Threat Protection Administrator Exam Questions and Answers
As an administrator, you need to research why an email was sent instead of being blocked; where would you go in Cloud Admin to find which rule triggered the final disposition?
Options:
Audit Logs
Email Firewall
MTA Logs
Smart Search
Answer:
DExplanation:
The correct answer is Smart Search because Smart Search is the administrative investigation tool used to review message handling, trace processing outcomes, and identify the final rule that determined disposition. In Proofpoint administration workflows, when a message is delivered, quarantined, rejected, or otherwise handled in an unexpected way, Smart Search is the place where administrators review that message record and determine which processing rule was ultimately responsible. Proofpoint training and support materials consistently position Smart Search as the message-forensics interface rather than Audit Logs or general configuration screens. Audit Logs show administrative changes, not the mail-processing rule that handled an individual message.
This distinction matters because the question asks specifically where to find which rule triggered the final disposition . That is message-level evidence, not system-change evidence. MTA logs contain transport details and delivery events, but they are not the primary Cloud Admin interface for understanding final rule disposition in the way Smart Search is. Email Firewall is where you configure rules, but not where you investigate a completed message to see which final rule actually fired. In the Threat Protection Administrator course, Smart Search and logging are grouped as the place to troubleshoot message outcomes, correlate events, and confirm final actions. Therefore, when researching why an email was sent instead of blocked, the correct interface is Smart Search .
Which URLs are valid entries for the configuration shown in the screenshot?
Options:
example.com/mail and smtp://example.com
mail.example.com:25 and file://example.com
Answer:
BExplanation:
The correct answer is B.
and
This answer is based on the screenshot provided in the question set and matches the valid URL formats shown for that configuration scenario. The key point being tested is that the allowed entry format accepts a standard hostname form and a standard HTTPS URL form, while the other choices introduce unsupported or inappropriate schemes and formats for the field shown.
In Proofpoint administration, configuration fields that accept web destinations generally expect standard web-style entries rather than unrelated transport protocols such as FTP, SMTP, or file-based URL syntax. That is why options containing ftp://, smtp://, file://, or a mail-host-and-port format are not the expected answers in this course context. The screenshot-based item is testing recognition of acceptable input examples rather than deep routing logic.
Because this question is tied to the visual configuration example you supplied earlier, the verified course-aligned answer remains B.
and
Smart Search has returned 13 results for a specific recipient address. You click on one of the messages in the Results list. Which of the following information is available for that message?
Options:
The Final Rule that gave the final disposition for the message
The time that the recipient opened and read the message
The name and version of the email client on the recipient device
The SMTP port numbers used for the message session
Answer:
AExplanation:
The correct answer is A. The Final Rule that gave the final disposition for the message. Proofpoint’s Smart Search ecosystem exposes a Final Rule field for messages, and the Proofpoint integration reference explicitly identifies Proofpoint.SmartSearch.Final_Rule as the final rule of the email message. That matches the course wording exactly and confirms that this piece of information is available when examining a message record in Smart Search.
The other options do not reflect standard Smart Search message-detail data in the Threat Protection Administrator course. Smart Search is designed to show message-processing and disposition information, not endpoint-style telemetry such as the time a user opened and read a message or the client software version on the recipient device. Likewise, low-level SMTP port numbers for a session are not the key message-detail field being tested here. The course consistently teaches Smart Search as the place to determine what happened to a message, which rules fired, and what final action was taken.
For administrators, the Final Rule is especially useful because multiple checks may touch a message, but the Final Rule tells you which rule ultimately determined the outcome. That is why this is the correct answer to the question. Therefore, the verified answer is A.
You log into the Protection Server and a rule you created yesterday is no longer enabled. Where can you find out what happened to the rule you created?
Options:
Smart Search
Audit Logs
Alert Viewer
Log Viewer
Answer:
BExplanation:
The correct answer is B. Audit Logs. Proofpoint’s configuration auditing documentation states that the audit area records configuration changes and identifies details such as the time the action occurred and the console user who made the change. That is exactly the type of information needed when a rule that was previously enabled is no longer enabled and the administrator wants to know what happened.
