Certified in Risk and Information Systems Control Questions and Answers
Within the risk management space, which of the following activities could be
delegated to a cloud service provider?
Options:
Risk oversight
Control implementation
Incident response
User access reviews
Answer:
BAn organization wants to assess the maturity of its internal control environment. The FIRST step should be to:
Options:
validate control process execution.
determine if controls are effective.
identify key process owners.
conduct a baseline assessment.
Answer:
DExplanation:
A baseline assessment is the first step in assessing the maturity of an organization’s internal control environment. A baseline assessment is a comprehensive evaluation of the current state of the internal control structure, processes, and activities across the organization. A baseline assessment helps to identify the strengths and weaknesses of the existing internal controls, as well as the gaps and opportunities for improvement. A baseline assessment also provides a reference point for measuring the progress and effectiveness of the internal control improvement initiatives. The other options are not the first steps in assessing the maturity of an internal control environment, although they may be part of the subsequent steps. Validating control process execution is a technique to verify that the internal control activities are performed as designed and intended. Determining if controls are effective is a process to evaluate the adequacy and efficiency of the internal controls in achieving the desired outcomes and mitigating the risks. Identifying key process owners is a task to assign the roles and responsibilities for the internal control design, implementation, and monitoring to the appropriate individuals or groupswithin theorganization. References = CRISC Review Manual, pages 153-1541; CRISC Review Questions, Answers & Explanations Manual, page 742
Which strategy employed by risk management would BEST help to prevent internal fraud?
Options:
Require control owners to conduct an annual control certification.
Conduct regular internal and external audits on the systems supporting financial reporting.
Ensure segregation of duties are implemented within key systems or processes.
Require the information security officer to review unresolved incidents.
Answer:
CExplanation:
Ensuring segregation of duties are implemented within key systems or processes is the best strategy employed by risk management to prevent internal fraud, because it reduces the opportunity for a single person to manipulate or misuse the system or process for fraudulent purposes. Segregation of duties is a control that assigns different roles and responsibilities to different individuals, such that no one person can perform all the steps of a transaction or process. Requiring control owners to conduct an annual control certification, conducting regular internal and external audits on the systems supporting financial reporting, and requiring the information security officer to review unresolved incidents are all useful strategies to detect ordeter internal fraud, but they are not the best strategy to prevent it, as they do not directly address the root cause of fraud. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.3.1, page 197
Which of the following BEST mitigates ethical risk?
Options:
Ethics committees
Contingency scenarios
Awareness of consequences for violations
Routine changes in senior management
Answer:
AExplanation:
Ethics committees are typically responsible for developing, implementing, and overseeing an organization’s ethical guidelines and policies. They play a crucial role in mitigating ethical risk by ensuring that the organization’s operations align with its ethical standards123.
References
1What Is Ethically Informed Risk Management? - Journal of Ethics
2Five Ways to Reduce Ethics and Compliance Risk - Free Ethics Toolkit
35 Ways to Manage Ethical Risks - ClearRisk
Which of the following is a risk practitioner ' s MOST appropriate course of action upon learning that an organization is not compliant with its patch management policy?
Options:
Document the concern in an issue tracker.
Strengthen data loss prevention (DLP) controls.
Apply the most recent available patches.
Escalate the issue to the ethics committee.
Answer:
AWhich of the following is the PRIMARY concern related to using pseudonymization for the protection of an organization’s processed privacy data?
Options:
Authorized users can access personal data.
Updates to privacy data content are not allowed.
Individual data subjects can be re-identified.
Other information about the data subject can be revealed.
Answer:
CExplanation:
Pseudonymizationreplaces identifying fields in a data record with artificial identifiers or pseudonyms. However, unlike full anonymization,re-identification remains possibleif the pseudonym can be matched with external or hidden reference data.
CRISC and privacy-risk guidance (aligned with GDPR principles) emphasize that:
“The primary concern when using pseudonymization as a privacy safeguard is the potential for re-identification of individual data subjects.”
Pseudonymized data can still be linked back to individuals if the mapping key or auxiliary datasets are compromised.
True anonymization eliminates any reasonable means of re-identification, but pseudonymization does not.
Therefore, while pseudonymization reduces exposure, it doesnot fully eliminateprivacy risk.
Options A, B, and D are not inherent to pseudonymization:
Authorized access and update restrictions are policy issues, not intrinsic to pseudonymization.
Other information disclosure (D) could occur through inference but is secondary to direct re-identification.
Hence,C. Individual data subjects can be re-identifiedis the correct and verified answer as per CRISC and GDPR-aligned data protection practices.
Which of the following is the MOST significant risk associated with using cloud computing for disaster recovery?
Options:
Cloud vendor lock-in and dependency
Lack of adequate incident management capabilities
Use of multiple cloud access service brokers (CASBs)
Availability issues with cloud storage solutions
Answer:
AExplanation:
In cloud-based disaster recovery, CRISC emphasizes that the most impactful strategic risk isvendor lock-in and dependency. When disaster recovery capabilities rely on a single cloud provider, organizations become fully dependent on that provider’s technology, APIs, and platform architecture. This dependency makes it difficult and costly to migrate to another provider, limits flexibility in recovery options, and increases exposure if the provider experiences outages or changes service terms. While availability issues, CASB usage, and incident management gaps are important, they do not present the same level of strategic long-term operational and resilience impact as vendor lock-in.
During which phase of the system development life cycle (SDLC) should information security requirements for the implementation of a new IT system be defined?
Options:
Monitoring
Development
Implementation
Initiation
Answer:
DExplanation:
Information security requirements should be defined during theInitiationphase of the SDLC. This ensures that security is integrated into the design from the beginning, minimizing vulnerabilities and aligning security measures with business requirements. Early identification of security needs reduces rework and costs associated with later stages.
What is the PRIMARY benefit of risk monitoring?
Options:
It reduces the number of audit findings.
It provides statistical evidence of control efficiency.
It facilitates risk-aware decision making.
It facilitates communication of threat levels.
Answer:
CExplanation:
Risk monitoring is the process of tracking and evaluating the performance and effectiveness of the risk management process and controls, and identifying any changes or emerging risks that may affect theenterprise’s objectives and strategy. The primary benefit of risk monitoring is that it facilitates risk-aware decision making, as it provides timely and relevant information and feedback to the decision-makers and stakeholders, and enables them to adjust the risk strategy and response actions accordingly. Risk monitoring also helps to ensure that the risk management process is aligned with the enterprise’s risk appetite and tolerance, and supports the achievement of the enterprise’s goals and value creation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 239. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 239. CRISC Sample Questions 2024, Question 239.
Which of the following BEST helps to balance the costs and benefits of managing IT risk?
Options:
Prioritizing risk responses
Evaluating risk based on frequency and probability
Considering risk factors that can be quantified
Managing the risk by using controls
Answer:
AExplanation:
Prioritizing risk responses helps to balance the costs and benefits of managing IT risk by ensuring that the most significant risks are addressed first and that the resources allocated to risk management are used efficiently and effectively. Evaluating risk based on frequency and probability is a part of risk analysis, not risk response. Considering risk factors that can be quantified is also a part of risk analysis, and it does not necessarily capture all the relevant aspects of risk. Managing the risk by using controls is a possible risk response, but it does not guarantee that the costs and benefits of risk management are balanced, as some controls may be too expensive or ineffective for the level of risk they mitigate. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk Response, page 145.
Which of the following is the MOST important component in a risk treatment plan?
Options:
Technical details
Target completion date
Treatment plan ownership
Treatment plan justification
Answer:
CExplanation:
A risk treatment plan is a document that outlines the approach and actions to be taken to address the unacceptable risks identified in the risk assessment process1. A risk treatment plan should include the following components2:
The risk identification number and description
The risk treatment option chosen (e.g., avoid, reduce, share, or accept)
The risk treatment owner, who is responsible for implementing and monitoring the risk treatment
The risk treatment actions, which are the specific tasks or steps to be performed to execute the risk treatment
The risk treatment resources, which are the human, financial, or technical resources required to support the risk treatment
The risk treatment target date, which is the deadline for completing the risk treatment
The risk treatment performance indicators, which are the measures to evaluate the effectiveness and efficiency of the risk treatment
The risk treatment status, which is the current progress or outcome of the risk treatment
Among the four options given, the most important component in a risk treatment plan is the treatment plan ownership. This is because the treatment plan ownership defines theaccountability and authority for the risk treatment, and ensures that the risk treatment actions are carried out as planned and reported as required3. The treatment plan ownership also facilitates the communication and coordination among the stakeholders involved in the risk treatment, and enables the escalation and resolution of any issues or challenges that may arise during the risk treatment process4.
References = Risk Treatment (With Examples), ISO 27001 Risk Assessment & Risk Treatment: The Complete Guide, Risk Management Framework - Treat Risks, Risk Management Plan Components
Which of the following BEST indicates the condition of a risk management program?
Options:
Number of risk register entries
Number of controls
Level of financial support
Amount of residual risk
Answer:
DExplanation:
The best indicator of the condition of a risk management program is the amount of residual risk. Residual risk is the risk that remains after the implementation of risk responses. Residual risk reflects the effectiveness and efficiency of the risk management program in reducing the risk exposure to an acceptable level, and in aligning the risk profile with the risk appetite and tolerance of the enterprise. A low amount of residual risk indicates that the risk managementprogram is performing well, and that the controls are adequate and appropriate. A high amount of residual risk indicates that the risk management program is not functioning properly, and that the controls are insufficient or ineffective. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.2, page 191
Which of the following would be a risk practitioner’s GREATEST concern related to the monitoring of key risk indicators (KRIs)?
Options:
Logs are retained for longer than required.
Logs are reviewed annually.
Logs are stored in a multi-tenant cloud environment.
Logs are modified before analysis is conducted.
Answer:
DExplanation:
Modifying logs before analysis compromises the integrity and reliability of monitoring processes. This action creates a risk of inaccurate data feeding into key risk indicators, which undermines the effectiveness of monitoring and decision-making. Maintaining log integrity is a foundational practice inRisk Monitoring and Reporting.
What is MOST important for the risk practitioner to understand when creating an initial IT risk register?
