Cisco Certified Design Expert (CCDE v3.1) Questions and Answers
An enterprise service provider is planning to migrate the customer network to MPLS to connect cloud applications The customer network team and service provider team are analyzing all process (tows before live migration and implementation Before planning the migration, what is a crucial task that must be executed?
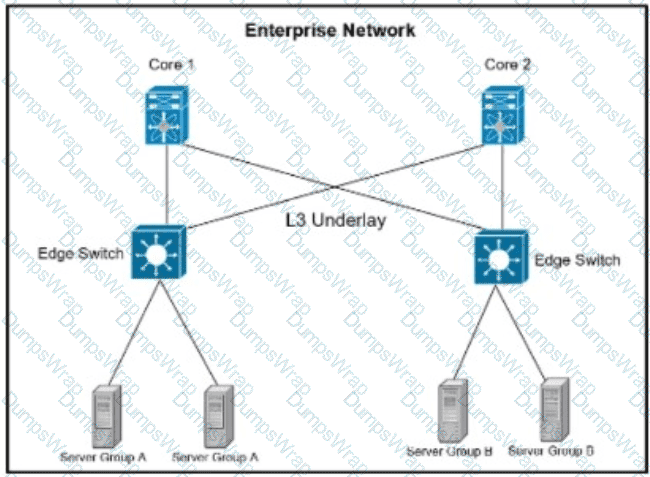
Refer to the exhibit. A company is running their data center based on VXLAN and BGP EVPN with stretched subnets for servers attaching to the edge devices being an important feature. The security team has defined a requirement where server group A must not be able to communicate with each other but is allowed to communicate with server group B. while servers in Group B must be able to communicate with all servers. Which scalable solution can be deployed to support these requirements?
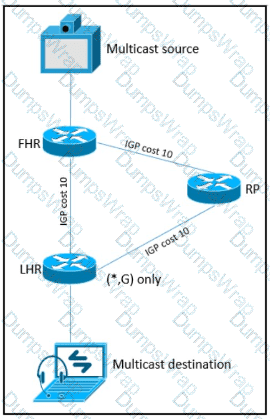
Refer to the exhibit. As part of a redesign project, you must predict multicast behavior . What happens to the multicast traffic received on the shared tree (*,G), if it is received on the LHR interface indicated*?
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
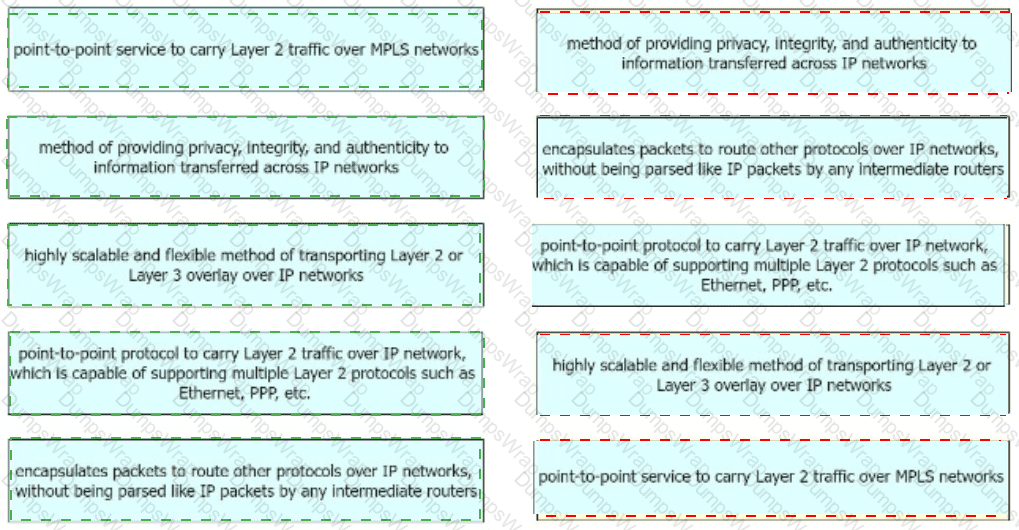
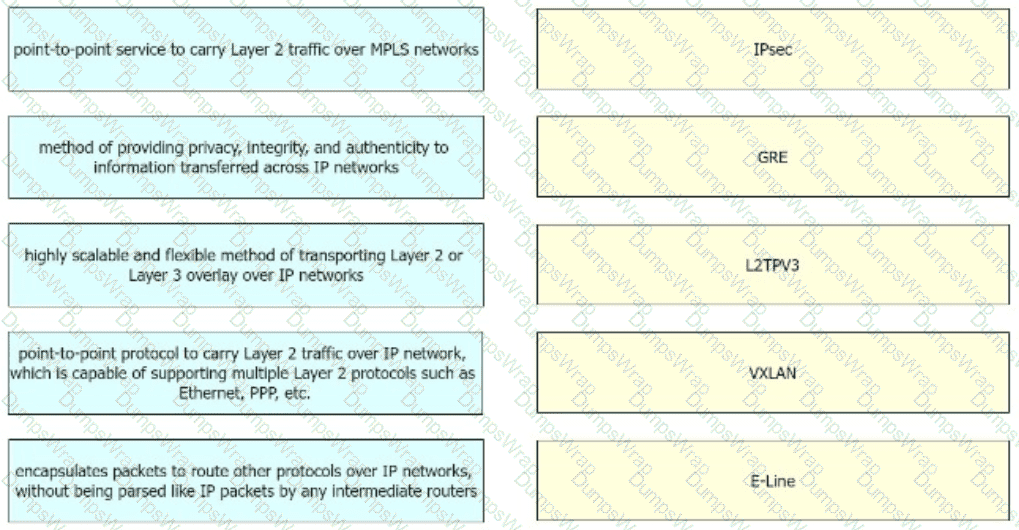
Drag and drop the right functional descriptions from the left onto the corresponding protocols on the right.
Which design method is achieved by layering the network control plane above a redundant physical infrastructure?
What is the most important operational driver when building a resilient and secure modular network design?
SD-WAN can be used to provide secure connectivity to remote offices, branch offices, campus networks, data centers, and the cloud over any type of IP-based underlay transport network. Which two statements describe SD WAN solutions? (Choose two.)
An architect receives a business requirement from a CTO that states the RTO for a new system should be 4 hours, and the RPO should be less than 1 hour. Business continuity must also be ensured in the event of a natural disaster. Which replication method and data center technology should be used?