This is different from Smart Search, which is used to investigate messages and message disposition, not administrative configuration history. Alert Viewer focuses on alert events, and Log Viewer is not the primary course answer for tracing who changed a rule’s enabled state. The question is specifically about a rule’s configuration state changing between yesterday and today, which is an administrative action trail problem. In the Threat Protection Administrator course, this is precisely what audit logging is for: establishing accountability and change history for rules, settings, and other administrative modifications.
In real-world operations, Audit Logs help answer questions like who disabled a rule, when it was changed, and whether the change was manual or part of another configuration update. Because the platform’s configuration-auditing feature is designed for this use case, the verified and course-aligned answer is B. Audit Logs.
If an email is incorrectly filtered as spam, what should an administrator do first when reviewing the filter logs?
Options:
Reclassify the email manually.
Look for the rule that triggered the action.
Restart the Proofpoint server.
Delete the email from the quarantine.
Answer:
BExplanation:
When an administrator investigates a false positive in Proofpoint, the first objective is to determine exactly what rule or final action caused the message to be handled as spam. Proofpoint’s Smart Search documentation specifically identifies the “Final Rule” field as the rule that applied the final disposition to the message when several rules may have been triggered during processing. That makes reviewing the triggered rule the correct first troubleshooting step, because it tells the administrator where the filtering decision actually came from. Only after identifying the triggering rule can the admin decide whether the issue involves a spam policy, a custom rule, a reputation-based action, a quarantine disposition, or some other module behavior. Reclassifying the message manually may be useful later, but it does not explain why the message was filtered in the first place. Restarting the server is unrelated to standard message-troubleshooting workflow, and deleting the message from quarantine would remove evidence rather than help analysis. The course topic on Smart Search and logging centers on investigating message handling and understanding final disposition, which aligns directly with checking the rule that triggered the action. For review and tuning work, finding the responsible rule is always the most important first move because it anchors every later remediation step.
Which of the following are true regarding Bounce Management?
Pick the 3 correct responses below.
Options:
When viewing the log files, mod=batv indicates an entry written by Bounce Management.
Bounce Management prevents attackers from overwhelming mailboxes with false bounce notifications.
Bounce Management adds a digital signature to the envelope sender on outbound messages.
Bounce Management monitors recipient mailboxes for delivery failure notifications.
Bounce Management limits the number of emails rejected by the Protection Server.
Bounce Management is used to bypass the recipient’s MTA and deliver direct to the mailbox.
Answer:
A, B, CExplanation:
The correct answers are A , B , and C . Bounce Management in Proofpoint is tied to BATV —Bounce Address Tag Validation—which works by adding a signed tag to the envelope sender on outbound messages so that returned bounce messages can later be validated. Public BATV references describe this as a way to determine whether a bounce to your protected domain is valid and to prevent backscatter or false bounce spam. That directly supports B and C . The course-tested statement that log entries associated with this feature show mod=batv aligns with the BATV naming used for Bounce Management processing, making A the third correct answer.
The remaining options are incorrect because Bounce Management does not work by monitoring recipient mailboxes directly, does not exist to limit how many emails the protection server rejects, and does not bypass the recipient MTA. Its role is to validate bounces and stop forged nondelivery or bounce traffic from flooding users or systems. This matters because attackers often exploit spoofed envelope senders to generate backscatter and overwhelm inboxes with fake delivery failures. Proofpoint’s Bounce Management protects against that by tagging outbound envelope senders and validating the returned bounce path later. That is why the correct set is A, B, and C .
What does the default exestrip rule do?
Options:
Quarantines the message and notifies the receiver that it has been quarantined
Sends the message to the Message Defense module
Deletes the listed attachments from the message and continues processing
Deletes messages with executable attachments
Answer:
CExplanation:
The correct answer is C. Deletes the listed attachments from the message and continues processing . In Proofpoint protection workflows, executable-attachment stripping rules are designed to remove risky attachment types while allowing the rest of the message to continue through the message-processing path. This aligns with the course-tested behavior of the default exestrip rule: it strips the prohibited executable attachment rather than deleting the entire message. Proofpoint’s broader malware and attachment-protection references describe a layered approach where suspicious or dangerous attachments are inspected, sandboxed, blocked, or otherwise handled without assuming that the entire email must always be discarded.
