Check Point Certified Security Expert R81.20 ( 156-315.81.20 ) Questions and Answers
SandBlast agent extends 0 day prevention to what part of the network?
GAiA Software update packages can be imported and installed offline in situation where:
One of major features in R81 SmartConsole is concurrent administration.
Which of the following is NOT possible considering that AdminA, AdminB and AdminC are editing the same Security Policy?
What is UserCheck?
To ensure that VMAC mode is enabled, which CLI command should you run on all cluster members?
Which SmartConsole tab is used to monitor network and security performance?
You can access the ThreatCloud Repository from:
Tom has connected to the R81 Management Server remotely using SmartConsole and is in the process of making some Rule Base changes, when he suddenly loses connectivity. Connectivity is restored shortly afterward.
What will happen to the changes already made?
In Logging and Monitoring, the tracking options are Log, Detailed Log and Extended Log. Which of the following options can you add to each Log, Detailed Log and Extended Log?
Please choose the path to monitor the compliance status of the Check Point R81.20 based management.
What does it mean if Deyra sees the gateway status? (Choose the BEST answer.)
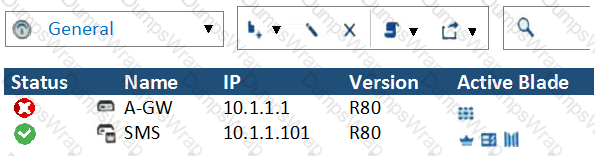
What CLI command compiles and installs a Security Policy on the target’s Security Gateways?
You notice that your firewall is under a DDoS attack and would like to enable the Penalty Box feature, which command you use?
For best practices, what is the recommended time for automatic unlocking of locked admin accounts?
With MTA (Mail Transfer Agent) enabled the gateways manages SMTP traffic and holds external email with potentially malicious attachments. What is required in order to enable MTA (Mail Transfer Agent) functionality in the Security Gateway?
Which is NOT an example of a Check Point API?
What are the methods of SandBlast Threat Emulation deployment?
SmartEvent provides a convenient way to run common command line executables that can assist in investigating events. Right-clicking the IP address, source or destination, in an event provides a list of default and customized commands. They appear only on cells that refer to IP addresses because the IP address of the active cell is used as the destination of the command when run. The default commands are:
Which of the following technologies extracts detailed information from packets and stores that information in state tables?
After the initial installation on Check Point appliance, you notice that the Management-interface and default gateway are incorrect.
Which commands could you use to set the IP to 192.168.80.200/24 and default gateway to 192.168.80.1.
What kind of information would you expect to see using the sim affinity command?
Fill in the blank: Identity Awareness AD-Query is using the Microsoft _______________ API to learn users from AD.
NO: 219
What cloud-based SandBlast Mobile application is used to register new devices and users?
In what way are SSL VPN and IPSec VPN different?
Which is NOT a SmartEvent component?
When SecureXL is enabled, all packets should be accelerated, except packets that match the following conditions:
Which Check Point software blade provides Application Security and identity control?
What is the order of NAT priorities?
What will SmartEvent automatically define as events?
You have a Gateway is running with 2 cores. You plan to add a second gateway to build a cluster and used a device with 4 cores.
How many cores can be used in a Cluster for Firewall-kernel on the new device?
You want to verify if your management server is ready to upgrade to R81.20. What tool could you use in this process?
Joey wants to upgrade from R75.40 to R81 version of Security management. He will use Advanced Upgrade with Database Migration method to achieve this.
What is one of the requirements for his success?
With SecureXL enabled, accelerated packets will pass through the following:
Which of the following Windows Security Events will not map a username to an IP address in Identity Awareness?
Ken wants to obtain a configuration lock from other administrator on R81 Security Management Server. He can do this via WebUI or via CLI.
Which command should he use in CLI? (Choose the correct answer.)
You have a Geo-Protection policy blocking Australia and a number of other countries. Your network now requires a Check Point Firewall to be installed in Sydney, Australia.
What must you do to get SIC to work?
When deploying SandBlast, how would a Threat Emulation appliance benefit from the integration of ThreatCloud?
Which file gives you a list of all security servers in use, including port number?
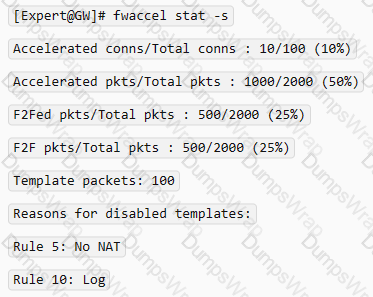
The system administrator of a company is trying to find out why acceleration is not working for the traffic. The traffic is allowed according to the rule base and checked for viruses. But it is not accelerated.