Options:
Enterprise architecture (EA)
Control environment
IT objectives
Organizational objectives
Answer:
DExplanation:
The most important factor for the risk practitioner to understand when creating an initial IT risk register is the organizational objectives. The organizational objectives are the specific, measurable, achievable, relevant, and time-bound (SMART) goals that the organization aims to accomplish. The organizational objectives should be aligned with the organization’s vision, mission, and strategy, as well as the stakeholder expectations and needs. The organizational objectives should also reflect the desired outcomes and benefits of the organization, such as increasing revenue, reducing costs, improving quality, or enhancing customer satisfaction. Understanding the organizational objectives is the most important factor when creating an initial IT risk register, because it provides the context, scope, and criteria for identifying, analyzing, and prioritizing the IT risks that may affect or be affected by the organizational objectives.Understanding the organizational objectives also helps to align the IT risk management process with the organizational risk management process, and to communicate the value and impact of the IT risks and the IT risk responses to the senior management and other stakeholders. The other options are not the most important factor, although they may be relevant or influential to the IT risk register. Enterprise architecture (EA) is a conceptual blueprint that defines the structure and operation of an organization. EA describes the current and future state of the organization in terms of its business processes, information systems, and technology infrastructure, and the relationships and dependencies among them. EA also provides the principles, standards, and guidelines for designing, developing, and implementing the organization’s solutions and services. EA can help to understand the IT risk sources, causes, and effects, as well as the IT risk mitigation options and opportunities, but it does not define the purpose or the scope of the IT risk register. Control environment is the set of policies, procedures, and mechanisms that ensure the reliability, security, and quality of the organization’s activities and information. Control environment includes the tone and culture at the top, the roles and responsibilities for governance and oversight, the internal control framework and methodology, and the monitoring and reporting systems. Control environment can help to assess the IT risk levels and the IT risk responses, as well as to ensure the compliance and accountability of the IT risk management process, but it does not provide the context or the criteria for the IT risk register. IT objectives are the specific, measurable, achievable, relevant, and time-bound (SMART) goals that the IT function aims to accomplish. IT objectives should be aligned and consistent with the organizational objectives, as well as the IT strategy and IT governance. IT objectives should also reflect the expected outcomes and benefits of the IT function, such as delivering value, enabling innovation, or supporting transformation. IT objectives can help to identify and prioritize the IT risks that may affect or be affected by the IT objectives, but they are not the same as or more important than the organizational objectives. References = Three Steps to Creating a Simple IT Risk Register - Gartner, Risk Register Template and Examples | Prioritize and Manage Risk, IT Resources | Knowledge & Insights | ISACA
When documenting a risk response, which of the following provides the STRONGEST evidence to support the decision?
Options:
Verbal majority acceptance of risk by committee
List of compensating controls
IT audit follow-up responses
A memo indicating risk acceptance
Answer:
DExplanation:
The strongest evidence to support a risk response decision is a memo indicating risk acceptance. A memo is a formal and written document that can clearly communicate the rationale, criteria, and approval of the risk acceptance decision. Verbal majority acceptance of risk by committee, list of compensating controls, and IT audit follow-up responses are weaker evidence, as they may not be documented, verified, or aligned with the risk response decision. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 11; CRISC Review Manual, 6th Edition, page 144.
Which of the following is the PRIMARY reason to compare the business impact analysis (BIA) against the organization ' s business continuity plan (BCP)?
Options:
The results of the BIA quantify the BCP objectives and supporting technology for each operational area.
The BCP provides detailed information on alternative facilities to use in case of business interruptions.
The results of the BIA quantify the cost of the technology environment needed to restart each operational area.
The BCP provides the backup and restoration procedures to follow in case of business interruptions.
Answer:
AExplanation:
The BIA identifies critical processes, maximum tolerable downtime, and the business impact of disruptions. CRISC and business continuity practices emphasize that the BCP must bealignedwith BIA results. Comparing the BIA with the BCP ensures that recovery strategies, objectives (RTOs/RPOs), and supporting technologies specified in the BCP actually reflect the priorities and impact levels identified in the BIA for each operational area. Alternative facilities and backup/restoration procedures are important BCP components, but theprimary reasonfor comparison is to validate that the chosen solutions and recovery targets match business requirements. The BIA does not primarily “quantify the cost of the technology environment”; cost analysis may follow but is not the core BIA purpose. Therefore, ensuring that BCP objectives and enabling technology are consistent with BIA findings is the key objective of the comparison.
Which of the following would be MOST helpful to a risk practitioner when preparing a summary of current IT risk for senior management review?
Options:
Changes in risk mitigation plans
Resolution status of audit findings
Areas of elevated risk
Industry risk management benchmarks
Answer:
CExplanation:
Senior management requireshigh-level, decision-relevantinformation. CRISC guidance states that the most valuable elements to communicate areareas of elevated risk, because these represent conditions that may exceed risk appetite or require immediate action. Changes in mitigation plans and audit findings are important operational details but do not provide a clear picture of current exposure. Industry benchmarks offer context but do not describe the organization’s actual risk posture. Highlighting elevated risks helps executives prioritize resources, make treatment decisions, and determine whether escalations are required.
Which of the following is MOST helpful in identifying loss magnitude during risk analysis of a new system?
Options:
Recovery time objective (RTO)
Cost-benefit analysis
Business impact analysis (BIA)
Cyber insurance coverage
Answer:
CExplanation:
Business impact analysis (BIA) is the most helpful tool in identifying loss magnitude during risk analysis of a new system, as it involves estimating the potential financial and operational losses resulting from the disruption or degradation of the system. Recovery time objective (RTO), cost-benefit analysis, and cyber insurance coverage are not the most helpful tools, as they are more related to the recovery, evaluation, andtransfer of the risk, respectively, rather than the identification of the loss magnitude. References = CRISC Review Manual, 7th Edition, page 108.
An organization wants to launch a campaign to advertise a new product Using data analytics, the campaign can be targeted to reach potential customers. Which of the following should be of GREATEST concern to the risk practitioner?
Options:
Data minimization
Accountability
Accuracy
Purpose limitation
Answer:
DExplanation:
The greatest concern for the risk practitioner when an organization wants to launch a campaign to advertise a new product using data analytics is the purpose limitation. Purpose limitation is a principle that states that personal data should be collected for specified, explicit, and legitimate purposes, and not further processed in a manner that is incompatible with those purposes. By using data analytics to target potential customers, the organization may violate the purpose limitation principle if the data was collected for a different purpose and the customers did not consent to the new use of their data. Data minimization, accountability, and accuracy are other principles that should be followed, but they are not as concerning as the purposelimitation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
The GREATEST concern when maintaining a risk register is that:
Options:
impacts are recorded in qualitative terms.
executive management does not perform periodic reviews.
IT risk is not linked with IT assets.
significant changes in risk factors are excluded.
Answer:
DExplanation:
A risk register is a tool that records and tracks the identified risks, their causes, impacts, likelihood, responses, and owners. The greatest concern when maintaining a risk register is that significant changes in risk factors are excluded. Risk factors are the internal and external variables that influence the occurrence and impact of risks. Risk factors can change over time due to changes in the business environment, the IT landscape, the threat landscape, or the regulatory requirements. If the risk register does not reflect the significant changes in risk factors, it may not provide an accurate and current view of the enterprise’s risk profile and may not support effective risk management decisions and actions. The other options are not as concerning as the exclusion of significant changes in risk factors, as they involve different aspects of the risk register:
Impacts are recorded in qualitative terms means that the risk register uses descriptive scales, such as low, medium, and high, to measure the potential consequences of the risks. This may not be asprecise or consistent as quantitative measures, such as monetary values or percentages, but it does not necessarily affect the validity or usefulness of the risk register.
Executive management does not perform periodic reviews means that the risk register is not regularly evaluated and updated by the senior leaders of the enterprise. This may indicate a lack of management commitment or oversight for risk management, but it does not directly affect the quality or completeness of the risk register.
IT risk is not linked with IT assets means that the risk register does not associate the identified risks with the specific IT resources, such as hardware, software, data, or services, that are affected by or contribute to the risks. This may limit the visibility and traceability of the risks, but it does not necessarily affect the identification or assessment of the risks. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.2.2, pp. 21-22.
Within the three lines of defense model, the responsibility for managing risk and controls resides with:
Options:
operational management.
the risk practitioner.
the internal auditor.
executive management.
Answer:
AExplanation:
According to the three lines of defense model, the responsibility for managing risk and controls resides with the operational management, which forms the first line of defense. The operational management is the function that owns and manages risk as part of their accountability for achieving objectives. They are responsible for identifying, assessing, mitigating, and reportingon risks and controls within their areas ofoperation. They are also responsible for implementing and maintaining effective internal controls and ensuring compliance with policies, standards, and regulations.
In which of the following system development life cycle (SDLC) phases should controls be incorporated into system specifications?
Options:
Implementation
Development
Design
Feasibility
Answer:
CExplanation:
Controls should be incorporated into system specifications in the design phase of the system development life cycle (SDLC), because this is the phase where the system requirements are translated into detailed specifications and architectures that define how the system will be built and operated. Incorporating controls in the design phase ensures that the system is secure, reliable, and compliant from the start, and reduces the cost and complexity of implementing controls later in the SDLC. The other options are not the correct answers, because they are not the phases where controls are incorporated into system specifications. The implementation phase is the phase where the system is installed, configured, and tested. The development phase is the phase where the system is coded, integrated, and tested. The feasibility phase is the phase where the system concept and scope are defined and evaluated. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Within the system development life cycle (SDLC), controls should be specified during:
Options:
project initiation
business case development.
system integration testing.
requirements definition.
Answer:
DExplanation:
The correct answer isDbecause controls should be specified during therequirements definitionstage of the SDLC. At this point, business, security, and control requirements are identified and documented so they can be designed into the system from the beginning rather than added later.
The other options are less appropriate:
A. project initiationbegins the project, but detailed control specification occurs later when requirements are defined.
B. business case developmentjustifies the project but does not specify controls in sufficient detail.
C. system integration testingis used to test implemented controls, not to specify them.
Exact Extracts supporting the answer:
“The system development life cycle stage MOST suitable for incorporating internal controls is design.”
“In the system development life cycle the risk practitioner should first become involved during the planning phase.”
“Initiation is the phase in the system development life cycle where risk related to system requirements should be determined.”
“Before moving on to the system design phase it MUST be accomplished that the risk associated with the proposed system and controls is accepted by management.”