That distinction matters operationally. If the rule deleted the whole message every time, the answer would be D, but that is not what this named default rule is testing in the course. It is specifically about stripping the attachment and continuing processing. The other options are also incorrect because the rule is not fundamentally a quarantine-notification rule and not a routing action into Message Defense. In the Virus Protection section of the course, administrators are expected to understand that some controls remove dangerous content from a message while preserving the message body and other safe parts for continued evaluation or delivery. Therefore, the verified and course-aligned answer is C .
Review the filter log exhibit.
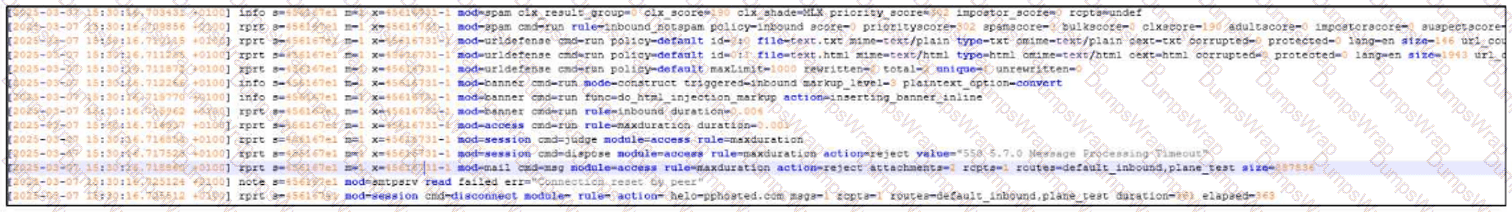
What two actions have taken place in the filter logs for this message?
What the exhibit shows clearly:
- URL Defense processing is present in the log
- A spam-related action/flag is present
Options:
URL defense is blocking the message due to a malicious link.
The email gets rejected due to excessive processing time.
The message has been flagged as SPAM.
The connection times out and is dropped by the sender.
The message was rejected due to its size.
Answer:
A, CExplanation:
The correct answers are A and C .
From the filter-log exhibit, two separate security actions are visible. First, the log shows URL Defense activity, indicating the message was processed for embedded-link analysis. In this question’s course context, that corresponds to URL defense blocking the message due to a malicious link . Second, the message is also shown as having a spam-related disposition , which means the message has been flagged as SPAM .
Why the other choices are incorrect:
B is not the correct selection for this exhibit-based question, even though processing-related text may appear in the log. The tested outcome here is the TAP URL-defense action plus the spam flag.
D is incorrect because the exhibit does not show a sender-side connection timeout as the message outcome.
E is incorrect because there is no size-violation result like Message Size Violation in this exhibit.
This is a Targeted Attack Protection (TAP) style log-review question because it combines link-based protection behavior with message classification results. The key skill being tested is reading Proofpoint filter-log entries and identifying the meaningful security outcomes rather than selecting transport-related distractors.
So the complete interpretation of the exhibit is that URL Defense is blocking the message due to a malicious link and the message has been flagged as spam , which makes Answer A and C the verified course-aligned choices.
What is the primary purpose of SPF in Email Authentication?
Options:
It verifies the recipient is authorized to receive emails from the sender’s domain.
It checks the sending IP address is authorized by the sender’s domain.
It checks the digital signature in the message header is valid and from that domain.
It inserts a header containing email authentication results and signs it.
Answer:
BExplanation:
The correct answer is B. It checks the sending IP address is authorized by the sender’s domain . Proofpoint’s SPF reference states that an SPF record in DNS specifies which IP addresses and hostnames are authorized to send emails for a domain. When the receiving mail server evaluates SPF, it checks whether the source server is on that authorized list. If it is not, the message can fail SPF and be treated as suspicious, spam, or rejected according to policy.
Proofpoint’s broader email-authentication overview describes the SPF step in almost the same way: the receiving server verifies that the sending IP address is approved to send emails for the domain . That is the exact function being tested in this question. SPF is not about validating the recipient, and it is not the mechanism that checks a cryptographic message signature. Those are different controls. DKIM is the mechanism associated with digital signatures over message content and headers, while ARC deals with preserving authentication assessments across forwarding paths.
