Symantec Data Loss Prevention 16.x Administration Technical Specialist Questions and Answers
What should an incident responder select in the Enforce management console to remediate multiple incidents simultaneously?
Which two automated response rules will be active in policies that include Exact Data Matching (EDM) detection rule? (Choose two.)
What is required on the Enforce server to communicate with the Symantec DLP database?
Which two (2) detection technology options run on the DLP agent? (Choose two.)
Which two Network Discover/Cloud Storage targets apply Information Centric Encryption as policy response rules?
Which statement accurately describes where Optical Character Recognition (OCR) components must be installed?
Which option correctly describes the two-tier installation type for Symantec DLP?
How do Cloud Detection Service and the Enforce server communicate with each other?
When managing an Endpoint Discover scan, a DLP administrator notices some endpoint computers are NOT completing their scans.
When does the DLP agent stop scanning?
Which of the following would have to be a custom attribute (and not an out-of -the-box system attribute) in incident snapshots?
Which two factors are common sources of data leakage where the main actor is well-meaning insider? (Choose two.)
Refer to the exhibit.
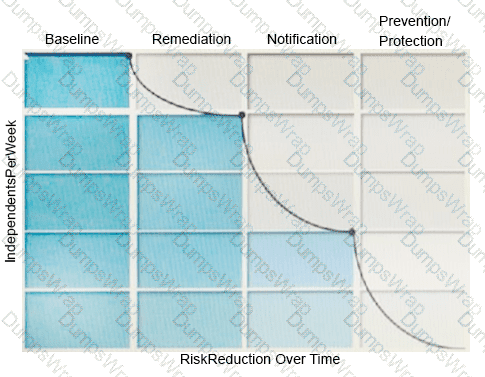
What activity should occur during the baseline phase, according to the risk reduction model?
Which two (2) actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
Which detection method depends on “training sets”?
What detection method utilizes Data Identifiers?
Which server target uses the “Automated Incident Remediation Tracking” feature in Symantec DLP?
What detection server type requires a minimum of two physical network interface cards?
How should a DLP administrator change a policy that it retains the original file when an endpoint incident has detected a “copy to USB device” operation?
A divisional executive requests a report of all incidents generated by a particular region, summarized by department.
What does the DLP administrator need to configure to generate this report?
A DLP administrator determines that the \SymantecDLP\Protect\Incidents folder on the Enforce server contains. BAD files dated today, while other. IDC files are flowing in and out of the \Incidents directory. Only .IDC files larger than 1MB are turning to .BAD files.
What could be causing only incident data smaller than 1MB to persist while incidents larger than 1MB change to .BAD files?
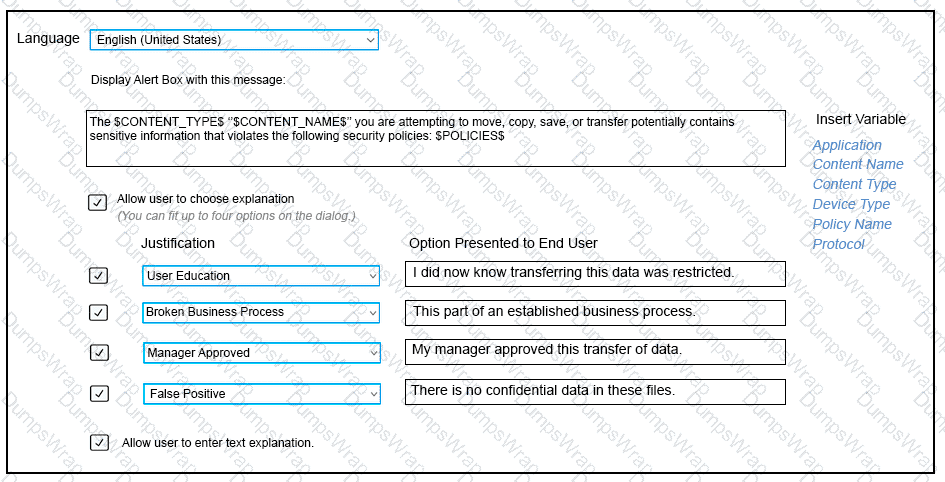
Refer to the exhibit. Which type of Endpoint response rule is shown?
Which detection server is available from Symantec as a hardware appliance?
Where do you configure the list of Endpoint Servers (or load balancers) to which a DLP Agent can report?
What is the Symantec recommended order for stopping Symantec DLP services on a Windows Enforce server?
What is one difference between Exact Data Matching (EDM) and Exact Match Data Identifiers (EMDI)?
What detection server is used for Network Discover, Network Protect, and Cloud Storage?
Which two detection servers are available as virtual appliances? (Choose two.)
Which type of response rule does Cloud Service for Email use to block confidential emails?
What are two reasons an administrator should utilize a manual configuration to determine the endpoint location? (Choose two.)
Which action should a DLP administrator take to secure communications between an on-premises Enforce server and detection servers hosted in the Cloud?