Which CIA triad principle is used by social media platforms to constitute a standard procedure of user IDs and passwords requirements?
When constraint-based routing is under consideration to be added to a network design, what are two inherent characteristics or impacts that must be considered? (Choose two)
Enterprise XYZ wants to implement fast convergence on their network and optimize timers for OSPF However they also want to prevent excess flooding of ISAs if there is a constantly flapping link on the network Which timers can help prevent excess flooding of LSAs for OSPF?
An enterprise requires MPLS connected branches to access cloud-based Microsoft 365 services over an SD-WAN solution. Internet access Is available only at dual regional hub sites that are connected to the MPLS network. Which connectivity method provides an optimum access method to the cloud-based services If one ISP suffers loss or latency?
Which technique facilitates analytics and knowledge discovery in big data systems to recognize hidden and complex patterns?
In large-scale networks controllers needs to be able to process millions of flows per second without compromising the quality of the service What are two actions that must be implemented to address scaling limitations when deploying the network*? (Choose two.)
Company XYZ has two routing domains in their network, EIGRP and OSPF. The company wants to provide full reachability between the two domains by implementing redistribution on a router running both protocols They need to design the redistribution in a way that the OSPF routers will see link costs added to external routes. How must the redistribution strategy be designed for this network?
Organic growth or decline comes from a company ' s normal business activities, rather than through acquisitions or divestment. Changes in usage patterns can also cause organic change in network requirements Which tool is useful when designing and operationalizing a network that is in the process of change?