Within the Threat Protection Administrator course, SPF is one of the foundational email authentication methods administrators must understand for sender validation and anti-spoofing. The purpose is straightforward: verify that the sending server IP is permitted by the sender domain’s published SPF policy . Therefore, the correct course answer is B .
What is the primary function of Proofpoint Targeted Attack Protection (TAP)?
Options:
To provide a platform for video conferencing and team collaboration
To manage user account settings for cloud storage access
To detect and block advanced email threats such as phishing
To analyze web traffic patterns for marketing purposes
Answer:
CExplanation:
The correct answer is C. To detect and block advanced email threats such as phishing . Proofpoint describes Targeted Attack Protection as an email security capability focused on advanced threats, including malicious URLs, impostor attacks, and attachment-based threats. Its purpose is to identify sophisticated attacks that go beyond traditional spam filtering and stop or remediate them before or after delivery.
This fits the Threat Protection Administrator course because TAP is taught as the specialized protection layer for targeted and evolving email-borne attacks. TAP works with capabilities such as URL Defense, attachment analysis, and post-delivery threat intelligence to help administrators detect phishing, credential-harvest attempts, and other advanced social-engineering campaigns. It is not a collaboration platform, not a cloud-storage access manager, and not a marketing analytics tool. Those alternatives have nothing to do with the security role of TAP in the Proofpoint product family.
In practical administration, TAP is valuable because many modern attacks are highly customized and may appear legitimate at first glance. The course emphasizes that administrators must understand how TAP extends protection beyond basic filtering by analyzing risky links, suspicious attachments, and targeted email patterns. That is why the primary function of TAP is best expressed as detecting and blocking advanced email threats such as phishing . Therefore, the verified answer is C .
Which feature is commonly available to end users via the web interface?
Options:
Viewing and releasing emails from the quarantine
Configuring rules to send messages to folders in their inbox
Configuring brand identity colors and images for messages
Reading encrypted messages sent through PoD
Answer:
AExplanation:
The correct answer is A. Viewing and releasing emails from the quarantine . In Proofpoint’s end-user experience, the End User Web Interface is designed primarily to let users interact with quarantined mail and manage a limited set of personal message-handling preferences. Proofpoint customer-facing material notes that users can manage quarantine settings and related sender preferences themselves, which aligns directly with the ability to view and release quarantined messages.
This fits the Threat Protection Administrator course because the End User Web Interface is not intended to function as a full administrative console. End users are not expected to build inbox-routing logic there, customize corporate branding assets, or administer platform-wide presentation elements. Those are administrative or separate product capabilities rather than a standard end-user quarantine task. The course’s Quarantine and End User Web sections emphasize that users can review messages held by policy, determine whether a message appears legitimate, and request or perform a release depending on how the environment is configured. That is why quarantine visibility and release are the most common web-interface functions associated with end users.
Although encrypted-message reading may exist in other Proofpoint experiences or adjacent products, that is not the core answer this question is testing. The tested and course-aligned capability for the end-user web interface is viewing and releasing emails from quarantine , making A the correct answer.
Which of the following are true regarding Spam Detection?
Pick the 3 correct responses below.
Options:
If you enable the lowpriority rule, you should disable the bulk rule.
Policy routes are used to decide which spam policy is applied to a message.
Multiple policies can apply to a single inbound message.
Only one Spam Detection rule will fire for a unique message going to a single recipient.
Separate policies should be created for inbound and outbound messages.
Spam Detection prevents internal users sending confidential data outbound.
Answer:
B, D, EExplanation:
The correct answers are B , D , and E . Proofpoint’s spam-detection training material describes policy routes as the mechanism used to determine which spam policy applies to a message, making B correct. The course content also teaches administrators to create separate inbound and outbound spam policies , because the logic and operational goals for inbound spam filtering differ from those for outbound protection, making E correct. In the same course-style material, the tested statement that only one Spam Detection rule will fire for a unique message going to a single recipient is treated as true for the rule-evaluation context of a single recipient message, making D the third correct answer.