These extracts show that controls must be identified before design and implementation, and among the answer choices,requirements definitionis the correct stage for specifying them.
===========
Which of the following BEST enables effective risk-based decision making?
Options:
Performing threat modeling to understand the threat landscape
Minimizing the number of risk scenarios for risk assessment
Aggregating risk scenarios across a key business unit
Ensuring the risk register is updated to reflect changes in risk factors
Answer:
DExplanation:
An updatedrisk registerensures that decision-makers have accurate, timely information about current risks, enabling informed, risk-based decisions that align with organizational priorities and changes in the environment.
Which of the following practices BEST mitigates risk related to enterprise-wide ethical decision making in a multi-national organization?
Options:
Customized regional training on local laws and regulations
Policies requiring central reporting of potential procedure exceptions
Ongoing awareness training to support a common risk culture
Zero-tolerance policies for risk taking by middle-level managers
Answer:
CExplanation:
The best practice to mitigate risk related to enterprise-wide ethical decision making in a multi-national organization is to provide ongoing awareness training to support a common risk culture. A common risk culture is a set of shared values, beliefs, and behaviors that influence how the organization identifies, analyzes, responds to, and monitors risks. Ongoing awareness training can help to promote a common risk culture by educating the employees about the enterprise’s risk management objectives, policies, procedures, roles, and responsibilities, as well as the ethical standards and expectations that apply to their work. Ongoing awareness training can also help to reinforce the benefits of ethical decision making and the consequences of unethical behavior. Customized regional training on local laws and regulations, policies requiring central reporting of potential procedure exceptions, and zero-tolerance policies for risk taking bymiddle-level managers are also useful practices, but they are not as effective as ongoing awareness training to support a common risk culture. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 37.
Which of the following is the MOST important benefit of key risk indicators (KRIs) '
Options:
Assisting in continually optimizing risk governance
Enabling the documentation and analysis of trends
Ensuring compliance with regulatory requirements
Providing an early warning to take proactive actions
Answer:
DExplanation:
The most important benefit of key risk indicators (KRIs) is providing an early warning to take proactive actions, because this helps organizations to prevent or mitigate potential risks that may impact their operations, objectives, or performance. KRIs are specific metrics that measure the level and impact of risks, and provide timely signals that something may be going wrong or needs urgent attention. By monitoring and analyzing KRIs, organizations can identify and assess emerging or existing risks, and initiate appropriate risk responses before the risks escalate intosignificant issues. This can enhance the organization’s resilience, competitiveness, and value creation. The other options are less important benefits of KRIs. Assisting in continually optimizing risk governance is a benefit of KRIs, but it is not the most important one. Risk governance is the framework and process that defines how an organization manages its risks, including the roles, responsibilities, policies, and standards. KRIs can help to evaluate and improve the effectiveness and efficiency of risk governance, but they are not the only factor that influences it. Enabling the documentation and analysis of trends is a benefit of KRIs, but it is not the most important one. Documenting and analyzingtrends can help organizations to understand the patterns, causes, and consequences of risks, and to learn from their experiences. However, this benefit is more relevant for historical or retrospective analysis, rather than for proactive action. Ensuring compliance with regulatory requirements is a benefit of KRIs, but it is not the most important one. Compliance is the adherence to the laws, regulations, and standards that apply to an organization’s activities and operations. KRIs can help to monitor and demonstrate compliance, but they are not the only tool or objective for doing so. References = Why Key Risk Indicators Are Important for Risk Management 1
A large organization is replacing its enterprise resource planning (ERP) system and has decided not to deploy the payroll module of the new system. Instead, the current payroll system will continue to be
used. Of the following, who should own the risk if the ERP and payroll system fail to operate as expected?
Options:
The business owner
The ERP administrator
The project steering committee
The IT project manager
Answer:
AExplanation:
The business owner should own the risk if the ERP and payroll system fail to operate as expected, because the business owner is ultimately responsible for the business processes and objectives that depend on the systems. The other options are not the risk owners, because:
Option B: The ERP administrator is responsible for the technical aspects of the ERP system, but not the payroll system or the business outcomes.
Option C: The project steering committee is responsible for overseeing the project of replacing the ERP system, but not the ongoing operation and maintenance of the systems or the business risks.
Option D: The IT project manager is responsible for managing the project of replacing the ERP system, but not the payroll system or the business risks. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 90.
Which of the following would be MOST helpful when selecting appropriate protection for data?
Options:
Business objectives
Risk tolerance level
Data access requirements
Data classification
Answer:
DExplanation:
According to theISACA CRISC Review Manual, thedata classification processidentifies data sensitivity, criticality, and required protection levels.
“The level of protection for data should be based on its classification — i.e., the value of the information to the enterprise, its confidentiality, integrity, and availability requirements.”
Once classification (e.g., confidential, internal, public) is determined, corresponding safeguards (encryption, access control, backup policies) can be appropriately applied.
AandBare broad organizational factors.
C(access requirements) relates to functionality, not classification-based protection.
Therefore,D. Data classificationis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Information Asset Protection.
Which of the following has the GREATEST positive impact on ethical compliance within the risk management process?
Options:
Senior management demonstrates ethics in their day-to-day decision making.
An independent ethics investigation team has been established.
Employees are required to complete ethics training courses annually.
The risk practitioner is required to consult with the ethics committee.
Answer:
AExplanation:
According to the ISACA Risk IT Framework, one of the key principles for effective risk management is to establish tone at the top and accountability. This means that senior management should set an example of ethical behavior and culture, and communicate the importance of ethics and compliance to the entire organization. Senior management should also ensure that the risk management process is aligned with the organization’s mission, vision, values, and code of conduct, and that ethical risks are identified, assessed, and treated appropriately. By demonstrating ethics in their day-to-day decision making, senior management can have the greatest positive impact on ethical compliance within the risk management process, as they can influence the attitudes, behaviors, and actions of all stakeholders.
Which of the following is the MOST important reason for a risk practitioner to identify stakeholders for each IT risk scenario?
Options:
To ensure enterprise-wide risk management
To establish control ownership
To enable a comprehensive view of risk
To identify key risk indicators (KRIs)
Answer:
CExplanation:
Identifying stakeholders ensures that all perspectives are considered, contributing to a holistic view of risk and improving communication and response planning.
An organization has just started accepting credit card payments from customers via the corporate website. Which of the following is MOST likely to increase as a result of this new initiative?
Options:
Risk tolerance
Risk appetite
Inherent risk
Residual risk
Answer:
CExplanation:
Inherent risk is the most likely to increase as a result of the new initiative, because it is the risk that exists before any controls or mitigating factors are applied. Inherent risk reflects the natural or raw level of exposure that the organization faces from a given risk source or scenario. Accepting credit card payments from customers via the corporate website introduces new sources and types of risk, such as fraud, theft, data breach, or non-compliance, that increase the inherent risk level of the organization. Risk tolerance, risk appetite, and residual risk are all related to the risk management process, but they are not the most likely to increase as a result of the new initiative, as they depend on the organization’s risk strategy, objectives, and controls. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.1, page 51
Which of the following is the MOST important input when developing risk scenarios?
Options:
Key performance indicators
Business objectives
The organization ' s risk framework
Risk appetite
Answer:
BExplanation:
The most important input when developing risk scenarios is the business objectives, as they provide the context and scope for the risk identification and analysis process. Risk scenarios are hypothetical situations that describe the possible causes, events, and consequences of a risk. Risk scenarios help to understand and communicate the nature and impact of the risk, and to supportthe risk assessment and response planning. The business objectives are the goals andtargets that the organization wants to achieve through its processes, functions, and projects. The business objectives define the expected outcomes and performance of the organization, and the criteria for measuring and evaluating the success or failure of the organization. The business objectives also reflect the organization’s vision, mission, values, and strategy, and the needs and expectations of the stakeholders. The other options are not the most important inputs when developing risk scenarios, although they may be useful or relevant information. Key performance indicators are metrics that measure and monitor the progress and achievement of the business objectives, but they do not provide the context or scope for the risk scenarios. The organization’s risk framework is the set of principles, policies, and processes that guide and support the risk management activities across the organization, but it does not provide the context or scope for the risk scenarios. Risk appetite is the level of risk that the organization is willing to accept or avoid in pursuit of its business objectives, but it does not provide the context or scope for the risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 58.
An engineer has been assigned to conduct data restoration after a server storage failure. However, the procedure was not successful. Which of the following is the MOST probable cause of this situation?
Options:
Failure to test the disaster recovery plan (DRP)
Failure to prepare a business continuity plan (BCP)
Insufficient data captured in the business impact analysis (BIA)
Insufficient definition of the recovery point objective (RPO)
Answer:
DExplanation:
The RPO defines how much data loss is acceptable during system failure. If not clearly defined, restoration may skip key data, leading to incomplete recovery. ISACA guidelines highlight that alignment of RPO/RTO with business objectives is critical for viable DR planning
Owners of technical controls should be PRIMARILY accountable for ensuring the controls are:
Options:
Mapped to the corresponding business areas.
Aligned with corporate security policies.
Effectively implemented and maintained.
Designed based on standards and frameworks.
Answer:
CExplanation:
Technical control owners are responsible for the day-to-day operation and maintenance of controls. Their primary accountability is to ensure that controls are effectively implemented and continue to operate as intended to mitigate associated risks.
Which of the following should be of GREATEST concern lo a risk practitioner reviewing the implementation of an emerging technology?
Options:
Lack of alignment to best practices
Lack of risk assessment
Lack of risk and control procedures
Lack of management approval
Answer:
BExplanation:
Risk assessment is a key process that identifies, analyzes, and evaluates the risks associated with the implementation of an emerging technology. It helps to determine the potential impact and likelihood of the risks, as well as the appropriate risk responses and controls. Lack of risk assessment can lead to poor decision making, inadequate risk mitigation, and unexpected consequences. Therefore, it should be of greatest concern to a risk practitioner reviewing the implementation of an emerging technology. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.2.1, p. 226-227
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of a disaster recovery plan (DRP)?