What is the best approach to ensure both scalability and high availability for a cloud-based storage solution over the IP network?
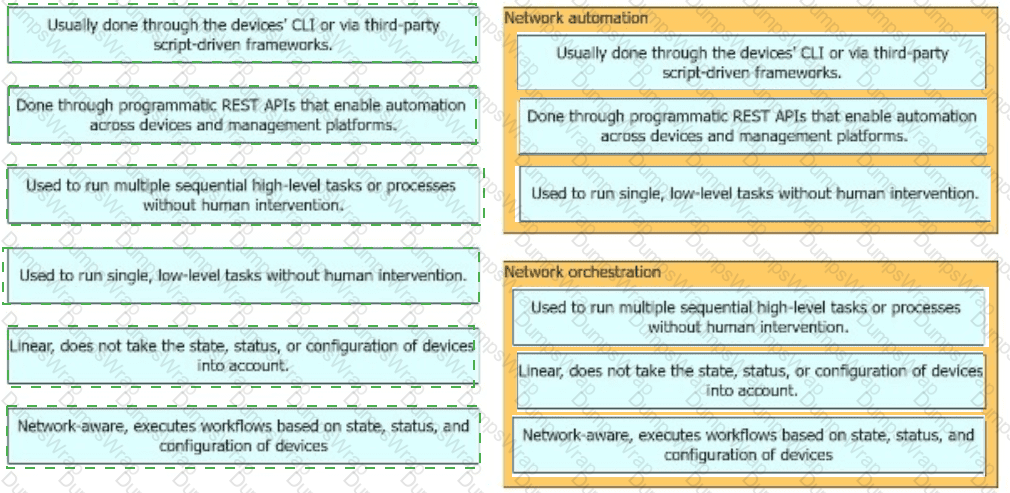
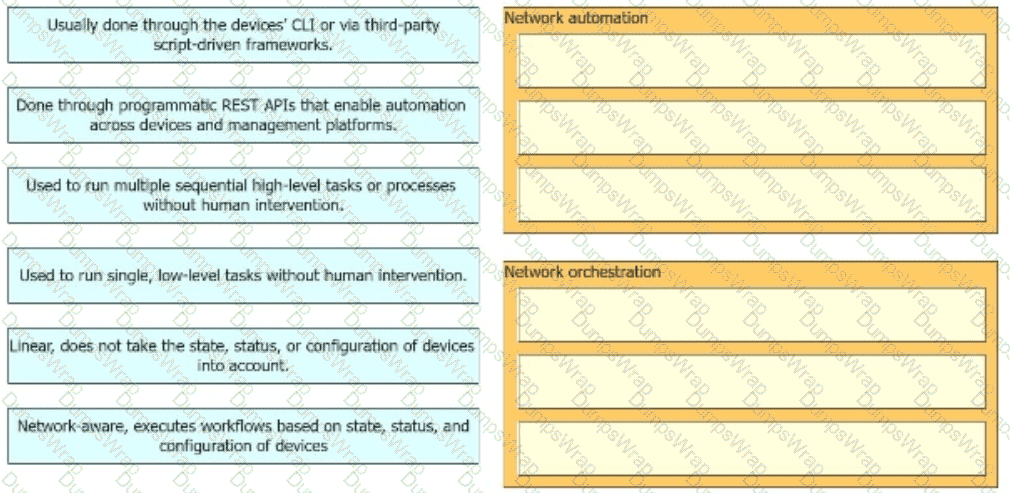
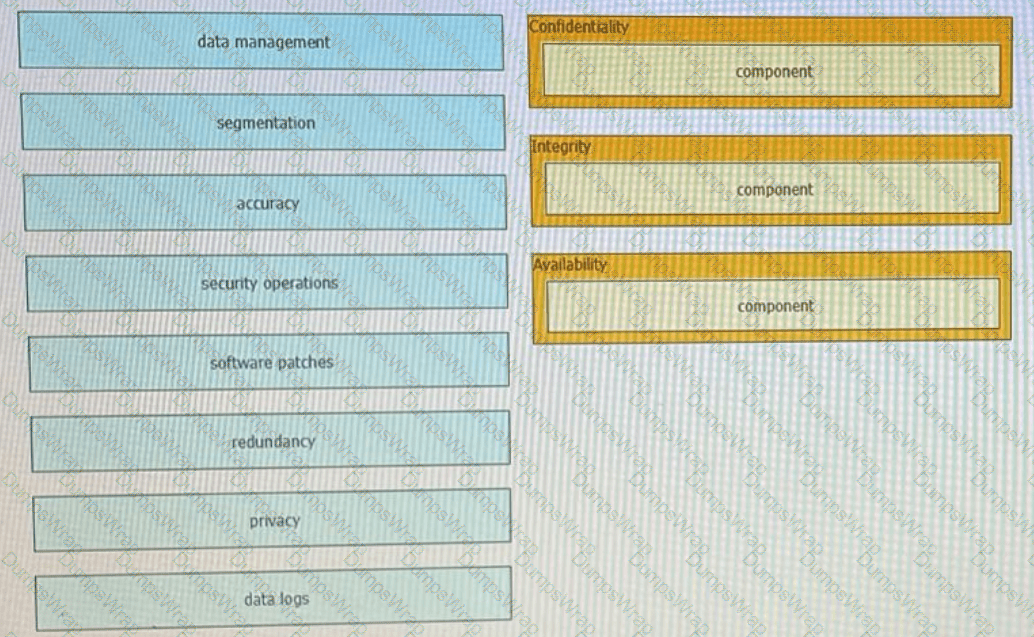
Drag and drop the high-level descriptions of network automation and network orchestration on the left to the corresponding category on the right in no particular order.
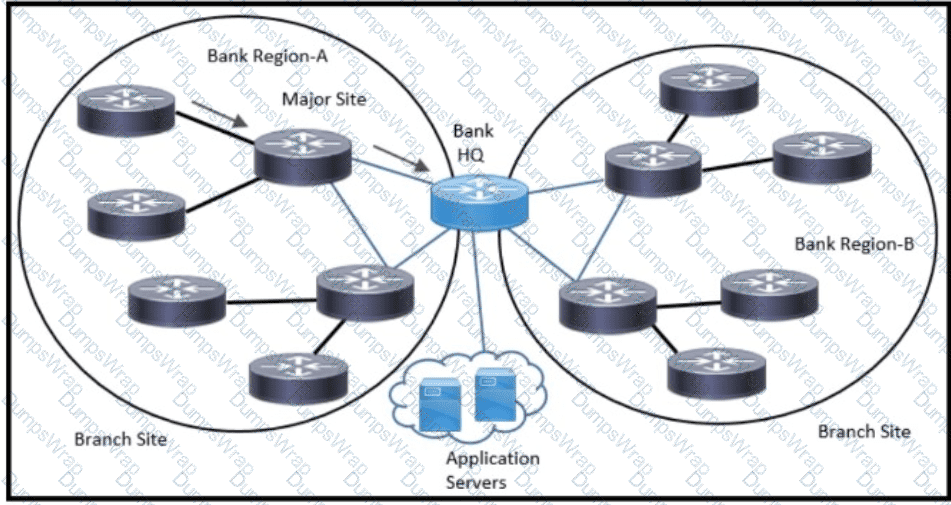
Refer to the exhibit. An architect has been tasked to design an ISIS solution for a medium-size financial customer. The resulting design must meet these requirements:
Which two ISIS design aspects must be included? (Choose two.)
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
Implementing a network automation architecture usually follows a phased approach that increases automation as the new technology and processes in the preceding phases are integrated and adopted. What provides a model that greatly simplifies the interaction with network devices?
Which two compliance audit functions are useful to meet business requirements? (Choose two.)
