CrowdStrike Certified SIEM Engineer Questions and Answers
What is the recommended order of the three required activities to build an efficient CQL query?
You need to provide a colleague the appropriate role to allow for configuration of connectors and creation of SOAR automations in Next-Gen SIEM.
Which role will provide these permissions while also maintaining least privilege?
Which command helps visualize in real time whether sources and sinks are working properly in the Log Collector?
You notice a larger than expected ingest delay from one of your high-volume streaming log collectors.
Which setting should you increase on the log collector to improve performance?
You are performing a search query using data from the Falcon Sensor and third-party data connectors.
Which Advanced Event Search data source should you choose?
You are reviewing logs and find that the content appears as one large block of text within the @rawstring field for incoming firewall logs. The other expected structured fields are empty.
What is the cause of this issue?
Which Falcon LogScale Collector mode keeps the log source configuration stored locally on the collector host instead of centrally in Fleet Management?
What dashboard presents a view of third-party data ingestion over the past 30 days?
An internal security team identified a small number of high-risk users. They ask you to create an app that will monitor these users and trigger an alert when specific suspicious behavior is detected.
Which Falcon feature should you use to develop this app?
Following the principle of least privilege, which is the appropriate role to grant a Falcon Next-Gen SIEM user the permissions to read case data and write XDR data while denying the permission to write case templates?
Which CQL statement below includes correct placement of the AND statements and the pipe symbol?
When setting up a data connector, which parser can be used to transform incoming data into searchable events that trigger detections in Next-Gen SIEM?
You are onboarding a log source that includes a timestamp with a different timezone.
How should you address any time parsing errors that occur?
An event has the following fields:
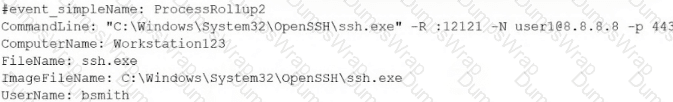
Which CQL query will output the frequency of a unique set of ComputerName, UserName, CommandLine?
You need to ingest data from a custom internal application hosted on-prem. The application writes logs to a file on a syslog server.
Which data connector would you use?
As a Next-Gen SIEM Engineer, you are responsible for managing and tuning correlation rules to improve the detection of potential security incidents. One of your correlation rules is designed to detect multiple failed login attempts that are followed by a successful login within a short time frame.
Which step would you take to tune this correlation rule to reduce false positives while maintaining its effectiveness?
You are reviewing a lookup file to determine whether an event was successfully parsed during ingestion.
Which metadata field indicates the event’s parsing status?
Which default parser would you use to parse the log event below?
Jan 15 14:22:07 host1 sshd[1234]: Failed login