Options:
Number of users that participated in the DRP testing
Number of issues identified during DRP testing
Percentage of applications that met the RTO during DRP testing
Percentage of issues resolved as a result of DRP testing
Answer:
CExplanation:
A key performance indicator (KPI) is a measurable value that demonstrates how effectively an organization is achieving its objectives. In the context of disaster recovery planning (DRP), a KPI should reflect the ability of the organization to recover its critical business processes and applications within the predefined time frames and service levels. One of the most important KPIs for DRP is the percentage of applications that met the recovery time objective (RTO) during DRP testing. The RTO is the maximum acceptable length of time that a business process or application can be down after a disaster. By measuring the percentage of applications that met the RTO during DRP testing, the organization can evaluate the performance and reliability of its DRP, identify any gaps or weaknesses, and implement corrective actions to improve its readiness and resilience. The other options are not the best KPIs for DRP, as they do not directly measure the effectiveness of the recovery process. The number of users that participated in the DRP testing is a measure of the involvement and awareness of the staff, but not of the outcome of the testing. The number of issues identified during DRP testing is a measure of the quality and completeness of the DRP, but not of the actual recovery time. The percentage of issues resolved as a result of DRP testing is a measure of the improvement and maturity of the DRP, but not of the current recovery capability. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.2.3.3, Page 138.
Which of the following risk scenarios should be considered in a disaster recovery plan (DRP)?
Options:
A pandemic situation requiring remote work
A ransomware attack affecting critical systems
A vendor failing to notify the organization of a data breach
Hacking activity leading to theft of sensitive data
Answer:
BWhich of the following should be the PRIMARY input when designing IT controls?
Options:
Benchmark of industry standards
Internal and external risk reports
Recommendations from IT risk experts
Outcome of control self-assessments
Answer:
BExplanation:
The primary input when designing IT controls should be internal and external risk reports. IT controls are specific activities performed by persons or systems to ensure that business objectives are met, and thatthe confidentiality, integrity, and availability of data and the overall management of the IT function are ensured1. Designing IT controls means creating and implementing the appropriate measures or actions to reduce the likelihood or impact of the IT risks that may affect the organization2. Internal and external risk reports are documents that provide information and analysis on the current and potential IT risks that the organization faces, as well as their sources, drivers, consequences, and responses3. Internal risk reports are generated by the organization itself, such as by the IT risk management function, the internal audit function, or the business units. External risk reports are obtained from external sources, such as regulators, industry associations, or third-party service providers. Internal and external risk reports are the primary input when designing IT controls, because they help to:
Identify and prioritize the IT risks that need to be addressed by the IT controls;
Evaluate the likelihood and impact of the IT risks, and compare them against the organization’s risk appetite and tolerance;
Determine the most suitable and effective IT control objectives and activities to mitigate the IT risks;
Align the IT control design and implementation with the organization’s objectives, strategies, and values;
Monitor and measure the performance and effectiveness of the IT controls in reducing the IT risks. The other options are not the primary input when designing IT controls, as they are either less relevant or less specific than internal and external risk reports. Benchmark of industry standards is a comparison of the organization’s IT control practices and performance with those of other organizations in the same industry or sector4. Benchmark of industry standards can help to improve the quality and consistency of the IT control design and implementation, as well as to identify the best practices and gaps. However, benchmark of industry standards is not the primary input when designing IT controls, as it does not address the specific IT risks that the organization faces, or the IT control objectives and activities that are appropriate and effective for the organization. Recommendations from IT risk experts are the suggestions or advice from the professionals or specialists who have the knowledge and experience in IT risk management and IT control design and implementation5. Recommendations from IT risk experts can help to enhance the IT control design and implementation, as well as to provide guidance and support to the organization. However, recommendations from IT risk experts are not the primary inputwhen designing IT controls, as they are based on the opinions and perceptions of the experts, and may not reflect the actual or objective level and nature of the IT risks, or the IT control objectives and activities that are suitable and efficient for the organization. Outcome of control self-assessments is the result or conclusion of the evaluation and testing of the design and operation of the existingIT controls by the organization itself, such as by the IT control owners, the IT risk management function, or the business units6. Outcome of control self-assessments can help to improve the IT control design and implementation, as well as to detect and correct any issues or deficiencies. However, outcome of control self-assessments is not the primary input when designing IT controls, as it does not cover the new or emerging IT risks that the organization may face, or the IT control objectives and activities that are relevant and necessary for the organization. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.2.1, Page 189.
Which of the following would BEST indicate to senior management that IT processes are improving?
Options:
Changes in the number of intrusions detected
Changes in the number of security exceptions
Changes in the position in the maturity model
Changes to the structure of the risk register
Answer:
CExplanation:
The best indicator to senior management that IT processes are improving is the changes in the position in the maturity model. A maturity model is a framework that defines the levels of capability and performance of a process, such as IT processes, based on the criteria such as governance, management, control, measurement, and improvement. A maturity model can help to assess the current state and the desired state of the IT processes, and to identify the gaps, strengths, and opportunities for improvement. A maturity model can also help to communicate the progress and the value of the IT processes to the senior management, and to support the strategic alignment and integration of the IT processes with the business objectives. Changes in the position in the maturity model indicate that the IT processes are improving, as they show that the IT processes are moving from a lower level to a higher level of maturity, and that they are achieving higher standards of quality, efficiency, and effectiveness. Changes in the number of intrusions detected, changes in the number of security exceptions, and changes to the structure of the risk register are not as good as changes in the position in the maturity model, as they do not provide a comprehensive and consistent measure of the IT processes improvement, and they may not reflect the actual impact and performance of the IT processes. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 36.
Which of the following is the MOST significant indicator of the need to perform a penetration test?
Options:
An increase in the number of high-risk audit findings
An increase in the number of security incidents
An increase in the percentage of turnover in IT personnel
An increase in the number of infrastructure changes
Answer:
BExplanation:
An increase in the number of security incidents is the most significant indicator of the need to perform a penetration test, because it suggests that the organization’s IT systems or networks are vulnerable to attacks and may not have adequate security controls in place. A penetration test is a simulated attack on an IT system or network to identify and exploit its weaknesses and evaluate its security posture. A penetration test can help to discover and remediate the vulnerabilities that may have caused or contributed to the security incidents, and to prevent or reduce the likelihood and impact of future incidents. An increase in the number of high-risk audit findings, an increase in the percentage of turnover in IT personnel, and an increase in the number of infrastructure changes are all possible indicators of the need to perform a penetration test, but they are not the most significant indicator, as they do not directly reflect the actual or potential occurrence of security incidents. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.3.2, page 200
when developing IT risk scenarios associated with a new line of business, which of the following would be MOST helpful to review?
Options:
Organizational threats
Resource allocation plan
Competitor analysis
Cost-benefit analysis
Answer:
AA risk practitioner has become aware of production data being used in a test environment. Which of the following should be the practitioner ' s PRIMARY concern?
Options:
Sensitivity of the data
Readability of test data
Security of the test environment
Availability of data to authorized staff
Answer:
AExplanation:
Production data is the data that is used in the actual operation of a system or application, such as customer information, financial records, transactions, etc.
Test data is the data that is used in the testing or development of a system or application, such as dummy data, sample data, simulated data, etc.
A risk practitioner has become aware of production data being used in a test environment. This indicates that there is a risk of unauthorized access, use, disclosure, modification, or destruction of the production data, which may affect the confidentiality, integrity, and availability of the data.
The primary concern of the risk practitioner in this situation is the sensitivity of the data. This means that the risk practitioner should assess how valuable, critical, or confidential the data is, and what would be the impact or consequence if the data is compromised or lost.
The sensitivity of the data helps to determine the level of protection and control that is needed to safeguard the data, and the priority and urgency of the risk response actions.
The other options are not the primary concerns of the risk practitioner in this situation. They are either secondary or not essential for data protection.
The references for this answer are:
Risk IT Framework, page 32
Information Technology & Security, page 26
Risk Scenarios Starter Pack, page 24
The MOST effective approach to prioritize risk scenarios is by:
Options:
assessing impact to the strategic plan.
aligning with industry best practices.
soliciting input from risk management experts.
evaluating the cost of risk response.
Answer:
AExplanation:
The most effective approach to prioritize risk scenarios is by assessing the impact to the strategic plan, because this will help to align the risk management process with the organization’s vision, mission, and goals. The strategic plan is the document that defines the organization’s direction, priorities, and objectives, and guides the allocation of resources and efforts. By assessing theimpact to the strategic plan, the organization can determine which risk scenarios pose the greatest threat or opportunity to the achievement of the strategic objectives, and prioritize them accordingly. The other options are not as effective as assessing the impact to the strategic plan, because they do not directly relate to the organization’s specific context, needs, and expectations, as explained below:
B. Aligning with industry best practices is an approach that involves following the standards, norms, and expectations for risk management that are established and followed by the peers or competitors in the same industry or sector. Aligning with industry best practices can help to benchmark and compare the organization’s risk management performance and maturity, and identify areas for improvement or innovation. However, this approach is not as effective as assessing the impact to the strategic plan, because it does not account for the organization’s unique and customized risk scenarios, which may differ from the industry average or standard.
C. Soliciting input from risk management experts is an approach that involves seeking advice, guidance, or feedback from the professionals or specialists who have the knowledge, experience, or skills in risk management. Soliciting input from risk management experts can help to enhance the quality and validity of the risk analysis and evaluation, and provide insights and recommendations for risk mitigation. However, this approach is not as effective as assessing the impact to the strategic plan, because it does not reflect the organization’s risk appetite, preferences, and expectations, which may differ from the risk management experts’ opinions or perspectives.
D. Evaluating the cost of risk response is an approach that involves estimating the resources and efforts required to implement the risk response strategies, such as avoiding, reducing, transferring, or accepting the risk. Evaluating the cost of risk response can help to optimize the risk management efficiency and effectiveness, and balance the potential benefits and costs of taking risks. However, this approach is not as effective as assessing the impact to the strategic plan, because it does not consider the potential consequences and outcomes of the risk scenarios, which may affect the organization’s performance and reputation. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.1, page 45. The Ultimate Guide to Risk Prioritization - Hyperproof, Risk Prioritization: What Is It? [2021 Guide & Matrix] - ERM Software, What is Risk Prioritization | Centraleyes, Scenario Planning in Risk Management: Why It is Needed - SmartCompliance
Which of the following should be the PRIMARY consideration when prioritizing limited resources needed to implement overdue corrective actions arising from a recent internal audit?
Options:
Level of risk impact
Cost-benefit analysis
Key control indicator (KCI) measures
Availability of other technical controls
Answer:
AExplanation:
When allocating scarce resources for overdue audit corrective actions,risk impactis the main prioritization criterion.