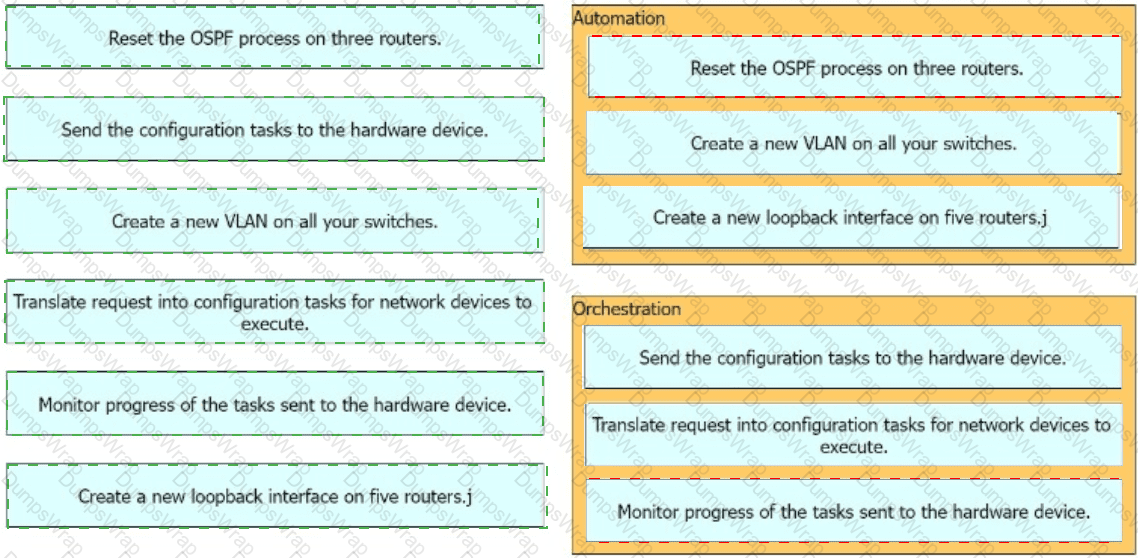
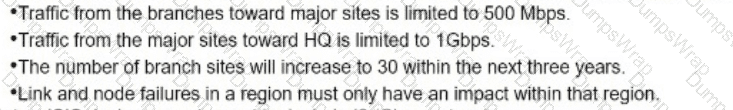
Indicate the nature of automation and orchestration tasks by dragging the tasks on the left to the corresponding category on the right in no particular order.
Company XYZ has implemented policy-based routing in their network. Which potential problem must be kept in mind about network reconvergence and PBR?
Company XYZ wants to use the FCAPS ISO standard for network management design. The focus of the design should be to minimize network outages by employing a set of procedures and activities to detect and isolate network issues and the appropriate corrective actions to overcome current issues and prevent them from occurring again. Which layer accomplishes this design requirement?
Which undesired effect of increasing the jitter compensation buffer is true?
If the desire is to connect virtual network functions together to accommodate different types of network service connectivity, what must be deployed?
An engineer is designing a DMVPN network where OSPF has been chosen as the routing protocol A spoke-to-spoke data propagation model must be set up Which two design considerations must be taken into account ? (Choose two)
Two companies need to implement an extranet overlay network solution by using a VPN tunnel over the internet to use each other ' s HTTP REST APIs. The solution must only provide data integrity because data confidentiality will be covered at the application layer The existing firewall devices will be used as VPN endpoints for the tunnel but they have limited available resources Which type of VPN tunnel must be deployed for the extranet service?