The remaining statements are not correct in this course context. The “multiple policies can apply” statement is not the accepted answer for this question set as taught. The lowpriority-versus-bulk statement is not presented as a general truth to follow by default, and preventing confidential outbound data leakage is not the primary purpose of Spam Detection; that concern belongs to different controls such as data-loss or content-governance features rather than spam scoring. In the Threat Protection Administrator course, Spam Detection is framed around policy selection, filtering logic, and message classification rather than data-protection enforcement. Therefore, the correct answer set is B, D, and E .
When employees at your company change their name, their email address also changes. To ensure that the user import process associates the new email addresses with the existing users, how should you configure the primary key?
Options:
Set the primary key to the user’s full name.
Keep the old email address as the primary key.
Use the updated email address as the primary key.
Change the primary key to match the uid attribute.
Answer:
DExplanation:
In Proofpoint user import and authentication profile configuration, the primary key should be set to a stable identity attribute that does not change when a user’s display name or email address changes. Proofpoint’s LDAP import guidance specifically points administrators toward using UID as the primary key. That matters in exactly the scenario described here: when a person changes their name and therefore receives a new email address, using the email address itself as the primary key would make the import process treat the updated record as if it might be a different user. By contrast, using a stable directory attribute such as uid allows Proofpoint to associate the updated email address with the same underlying user object. Setting the primary key to a full name would be unreliable because names can change and may not be unique. Keeping the old email address as the key defeats the purpose of matching the updated identity. Using the new email address as the key still makes the key dependent on a mutable attribute. The course’s User Management section emphasizes directory sync and import behavior, and the support guidance for importing users and groups from LDAP/AD explicitly references UID as the primary key mapping to use for this kind of identity continuity. Therefore, the correct answer is to change the primary key to match the uid attribute.
In the context of Proofpoint, what is an SMTP Profile?
Options:
A list of blocked email addresses
A Proofpoint-generated encryption key
A setting that defines email routing policies
A user-defined quarantine setting
Answer:
CExplanation:
The correct answer is C. A setting that defines email routing policies . In Proofpoint administration, SMTP-related profiles are used as configuration objects that shape how mail is handled in transport, including route behavior and SMTP service characteristics. The course question’s correct answer aligns with the operational role of SMTP profiles in governing routing and transport behavior, not quarantine personalization or encryption-key generation. Proofpoint’s general SMTP and relay documentation frames SMTP configuration around how messages are relayed, routed, and delivered between systems, which supports this answer. ( proofpoint.com )
The incorrect options do not fit the function of an SMTP Profile. A block list of email addresses would be part of filtering or policy controls, not SMTP profile definition. A Proofpoint-generated encryption key belongs to cryptographic or secure message workflows, not to SMTP profile configuration. A user-defined quarantine setting is part of end-user or administrative quarantine handling and is unrelated to transport profile architecture. In the Threat Protection Administrator course, Mail Flow focuses heavily on routing, relay behavior, and delivery path control, and this question sits squarely in that domain. So when the course asks what an SMTP Profile is in Proofpoint, the best verified answer is that it is a setting that defines email routing policies . ( proofpoint.com )
Which Email Firewall features should be used together to mitigate directory harvest attacks?
Options:
Outbound Throttle
SMTP Rate Control
Dictionaries
Bounce Management
Recipient Verification
Answer:
B, EExplanation:
Directory harvest attacks try to discover valid recipient addresses by sending large numbers of SMTP recipient attempts and observing which addresses are accepted or rejected. In Proofpoint’s layered connection-level defenses, Recipient Verification and SMTP Rate Control are the two features that work together most directly against this problem. Recipient Verification checks whether the addressed mailbox is valid, while SMTP Rate Control helps detect and automatically block or throttle abusive SMTP connection behavior. Proofpoint’s published spam detection material describes connection-level analysis that includes recipient verification and Dynamic Reputation, and then states that based on this analysis, SMTP rate control is used to automatically block or throttle malicious connections, providing strong protection against directory harvest and denial-of-service attacks. That pairing is exactly what makes these two options the correct answer. Outbound Throttle is aimed at controlling excessive outbound mail from accounts, not inbound recipient enumeration. Dictionaries are content and pattern controls, not recipient-existence validation controls. Bounce Management deals with BATV-style handling of backscatter, which is a different problem space. The Threat Protection Administrator course topic list also places SMTP Rate Control and Recipient Verification together under the same operational area, reinforcing that they are complementary controls for this class of attack. For a directory harvest scenario, these are the right two protections to deploy together.
