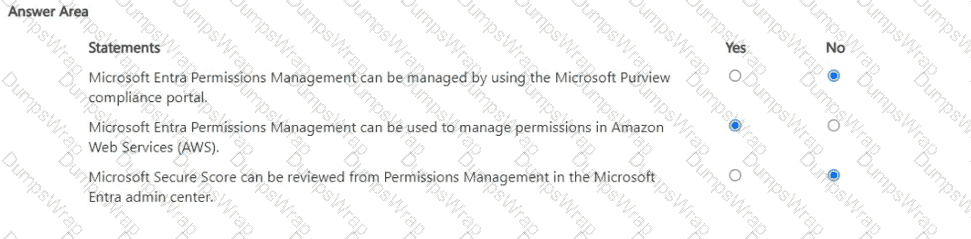
Microsoft Entra Permissions Management is Microsoft’s cloud infrastructure entitlement management (CIEM) solution delivered in the Microsoft Entra admin center, not in the Microsoft Purview compliance portal. Microsoft guidance describes it as a CIEM service that provides “centralized visibility, right-sizing, and governance of permissions across clouds” and is accessed and administered from the Entra portal under Permissions Management. The Purview compliance portal is used for compliance solutions such as Compliance Manager, Information Protection, DLP, eDiscovery, and Insider Risk—not CIEM—so statement 1 is No.
Permissions Management supports multicloud environments. Microsoft documentation states that it “discovers, monitors, and manages permissions for identities and resources across Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform (GCP).” It calculates a Permission Creep Index (PCI), surfaces excessive permissions, and recommends remediation across these clouds; therefore, using it to manage permissions in AWS is supported—statement 2 is Yes.
Regarding secure scores: Permissions Management focuses on entitlements (e.g., effective permissions, PCI, right-sizing actions). Microsoft Secure Score (and Identity Secure Score) are separate posture metrics exposed in Microsoft 365 Defender and Microsoft Entra ID, respectively. The Permissions Management blade does not present Microsoft Secure Score; instead, it shows CIEM-specific insights and PCI. Consequently, the claim that Secure Score can be reviewed from Permissions Management in the Entra admin center is No.
Which two tasks can you implement by using data loss prevention (DLP) policies in Microsoft 365? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Options:
Display policy tips to users who are about to violate your organization’s policies.
Enable disk encryption on endpoints.
Protect documents in Microsoft OneDrive that contain sensitive information.
Apply security baselines to devices.
Answer:
A, CExplanation:
Microsoft Purview Data Loss Prevention (DLP) is designed to prevent the inadvertent or inappropriate sharing of sensitive data across Microsoft 365 services. Microsoft’s guidance states that DLP “helps you discover, monitor, and protect sensitive items across Microsoft 365,” and that with DLP policies you can “identify, monitor, and automatically protect sensitive items in Exchange Online, SharePoint Online, OneDrive for Business, and Microsoft Teams.” This directly supports option C, because DLP can detect sensitive info in OneDrive documents and automatically apply protective actions such as blocking external sharing, restricting access, or auditing the event.
DLP also provides end-user coaching through policy tips: “Policy tips are informative notices that appear when users are working with content that contains sensitive info … to help prevent data loss.” When a user is about to send or share sensitive data in violation of policy, these tips surface in Outlook and Office apps (including when files are stored in SharePoint/OneDrive), aligning with option A.
By contrast, enabling disk encryption (e.g., BitLocker) and applying device security baselines are endpoint/device management tasks handled through Microsoft Intune or Group Policy—not by DLP. Therefore, A and C are the correct tasks you can implement with Microsoft 365 DLP policies.
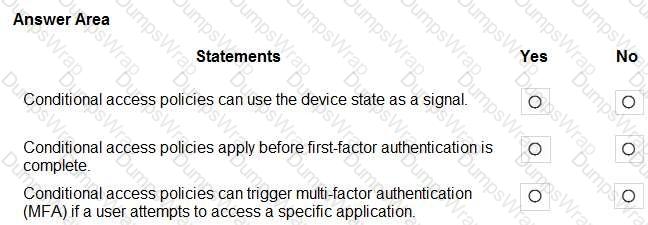
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
Microsoft’s Conditional Access (part of Microsoft Entra ID) evaluates multiple signals to make access decisions. The official description lists typical signals such as “user or group membership, IP location information, device state, application, and real-time risk.” The device state element explicitly refers to conditions like “compliant or hybrid Azure AD joined devices,” allowing policies that grant or block access—or require extra controls—based on whether a device meets compliance/registration requirements.
Regarding evaluation timing, Microsoft’s guidance states that Conditional Access “policies are enforced after the first-factor authentication is completed.” This means the engine needs the user’s primary sign-in context (who the user is and how they authenticated) to evaluate the conditions and then decide whether to allow, block, or require additional controls. Therefore, the statement that policies apply before first factor is not correct.
Finally, Conditional Access includes grant controls such as “Require multi-factor authentication,” and policies can be scoped to specific cloud apps or actions. As a result, you can target a particular application and require MFA when a user attempts to access it, satisfying application-specific risk mitigation while preserving user productivity.
Which statement represents a Microsoft privacy principle?
Options:
Microsoft does not collect any customer data.
Microsoft uses hosted customer email and chat data for targeted advertising.
Microsoft manages privacy settings for its customers.
Microsoft respects the local privacy laws that are applicable to its customers.
Answer:
DExplanation:
Microsoft’s privacy commitments are framed as principles that include Control, Transparency, Security, Strong legal protections, No content-based targeting, and Benefits to you. Under these commitments, Microsoft emphasizes compliance with regional and sectoral laws: it provides “strong legal protections” for data and commits to handling data “in accordance with applicable laws,” including respecting local privacy and data-protection requirements and supporting cross-border transfers only as permitted by law. The principles also state Microsoft does not use customer content for advertising, and it enables customers to manage their own privacy settings and choices. Therefore:
A is false (Microsoft does collect data but minimizes and protects it).
B is false (Microsoft states no content-based targeting for customer email/chat).
C is false (Microsoft provides settings; customers control them).
D aligns with Microsoft’s principle to respect and comply with applicable local privacy laws.
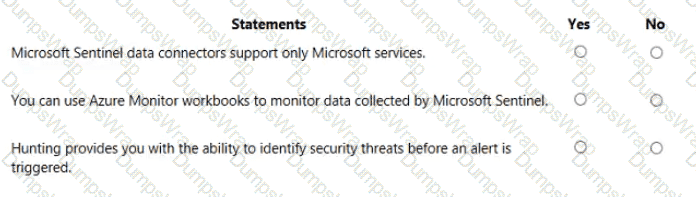
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point
Options:
Answer:

Explanation:
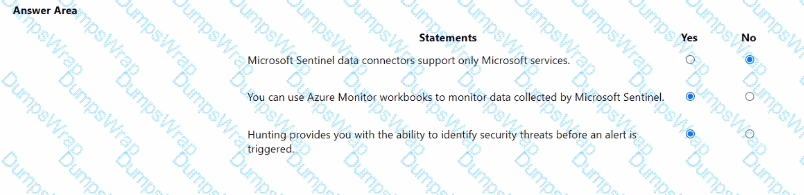
Microsoft states that Microsoft Sentinel includes connectors for both Microsoft and non-Microsoft sources. The product overview explains that Sentinel “comes with built-in connectors” for services such as Microsoft 365, Defender, and Azure sources, and also built-in connectors for non-Microsoft solutions like firewalls and other security products. Therefore, the claim that data connectors support only Microsoft services is false.
For visualization and monitoring, the documentation clarifies that “Microsoft Sentinel uses Azure Monitor workbooks to provide rich visualizations of your data.” Workbooks are the native dashboarding framework in Sentinel and can be customized to monitor logs, incidents, and telemetry that Sentinel ingests. Hence, using Azure Monitor Workbooks to monitor data collected by Sentinel is true.
Regarding threat hunting, Microsoft describes the Hunting capability as a proactive feature: “Hunting lets you proactively hunt for security threats,” using Kusto Query Language queries and analytic patterns to find indicators of compromise before alerts are generated. Analysts can run, save, and schedule hunts to uncover suspicious activity that hasn’t yet raised an alert, making the statement about identifying threats before an alert is triggered true.
Which score measures an organization ' s progress in completing actions that help reduce risks associated to data protection and regulatory standards?
Options:
Microsoft Secure Score
Productivity Score
Secure score in Azure Security Center
Compliance score
Answer:
DExplanation:
The Compliance score in Microsoft Purview Compliance Manager is a measurement tool that evaluates an organization’s progress toward meeting data protection and regulatory compliance requirements. It is specifically designed to help organizations reduce risks related to data governance, privacy, and compliance with various standards such as GDPR, ISO 27001, NIST 800-53, and Microsoft Data Protection Baselines.
According to Microsoft’s official documentation on Compliance Manager, the Compliance score “helps organizations track, improve, and demonstrate their compliance posture by providing a quantifiable measure of compliance with regulations and standards.” Each action within Compliance Manager contributes a certain number of points to the overall score. These points are weighted based on risk, meaning that actions with a greater impact on reducing compliance risk contribute more significantly to the total score.
The score is not an absolute measure of legal compliance but rather an indicator of progress toward implementing recommended controls and risk-reducing actions. Microsoft emphasizes that Compliance score “assists organizations in identifying areas of improvement, prioritizing compliance tasks, and maintaining an auditable record of their compliance activities.”
By contrast, Microsoft Secure Score measures security posture related to identity, device, and application protection, while Productivity Score evaluates collaboration and technology experience. Thus, the metric that specifically assesses data protection and regulatory compliance progress is the Compliance score in Microsoft Purview Compliance Manager.
What should you use in the Microsoft Defender portal to view security trends and track the protection status of identities?
Options:
Secure score
Reports
Hunting
Incidents
Answer:
BExplanation:
In the Microsoft 365 Defender (Microsoft Defender XDR) portal, the Reports area is the feature designed to surface security trends and provide protection status views across workloads, including identities. Microsoft guidance explains that the Reports workspace offers curated dashboards and exportable reports for specific domains (for example, Identities, Email & collaboration, Endpoints), so security teams can review trend lines, coverage/health, and status without running queries. For identities specifically (backed by Microsoft Defender for Identity), the reports include overview dashboards and scheduled/on-demand reports that show items such as identity security posture, open health issues, alert volumes over time, and sensor/coverage status. This aligns with SCI learning paths that distinguish portal areas by purpose: Secure score is a measurement of overall posture and recommended actions, Incidents is for triage and response to individual cases, and Hunting is for ad-hoc, query-driven investigations. When the task is to “view security trends and track the protection status of identities,” Microsoft directs administrators to the Reports > Identities experience in the Defender portal, which provides the built-in, continuously updated visualizations and summaries required for ongoing monitoring.
Select the answer that correctly completes the sentence.
Options:
Answer:

You have an Azure subscription.
You need to implement approval-based time-bound role activation.
What should you use?
Options:
Microsoft Entra ID Protection
Microsoft Entra Conditional access
Microsoft Entra Privileged Management
Microsoft Entra Access Reviews
Answer:
CExplanation:
Microsoft documents describe Microsoft Entra Privileged Identity Management (PIM) as the service that delivers approval-based, time-limited elevation to privileged roles. Official guidance states: “Privileged Identity Management (PIM) enables you to manage, control, and monitor access to important resources in Microsoft Entra ID, Azure, and Microsoft 365.” PIM specifically supports just-in-time and time-bound activations: “PIM provides just-in-time privileged access to Microsoft Entra roles and Azure resources” and “allows you to make access time-bound by setting start and end dates.” It also supports approval workflows: “You can require approval to activate privileged roles, and designate approvers to receive and approve requests.” Additional controls include “require multi-factor authentication to activate, provide a justification, and ticket number,” and auditing: “PIM records all activations and changes for review and alerting.”
By contrast, Microsoft Entra ID Protection focuses on risk detections and automated remediation, not role elevation workflows. Conditional Access enforces access policies at sign-in and session but does not provide approval-based role activation. Access Reviews help you “review and attest to continued access” but do not supply just-in-time elevation. Therefore, the Microsoft Purview/Entra feature that implements approval-based, time-bound role activation is Microsoft Entra Privileged Identity Management (PIM).
Which compliance feature should you use to identify documents that are employee resumes?
Options:
pre-trained classifiers
Content explorer
Activity explorer
eDiscovery
Answer:
AExplanation:
In Microsoft Purview Information Protection, pre-trained (Microsoft-provided) trainable classifiers are designed to automatically recognize specific categories of content by learning from examples rather than relying only on patterns or keywords. Microsoft’s guidance explains that trainable classifiers “look for data by learning from examples,” and that Microsoft supplies a catalog of “pre-trained classifiers that you can use immediately in your tenant.” The documentation explicitly lists content types these classifiers can recognize, including “Resumes,” along with other categories such as Source code, Threat and harassment, and more. Because they’re already trained by Microsoft, you can use them “to identify and classify items across SharePoint, OneDrive, and Exchange,” and then take actions such as auto-labeling or enforcing DLP policies based on the classifier match.
By contrast, Content explorer is a reporting tool that lets you view where sensitive info types/labels were found; it doesn’t identify resumes on its own. Activity explorer shows events like DLP policy matches over time. eDiscovery is used for legal hold, search, and review, not for semantic content identification. Therefore, to identify documents that are employee resumes, the correct Microsoft compliance feature is the pre-trained (Microsoft-provided) trainable classifier for Resumes.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
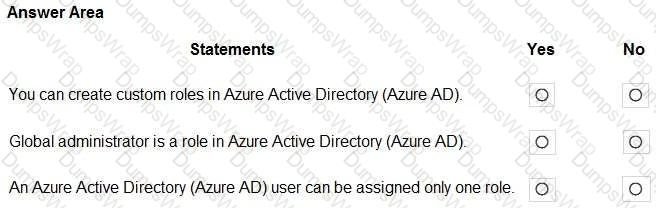
Options:
Answer:
Explanation:
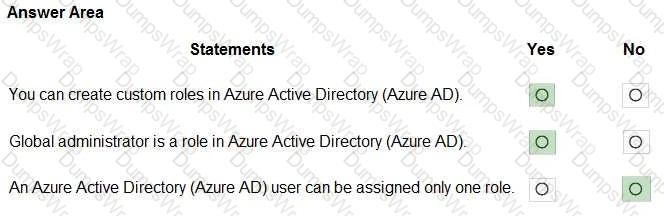
Microsoft’s identity platform (Microsoft Entra ID, formerly Azure AD) supports built-in and custom directory roles. The official guidance states that you can “create your own custom roles to grant permissions for management of Microsoft Entra resources,” and those roles consist of specific role permissions that you select to tailor least-privilege administration. The documentation also lists Global administrator (formerly Company Administrator) as a built-in role that “has access to all administrative features” and can delegate role assignments, reset passwords for all users, and manage identity settings across the tenant. Regarding assignments, Microsoft is explicit that role assignment is many-to-many: administrators can “assign one or more roles to a user,” and the user’s effective permissions are the union of the privileges from all assigned roles. Consequently, (1) creating custom roles is supported (Yes), (2) Global administrator is indeed a defined Azure AD/Microsoft Entra role (Yes), and (3) a user being limited to only one role is incorrect (No) because multiple role assignments to the same user are permitted and commonly used to implement least privilege and separation of duties.
Box 1: Yes
Azure AD supports custom roles.
Box 2: Yes
Global Administrator has access to all administrative features in Azure Active Directory. Box 3: No
What do you use to provide real-time integration between Azure Sentinel and another security source?
Options:
Azure AD Connect
a Log Analytics workspace
Azure Information Protection
a data connector
Answer:
DExplanation:
To on-board Azure Sentinel, you first need to connect to your security sources. Azure Sentinel comes with a number of connectors for Microsoft solutions, including Microsoft 365 Defender solutions, and Microsoft 365 sources, including Office 365, Azure AD, Microsoft Defender for Identity, and Microsoft Cloud App Security, etc.
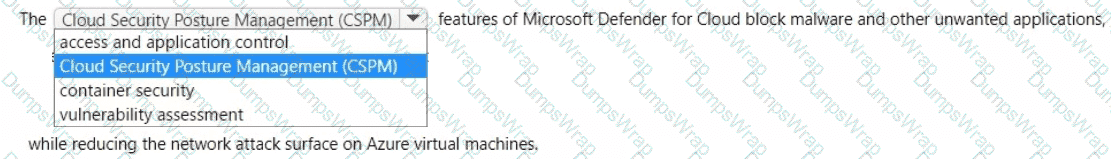
Select the answer that correctly completes the sentence.
Options:
Answer:

Explanation:
access and application control
In Microsoft Defender for Cloud, the capabilities grouped as access and application control are designed to harden Azure virtual machines by limiting both what can access a VM and what can run on it. Microsoft’s documentation explains that Adaptive application controls “help you control which applications can run on your VMs by allowing only known-safe applications,” which directly helps block malware and other unwanted applications. In the same family, Just-in-time (JIT) VM access “reduces exposure to attacks by locking down inbound traffic to your VMs and opening only the required ports, for approved users, for a limited time,” thereby reducing the network attack surface. These capabilities are surfaced in Defender for Cloud recommendations and policies to enforce least privilege at the network edge and on the endpoint execution layer.
By contrast, Cloud Security Posture Management (CSPM) provides continuous assessment and secure-score-driven recommendations but isn’t the control that actively blocks applications or time-bounds inbound access. Container security targets container images and runtimes, and vulnerability assessment identifies software vulnerabilities but doesn’t enforce allow-listing or time-bound access. Therefore, the correct completion is access and application control, which encompasses Adaptive application controls and JIT VM access to protect VMs from unwanted apps and minimize exposed network surface.
You have a Microsoft 365 E3 subscription.
You plan to audit user activity by using the unified audit log and Basic Audit.
For how long will the audit records be retained?
Options:
15 days
30 days
90 days
180 days
Answer:
DExplanation:
In Microsoft 365, the unified audit log retention depends on the audit tier included with the subscription. Current SCI/Compliance documentation states that Audit (Standard)—which is available with Microsoft 365 E3—retains audit records for 180 days. The docs describe that organizations with E3 receive “up to 180 days of audit log retention” for user and admin activities captured in the unified audit pipeline. Longer retention (for example 365 days and beyond with customizable policies) is part of Audit (Premium) features generally associated with E5/E5 Compliance. Because the scenario specifies a Microsoft 365 E3 subscription using the unified audit log and Basic/Standard Audit, the retention period for audit records is 180 days.
Select the answer that correctly completes the sentence.

