Nutanix Certified Professional - Network and Security (NCP-NS) 7.5 Questions and Answers
What is the role of the Network Controller in Flow Virtual Networking?
An administrator is building a VPC... VPC CIDR: 10.10.0.0/16 Subnet CIDR: 10.10.10.0/24 "Ext_Net_Ext" (NAT): 192.168.1.0/24 "Ext_Net_Internal" (Routed): 172.16.1.0/24 The on-premises application server has an IP address of 172.16.2.50/24. A VM (10.10.10.100) in the VPC Subnet can reach the internet but cannot reach the on-premises server. Which static route needs to be added to the VPC route table to resolve this?
An administrator is configuring a Nutanix environment for Flow Network Security Next-Gen. Where should the MTU be set to ensure that Geneve encapsulation overhead is properly accounted for?
What is the additional resource requirement for each Prism Central VM when enabling Flow Virtual Networking on a Small Prism Central deployment?
What type of policy would be used to block all traffic between VMs in the category Environment:Sandbox and VMs in the category Environment:Production?
An administrator needs to allow communication between several VPCs without requiring to configure routes in the physical network or using a dynamic routing protocol like BGP. How should the administrator satisfy this requirement?
Refer to Exhibit:
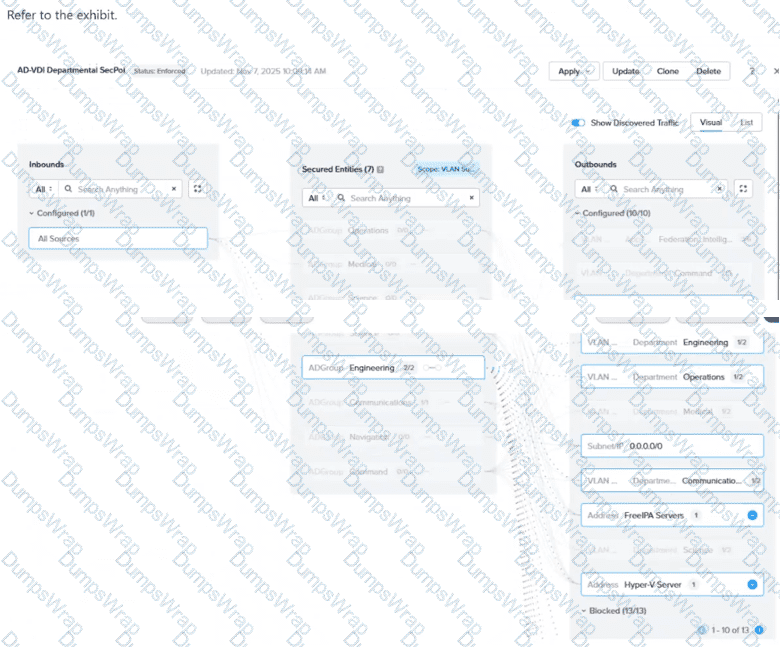
In the AD-VDI Departmental SecPol policy shown in the exhibit, ADGroup: Engineering is configured as a secured entity in a VDI Security Policy. Prism Central shows 2 / 2 active sessions under this group, but the administrator confirms that three Engineering users are currently logged in to persistent VDI desktops. The third user's VM shows no ADGroup assignment in its VM details in Prism Central, even after the user has successfully logged in. All three users are members of the same AD group, and the Domain Controller event logs confirm a successful interactive login for the third user. Which condition explains why the third user's VM is not being assigned the ADGroup: Engineering category?
An administrator must delegate management of a single tenant VPC to a junior engineer. The engineer should be able to modify that VPC but must not see or change any other VPCs or networking configurations in Prism Central. The administrator wants to meet this requirement using RBAC. Which action should the administrator take to meet this requirement?
Before creating a new Application Security Policy in Prism Central, what prerequisite must exist?
An administrator has configured a VPC with multiple overlay subnets and attached a VPN gateway using IPSec. After enabling Jumbo Frames on the physical network, VMs are still experiencing packet drops. What is the most likely reason?
An administrator has been tasked with upgrading the Nutanix cluster to a newer version of AOS. The cluster is running a mix of different versions across nodes... What is the recommended first step when upgrading a Nutanix cluster with different AOS versions across nodes?
An administrator wants to configure the subnet 10.1.1.0/24 to stretch across two VPCs over a Network Gateway in VXLAN mode. The VMs on this subnet need to communicate with a traffic pattern of size 2000 Bytes. What is the minimum MTU required in the underlay network to ensure communication happens without fragmentation or traffic drops?
Which step is required to prepare an AHV cluster for Flow Network Security Next-Gen?