What is the most likely reason that the traffic is not accelerated?
The essential means by which state synchronization works to provide failover in the event an active member goes down, ____________ is used specifically for clustered environments to allow gateways to report their own state and learn about the states of other members in the cluster.
How many layers make up the TCP/IP model?
Which blades and or features are not supported in R81?
What must you do first if “fwm sic_reset” could not be completed?
Which of the following is NOT an option to calculate the traffic direction?
Vanessa is a Firewall administrator. She wants to test a backup of her company’s production Firewall cluster Dallas_GW. She has a lab environment that is identical to her production environment. She decided to restore production backup via SmartConsole in lab environment.
Which details she need to fill in System Restore window before she can click OK button and test the backup?
What command would show the API server status?
Fill in the blank: The “fw monitor” tool can be best used to troubleshoot ____________________.
You have existing dbedit scripts from R77. Can you use them with R81.20?
Which of the following is NOT a component of Check Point Capsule?
Which process is available on any management product and on products that require direct GUI access, such as SmartEvent and provides GUI client communications, database manipulation, policy compilation and Management HA synchronization?
You find one of your cluster gateways showing “Down” when you run the “cphaprob stat” command. You then run the “clusterXL_admin up” on the down member but unfortunately the member continues to show down. What command do you run to determine the cause?
The Correlation Unit performs all but the following actions:
Using ClusterXL, what statement is true about the Sticky Decision Function?
What scenario indicates that SecureXL is enabled?
You are investigating issues with to gateway cluster members are not able to establish the first initial cluster synchronization. What service is used by the FWD daemon to do a Full Synchronization?
What is the name of the secure application for Mail/Calendar for mobile devices?
Which statement is true about ClusterXL?
SmartEvent has several components that function together to track security threats. What is the function of the Correlation Unit as a component of this architecture?
How do you enable virtual mac (VMAC) on-the-fly on a cluster member?
You want to store the GAIA configuration in a file for later reference. What command should you use?
Can multiple administrators connect to a Security Management Server at the same time?
How do Capsule Connect and Capsule Workspace differ?
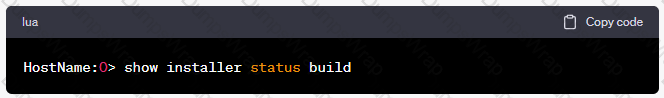
The following command is used to verify the CPUSE version:
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Wire Mode configuration, chain modules marked with ____________ will not apply.
What processes does CPM control?
What is considered Hybrid Emulation Mode?
Which of these is an implicit MEP option?
When setting up an externally managed log server, what is one item that will not be configured on the R81 Security Management Server?
When Dynamic Dispatcher is enabled, connections are assigned dynamically with the exception of:
How would you deploy TE250X Check Point appliance just for email traffic and in-line mode without a Check Point Security Gateway?
You are asked to check the status of several user-mode processes on the management server and gateway. Which of the following processes can only be seen on a Management Server?
What is the protocol and port used for Health Check and State Synchronization in ClusterXL?
Security Checkup Summary can be easily conducted within:
What is the command to check the status of the SmartEvent Correlation Unit?
What is mandatory for ClusterXL to work properly?
Which Check Point daemon monitors the other daemons?
To enable Dynamic Dispatch on Security Gateway without the Firewall Priority Queues, run the following command in Expert mode and reboot:
Which Check Point software blades could be enforced under Threat Prevention profile using Check Point R81.20 SmartConsole application?
An administrator would like to troubleshoot why templating is not working for some traffic. How can he determine at which rule templating is disabled?
When gathering information about a gateway using CPINFO, what information is included or excluded when using the “-x” parameter?
Which of the following will NOT affect acceleration?
SmartConsole R81 requires the following ports to be open for SmartEvent R81 management:
: 131
Which command is used to display status information for various components?
What is a best practice before starting to troubleshoot using the “fw monitor” tool?
In SmartEvent, what are the different types of automatic reactions that the administrator can configure?
SandBlast offers flexibility in implementation based on their individual business needs. What is an option for deployment of Check Point SandBlast Zero-Day Protection?
Which of the following links will take you to the SmartView web application?
What is the difference between SSL VPN and IPSec VPN?
What is the port used for SmartConsole to connect to the Security Management Server?
Which of the following is NOT a type of Check Point API available in R81.x?