CRISC guidance dictates that corrective actions should first address risksposing the greatest potential harmto the enterprise’s objectives—whether financial, reputational, operational, or compliance-related.
Supporting extract (CRISC study materials):
“Prioritization of treatment options for numerous risk scenarios will be most effective when based on the likelihood of compromise and subsequent impact.” (Slide 311).
Thus, thelevel of risk impactdetermines:
Which issues could cause the most damage if unaddressed.
Which corrective actions are most urgent.
The most effective allocation of resources for mitigation.
While cost-benefit and control indicators are valuable supplementary factors,impact severityalways takes precedence in a risk-based prioritization model.
Hence, the correct answer isA. Level of risk impact.
An organization is developing a risk universe to create a holistic view of its overall risk profile. Which of the following is the GREATEST barrier to achieving the initiative ' s objectives?
Options:
Lack of cross-functional risk assessment workshops within the organization
Lack of common understanding of the organization ' s risk culture
Lack of quantitative methods to aggregate the total risk exposure
Lack of an integrated risk management system to aggregate risk scenarios
Answer:
BExplanation:
Lack of common understanding of the organization’s risk culture is the greatest barrier to achieving the initiative’s objectives, because it hinders the alignment and integration of risk management across the organization. Risk culture is the set of shared values, beliefs, and behaviors that influence how risk is perceived and managed in an organization. A risk universe is a comprehensive and structured representation of all the sources and types of risk that an organization faces. Developing a risk universe requires a common understanding of the organization’s risk culture, as it affects the risk appetite, tolerance, and strategy of the organization. Lack of cross-functional risk assessment workshops, lack of quantitative methods to aggregate the total risk exposure, and lack of an integrated risk management system are all challenges that may affect thedevelopment of a risk universe, but they are not the greatest barrier, as they can be overcome with appropriate tools and techniques. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1, page 44
A risk owner has identified a risk with high impact and very low likelihood. The potential loss is covered by insurance. Which of the following should the risk practitioner do NEXT?
Options:
Recommend avoiding the risk.
Validate the risk response with internal audit.
Update the risk register.
Evaluate outsourcing the process.
Answer:
CExplanation:
According to the CRISC Review Manual1, the risk register is a tool that records the results of risk identification, analysis, evaluation, and treatment. The risk register should be updated whenever there is a change in the risk profile, such as when a risk response is implemented or a new risk is identified. Updating the risk register allows the organization to monitor the current status of risks and the effectiveness of risk responses. Therefore, the next step for the risk practitioner after identifying a risk with high impact and very low likelihood that is covered by insurance is to update the risk register with the new information. References = CRISC Review Manual1, page 191.
The BEST way to justify the risk mitigation actions recommended in a risk assessment would be to:
Options:
align with audit results.
benchmark with competitor s actions.
reference best practice.
focus on the business drivers
Answer:
DExplanation:
The best way to justify the risk mitigation actions recommended in a risk assessment would be to focus on the business drivers, which are the factors that influence the organization’s objectives, performance, and value creation12.
Focusing on the business drivers means aligning the risk mitigation actions with the organization’s strategic goals, priorities, and values, and demonstrating how the actions will support or enhance the organization’s capabilities, opportunities, and competitive advantage12.
Focusing on the business drivers also means communicating the benefits, costs, and trade-offs of the risk mitigation actions to the relevant stakeholders, and showing how the actions will address the organization’s risk appetite, tolerance, and exposure12.
The other options are not the best way to justify the risk mitigation actions, but rather possible sources of information or guidance that may support the justification. For example:
Aligning with audit results is a way to validate the effectiveness and efficiency of the risk mitigation actions, and to identify any gaps or weaknesses that need improvement34. However, audit results may not reflect the organization’s current or future business drivers, and may not capture the full scope or impact of the risk mitigation actions34.
Benchmarking with competitor’s actions is a way to compare the organization’s risk mitigation actions with the best practices or standards of the industry or market, and to identify any areas of improvement or differentiation56. However, competitor’s actions may not be suitable or applicable for the organization’s specific context, needs, or challenges, and may not align with the organization’s business drivers56.
Referencing best practice is a way to adopt the proven or accepted methods or techniques for risk mitigation, and to ensure the quality and consistency of the risk mitigation actions78. However, best practice may not be the most optimal or innovative solution for the organization’s unique situation, and may not address the organization’s business drivers78. References =
1: Risk IT Framework, ISACA, 2009
2: IT Risk Management Framework, University of Toronto, 2017
3: IT Audit and Assurance Standards, ISACA, 2014
4: IT Audit and Assurance Guidelines, ISACA, 2014
5: Benchmarking IT Risk Management Practices, ISACA Journal, Volume 4, 2017
6: Benchmarking: A Tool for Improving IT Risk Management, ISACA Now Blog, March 27, 2017
7: IT Risk Management Best Practices, ISACA Journal, Volume 1, 2018
8: IT Risk Management Best Practices, ISACA Now Blog, January 9, 2018
Which of the following is MOST important when determining risk appetite?
Options:
Assessing regulatory requirements
Benchmarking against industry standards
Gaining management consensus
Identifying risk tolerance
Answer:
DWhich of the following risk events would require the creation of a business continuity plan (BCP)?
Options:
A hardware failure resulting in system downtime
A phishing attack resulting in financial fraud
A ransomware attack resulting in encrypted data storage
An insider threat resulting in data leakage
Answer:
CExplanation:
The correct answer is C because a ransomware attack resulting in encrypted data storage directly threatens the organization’s ability to continue operations and recover critical business processes. A business continuity plan is required for events that can significantly disrupt the organization’s ability to operate over time. Ransomware can make systems and data unavailable for an extended period, which is exactly the kind of scenario that drives continuity and recovery planning.
The other options are less appropriate as the best answer:
A. A hardware failure resulting in system downtime may be handled through normal resilience, redundancy, incident response, or disaster recovery procedures, depending on severity.
B. A phishing attack resulting in financial fraud is serious, but it is more directly associated with security incident response, fraud handling, and financial controls.
D. An insider threat resulting in data leakage is also serious, but it primarily affects confidentiality and incident response rather than continuity of operations.
Exact Extracts supporting the answer:
“A business impact analysis is primarily used to evaluate the impact of disruption on an enterprise’s ability to operate over time.”
“The objective of a business impact analysis is best described as the identification of time-sensitive critical business functions and interdependencies.”
“The most critical process for prioritizing actions in a business continuity plan is business impact analysis.”
“The MOST significant threat to an enterprise” related to business continuity plans is when “plans are not up to date.”
“The MOST important risk an enterprise must consider when developing a disaster recovery plan is A business impact analysis has not been conducted.”
These extracts show that BCP is centered on sustained operational disruption. Among the options, ransomware resulting in encrypted data storage is the strongest continuity-driven event and therefore the best answer.
===========
QUESTION NO: 120 [Governance]
Which of the following BEST enables an organization to effectively mitigate internal conflicts of interest associated with vendor negotiations?
A. Performing a vendor risk assessment
B. Training employees to act ethically
C. Aligning governance policies with corporate objectives
D. Implementing compliance reporting
Answer: B
The correct answer is B because the best way to mitigate internal conflicts of interest in vendor negotiations is to strengthen ethical behavior through awareness, training, and reinforcement. Conflicts of interest are primarily people and conduct issues, so the most effective preventive approach is ensuring employees understand ethical expectations and act accordingly.
The other options are less effective for this specific issue:
A. Performing a vendor risk assessment evaluates vendor-related risk, but does not directly address employees’ internal conflicts of interest.
C. Aligning governance policies with corporate objectives is important broadly, but it is less direct than ethics-focused prevention.
D. Implementing compliance reporting may help detect issues, but training and ethical reinforcement are more effective preventive measures.
Exact Extracts supporting the answer:
“The best proactive approach for practicing professional ethics within an enterprise is to provide ethics awareness training.”
“The most effective way to support adherence to an enterprise ' s code of ethics is by ensuring periodic training evaluation and attestation of employees.”
“Upon identifying a contractor as both a software solutions provider and the architect for a digital transformation program the first recommended action is to identify and register a potential conflict of interest.”
“Developing and practicing ethical behavior within an enterprise contributes the most to building the risk culture.”
These extracts support that conflicts of interest are best mitigated through ethical awareness and conduct controls. Therefore, the best answer is training employees to act ethically .
===========
QUESTION NO: 121 [Governance]
The PRIMARY responsibility of the second line in the three lines model is to
A. review risk decisions
B. monitor policy compliance
C. implement controls.
D. audit controls
Answer: B
The correct answer is B because the second line in the three lines model is primarily responsible for monitoring policy compliance , overseeing risk management, and providing guidance and framework support. The second line does not own operational controls like the first line, and it does not provide independent assurance like the third line.
The other options are less appropriate:
A. review risk decisions may occur as part of oversight, but it is not the primary definition of the second line.
C. implement controls is primarily a first-line responsibility.
D. audit controls is a third-line responsibility, usually internal audit.
Exact Extracts supporting the answer:
“Establishing a risk management framework is a direct responsibility of the second line of defense.”
“Financial risk management would MOST likely be the responsibility of the second line of defense.”
“According to the three lines of defense model the data ethics function would MOST likely reside in the second line of defense.”
“Operational management is the function that manages risk according to the three lines of defense model.”
“The MOST significant benefit of using the three lines of defense model in a risk management framework of an enterprise is that it clarifies essential roles of the key stakeholders.”
These extracts show that the second line provides governance, oversight, and compliance-oriented monitoring rather than operational control implementation or independent audit. Therefore, the best answer is monitor policy compliance .
Which of the following criteria for assigning owners to IT risk scenarios provides the GREATEST benefit to an organization?
Options:
The risk owner understands the effect of loss events on business operations.
The risk owner is a member of senior leadership in the IT organization.
The risk owner has strong technical aptitude across multiple business systems.
The risk owner has extensive risk management experience.
Answer:
AExplanation:
The risk owner should be someone who has the authority, responsibility, and knowledge to manage the risk effectively and align it with the organizational strategy and objectives. The risk owner should also be able to communicate the impact of the risk on the business operations and the value proposition of the risk response. Understanding the effect of loss events on business operations is a key criterion for assigning risk owners, as it helps to prioritize and mitigate the risks that matter most to the organization.