Options:
Answer:
Explanation:
Azure AD Identity Protection (now part of Microsoft Entra ID) is the Microsoft service that “automates the detection and remediation of identity-based risks.” It continuously evaluates user risk and sign-in risk using signals such as leaked credentials, atypical travel, unfamiliar sign-in properties, and malware-linked IPs. Microsoft documentation clarifies that Identity Protection “uses adaptive machine learning and heuristics to detect risky behaviors and sign-ins” and enables administrators to configure risk-based policies (for example, require MFA or block access) to automatically respond. It also provides rich investigations through risk reports so security teams can triage and remediate compromised identities. This distinctly differs from other Entra capabilities: Privileged Identity Management (PIM) governs just-in-time privileged access and role activation, while MFA is an authentication method enforced by policies. Because the service that specifically detects risk and applies automated protection based on risk is Azure AD Identity Protection, it is the correct completion for the sentence about identity risk detection and remediation.QUESTION NO: 148 HOTSPOT
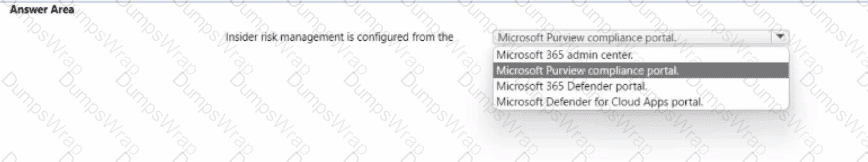
Select the answer that correctly completes the sentence.
Answer: < map > < m x1= " 491 " x2= " 699 " y1= " 63 " y2= " 79 " ss= " 0 " a= " 0 " / > < /map >
In Microsoft’s SCI guidance, Insider risk management is a Microsoft Purview capability surfaced and administered from the Microsoft Purview compliance portal. The official description states that Insider risk management “helps you minimize internal risks by enabling you to detect, investigate, and act on risky activities in your organization.” Microsoft further clarifies access and configuration by directing admins to “use the Microsoft Purview compliance portal to configure and manage insider risk policies, alerts, and investigations,” and that you can “go to the Microsoft Purview compliance portal and select Insider risk management” to start. These statements place the feature squarely in the compliance plane—not the Microsoft 365 admin center (tenant-wide service management), not the Microsoft 365 Defender portal (threat protection and incident response), and not Microsoft Defender for Cloud Apps (app discovery and cloud app protection). In the SCI learning path, Insider risk is consistently grouped with Microsoft Purview solutions (Information Protection, DLP, eDiscovery, and Audit), emphasizing compliance workflows, risk indicators, policy tuning, and case management. Therefore, the correct completion of the sentence “Insider risk management is configured from the” is the Microsoft Purview compliance portal, where administrators create policies, review alerts, investigate user activity timelines, and take appropriate remediation actions within a compliance-centric experience.
Select the answer that correctly completes the sentence.
Options:
Answer:

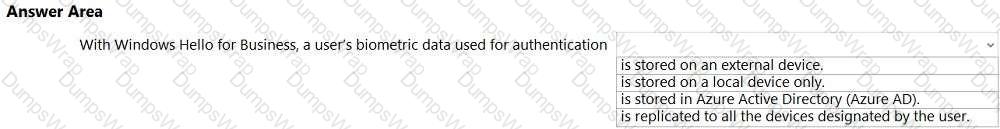
Explanation:
Biometrics templates are stored locally on a device. Reference:
Select the answer that correctly completes the sentence.
Options:
Answer:
Explanation:
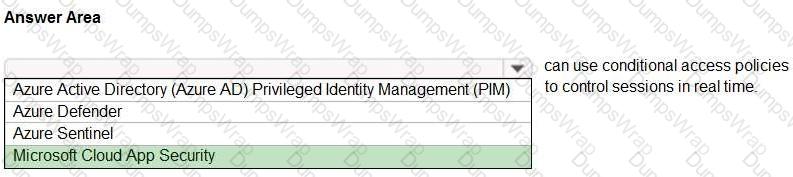
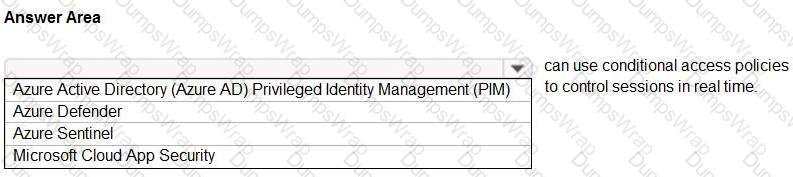
In Microsoft’s Security, Compliance, and Identity guidance, Microsoft Cloud App Security (now Microsoft Defender for Cloud Apps) integrates with Azure AD Conditional Access to provide Conditional Access App Control. This capability enables organizations to “monitor and control user sessions in real time” by routing traffic through a reverse proxy once a Conditional Access policy is triggered. With session controls, admins can enforce actions such as block, allow with inspection, apply download restrictions, require label application, or limit access to web apps based on context (user, device state, location, risk). SCI learning paths describe that Defender for Cloud Apps works with Conditional Access policies to provide session-based conditional access that “protects data in real time,” giving granular control after authentication while a session is active.
By comparison, Azure AD Privileged Identity Management (PIM) focuses on just-in-time elevation and governance of privileged roles, not real-time in-app session control. Azure Defender (Defender for Cloud) provides cloud workload protection and posture management, not Conditional Access session enforcement. Azure Sentinel (Microsoft Sentinel) is a SIEM/SOAR platform for analytics, hunting, and automation and does not apply Conditional Access session policies. Therefore, the Microsoft product that uses Conditional Access policies to control sessions in real time is Microsoft Cloud App Security (Defender for Cloud Apps).
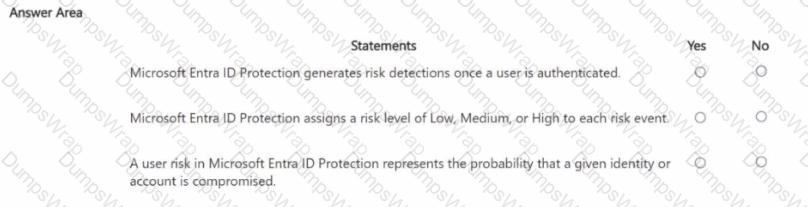
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
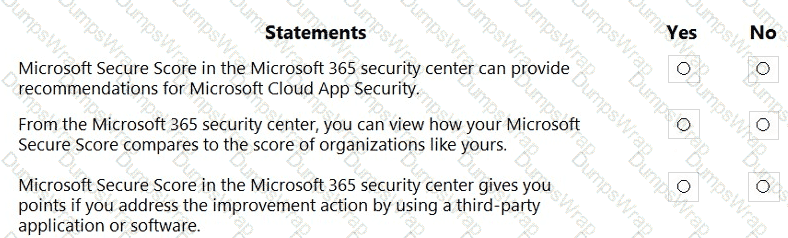
Options:
Answer:

Explanation:
Microsoft Secure Score in the Microsoft 365 Defender portal aggregates improvement actions across Microsoft security workloads, including Microsoft Defender for Cloud Apps (formerly Cloud App Security). Microsoft states that “Defender for Cloud Apps automatically provides SSPM data in Microsoft Secure Score, for any supported and connected app.” This means Secure Score can surface and recommend actions tied to Cloud App Security/Defender for Cloud Apps, validating statement 1 as Yes. Microsoft Learn
Secure Score also includes peer comparison so organizations can benchmark their progress. The Microsoft documentation explicitly notes: “Compare your score to organizations like yours. There are two places to see how your score compares to organizations that are similar to yours.” This capability appears on the Overview experience in the Defender portal, confirming statement 2 as Yes. Microsoft Learn
Finally, Secure Score recognizes mitigations implemented outside Microsoft tooling. In the official guidance for improvement actions, Microsoft explains the status options “Resolved through third party and Resolved through alternate mitigation,” adding: “You’ll gain the points that the action is worth, so your score better reflects your overall security posture.” Therefore, if you address an improvement action via a third-party product, Secure Score awards the associated points—making statement 3 Yes.
What should you create to search and export content preserved in an eDiscovery hold?
Options:
a Microsoft SharePoint Online site
a case
a Microsoft Exchange Online public folder
Azure Files
Answer:
BExplanation:
In Microsoft Purview eDiscovery, to search, preserve, analyze, and export content, you must first create a case. A case acts as a container for all eDiscovery activities, including placing users and content locations on litigation hold, running content searches, and exporting results for legal or compliance review.
SCI Extract: " Cases are used in Microsoft Purview eDiscovery (Standard and Premium) to manage, organize, and execute the various tasks associated with identifying and delivering content during an investigation or litigation. "
Select the answer that correctly completes the sentence.