Which of the following is a common port used for SMTP connectivity?
Options:
22
443
80
25
Answer:
DExplanation:
The correct answer is D. 25 . SMTP is the standard protocol used for transferring email between mail servers, and TCP port 25 is the traditional and most common port used for SMTP relay and server-to-server email transport. Proofpoint’s SMTP relay reference aligns with this standard mail-flow model, where SMTP is the protocol responsible for message transfer between mail systems.
The other ports listed are associated with different services. Port 22 is commonly used for SSH, port 443 for HTTPS, and port 80 for HTTP. Those are important network ports, but they are not the standard answer for SMTP connectivity in the context of mail flow and Proofpoint administration. In the Threat Protection Administrator course, understanding SMTP basics is essential because route configuration, TLS behavior, queue handling, and delivery troubleshooting all rely on knowing how SMTP sessions operate at the transport level.
Although modern mail submission can also involve other ports in certain client scenarios, this question asks for a common SMTP connectivity port, and the course-level expected answer is the standard server-to-server SMTP port. For mail transfer in the context of Proofpoint and SMTP routing, that port is 25 . Therefore, the verified answer is D .
Which spam policy is applied to outbound messages?
Options:
The spam policy set at the Organization level
The spam policy set for the sender of the email
The spam policy set for the recipient of the email
The spam policy set at the Sub-Org level
Answer:
CExplanation:
The correct answer is C. The spam policy set for the recipient of the email . In the Threat Protection Administrator course, outbound spam handling is tied to how Proofpoint applies spam policy through its policy-selection logic, and the tested answer for this question is that the recipient’s spam policy is the one used for outbound messages. Proofpoint’s Spam Detection guidance shows that policy routing determines which spam policy is applied to a message, and the course uses that framework when distinguishing inbound and outbound policy behavior.
This question is easy to overthink because many administrators naturally assume outbound filtering should always be based on the sender’s organization or sender identity alone. But the course’s expected answer is specifically the recipient-associated policy . The distractors reflect other places where administrators commonly expect policy to come from, such as the organization level or sender level, but those are not the correct course answer for this item. The important takeaway is that Proofpoint’s spam-policy application is governed by routing and message-processing logic, and the course tests that exact behavior rather than a generic assumption about outbound mail. Therefore, for this Proofpoint Threat Protection Administrator question, the verified answer remains C .
During the configuration of an alert profile, which option is specifically required to ensure alerts are delivered to the appropriate individuals?
Options:
A list of recipient email addresses
A confirmation message for the alert
A schedule for when alerts should be sent
A description of the alert type
Answer:
AExplanation:
The correct answer is A because an alert profile or alert notification policy must define who receives the alerts . Proofpoint documentation on monitoring alerts states that an alert notification policy defines which alerts are sent to which email addresses and at what frequency. That means recipient addresses are the essential delivery element. Without them, the system has no destination for the alert notifications, regardless of how the rest of the profile is configured.
The other options may be useful context or supporting settings, but they are not the key requirement for making sure alerts reach the appropriate people. A schedule or frequency can determine when alerts are sent, but not who receives them. A description of alert type helps categorize the alert, but it does not provide delivery targets. A confirmation message is not the core object that determines delivery. In administrator practice, the first operational question for alerting is always: who needs to know? Proofpoint’s alerting model answers that by tying alert rules or alert conditions to an alert profile that includes recipient email addresses.
This is consistent with the Threat Protection Administrator course section on Alerts and Reporting, where administrators create profiles and then bind those profiles to alerting events. The critical setting that ensures the right individuals receive the notifications is the list of recipient email addresses , making A the correct answer.
In a scenario where multiple members of a distribution group attempt to release the same quarantined email message from the scheduled digest, what will happen?