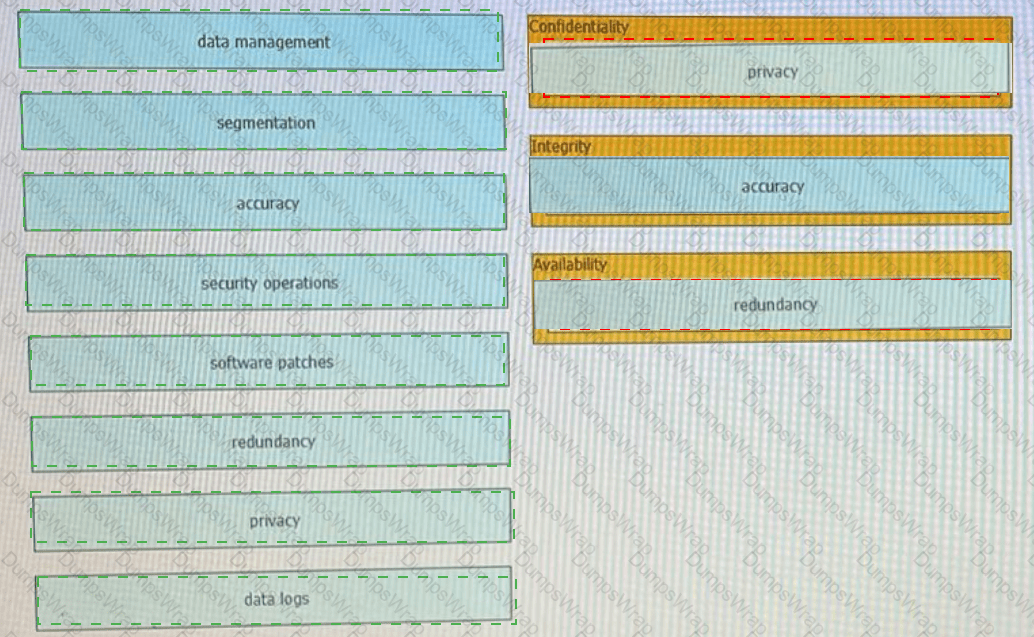
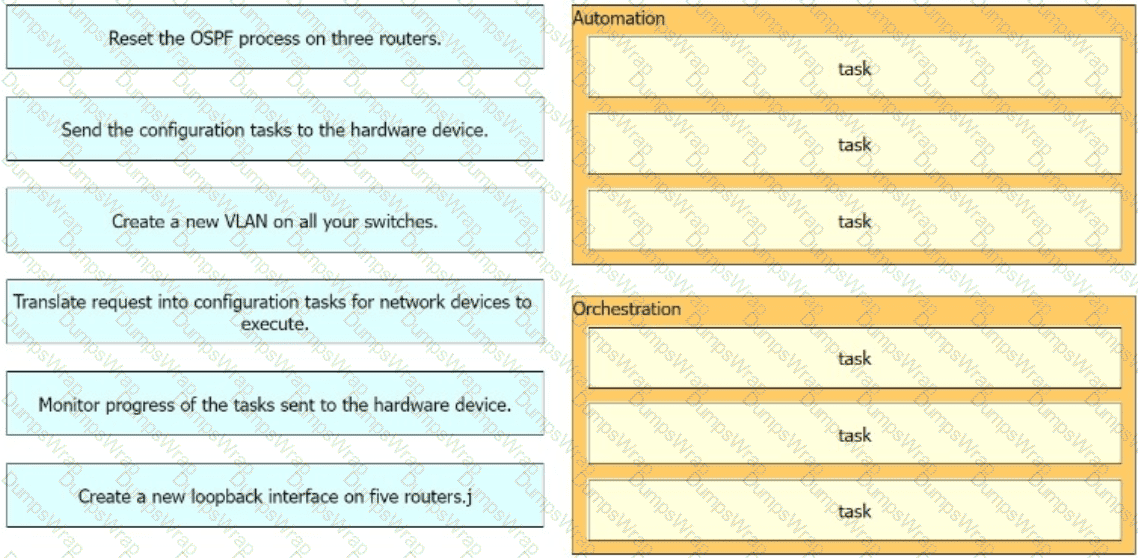
Drag t he components that are part of the CIA triad to the correct target on the right. Not all components are used.