What component of R81 Management is used for indexing?
Which encryption algorithm is the least secured?
When installing a dedicated R81 SmartEvent server. What is the recommended size of the root partition?
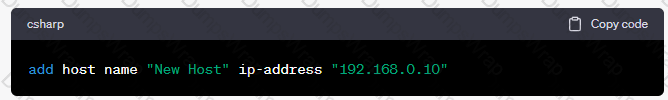
What API command below creates a new host with the name “New Host” and IP address of “192.168.0.10”?
What is the limitation of employing Sticky Decision Function?
You want to gather and analyze threats to your mobile device. It has to be a lightweight app. Which application would you use?
The Security Gateway is installed on GAIA R81. The default port for the Web User Interface is ______ .
On R81.20 when configuring Third-Party devices to read the logs using the LEA (Log Export API) the default Log Server uses port:
Which of the following authentication methods ARE NOT used for Mobile Access?
Which method below is NOT one of the ways to communicate using the Management API’s?
Which statement is correct about the Sticky Decision Function?
What is true about the IPS-Blade?
What is not a component of Check Point SandBlast?
To fully enable Dynamic Dispatcher with Firewall Priority Queues on a Security Gateway, run the following command in Expert mode then reboot:
What command verifies that the API server is responding?
SSL Network Extender (SNX) is a thin SSL VPN on-demand client that is installed on the remote user’s machine via the web browser. What are the two modes of SNX?
Full synchronization between cluster members is handled by Firewall Kernel. Which port is used for this?
Which TCP-port does CPM process listen to?
You are working with multiple Security Gateways enforcing an extensive number of rules. To simplify security administration, which action would you choose?
To help SmartEvent determine whether events originated internally or externally you must define using the Initial Settings under General Settings in the Policy Tab. How many options are available to calculate the traffic direction?
Advanced Security Checkups can be easily conducted within:
Connections to the Check Point R81 Web API use what protocol?
You have successfully backed up Check Point configurations without the OS information. What command would you use to restore this backup?
You can select the file types that are sent for emulation for all the Threat Prevention profiles. Each profile defines a(n) _____ or _____ action for the file types.
What is the difference between an event and a log?
Which command can you use to enable or disable multi-queue per interface?
Check Point Management (cpm) is the main management process in that it provides the architecture for a consolidates management console. CPM allows the GUI client and management server to communicate via web services using ___________.
Which of these statements describes the Check Point ThreatCloud?
Fill in the blank: The command ___________________ provides the most complete restoration of a R81 configuration.
How many images are included with Check Point TE appliance in Recommended Mode?
In R81 spoofing is defined as a method of:
What makes Anti-Bot unique compared to other Threat Prevention mechanisms, such as URL Filtering, Anti-Virus, IPS, and Threat Emulation?
There are 4 ways to use the Management API for creating host object with R81 Management API. Which one is NOT correct?
Automatic affinity means that if SecureXL is running, the affinity for each interface is automatically reset every
CoreXL is supported when one of the following features is enabled:
Which of the following is a new R81 Gateway feature that had not been available in R77.X and older?
Which Mobile Access Application allows a secure container on Mobile devices to give users access to internal website, file share and emails?
Check Pont Central Deployment Tool (CDT) communicates with the Security Gateway / Cluster Members over Check Point SIC _______ .
Which view is NOT a valid CPVIEW view?
Check Point Management (cpm) is the main management process in that it provides the architecture for a consolidated management console. It empowers the migration from legacy Client-side logic to Server-side logic. The cpm process:
What is the correct command to observe the Sync traffic in a VRRP environment?
Identify the API that is not supported by Check Point currently.
Which command will allow you to see the interface status?
Session unique identifiers are passed to the web api using which http header option?
R81.20 management server can manage gateways with which versions installed?
Tom has been tasked to install Check Point R81 in a distributed deployment. Before Tom installs the systems this way, how many machines will he need if he does NOT include a SmartConsole machine in his calculations?
The CPD daemon is a Firewall Kernel Process that does NOT do which of the following?
Which command shows actual allowed connections in state table?
If you needed the Multicast MAC address of a cluster, what command would you run?
What SmartEvent component creates events?
What is a feature that enables VPN connections to successfully maintain a private and secure VPN session without employing Stateful Inspection?
An administrator wishes to enable Identity Awareness on the Check Point firewalls. However, they allow users to use company issued or personal laptops. Since the administrator cannot manage the personal laptops, which of the following methods would BEST suit this company?