Options:
Answer:

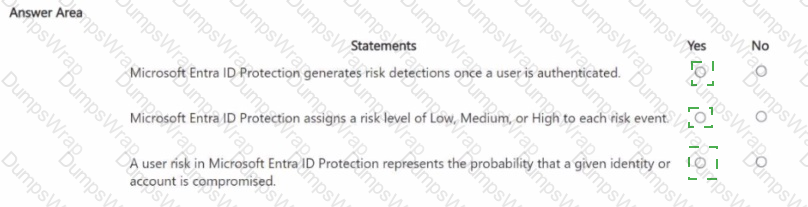
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
documents: =
Microsoft Entra ID Protection evaluates risk during authentication, not only after the user is authenticated. The service provides “real-time” assessment as part of the sign-in flow and also processes “offline” detections, enabling Conditional Access to act before a session is granted. In Microsoft’s terminology, “sign-in risk represents the probability that a given authentication request isn’t authorized by the identity owner,” while “user risk represents the probability that a given identity or account is compromised.” These risks are surfaced as risk detections and can be used to trigger MFA, block access, or require secure password reset. Each detection and calculated risk is classified by Microsoft Entra ID Protection with “Low, Medium, or High” levels so administrators can triage and automate policy responses appropriately. Because detections are calculated in real time as part of the sign-in evaluation (and also through subsequent analysis), it is incorrect to say they are generated once the user is authenticated. The accurate view is that Identity Protection continuously analyzes telemetry and produces detections and risk levels that may be acted upon before, during, and after sign-in, with user risk expressing the likelihood that the identity itself is compromised and sign-in risk expressing the likelihood that a particular authentication attempt is not legitimate.
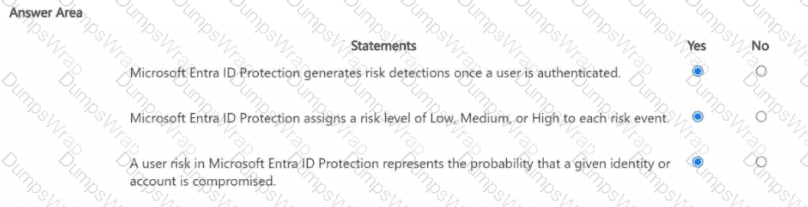
For each of the following statement, select Yes if the statement is true Otherwise, select No.
NOTE: Each connect selection a worth one point.
Options:
Answer:

Explanation:
An external email address can be used to authenticate self-service password reset (SSPR). → Yes
A notification to the Microsoft Authenticator app can be used to authenticate self-service password reset (SSPR). → Yes
To perform self-service password reset (SSPR), a user must already be signed in and authenticated to Azure AD. → No
For Microsoft Entra self-service password reset (SSPR), users must register one or more authentication methods that can later be used when they forget their password or are locked out. Microsoft’s end-user guidance states that an email address option lets users configure “an alternate email address that can be used without requiring your forgotten or missing password,” and that this method is available only for password reset. In practice, this alternate address is typically a personal or external email (for example, Gmail), so using an external email to authenticate SSPR is valid.
SSPR can also use the Microsoft Authenticator app as an authentication method. Microsoft documents that Authenticator push notifications, including number matching, are supported for several scenarios, explicitly listing self-service password reset (SSPR) among them. This means a push notification to the app on the user’s device can be used to verify identity during SSPR.
Finally, SSPR is designed for situations where the user cannot sign in. Official SSPR process descriptions explain that users start from the “Can’t access your account?” or password-reset page, provide their username, and then use their registered methods to prove identity. They do not need to be already authenticated to Azure AD; SSPR exists precisely to recover access when sign-in fails.
In the shared responsibility model, for what is Microsoft responsible when managing Azure virtual machines?
Options:
Updating the operating system.
Configuring the permissions for shared folders.
Updating the firmware of the disk controller.
Updating installed applications.
Answer:
CExplanation:
In Microsoft’s shared responsibility model, responsibilities vary by service type. For IaaS (for example, Azure Virtual Machines), Microsoft states that it is responsible for protecting and maintaining the cloud infrastructure that runs customer workloads, while customers secure what they deploy in that infrastructure. Microsoft’s guidance explains that Microsoft “operates and secures the datacenters, physical hosts, networking, and the virtualization fabric,” and handles the underlying platform maintenance, including “hardware and firmware” that support those hosts. Conversely, customers are responsible for what runs inside their VM: “the guest operating system (including updates and security configuration), applications, identity, and data.”
Applied to the options in this question:
Updating the operating system and updating installed applications are customer tasks because they are inside the guest VM.
Configuring permissions for shared folders is also a customer responsibility because it’s an OS/application configuration within the guest.
Updating the firmware of the disk controller belongs to Microsoft, because firmware and hardware on the physical hosts (including storage controllers) are part of the infrastructure of the cloud that Microsoft manages and secures.
This aligns with SCI study materials that summarize: Microsoft secures “the security of the cloud” (physical datacenter, hosts, network, and hypervisor/firmware), while customers secure “security in the cloud” (guest OS, apps, and data).
What can you use to view the Microsoft Secure Score for Devices?
Options:
Microsoft Defender for Cloud Apps
Microsoft Defender for Endpoint
Microsoft Defender for Identity
Microsoft Defender for Office 365
Answer:
BExplanation:
Microsoft Secure Score for Devices
Artikel
12.05.2022
3 Minuten Lesedauer
Applies to:
Microsoft Defender for Endpoint Plan 2
Microsoft Defender Vulnerability Management
Microsoft 365 Defender
Some information relates to pre-released product which may be substantially modified before it ' s commercially released. Microsoft makes no warranties, express or implied, with respect to the information provided here.
To sign up for the Defender Vulnerability Management public preview or if you have any questions, contact us (mdvmtrial@microsoft.com).
Already have Microsoft Defender for Endpoint P2? Sign up for a free trial of the Defender Vulnerability Management Add-on.
Configuration score is now part of vulnerability management as Microsoft Secure Score for Devices.
Your score for devices is visible in the Defender Vulnerability Management dashboard of the Microsoft 365 Defender portal. A higher Microsoft Secure Score for Devices means your endpoints are more resilient from cybersecurity threat attacks. It reflects the collective security configuration state of your devices across the following categories:
Application
Operating system
Network
Accounts
Security controls
Select a category to go to the Security recommendations page and view the relevant recommendations.
Turn on the Microsoft Secure Score connector
Forward Microsoft Defender for Endpoint signals, giving Microsoft Secure Score visibility into the device security posture. Forwarded data is stored and processed in the same location as your Microsoft Secure Score data.
Changes might take up to a few hours to reflect in the dashboard.
In the navigation pane, go to Settings > Endpoints > General > Advanced features
Scroll down to Microsoft Secure Score and toggle the setting to On.
Select Save preferences.
How it works
Microsoft Secure Score for Devices currently supports configurations set via Group Policy. Due to the current partial Intune support, configurations which might have been set through Intune might show up as misconfigured. Contact your IT Administrator to verify the actual configuration status in case your organization is using Intune for secure configuration management.
The data in the Microsoft Secure Score for Devices card is the product of meticulous and ongoing vulnerability discovery process. It is aggregated with configuration discovery assessments that continuously:
Compare collected configurations to the collected benchmarks to discover misconfigured assets
Map configurations to vulnerabilities that can be remediated or partially remediated (risk reduction)
Collect and maintain best practice configuration benchmarks (vendors, security feeds, internal research teams)
Collect and monitor changes of security control configuration state from all assets
Which service includes the Attack simulation training feature?
Options:
Answer:
Microsoft Defender for Cloud Apps
Answer:Microsoft Defender for Office 365
Answer:Microsoft Defender for Identity
Answer:Microsoft Defender for SQL
Answer:BMicrosoft places Attack simulation training under the email and collaboration protection workloads of Microsoft Defender for Office 365 (MDO). The official product guidance describes it as a built-in capability that “lets you run realistic attack scenarios in your organization to identify vulnerable users and train users to recognize and report phishing and other social-engineering techniques.” Microsoft further notes that Attack simulation training “provides editable phishing payloads, credential-harvesting and attachment scenarios, landing pages, user training, and detailed reporting,” enabling security teams to measure compromise rates and improve user resilience over time. The service scope is explicit: “Attack simulation training is a feature of Microsoft Defender for Office 365 Plan 2,” and it is included in suites that contain MDO P2 such as Microsoft 365 E5 and Office 365 E5. In the Microsoft 365 Defender portal, you access it under Email & collaboration → Attack simulation training, where admins can create simulations, target groups, assign training, and review metrics like repeat offenders, resilience score, and simulation results. By design, this feature is not part of Microsoft Defender for Cloud Apps (cloud app security and CASB functions), not part of Microsoft Defender for Identity (on-prem AD identity threat detection), and not part of Defender for SQL. Therefore, the Microsoft SCI documentation aligns that the correct service hosting Attack simulation training is Microsoft Defender for Office 365 (Plan 2).
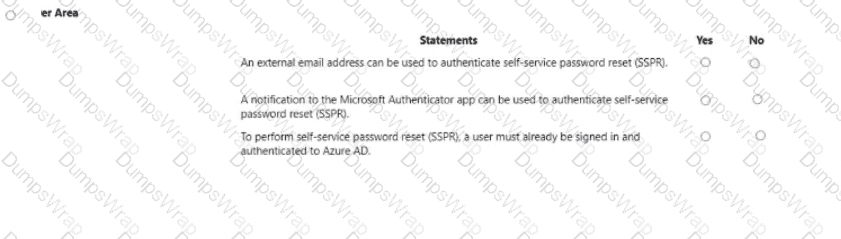
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
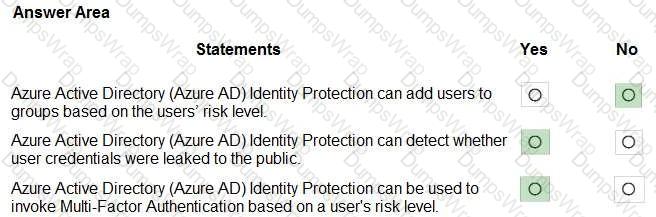
Microsoft’s Identity Protection provides risk-based detections and automated policies—not group management. Microsoft Learn explains that Identity Protection “uses detections to identify potential vulnerabilities affecting your organization’s identities” and exposes user risk and sign-in risk for policy decisions. It does not support adding users to groups by “risk level”; group membership is handled by static or dynamic rules based on directory attributes, while risk is a transient signal surfaced to policies.
Identity Protection includes specific detections such as “Leaked credentials”, where Microsoft’s threat intelligence finds credentials “on the dark web or other dumps,” and flags the affected account as risky. This directly confirms the ability to detect whether credentials have been exposed publicly.
For enforcement, Identity Protection policies and Conditional Access can require stronger authentication when risk is present. The documentation states that you can configure policies to “require multi-factor authentication for sign-ins assessed as risky” and use Conditional Access conditions like User risk or Sign-in risk with the grant control Require multi-factor authentication. Thus, Identity Protection signals can invoke MFA based on risk, but they do not place users into groups.
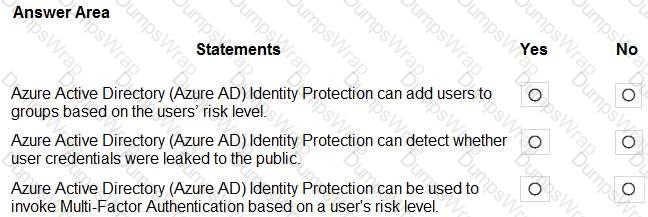
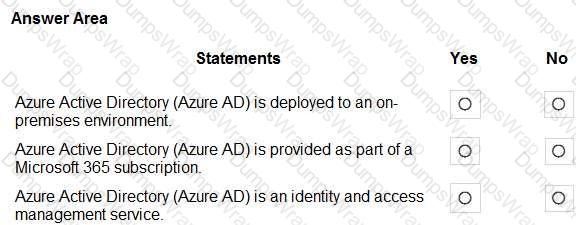
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
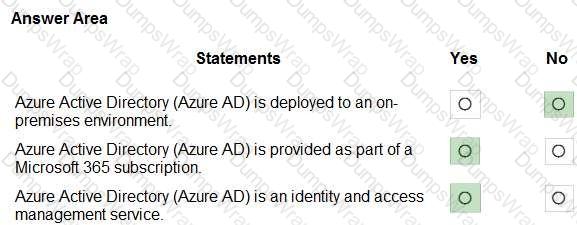
Microsoft’s SCI/Learn content describes Azure AD (now Microsoft Entra ID) as a cloud service, not something you install on-premises. The docs state Azure AD is a “cloud-based identity and access management service” that “helps your employees sign in and access resources.” This clarifies the third statement (IAM service) as Yes, and the first statement (on-premises deployment) as No, because the native on-prem directory is Windows Server Active Directory, whereas Azure AD runs in Microsoft’s cloud and can be synchronized with on-prem AD via tools like Azure AD Connect.
Microsoft also explains licensing/availability: the service comes in several editions, and the free/Office 365 tier is included with many suites. The documentation explicitly notes that Azure AD is “included with subscriptions such as Microsoft 365” (formerly Office 365) and provides tenant-wide identity for those services. Therefore, stating that Azure AD is provided as part of a Microsoft 365 subscription is Yes.
In summary: Azure AD/Entra ID is a cloud identity and access management platform; it’s not deployed on-premises, and Microsoft 365 subscriptions include an Azure AD tenant/edition to manage users, groups, apps, and access policies.
Which Microsoft Purview data classification type supports the use of regular expressions?
Options:
exact data match (EDM)
fingerprint classifier
sensitive information types (SlTs)
trainable classifier
Answer:
CExplanation:
Sensitive Information Types (SITs) support regular expressions (regex), which allow for custom pattern matching to detect sensitive content like credit card numbers, social security numbers, or custom identifiers. Regex is fundamental to the detection logic within SITs.
SCI Extract: " Sensitive information types use pattern matching techniques, including regular expressions, keyword matches, and checksums to identify sensitive data. "
Which portal contains the solution catalog?
Options:
Microsoft 365 Apps admin center
Microsoft 365 Defender portal
Microsoft 365 admin center
Microsoft Purview compliance portal
Answer:
DExplanation:
In Microsoft’s SCI materials, the Solutions catalog is described as part of the Microsoft Purview experience: “The Microsoft Purview compliance portal is the home for solutions to manage your organization’s data security and compliance needs.” Within this portal, Microsoft states that “the Solutions catalog provides a single place to discover, learn about, and set up Microsoft Purview solutions.” The catalog organizes capabilities across compliance domains, for example “Information Protection, Data Lifecycle Management, Data Loss Prevention, Insider Risk Management, eDiscovery, Audit, and Compliance Manager,” and from the catalog “administrators can open setup guides and configuration wizards for each solution.” This positioning makes the Purview compliance portal the correct portal when you are asked where the solution catalog lives.
By comparison, the Microsoft 365 admin center focuses on tenant administration and licensing, the Microsoft 365 Defender portal consolidates threat protection and security operations, and the Microsoft 365 Apps admin center targets Office app management and servicing. None of these are identified as the home of the Purview Solutions catalog. Therefore, the portal that contains the solution catalog is the Microsoft Purview compliance portal.
What can you protect by using the information protection solution in the Microsoft 365 compliance center?
Options:
computers from zero-day exploits
users from phishing attempts
files from malware and viruses
sensitive data from being exposed to unauthorized users
Answer:
DExplanation:
Microsoft Purview Information Protection (in the Microsoft 365 compliance center) enables you to discover, classify, label, and protect sensitive information across emails, documents, and other data stores. Labels and policies can enforce encryption, access restrictions, and visual markings, helping prevent unauthorized disclosure of sensitive data—inside or outside your organization.
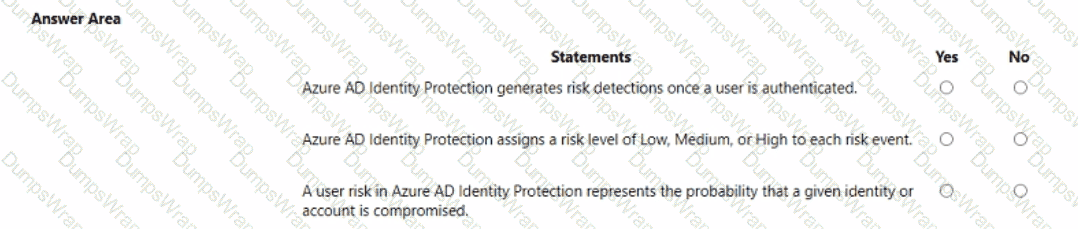
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
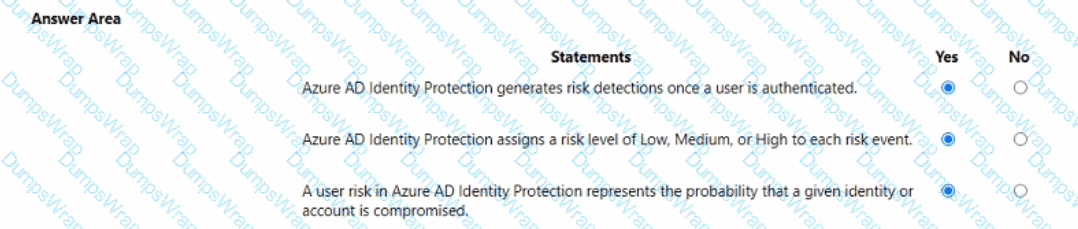
Microsoft describes Identity Protection as a capability that “detects risky users and risky sign-ins using real-time and offline detections and allows you to configure automated responses.” Microsoft is explicit that detections aren’t limited to after authentication; rather, signals are evaluated during sign-in and also by offline analytics, where “some detections are offline and can take up to 48 hours to appear.” Therefore, saying it only “generates risk detections once a user is authenticated” is incorrect.
For risk scoring, Microsoft states that Identity Protection “assigns a risk level to each detection,” and that “risk levels are Low, Medium, or High,” which are then used by user-risk and sign-in-risk policies to drive remediation (for example, requiring password change or MFA).
Microsoft also defines the two core risk concepts: “User risk represents the probability that a given identity or account is compromised,” while “Sign-in risk represents the probability that a given authentication request isn’t authorized by the identity owner.” These definitions underpin Conditional Access and Identity Protection policies that can require additional verification or block access based on the assessed risk.
Taken together, the documentation confirms: detections are not restricted to post-authentication (No), detections carry Low/Medium/High levels (Yes), and user risk is the probability the identity is compromised (Yes).
Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
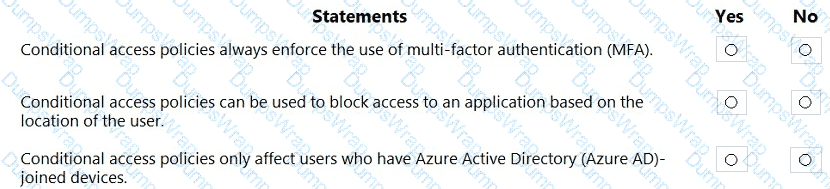
Options:
Answer:

Explanation:
Microsoft Entra Conditional Access evaluates signals to make real-time access decisions. Microsoft describes it as bringing “signals together to make decisions and enforce organizational policies,” where administrators choose controls such as Block access, Require multi-factor authentication, Require device to be marked as compliant, or Require hybrid Azure AD joined device. Because MFA is only one of several grant controls, it is incorrect that policies always enforce MFA; they can also simply block, allow, or require other conditions.
Location is a first-class condition. Microsoft states you can define named locations (by countries/regions or IP ranges) and then use them in policy conditions to block or grant access. A common scenario is “Block access from specific locations” or require additional controls when a sign-in originates from an untrusted network. Therefore, Conditional Access can block access to an application based on user location.
Finally, Conditional Access targets users, groups, workload identities, and cloud apps regardless of device join state. Device-related conditions and filters are optional; policies are not limited to “Azure AD-joined devices.” Controls like Require device to be marked as compliant or Require Hybrid Azure AD joined device are only enforced if configured. Hence, Conditional Access does not only affect users on Azure AD-joined devices.
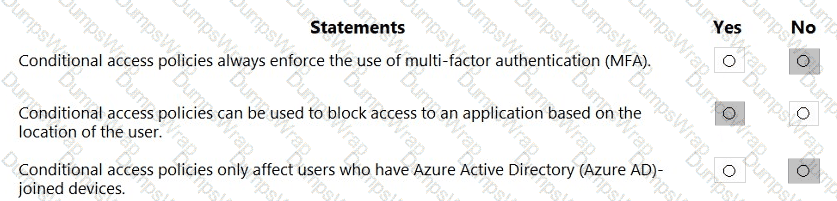
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
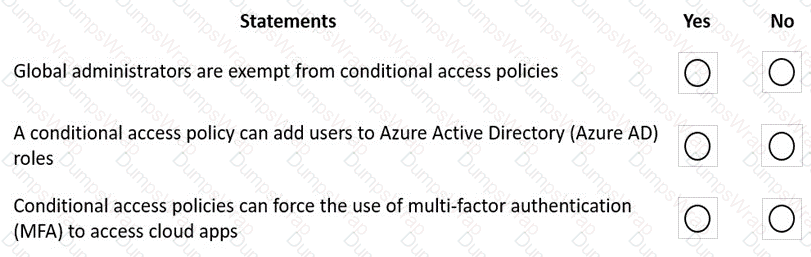
Options:
Answer:

Explanation:
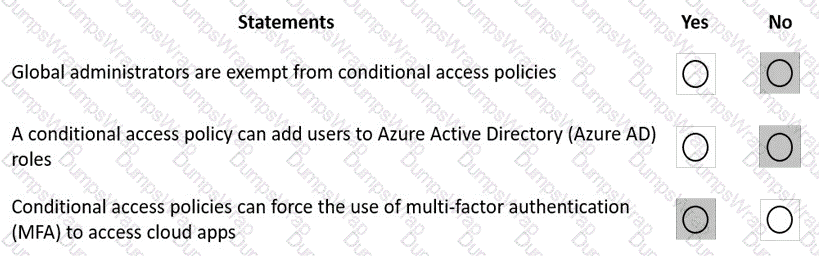
Microsoft explains that Conditional Access (CA) evaluates signals and then enforces access decisions using grant and session controls: “Conditional Access policies are enforced after first-factor authentication is completed” and are used to “make access control decisions.” CA policies target users and groups—including administrators—unless explicitly excluded. Microsoft guidance recommends excluding only break-glass accounts: “Customers with Azure AD roles such as Global administrator should have at least one emergency access account excluded from policies.” This means admins are not exempt by default; they are in scope unless you configure exclusions.
CA does not manage directory role assignments; that is handled by role assignment and Privileged Identity Management (PIM). CA’s grant controls focus on access conditions: “Grant access… Require multi-factor authentication” and Microsoft lists a common baseline: “Require multi-factor authentication for all users.” Therefore, CA can require MFA to access cloud apps, but it cannot add users to Azure AD roles.
These statements from Microsoft’s SCI materials confirm the outcomes: Admins are not inherently exempt (No), CA cannot assign roles (No), and CA can force MFA for app access (Yes).
Select the answer that correctly completes the sentence.
Options:
Answer:
Explanation:
Which feature is included in Microsoft Entra ID Governance?
Options:
Verifiable credentials
Permissions Management
Identity Protection
Privileged Identity Management
Answer:
DExplanation:
Microsoft defines Microsoft Entra ID Governance as the capability to manage “the identity lifecycle, access lifecycle, and privileged access” so organizations can ensure “the right people have the right access to the right resources at the right time.” The product family explicitly lists the following core features: “Lifecycle workflows, Entitlement management, Access reviews, and Privileged Identity Management (PIM).” Microsoft further explains that PIM helps you “manage, control, and monitor access within your organization,” enabling just-in-time elevation, approval workflows, MFA/justification on activation, and detailed auditing for privileged roles. By contrast, the other options are separate Microsoft Entra offerings outside ID Governance: Verifiable credentials (Microsoft Entra Verified ID) issues and validates digital credentials; Permissions Management (Microsoft Entra Permissions Management) provides CIEM for multi-cloud permissions; and Identity Protection offers risk-based detection and policies for sign-ins and users. Therefore, among the choices, the feature that is included in Microsoft Entra ID Governance is Privileged Identity Management (PIM), which is specifically called out by Microsoft as a pillar of ID Governance and is used to govern privileged access with policy-based controls, time-bound assignments, approvals, and comprehensive auditability.
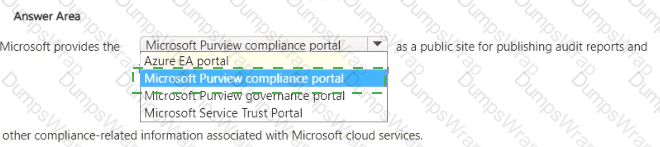
completes the sentence.
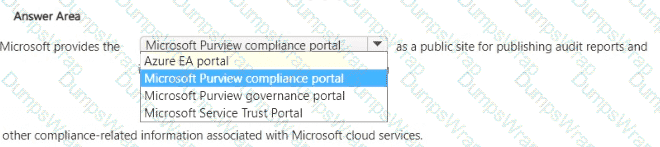
Options:
Answer:

Explanation:
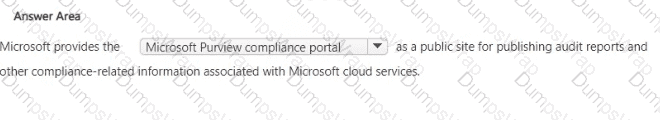
In Microsoft’s Security, Compliance, and Identity guidance, the Microsoft Service Trust Portal (STP) is identified as the public destination where Microsoft publishes independent audit reports, compliance certifications, assessment reports, and trust-related documentation for Microsoft cloud services. The documentation explains that the STP provides customers with access to materials such as SOC 1/SOC 2 reports, ISO/IEC certifications, audit summaries, and compliance guides, enabling organizations to evaluate Microsoft’s controls and map them to their own regulatory requirements. The STP is expressly positioned for transparency and due diligence, allowing customers and auditors to review Microsoft’s compliance posture and understand how Microsoft manages security, privacy, and compliance across its cloud platforms.
By contrast, the Microsoft Purview compliance portal is a tenant-admin portal used to configure and manage compliance solutions (e.g., DLP, Information Protection, eDiscovery, Insider Risk, Compliance Manager) within your organization—not a public repository of Microsoft’s audit artifacts. The Microsoft Purview governance portal focuses on data governance and cataloging scenarios. The Azure EA portal is used for Enterprise Agreement billing and usage management. Therefore, the public site for publishing audit reports and other compliance-related information for Microsoft cloud services is the Microsoft Service Trust Portal.
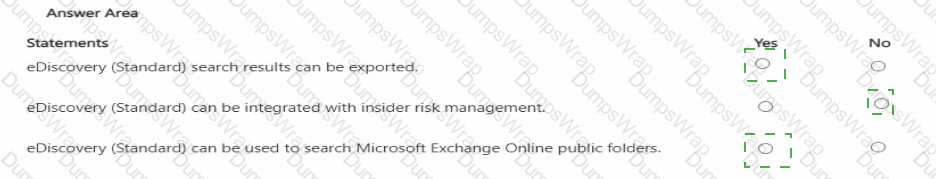
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
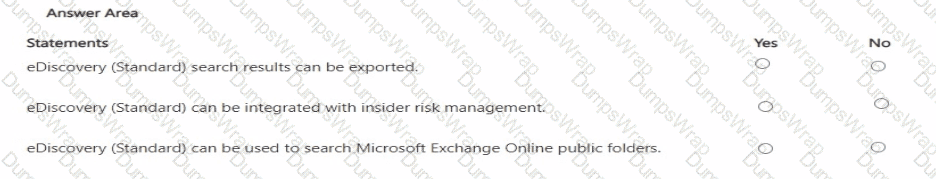
Options:
Answer:

Explanation:
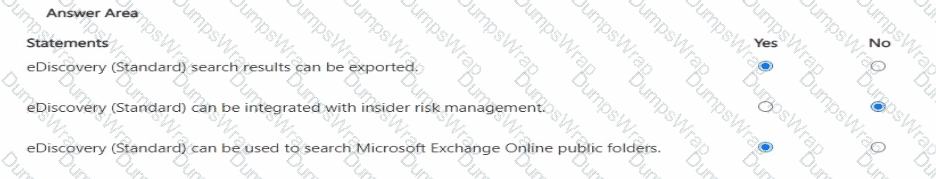
In Microsoft Purview, eDiscovery (Standard) (formerly Core eDiscovery) provides case management, holds, searches, and export. Microsoft describes that eDiscovery (Standard) lets investigators “search across Microsoft 365 data sources and export the results,” including options to export native files, email to PST, and CSV reports for further review. It uses the same Content search engine and supports selecting locations such as **Exchange Online mailboxes, Microsoft 365 Groups, Teams, SharePoint sites, OneDrive accounts, and Exchange public folders,” enabling organization-wide discovery that includes public folders.
Integration for end-to-end legal review from Microsoft Purview Insider Risk Management is specifically aligned to eDiscovery (Premium) (formerly Advanced eDiscovery). Insider Risk cases provide actions like “Send to eDiscovery (Premium)” to create a review set and apply advanced processing, analytics, and review workflows. Those advanced integrations (review sets, analytics, legal hold communications) are not features of eDiscovery (Standard). Therefore: exporting results (Yes), Insider Risk integration (No, as it targets eDiscovery Premium), and searching Exchange Online public folders (Yes) are the correct evaluations based on the Microsoft Security, Compliance, and Identity study materials for Purview eDiscovery capabilities.
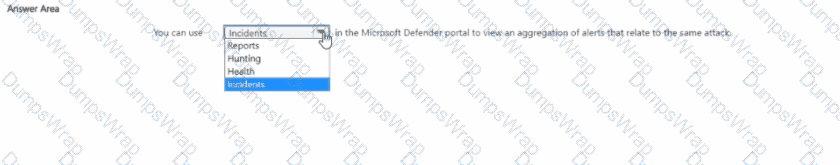
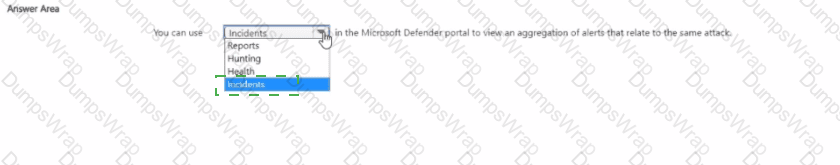
Select the answer that correctly completes the sentence.
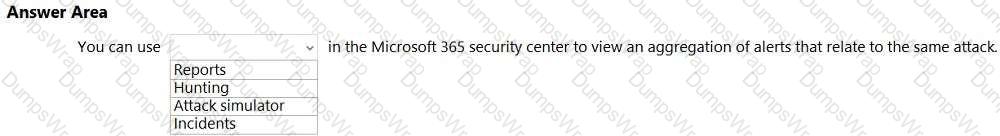
Options:
Answer:

Explanation:
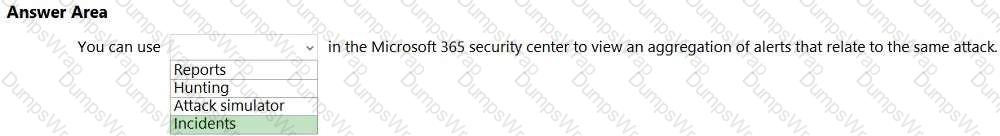
In Microsoft 365 Defender (Microsoft 365 security center), Incidents are designed to consolidate and correlate security signals so analysts can see the full scope of an attack. Microsoft’s documentation explains that an incident is “a collection of related alerts that, when viewed together, provide a richer context for the attack and its impact.” The service “automatically groups alerts that are likely to be associated with the same threat activity,” which allows security teams to investigate a single incident rather than many fragmented alerts. Microsoft further notes that incidents “aggregate alerts, affected assets (users, devices, mailboxes), evidences, and entities into one view,” helping analysts triage, investigate, and remediate more efficiently.
This is distinct from other areas in the portal: Reports provide trend and posture reporting; Hunting offers proactive, query-based threat hunting across raw data; and Attack simulator (in Defender for Office 365) is used to run training and awareness simulations (e.g., phishing), not to aggregate real alerts. Therefore, when you need to “view an aggregation of alerts that relate to the same attack” in the Microsoft 365 security center, the correct place is Incidents, which presents the correlated attack story and enables end-to-end response and remediation from a single, consolidated record.
You company is evaluating various security products, including a security information and event management (SIEM) solution. You need to provide information about the functionality of SIEM solutions. What is a function of a SIEM solution?
Options:
the ability to review network activity and provide reports about which applications and services can communicate
an alerting system that triggers an alert when users reach their Azure spending limit
the ability to review logs and provide reports about malicious activity
automated incident remediation
Answer:
CTo which type of resource can Azure Bastion provide secure access?
Options:
Azure Files
Azure SQL Managed Instances
Azure virtual machines
Azure App Service
Answer:
CExplanation:
Azure Bastion is a managed PaaS service that provides secure and seamless RDP/SSH connectivity to your Azure virtual machines directly from the Azure portal over TLS/HTTPS. SCI and Azure security documentation summarize it as eliminating public IP exposure on VMs by using a fully managed bastion host deployed inside your virtual network. Users connect through their browser and the service brokers the RDP or SSH session, which “protects your VMs from exposing RDP/SSH to the Internet.” Bastion does not provide access to Azure Files, SQL Managed Instance, or App Service; it is specifically built to secure management access to VMs without requiring a VPN or public endpoints. Therefore, the resource type Azure Bastion securely connects to is Azure virtual machines.
Select the answer that correctly completes the sentence.
Options:
Answer:
Explanation:
In Microsoft Sentinel, playbooks are the feature that integrates with Azure Logic Apps to automate response. Microsoft’s documentation describes them as “collections of procedures that can be run from Microsoft Sentinel in response to an alert” and clarifies that “playbooks are built on Azure Logic Apps” providing a workflow engine and a gallery of connectors to other Microsoft and third-party services. Playbooks can be triggered automatically from analytics rules or manually from incidents and alerts, enabling orchestration such as assigning owners, creating tickets, disabling accounts, blocking IPs, or posting to collaboration channels. The platform emphasizes that the Logic Apps foundation gives security teams a visual designer, managed connectors, and run history to track execution and outcomes. In short, Sentinel uses playbooks to “automate and orchestrate responses to alerts and incidents”, reducing mean-time-to-respond and standardizing actions across your SOC. Other Sentinel components serve different purposes: analytic rules detect threats, hunting queries aid proactive investigation, and workbooks provide dashboards and visualizations. Therefore, the correct completion is: Microsoft Sentinel playbooks use Azure Logic Apps to automate and orchestrate responses to alerts.
What can you use to ensure that all the users in a specific group must use multi-factor authentication (MFA) to sign in to Azure AD?
Options:
Azure Policy
a communication compliance policy
a Conditional Access policy
a user risk policy
Answer:
CExplanation:
According to Microsoft’s Security, Compliance, and Identity (SCI) documentation and learning paths (specifically SC-900, SC-300, and Azure AD Identity Protection modules):
“Conditional Access policies in Azure AD are the primary method for enforcing access controls based on specific conditions such as user, group, location, device compliance, and application.”
In this case, the organization can configure a Conditional Access policy that targets a specific Azure AD group and requires MFA as a condition before access is granted. The typical policy setup includes:
Assignments: Target users or groups (e.g., “Finance Department Users”).
Cloud apps or actions: Specify which applications or services are protected (e.g., Microsoft 365).
Access controls: Set the control to “Require multi-factor authentication.”
Microsoft’s SCI training materials further state:
“Conditional Access enables administrators to enforce MFA for specific users, groups, or scenarios. It provides flexibility to protect access without enabling MFA globally for all users.”
Other options explained:
Azure Policy (A) applies to Azure resources, not user authentication.
Communication compliance policy (B) monitors message content for compliance violations.
User risk policy (D) is part of Azure AD Identity Protection, enforcing MFA based on detected user risk levels, not group membership.
Therefore, the verified and correct answer is: ✅ C. a Conditional Access policy.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
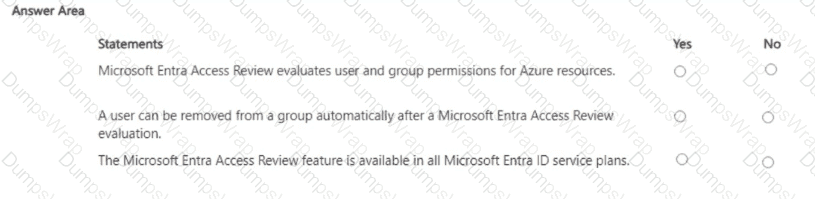
Options:
Answer:

Explanation:

Microsoft Entra Access Reviews are designed to help organizations regularly validate and right-size access. Microsoft’s documentation explains that access reviews can target group memberships, enterprise app assignments, Azure AD roles, and Azure resource roles (via Privileged Identity Management), allowing reviewers to assess whether users, service principals, or groups should retain access to Azure resources—confirming the first statement. Access Reviews support automation: you can configure a review to “Auto-apply results”, so when the review ends, users who were denied or not reviewed are automatically removed from the group, application assignment, or role—validating the second statement. Finally, Access Reviews are a Premium P2 capability (now Microsoft Entra ID P2) alongside PIM and advanced identity governance. They are not included in all service plans; tenants require the appropriate P2 licenses for reviewers and users in scope—therefore the third statement is No.
You need to identify which cloud service models place the most responsibility on the customer in a shared responsibility model.
in which order should you list the service models from the most customer responsibility (on the top) to the least customer responsibility (on the bottom)? To answer, move all models from the list of models to the answer area and arrange them in the correct order.
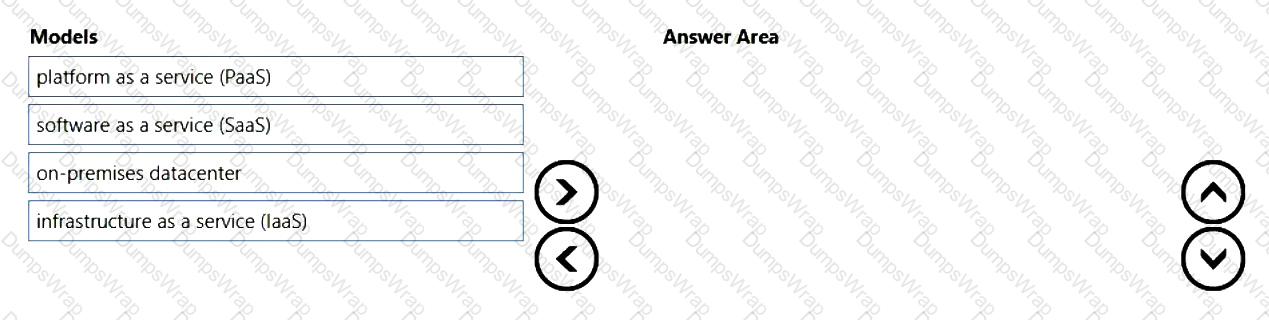
Options:
Answer:
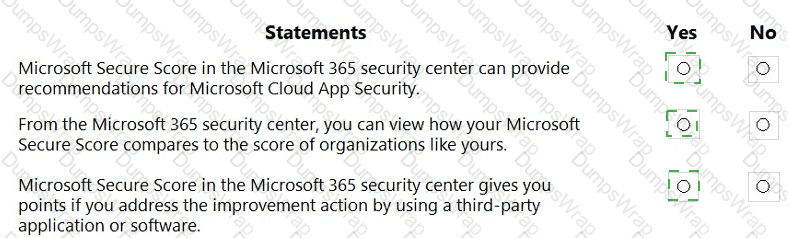
Explanation:
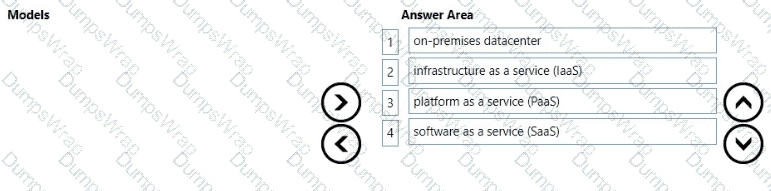
Microsoft’s shared responsibility guidance explains that the customer’s responsibility decreases as you move from on-premises to SaaS. In an on-premises datacenter, “you own the whole stack—applications, data, runtime, middleware, OS, virtualization, servers, storage, and networking.” With IaaS, the cloud provider operates the physical datacenter and virtualization, while “you’re responsible for configuring and managing the guest OS, network controls, identity, applications, and data.” With PaaS, the provider operates more of the stack so that “the cloud provider manages the platform (OS, middleware, and runtime) and you focus on your applications and data.” Finally, with SaaS, responsibility is minimized for customers because “the service provider manages the application and underlying infrastructure; customers primarily manage identity, data, and access/usage.”
These Microsoft Learn statements map directly to the requested order—from most customer responsibility (on-premises) to least (SaaS)—with IaaS and PaaS in between, reflecting the progressive shift of operational and security controls from the customer to the cloud provider as the service model moves up the stack.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
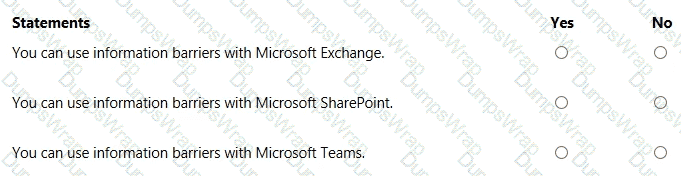
Options:
Answer:

Explanation:
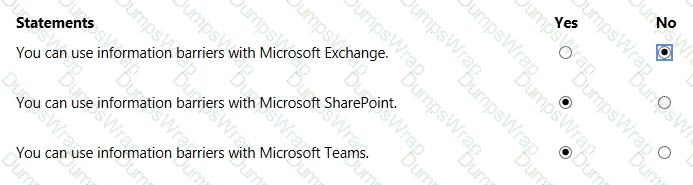
Microsoft defines Information Barriers (IB) as policies that “restrict communication and collaboration between specific users or groups” to meet regulatory or conflict-of-interest requirements. In Microsoft 365, IB enforcement is provided across collaboration workloads—most notably Microsoft Teams and, with IB v2, SharePoint and OneDrive—so that users placed in segments that shouldn’t interact are prevented from chatting, meeting, or sharing files with one another. The service “controls who can communicate and collaborate with whom” and applies those controls to Teams chats/channels and SharePoint/OneDrive sites and files so that segment boundaries are honored when users attempt to share or access content.
By contrast, Exchange Online email is not a supported enforcement surface for Information Barriers; IB does not block or route mail. Email restrictions are handled with other capabilities (for example, mail flow rules), not IB. Therefore, in alignment with Microsoft’s SCI guidance: IB does work with Microsoft Teams and with Microsoft SharePoint/OneDrive, but it does not provide policy enforcement for Exchange email.
Select the answer that correctly completes the sentence.
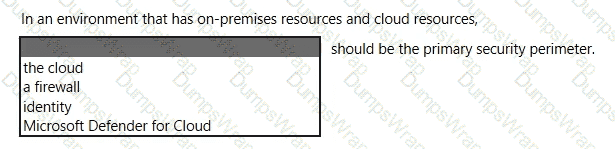
Options:
Answer:

Explanation:
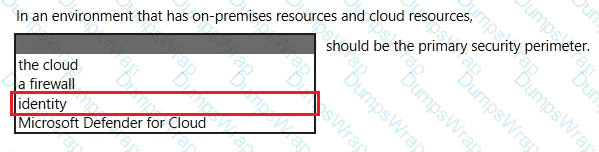
Microsoft’s security guidance for hybrid and cloud environments adopts the Zero Trust approach, which explicitly positions identity as the primary boundary for access decisions. Microsoft states that in modern, distributed environments, “the traditional network perimeter is no longer sufficient” and that identity becomes the new security perimeter for protecting access to resources across on-premises and cloud. In Zero Trust, access is granted based on who the user or workload is, the risk of the sign-in, the device health, and the context of the session. Microsoft summarizes this shift as: “Identity is the control plane,” emphasizing that authentication, authorization, and continuous evaluation of trust are enforced through identity-centric controls such as Conditional Access, multifactor authentication, Privileged Identity Management, device compliance, and session controls.
While tools like firewalls and services such as Microsoft Defender for Cloud remain important layers in a defense-in-depth strategy, they are not the primary perimeter in a hybrid model. Because users, devices, and applications operate from anywhere, identity is the consistent, verifiable layer through which policy is enforced for both on-premises and cloud resources. Therefore, in an environment that spans on-premises and cloud, Microsoft recommends treating identity as the primary security perimeter, applying continuous verification and least-privilege access through identity-driven policies.