Network designers often segment networks by creating modules for various reasons Sometimes however a network can be unintentionally segmented For instance, if the only way to connect a remote site to a headquarters or regional site is to connect them both to the public Internet the corporate network is now unintentionally segmented Which of the following option can be used to desegment the network in this situation?
By monitoring the effects of the design variations, you can characterize the relative resilience of the design. Which method involves disturbing the network by removing an active interface and monitoring how the change is handled by the network?
Which hybrid cloud environment enables businesses to more readily stage data-intensive and time-sensitive tasks closer to the source, which reduces latency, eases networking requirements, and improves data protection?
Which security architecture component offers streamlined security operations, ease of use, and visibility across all network security elements, independent of location or form factor?
The API of an SDN controller named CTL-A uses the HTTP POST method and the same URL for all resources The JSON body of each message is used to get information for specific resources and operations The API of a SDN controller named CTL-B uses HTTP CRUD methods and a uniform interface with different URLs for each resource Which API type is used by each SDN controller?
An Agile for Infrastructure transition often means dismantling traditional IT hierarchies and rebuilding it to align with business objectives and workflows Organizations are seeing the benefits of using automation tools in the network such as faster more efficient more effective delivery of products and services. Which two components help increasing overall productivity and improve company culture? (Choose two.)
In an OSPF network with routers connected together with Ethernet cabling, which topology typically takes the longest to converge?
A network automation team plans to develop tasks to configure services on a network by using a Python controller The configuration tasks must be implemented by using operations that support network-wide transactions The candidate configuration must be validated automatically for all targeted devices before being applied to each specific device What can be used to apply the configuration to the network devices?
Software-defined networking architecture is used for cost-effective, adaptable, and easily manageable applications. In which two software-defined networks is SDN commonly used? (Choose two.)
What is the key strategy to address scalability challenges In the rapidly evolving digital landscape with resilient designs?
A centralized control plane generally means one or more controllers gather the reachability and topology information from each switching device and calculate some part of the forwarding information at some place. How can a centralized control plane be defined or described?
What is a characteristic of a secure cloud architecture model?
A customer migrates from a traditional Layer 2 data center network Into a new SDN- based, spine-and-leaf VXLAN EVPN data center within the same location. The networks are joined to enable host migration at Layer 2. Which activity should be completed each time a legacy network is migrated?
Which two advantages of using DWDM over traditional optical networks are true? (Choose two.)
Which two statements describe network automation and network orchestration? (Choose two)
Company XYZ is designing the network for IPv6 security and they have these design
requirements:
A switch or router must deny access to traffic from sources with addresses that are correct, but are topologically incorrect
Devices must block Neighbor Discovery Protocol resolution for destination addresses that are not found in the binding table.
Which two IPv4 security features are recommended for this company? (Choose two)
The first step to building en A! strategy is understanding how it helps achieve business goals and objectives Al-first scorecard is an assessment of your organization ' s readiness to adopt and integrate AI technologies to gauge your capabilities and align stakeholders. Which scorecard is useful to understand whether the organization ' s digital infrastructure is strong enough to ensure seamless, standardized data flow between systems with optimal performance?
A network architect is working on the baseline policies dealing with the use of Infrastructure-as-Code within an IT department, and has been requested to present the plan at the monthly management board meeting. What are two examples of operational aspects of Infrastructure-as-Code that can be highlighted during the presentation? (Choose two.)
A large enterprise customer is planning a new WAN connection to its headquarters The current architecture is dual homed with static routing but users complain when a specific link fails Failure of the other link does not affect any services or applications The new WAN connection must provide the headquarters with a resilient network design and increase the return on investment Which solution should be recommended to the customer?
Scalability is a desirable attribute of a network, system, or process Poor scalability can result in poor system performance, necessitating the reengineering or duplication of systems Load scalability is the ability of a system to perform gracefully as traffic increases Which two problems can occur due to poor load scalability design? (Choose two )
Before migrating anything to the cloud, what are three cloud readiness assessment steps that are required to perform? (Choose three.)