Which Check Point software blade provides protection from zero-day and undiscovered threats?
Return oriented programming (ROP) exploits are detected by which security blade?
What feature allows Remote-access VPN users to access resources across a site-to-site VPN tunnel?
How does the Anti-Virus feature of the Threat Prevention policy block traffic from infected websites?
How many interfaces can you configure to use the Multi-Queue feature?
Bob has finished io setup provisioning a secondary security management server. Now he wants to check if the provisioning has been correct. Which of the following Check Point command can be used to check if the security management server has been installed as a primary or a secondary security management server?
Due to high CPU workload on the Security Gateway, the security administrator decided to purchase a new multicore CPU to replace the existing single core CPU. After installation, is the administrator required to perform any additional tasks?
The WebUI offers several methods for downloading hotfixes via CPUSE except:
identity Awareness allows easy configuration for network access, and auditing based on what three items?
What is the benefit of Manual NAT over Automatic NAT?
Which of the completed statements is NOT true? The WebUI can be used to manage user accounts and:
Using AD Query, the security gateway connections to the Active Directory Domain Controllers using what protocol?
On R81.20 the IPS Blade is managed by:
What is the minimum number of CPU cores required to enable CoreXL?
Secure Configuration Verification (SCV), makes sure that remote access client computers are configured in accordance with the enterprise Security Policy. Bob was asked by Alice to implement a specific SCV configuration but therefore Bob needs to edit and configure a specific Check Point file. Which location file and directory is true?
Which command is used to add users to or from existing roles?
Which command lists firewall chain?
Identity Awareness allows easy configuration for network access and auditing based on what three items?
SmartEvent Security Checkups can be run from the following Logs and Monitor activity:
Which upgrade method you should use upgrading from R80.40 to R81.20 to avoid any downtime?
Identity Awareness allows the Security Administrator to configure network access based on which of the following?
Choose the correct syntax to add a new host named “emailserver1” with IP address 10.50.23.90 using GAiA Management CLI?
What is "Accelerated Policy Installation"?
Which Check Point process provides logging services, such as forwarding logs from Gateway to Log Server, providing Log Export API (LEA) & Event Logging API (EL-A) services.
Which of the following statements about Site-to-Site VPN Domain-based is NOT true?
Check Point Support in many cases asks you for a configuration summary of your Check Point system. This is also called:
From SecureXL perspective, what are the three paths of traffic flow:
When using the Mail Transfer Agent, where are the debug logs stored?
Which of the following is NOT a valid type of SecureXL template?
To optimize Rule Base efficiency, the most hit rules should be where?
You pushed a policy to your gateway and you cannot access the gateway remotely any more. What command should you use to remove the policy from the gateway by logging in through console access?
In the Check Point Security Management Architecture, which component(s) can store logs?
Which pre-defined Permission Profile should be assigned to an administrator that requires full access to audit all configurations without modifying them?
Bob works for a big security outsourcing provider company and as he receives a lot of change requests per day he wants to use for scripting daily tasks the API services (torn Check Point for the GAIA API. Firstly he needs to be aware if the API services are running for the GAIA operating system. Which of the following Check Point Command is true:
After having saved the Clish Configuration with the "save configuration config.txt" command, where can you find the config.txt file?
Which Check Point software blade provides visibility of users, groups and machines while also providing access control through identity-based policies?
SecureXL is able to accelerate the Connection Rate using templates. Which attributes are used in the template to identify the connection?
Fill in the blank: Permanent VPN tunnels can be set on all tunnels in the community, on all tunnels for specific gateways, or ______ .
What is the base level encryption key used by Capsule Docs?
Gaia has two default user accounts that cannot be deleted. What are those user accounts?
Vanessa is expecting a very important Security Report. The Document should be sent as an attachment via e-mail. An e-mail with Security_report.pdf file was delivered to her e-mail inbox. When she opened the PDF file, she noticed that the file is basically empty and only few lines of text are in it. The report is missing some graphs, tables and links.
Which component of SandBlast protection is her company using on a Gateway?
After upgrading the primary security management server from R80.40 to R81.10 Bob wants to use the central deployment in SmartConsole R81.10 for the first time. How many installations (e.g. Jumbo Hotfix, Hotfixes or Upgrade Packages) can run of such at the same time:
Which type of Endpoint Identity Agent includes packet tagging and computer authentication?
Which Queue in the Priority Queue has the maximum priority?
Which two Cluster Solutions are available under R81.20?
Which one of the following is NOT a configurable Compliance Regulation?