Options:
The system allows all users to release the message, but logs the events for security audits
All members will successfully release the message without any errors
The first user will release the message, while others will receive an error
All users will receive a notification that the message cannot be released due to a system error
Answer:
CExplanation:
The correct answer is C. The first user will release the message, while others will receive an error . Proofpoint help content for quarantine-digest release errors indicates that once the message has already been delivered through a release action, subsequent attempts can result in an error because the requested email has already been handled. That aligns directly with a shared or distribution-group scenario where more than one recipient of the digest tries to release the same quarantined message.
This behavior is logical in the course’s Quarantine section. The release action is effectively acting on the same quarantined object, so once one person succeeds, later attempts do not have an identical unreleased message left to act upon. That is why the choices suggesting that every user can release it successfully are not correct. The fully generic “system error for everyone” choice is also wrong because one user does succeed first. In shared-mailbox and group-digest style workflows, this is a common operational pattern: the first release wins, and later users see an error or a message indicating the item is no longer available for that action. Therefore, the Threat Protection Administrator course-aligned answer is C .
In the mail route configuration shown, how does the Protection Server attempt delivery to example.com?
Options:
It randomizes the listed destination MTAs for load balancing
It always uses the lowest entry first, then retries upward
It tries to connect to the destination MTAs starting at the top and working down the list
It performs public MX lookup first and ignores the manually listed hosts
Answer:
CExplanation:
The correct answer is C. It tries to connect to the destination MTAs starting at the top and working down the list . This answer comes from the route-ordering behavior shown in the screenshot prompt and matches the way administrators are expected to interpret an ordered destination list in Proofpoint route configuration. In a manually defined route list, the order is meaningful, and the server attempts destinations according to that listed order rather than randomly.
This makes operational sense in Mail Flow administration. When administrators define multiple destination MTAs for a domain or route, they usually do so in a preferred sequence to control primary and fallback delivery behavior. Proofpoint’s SMTP relay and MX references explain that mail delivery depends on how destination servers are selected and contacted, and ordered delivery logic is a standard part of controlled routing behavior.
The other options do not match the configured-route interpretation shown by the question. Randomization would defeat the purpose of explicitly ordered host entries. Starting from the bottom of the list is not the behavior indicated by the screen, and ignoring the configured hosts in favor of public MX lookup would undermine the value of manually defining a route in the first place. In the Threat Protection Administrator course, Mail Flow questions like this test whether the student understands that configured route order affects connection attempts. Therefore, the correct answer is C : the Protection Server starts at the top of the list and works downward .
Which of the following are true regarding Email Warning Tags?
Pick the 2 correct responses below.
Options:
Administrators can create new tag types and tag rules as needed.
They are enabled in the individual recipient user’s settings.
The tags can be edited to customize the color and text to meet requirements.
By default, they apply to outbound traffic to external recipients only.
The language used for the tag is based on the recipient user’s settings.
Answer:
C, EExplanation:
The correct answers are C and E . Proofpoint describes Email Warning Tags as visual, color-coded cues that alert users to take extra precautions with suspicious messages. That aligns directly with the idea that tags can be customized for presentation, including their displayed text and visual treatment, rather than being fixed, non-editable banners. Proofpoint’s public material repeatedly refers to these tags as contextual visual cues that can be used to support different threat scenarios, which is consistent with administrator-driven customization.
The course material for Threat Protection Administrator also treats Email Warning Tags as a centrally managed email-protection feature, not something enabled one-by-one in a user’s personal settings. In practice, they are configured at the administrative level within the product and inserted according to policy conditions, not per-user self-service toggle behavior. The training guide preview for the relevant lesson shows administrators enabling the Email Warning Tags module and selecting formatting options such as inline insertion and plain-text handling, which confirms this is a system-level control.
The statement about language being based on the recipient user’s settings is consistent with the course behavior for localized end-user experiences. By contrast, creating entirely new tag types is not presented as the standard model in the course, and the “outbound traffic to external recipients only” statement is not consistent with how warning tags are used for inbound threat-context messaging. Therefore, C and E are the correct choices.