References
•Why Assigning a Risk Owner is Important and How to Do It Right
•How to Write Strong Risk Scenarios and Statements - ISACA
•What Everybody Ought To Know About Project Risk Owners
Which of the following is the PRIMARY reason to conduct risk assessments at periodic intervals?
Options:
To ensure emerging risk is identified and monitored
To establish the maturity level of risk assessment processes
To promote a risk-aware culture among staff
To ensure risk trend data is collected and reported
Answer:
AWhat is the BEST information to present to business control owners when justifying costs related to controls?
Options:
Loss event frequency and magnitude
The previous year ' s budget and actuals
Industry benchmarks and standards
Return on IT security-related investments
Answer:
DExplanation:
The best information to present to business control owners when justifying costs related to controls is the return on IT security-related investments, because this shows the value and benefits of the controls in relation to their costs. Return on IT security-related investments is a metric that measures the effectiveness and efficiency of IT security controls by comparing the amount of money saved or gained from preventing or mitigating IT-related risks with the amount of money spent on implementing and maintaining the controls. By presenting this information, business control owners can see how the controls contribute to the achievement of the business objectives, such as reducing losses, increasing revenues, enhancing customer satisfaction, or improving compliance. This information can also help business control owners to prioritize and allocate resources for the most critical and beneficial controls, and to optimize the balance between risk and return. References = Cost Control: How Businesses Use It to Increase Profits
After an annual risk assessment is completed, which of the following would be MOST important to communicate to stakeholders?
Options:
A decrease in threats
A change in the risk profile
An increase in reported vulnerabilities
An increase in identified risk scenarios
Answer:
BExplanation:
A change in the risk profile would be the most important information to communicate to stakeholders after an annual risk assessment is completed, as it indicates how the risk landscape of the organization has changed over time, and how it affects the achievement of the business goals and objectives. A decrease in threats, an increase in reported vulnerabilities, and an increase in identified risk scenarios are also important information, but they are not the most important, as they are specific aspects of the risk profile, and do not provide a holistic view of the risk exposure and appetite of the organization. References = CRISC Review Manual, 7th Edition, page 109.
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of an anti-virus program?
Options:
Frequency of anti-virus software updates
Number of alerts generated by the anti-virus software
Number of false positives detected over a period of time
Percentage of IT assets with current malware definitions
Answer:
DExplanation:
An anti-virus program is a software that detects and removes malicious software, such as viruses, worms, or ransomware, from the IT assets, such as computers, servers, or networks. The effectiveness of an anti-virus program can be measured by the key performance indicators (KPIs) that reflect the achievement of the program objectives and the alignment with the enterprise’s risk appetite and tolerance. The best KPI to measure the effectiveness of an anti-virus program is the percentage of IT assets with current malware definitions. Malware definitions are the files or databases that contain the signatures or patterns of the known malicious software, and they are used by the anti-virus program to scan and identify the malware. The percentage of IT assets with current malware definitions indicates how well the anti-virus program is able to protect the IT assets from the latest or emerging threats, and reduce the exposure and impact of the risks associated with the malware. The other options are not as good as the percentage of IT assets with current malware definitions, as they may not reflect the quality or timeliness of the protection, or the alignment with the enterprise’s risk appetite and tolerance. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.3.2.1, pp. 171-172.
An organization has detected unauthorized logins to its client database servers. Which of the following should be of GREATEST concern?
Options:
Potential increase in regulatory scrutiny
Potential system downtime
Potential theft of personal information
Potential legal risk
Answer:
CExplanation:
Potential theft of personal information should be of greatest concern for an organization that has detected unauthorized logins to its client database servers, as it poses a serious threat to theconfidentiality, integrity, and availability of the client data and the reputation and trust of the organization. Potential theft of personal information is a scenario that involves the unauthorized access, disclosure, or use of the client data by malicious actors, such as hackers, competitors, or insiders. Potential theft of personal information can have significant impacts and consequences for the organization and its clients, such as:
It can compromise the privacy and security of the client data, and expose the clients to identity theft, fraud, or blackmail.
It can violate the legal and regulatory obligations and requirements of the organization, such as the General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), or the Payment Card Industry Data Security Standard (PCI DSS), and result in fines, penalties, or lawsuits.
It can damage the reputation and credibility of the organization, and erode the confidence and loyalty of the clients, and lead to loss of business or market share.
The other options are not the greatest concerns for an organization that has detected unauthorized logins to its client database servers. Potential increase in regulatory scrutiny is a possibleconsequence of the unauthorized logins, as it may trigger audits, investigations, or sanctions by the relevant authorities, but it is not the most critical or immediate concern. Potential system downtime is a possible consequence of the unauthorized logins, as it may disrupt or degrade the performance or availability of the database servers or the applications that depend on them, but it is not the most severe or lasting concern. Potential legal risk is a possible consequence of the unauthorized logins, as it may expose the organization to litigation or liability claims by the affected clients or parties, but it is not the most direct or urgent concern. References = Data Breach Response: A Guide for Business - Federal Trade Commission, IT Risk Resources | ISACA, How to Prevent Unauthorized Access to Your Database - ScaleGrid
Which of the following would be a risk practitioner ' s GREATEST concern with the use of a vulnerability scanning tool?
Options:
Increased time to remediate vulnerabilities
Inaccurate reporting of results
Increased number of vulnerabilities
Network performance degradation
Answer:
BExplanation:
The greatest concern for a risk practitioner with the use of a vulnerability scanning tool is the inaccurate reporting of results. A vulnerability scanning tool is a software that scans the network or system for known vulnerabilities and generates a report of the findings. However, the tool may produce false positives (reporting vulnerabilities that do not exist) or false negatives (missing vulnerabilities that do exist). This can lead to incorrect risk assessment, ineffective risk response, and wasted resources. Increased time to remediate vulnerabilities, increased number of vulnerabilities, and network performance degradation are other possible concerns, but they are not as critical as the inaccurate reporting of results. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
Which of the following is the MOST important consideration when communicating the risk associated with technology end-of-life to business owners?
Options:
Cost and benefit
Security and availability
Maintainability and reliability
Performance and productivity
Answer:
AExplanation:
The most important consideration when communicating the risk associated with technology end-of-life to business owners is the cost and benefit of the risk response options. Technology end-of- life is the situation when a technology product or service is no longer supported by the vendor or manufacturer, and may pose security, compatibility, or performance issues. The risk practitioner should communicate the cost and benefit of the possible risk responses, such as replacing, upgrading, or maintaining the technology, to the business owners, and help them to make informed and rational decisions. Security and availability, maintainability and reliability, and performance and productivity are other possible considerations, but they are not as important as the cost and benefit. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
An organization has decided to use an external auditor to review the control environment of an outsourced service provider. The BEST control criteria to evaluate the provider would be based on:
Options:
a recognized industry control framework
guidance provided by the external auditor
the service provider ' s existing controls
The organization ' s specific control requirements
Answer:
AExplanation:
The best control criteria to evaluate the outsourced service provider would be based on a recognized industry control framework. A control framework is a set of best practices, guidelines, and methodologies that provide a comprehensive and consistent approach to designing, implementing, and assessing controls. A recognized industry control framework is a control framework that is widely accepted and adopted by the industry and the regulators, and that reflects the current and emerging standards andexpectations for the control environment. A recognized industry control framework can help to ensure that the outsourced service provider meets the minimum and acceptable level of control quality and effectiveness, and that the control evaluation is objective, reliable, and comparable. The other options are not as good as a recognized industry control framework, as they are related to the specific sources, aspects, or requirements of the control criteria, not the overall structure and quality of the control criteria. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: IT Control Assessment, page 69.
The FIRST step for a startup company when developing a disaster recovery plan (DRP) should be to identify:
Options:
Current vulnerabilities
Recovery time objectives (RTOs)
Critical business processes
A suitable alternate site
Answer:
CExplanation:
Thefoundationof any DRP is identifying whichbusiness processes are criticalto the organization’s operations and survival.
CRISC guidance:
“The initial step in disaster recovery and business continuity planning is identifying and prioritizing critical business processes and the resources required to support them.”
From there, RTOs and recovery strategies are developed.
Hence,C. Critical business processesis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Business Impact and Continuity Planning.
Improvements in the design and implementation of a control will MOST likely result in an update to:
Options:
inherent risk.
residual risk.
risk appetite
risk tolerance
Answer:
BExplanation:
Residual risk is the risk that remains after applying controls to mitigate the inherent risk. Inherent risk is the risk that exists before considering the controls. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk tolerance is the acceptable level of variation from the risk appetite. Improvements in the design and implementation of a control will most likely result in an update to the residual risk, because they will reduce the likelihood and impact of the risk event, and therefore lower the risk exposure and value. By improving the design and implementation of a control, the organization can enhance the effectiveness and efficiency of the control, and ensure that it is aligned with the risk objectives, expectations, and outcomes. The improvement can also address any gaps, overlaps, redundancies, or conflicts among the controls, and any changes or enhancements that are needed to optimize the controls. The other options are less likely to be updated due to improvements in the design and implementation of a control. The inherent risk will not change, as it is based on the nature and value of the asset and the threats and vulnerabilities that exist. The risk appetite and the risk tolerance will also not change, as they are based on the organization’s culture, strategy, and stakeholder expectations. Therefore, the most likely factor to be updated is the residual risk, as it reflects the actual risk level that the organization faces after applying the controls. References = Risk IT Framework, ISACA, 2022, p. 131
Which of the following BEST enables the timely detection of changes in the security control environment?
Options:
Control self-assessment (CSA)
Log analysis
Security control reviews
Random sampling checks
Answer:
AExplanation:
Understanding the Question:
The question asks which method best enables timely detection of changes in the security control environment.
Analyzing the Options:
A. Control self-assessment (CSA):Allows for continuous monitoring and quick detection of any changes or deficiencies in controls.
B. Log analysis:Useful for detecting security incidents but not as comprehensive as CSA for overall control environment changes.
C. Security control reviews:Typically periodic and might not be as timely.
D. Random sampling checks:Not as systematic or comprehensive as CSA.
Control Self-Assessment (CSA):CSA involves regular, structured evaluations by internal staff to ensure controls are working effectively. It promotes early detection of issues by those directly responsible for the controls.