Company XYZ wants to improve the security design of their network to include protection from reconnaissance and DoS attacks on their sub interfaces destined toward next hop routers. Which technology can be used to prevent these types of attacks?
Comparing traditional networks with SDN, where the network is only application aware, what is the advantage of SDN architecture?
risk is a major determining factor in whether a company chooses to go with a public cloud, a private, or a hybrid of both. what are two factors that impact the decision on which cloud service placement model to use? (choose two)
Setting a specific goal for throughput based on per-second data rates between end hosts does not identify the requirements for specific applications When specifying throughput goals for applications, it is important to understand the throughput requirements for each application Which two factors that can constrain application layer throughput? (Choose two.)
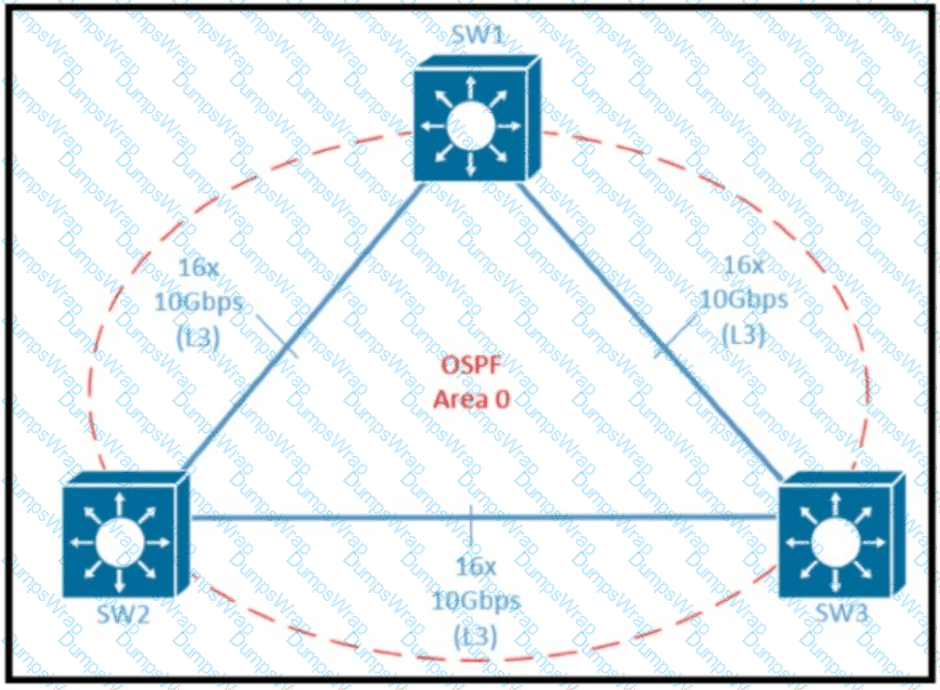
Refer to the exhibit Which two design options reduce the size of OSPF database in the shown topology? (Choose two.)
PaaS provides a cloud-based platform for developing, running, managing applications. Users access the PaaS through a GUI, where development or DevOps teams can collaborate on all their work across the entire application lifecycle including coding, integration, testing, delivery, deployment, and feedback. Which benefit does an organization get by using PaaS?
When consumers that leverage laaS reach 100% resource capacity what can be used to redirect the overflow of traffic to the public cloud, so there is no disruption to service?
A customer has a functional requirement that states HR systems within a data center must be segmented from other systems that reside in the same data center and same VLAN The systems run legacy applications by using hard-coded IP addresses with all HR systems dedicated to 129 to 254 of the 10 20.20 0/24 prefix Which segmentation method is optimal for the customer?
Company XYZ has designed their network to run GRE over IPsec on their Internet- based VPN to connect two sites Which IPsec tunneling feature can they enable to optimize the data flow while ensuring that the headers contain no duplicate IP addresses?