An administrator is deploying a multi-tier (web, app, database) application on a Nutanix cluster using AHV. The administrator needs to allow internal communication between tiers and provide external access to the web tier. How should the administrator satisfy this requirement?
After creating a BGP session in Flow Virtual Networking, the session status remains down. Which log should an administrator use first in Prism Central to troubleshoot the issue?
An administrator recently deployed a new set of virtual machines... 3-tier web application... restricted as follows: Only application VMs can talk to database VMs on port 3306 Frontend VMs should only communicate with application VMs on port 8080 Which action will correctly create and configure the Security Policies in Nutanix Flow to satisfy this task?
Which action allows an administrator to reuse a single existing policy in a different scope?
A service-insertion firewall VM protects user VMs access to the internet. The virtual and physical switches, as well as all user VMs, currently use the default MTU size of 1500. Everything functions normally until a user VM is migrated to another host. After the migration, the user reports that some websites fail to load while ping to those same sites still succeeds. Routing and security policies appear normal. Which two configuration changes could resolve the issue? (Choose two.)
An administrator is responsible for managing user access to a Nutanix cluster... configure custom user roles... What is the first step in configuring and managing user roles for a Nutanix cluster?
While configuring third-party services (Service Insertion) in Flow Network Security Next-Gen, an administrator notices dropped packets when redirecting traffic through a network function. Which configuration change would address this issue?
An administrator is using Flow Network Security to secure a 3-tier application and has already created and assigned the categories. The administrator does not have the details of the rules that need to be allowed to secure the application. How can the administrator use Flow Network Security to monitor the traffic and help with the policy creation without impacting the applications connectivity?
What is the first step in preparing a Nutanix cluster for Flow Virtual Networking?
When cloning a Flow Network Security policy, what should be verified before enabling Enforce mode?
A newly-deployed Flow Virtual Networking VPC environment is experiencing connectivity issues... A packet capture on the physical switch shows packets are being fragmented. What is the probable cause of the packet fragmentation and performance issues?
A new multi-tier application is being deployed across several subnets in a Nutanix environment. The security team wants to create a Flow Network Security Policy to restrict traffic between the tiers, but the complete matrix of required network ports and protocols is not fully documented. Which strategy should the team employ first to accurately capture the necessary communication patterns without risking application outage?
An administrator plans to upgrade a Nutanix cluster running AHV and Prism Central. The current cluster is on AOS 6.10, and the administrator wants to move to AOS 7.3 while ensuring all components remain compatible. What is the correct upgrade order to minimize downtime and maintain cluster functionality?
What does placing a policy in Monitor mode accomplish?
Which policy mode blocks all traffic that is not explicitly allowed by the policy?
Which statement is correct about cloning Application Security Policies?
Refer to Exhibit:
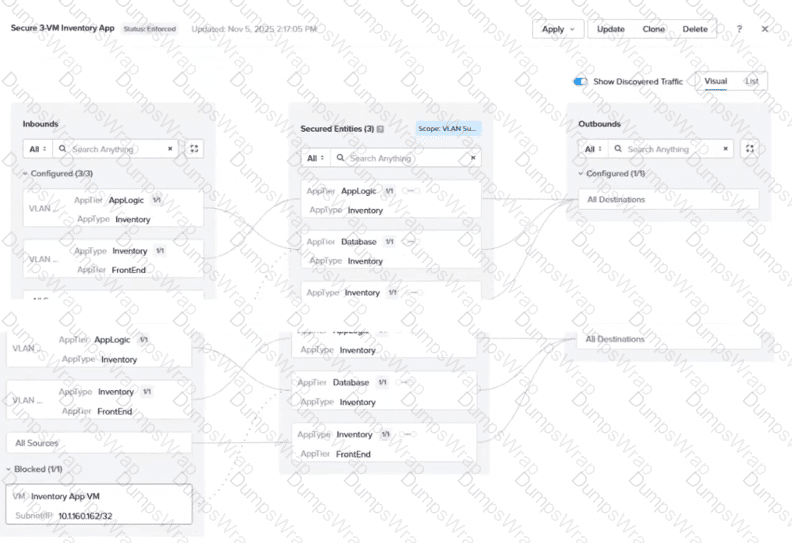
An administrator is reviewing an enforced security policy "Secure 3-VM Inventory App", as shown in the exhibit. The policy's inbound rules are configured to allow traffic from specific sources to each tier of the application. The visualization shows one blocked traffic flow. Based on the information presented in the exhibit, which statement best describes this behavior?
Which two options are supported as a Secured Entity in Flow Network Security Application Policies? (Choose two.)