Timeliness:CSA is an ongoing process, making it more timely in identifying changes compared to periodic reviews or random checks.
The BEST key performance indicator (KPI) to measure the effectiveness of a backup process would be the number of:
Options:
resources to monitor backups
restoration monitoring reports
backup recovery requests
recurring restore failures
Answer:
DExplanation:
The number of recurring restore failures is the best key performance indicator (KPI) to measure the effectiveness of a backup process, as it helps to evaluate the reliability and quality of the backup data and the backup system. A backup process is a process of creating and storing copies of data or systems to enable recovery in case of data loss, corruption, or disaster. A restore process is a process of retrieving and restoring the backup data or systems to the original or alternative location or state. A restore failure is an event that occurs when the restore processfails to complete successfully or correctly, due to various reasons, such as corrupted or missing backup data, incompatible or outdated backup system, or insufficient or unavailable resources. A recurring restore failure is a restore failure that happens repeatedly or frequently, indicating a persistent or systemic problem with the backup process.
The number of recurring restore failures helps to measure the effectiveness of the backup process by providing the following benefits:
It indicates the extent and magnitude of the backup process performance and quality issues, and the impact and severity of the backup process failures on the data or system availability and integrity.
It identifies and analyzes the root causes and contributing factors of the backup process failures, and the gaps or weaknesses in the backup process design, implementation, operation, or monitoring.
It provides feedback and learning opportunities for the backup process improvement and enhancement, and guides the development and implementation of corrective or preventive actions.
It communicates and reports the backup process status and results to the relevant stakeholders, and supports the alignment of the backup process with the organizational strategy and objectives.
The other options are not the best key performance indicators (KPIs) to measure the effectiveness of a backup process. The number of resources to monitor backups is a measure of the inputs or costs of the backup process, but it does not indicate the outputs or benefits of the backup process. The number of restoration monitoring reports is a measure of the documentation or communication of the backup process, but it does not reflect the actual or potential performance or quality of the backup process. The number of backup recovery requests is a measure of the demand or frequency of the backup process, but it does not evaluate the reliability or quality of the backup process. References = 12 Process KPIs to Monitor Process Performance in 2024 - AIMultiple, IT Risk Resources | ISACA, Mastering RTO and RPO in Backup Strategies: A Key to Data Recovery Success
Which of the following is the PRIMARY concern for a risk practitioner regarding an organization ' s adoption of innovative big data analytics capabilities?
Options:
It may be expensive to maintain a data lake.
It may be difficult to find experts who can develop analytical queries.
There may be a lack of documented processes for big data analysis.
Analytics methods may identify someone who was previously de-identified.
Answer:
DExplanation:
The primary concern for a risk practitioner in adopting innovative big data analytics is the potential re-identification of individuals from previously anonymized data. Advanced analytics techniques can inadvertently combine datasets in ways that reveal personal identities, leading to privacy breaches and regulatory non-compliance. This risk is heightened when data from multiple sources are aggregated, increasing the chance of re-identification.
Which of the following is the FIRST step when developing a business case to drive the adoption of a risk remediation project by senior management?
Options:
Calculating the cost
Analyzing cost-effectiveness
Determining the stakeholders
Identifying the objectives
Answer:
DExplanation:
The first step when developing a business case to drive the adoption of a risk remediation project by senior management is to identify the objectives of the project. The objectives are the specific, measurable, achievable, relevant, and time-bound (SMART) goals that the project aims to accomplish. The objectives should be aligned with the organization’s vision, mission, and strategy, as well as the identified business problem or opportunity. The objectives should also reflect the expected benefits and outcomes of the project, such as reducing the risk exposure, enhancing the security posture, or improving the business performance. Identifying the objectives is the first step because it provides the direction, scope, and justification for the project, and it serves as the basis for evaluating the alternative solutions, estimating the costs and benefits, and communicating the value proposition to the senior management and other stakeholders. The other options are not the first step, although they may be subsequent or concurrent steps in the business case development process. Calculating the cost is a part of the financial analysis, which estimates the total expenditure and funding sources of the project, but it does not define the purpose or the scope of the project. Analyzing cost-effectiveness is a part of the economic analysis, which compares the costs and benefits of the alternative solutions and recommends the optimal one, but it does not specify the goals or the criteria of the project. Determining the stakeholders is a part of the stakeholder analysis, which identifies and assesses the interests, expectations, and influence of the parties involved in or affected by the project, but it does not establish the objectives or the rationale of the project. References = Business case: 7 key steps to build it and use it - Twproject: project …, Guide to developing the Project Business Case - GOV.UK, How to Write a Business Case: Template & Examples | Adobe Workfront
Which of the following would MOST likely drive the need to review and update key performance indicators (KPIs) for critical IT assets?
Options:
The outsourcing of related IT processes
Outcomes of periodic risk assessments
Changes in service level objectives
Findings from continuous monitoring
Answer:
BExplanation:
Key performance indicators (KPIs) are metrics used to measure and evaluate the achievement of the organization’s objectives and strategies1. KPIs for critical IT assets are KPIs that focus onthe performance and value of the IT assets that are essential for the organization’s operations and functions2. KPIs for critical IT assets may include metrics such as availability, reliability, utilization, cost, and security of the IT assets3. The need to review and update KPIs for critical IT assets may be driven by various factors, such as changes in the business environment, customer expectations, or regulatory requirements. However, the most likely factor that would drive the need to review and update KPIs for critical IT assets is the outcomes of periodic risk assessments. A risk assessment is a process that involves identifying, analyzing, and evaluating the risks and their potential impacts on the organization’s objectives and performance4. A periodic risk assessment is a risk assessment that is performed at regular intervals, such as monthly, quarterly, or annually, to capture the changes and updates in the risk environment and the risk profile5. The outcomes of periodic risk assessments would most likely drive the need to review and update KPIs for critical IT assets, as they would provide insights into the current and emerging risks that may affect the performance and value of the critical IT assets, as well as the effectiveness and efficiency of the existingand planned controls and responses. By reviewing and updating the KPIs for critical IT assets based on the outcomes of periodic risk assessments, the organization can ensure that the KPIs are relevant, realistic, and aligned with the organization’s risk appetite and tolerance, and that they provide accurate and timely information for decision making and reporting. The outsourcing of related IT processes, changes in service level objectives, and findings from continuous monitoring are not the most likely factors that would drive the need to review and update KPIs for critical IT assets, as they do not provide the same level of information and impact as the outcomes of periodic risk assessments. The outsourcing of related IT processes is a decision that involves transferring some or all of the IT processes that support or enable the critical IT assets to an external service provider. The outsourcing of related IT processes may affect the performance and value of the critical IT assets, but it does not necessarily require a review and update of the KPIs for critical IT assets, as the KPIs may still be valid and applicable for the outsourced IT processes. Changes in service level objectives are changes in the expected or agreed level of quality or performance of the IT services that support or enable the critical IT assets. Changes in service level objectives may affect the performance and value of the critical IT assets, but they do not necessarily require a review and update of theKPIs for critical IT assets, as the KPIs may still be consistent and compatible with the changed service level objectives. Findings from continuous monitoring are the results or outcomes of the ongoing observation and measurement of the performance and compliance of the IT processes and systems that support or enable the critical IT assets. Findings from continuous monitoring may affect the performance and value of the critical IT assets, but they do not necessarily require a review and update of the KPIs for critical IT assets, as the KPIs may still be relevant and reliable for the continuously monitored IT processes and systems. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.
Which of the following trends would cause the GREATEST concern regarding the effectiveness of an organization ' s user access control processes? An increase in the:
Options:
ratio of disabled to active user accounts.
percentage of users with multiple user accounts.
average number of access entitlements per user account.
average time between user transfers and access updates.
Answer:
DExplanation:
The average time between user transfers and access updates is a trend that would cause the greatest concern regarding the effectiveness of an organization’s user access control processes, as it indicates thedelay or inefficiency in updating the user access rights and privileges according to the user’s current role and responsibilities. This can result in unauthorized or excessive access to the organization’s information assets, and increase the risk of data leakage, fraud, or misuse. The user access control processes should ensure that the user access rights and privileges are reviewed and modified regularly, and especially when the user’s role or status changes, such as transfer, promotion, demotion, or termination. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question241. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 241. CRISC Sample Questions 2024, Question 241.
Which of the following is the MOST important consideration when developing an organization ' s risk taxonomy?
Options:
Leading industry frameworks
Business context
Regulatory requirements
IT strategy
Answer:
DWhich of the following would MOST likely result in updates to an IT risk appetite statement?
Options:
External audit findings
Feedback from focus groups
Self-assessment reports
Changes in senior management
Answer:
DExplanation:
An IT risk appetite statement is a document that expresses the amount and type of IT risk that an organization is willing to accept or pursue in order to achieve its objectives. An IT risk appetite statement can help guide the IT risk management process, by setting the boundaries, criteria, andtargets for IT risk identification, assessment, response, and reporting. An IT risk appetite statement should be aligned with the organization’s overall risk appetite and strategy, and should be reviewed and updated periodically to reflect the changes in the internal and external environment. One of the factors that would most likely result in updates to an IT risk appetite statement is changes in senior management. Senior management is the group of executives who have the authority and responsibility for the strategic direction and performance of the organization. Changes in senior management can affect the IT risk appetite statement, as they may introduce new perspectives, priorities, expectations, or preferences for IT risk taking or avoidance. Changes in senior management can also affect the IT risk appetite statement, as they may require new or revised IT objectives, goals, or initiatives, which may entail different levelsor types of IT risk. Therefore, changes in senior management should trigger a review and update of the IT risk appetite statement, to ensure that it is consistent and compatible with the new leadership and direction of the organization. References = Organisations must define their IT risk appetite and tolerance, Risk Appetite Statements - Institute of Risk Management, Develop Your Technology Risk Appetite - Gartner.
Which of the following is the BEST way to prevent the loss of highly sensitive data when disposing of storage media?
Options:
Physical destruction
Degaussing
Data anonymization
Data deletion
Answer:
AExplanation:
When disposing of storage media, the best way to prevent the loss of highly sensitive data is physical destruction. Here’s why:
Physical Destruction:
Physical destruction involves destroying the storage media so that the data it contains cannot be recovered or reconstructed.
Methods include shredding, crushing, incinerating, or using industrial-grade degaussers that destroy the magnetic fields on the media.
Comparison with Other Methods:
Degaussing:This method erases data by disrupting the magnetic fields of the storage media. While effective for some types of media, it may not work on all (e.g., solid-state drives) and does not provide a visual confirmation that the data is irrecoverable.
Data Anonymization:This process involves altering data to prevent identification of individuals, but it does not destroy the data itself and is not applicable for disposing of storage media.
Data Deletion:Simply deleting data does not remove it permanently. Deleted data can often be recovered using specialized software unless it is overwritten multiple times, which is still less reliable than physical destruction.
Security Best Practices:
Physical destruction is considered the most secure method because it ensures that the media is rendered completely unusable and the data cannot be retrieved by any means.
This method is recommended by various standards and frameworks, including NIST Special Publication 800-88 Guidelines for Media Sanitization.
When assessing the maturity level of an organization’s risk management framework, which of the following should be of GREATEST concern to a risk practitioner?
Options:
Reliance on qualitative analysis methods.
Lack of a governance, risk, and compliance (GRC) tool.
Lack of senior management involvement.
Use of multiple risk registers.
Answer:
CExplanation:
Senior management involvement is a critical driver for the success of any risk management program. Without their engagement, there is a lack of strategic oversight, resource allocation, and prioritization of risk management initiatives, directly impacting the organization ' s ability to meet risk objectives. This is emphasized in theGovernance Principlesof CRISC.
What is the BEST course of action when the business impact of a risk event is rated high, but the likelihood of risk materialization has decreased?
Options:
Adjust risk tolerance thresholds.
Adjust the associated key risk indicator (KRI).
Further mitigate the risk.
Accept the risk if within tolerance.
Answer:
DExplanation:
The correct answer isDbecause even though thebusiness impact remains high, thelikelihood has decreased, so the overall risk may now fall within acceptable tolerance. In CRISC, the appropriate course of action is to compare the resulting risk level against appetite and tolerance. If the residual exposure is now acceptable, the organization may accept the risk.
The other options are less appropriate:
A. Adjust risk tolerance thresholdsshould not be done simply because one risk has changed.
B. Adjust the associated key risk indicator (KRI)may be considered later if monitoring needs refinement, but it is not the primary action.
C. Further mitigate the riskmay be unnecessary if the risk is already within tolerance.
Exact Extracts supporting the answer:
“It is most important to reduce risk to a level that the enterprise is willing to accept when defining risk management strategies.”
“Residual risk is best reflected as risk remaining after the implementation of new or enhanced controls.”
“Acceptable risk for an enterprise is achieved when residual risk is within tolerance levels.”
“The risk treatment plan should be developed when risk levels exceed risk appetite or tolerance.”
These extracts support that the decision should be based on whether the remaining risk is within tolerance. If it is, the best course is toaccept the risk.
Participants in a risk workshop have become focused on the financial cost to mitigate risk rather than choosing the most appropriate response. Which of the following is the BEST way to address this type of issue in the long term?
Options:
Perform a return on investment analysis.
Review the risk register and risk scenarios.
Calculate annualized loss expectancy of risk scenarios.
Raise the maturity of organizational risk management.
Answer:
DExplanation:
The maturity of organizational risk management refers to the degree to which risk management is embedded and integrated into the organization’s culture, processes, and decision-making1. A higher level of maturity implies that the organization has a clear and consistent understanding ofits risk appetite and tolerance, and that it can effectively identify, assess, respond, monitor, and communicate risks2.
The best way to address the issue of participants focusing on the financial cost to mitigate risk rather than choosing the most appropriate response is to raise the maturity of organizational risk management. This can help to:
Ensure that risk management is aligned with the organization’s strategic objectives and values, and that risk responses are based on the potential impact and likelihood of risks, not just on the cost of mitigation
Foster a risk-aware culture that encourages proactive and collaborative risk management, and that recognizes and rewards good risk management practices
Provide adequate training and guidance for risk management roles and responsibilities, and ensure that risk management skills and competencies are developed and maintained
Implement a robust and consistent risk management framework, methodology, and tools that support the risk management process and enable continuous improvement and learning
Enhance the quality and reliability of risk information and reporting, and ensure that risk management performance and outcomes are measured and evaluated3
References = Risk Maturity Model - Wikipedia, Risk Maturity Model - ISACA, Risk Maturity Model - IRM
An organization moved its payroll system to a Software as a Service (SaaS) application. A new data privacy regulation stipulates that data can only be processed within the countrywhere it is collected. Which of the following should be done FIRST when addressing this situation?
Options:
Analyze data protection methods.
Understand data flows.
Include a right-to-audit clause.
Implement strong access controls.
Answer:
BExplanation:
The first step when addressing the situation of moving the payroll system to a SaaS application and complying with the new data privacy regulation is to understand the data flows. This means identifying where the data is collected, stored, processed, and transferred, and who has access to it. Understanding the data flows can help to determine the scope and impact of the regulation, as well as the potential risks and gaps in the current state. It can also help to identify the roles and responsibilities of the organization and the SaaS provider regarding data protection and compliance. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.3.1.2, p. 237-238
Which of the following would have the GREATEST impact on reducing the risk associated with the implementation of a big data project?
Options:
Data processing
Data quality
Data scalability
Data governance
Answer:
DExplanation:
Data governanceprovides a structured framework for handling data access, classification, compliance, and security. It ensures accountability, roles, and control mechanisms—critical formanaging risk in big data environments.
Which of the following is the FIRST step in managing the security risk associated with wearable technology in the workplace?
Options:
Identify the potential risk.
Monitor employee usage.
Assess the potential risk.
Develop risk awareness training.
Answer:
AExplanation:
The security risk associated with wearable technology in the workplace is the possibility and impact of unauthorized access, disclosure, or use of the data or information that are collected, stored, or transmitted by the wearable devices, such as smartwatches, fitness trackers, or glasses, that are worn or used by the employees12.
The first step in managing the security risk associated with wearable technology in the workplace is to identify the potential risk, which is the process of recognizing and describing the sources,causes, and consequences of the risk, and the potential impacts on the organization’s objectives, performance, and value creation34.
Identifying the potential risk is the first step because it provides the basis and input for the subsequent steps of the risk management process, such as assessing, treating, monitoring, and communicating the risk34.
Identifying the potential risk is also the first step because it enables the organization to understand and prioritize the risk, and to allocate the appropriate resources and controls for the risk management process34.
The other options are not the first step, but rather possible subsequent steps that may depend on or follow the identification of the potential risk. For example:
Monitoring employee usage is a step that involves collecting and analyzing data and information on the frequency, duration, and purpose of the wearable devices that are used by the employees, and detecting and reporting any deviations, anomalies, or issues that may indicate a security risk5 . However, this step is not the first step because it requires theidentification of the potential risk to provide the guidance and standards for the monitoring process5 .
Assessing the potential risk is a step that involves estimating and evaluating the likelihood and impact of the risk, and the level of risk exposure or tolerance for the organization34. However, this step is not the first step because it requires the identification of the potential risk to provide the information and data for the assessment process34.
Developing risk awareness training is a step that involves educating and training the employees and other stakeholders on the security risks and best practices associated with the wearable technology, and informing them of their roles, obligations, and responsibilities for the risk management process . However, this step is not the first step because it requires the identification of the potential risk to provide the content and objectives for the training process . References =
1: Wearable Devices in the Workplace: Security Threats and Protection1
2: 10 security risks of wearables | CSO Online2
3: Risk IT Framework, ISACA, 2009
4: IT Risk Management Framework, University of Toronto, 2017
5: Continuous Monitoring - ISACA3
Continuous Monitoring: A New Approach to Risk Management - ISACA Journal4
What Is Security Awareness Training and Why Is It Important? - Kaspersky5
Security Awareness Training - Cybersecurity Education Online | Proofpoint US
Which of the following is the MOST important consideration when multiple risk practitioners capture risk scenarios in a single risk register?
Options:
Aligning risk ownership and control ownership
Developing risk escalation and reporting procedures
Maintaining up-to-date risk treatment plans
Using a consistent method for risk assessment
Answer:
DExplanation:
A risk register is a document that records and tracks the information and status of the identified risks and their responses. It includes the risk description, category, source, cause, impact, probability, priority, response, owner, action plan, status, etc.
A risk scenario is a description or representation of a possible or hypothetical situation or event that may cause or result in a risk for the organization. A risk scenario usually consists of three elements: a threat or source of harm, a vulnerability or weakness, and an impact or consequence.
Multiple risk practitioners are the individuals or groups that are involved or responsible for the identification, analysis, evaluation, and communication of the risks and their responses. They may include the risk owners, risk managers, risk analysts, risk consultants, risk auditors, etc.
A single risk register is a risk register that is shared or used by multiple risk practitioners across the organization, and that contains the information and status of all the risks and their responses that are relevant or applicable to the organization.
The most important consideration when multiple risk practitioners capture risk scenarios in a single risk register is using a consistent method for risk assessment, which is the process of determining the significance and urgency of the risks that may affect the organization’s objectives and operations. Risk assessment involves measuring and comparing the likelihood and impact of various risk scenarios, and prioritizing them based on their magnitude and importance.
Using a consistent method for risk assessment when multiple risk practitioners capture risk scenarios in a single risk register ensures that the risk scenarios are captured and recorded in a uniform and standardized way, and that they are comparable and compatible with each other. It alsohelps to avoid or reduce the inconsistencies, discrepancies, or conflicts that may arise from the different perspectives, assumptions, or judgments of the multiple risk practitioners, and to ensure the accuracy, reliability, and validity of the risk register.
The other options are not the most important considerations when multiple risk practitioners capture risk scenarios in a single risk register, because they do not address the main challenge or issue that may arise from the multiple risk practitioners capturing risk scenarios in a single risk register, which is the lack of consistency or standardization in the risk assessment method.
Aligning risk ownership and control ownership means ensuring that the individuals or groups that are accountable and responsible for the risks and their responses are clearly defined and assigned, and that they have the authority and resources to perform their roles and duties. Aligning risk ownership and control ownership is important when multiple risk practitioners capture risk scenarios in a single risk register, but it is not the most important consideration, because it does not ensure that the risk scenarios are captured and recorded in a uniform and standardized way, and that they are comparable and compatible with each other.
Developing risk escalation and reporting procedures means establishing and implementing the processes and guidelines for communicating and sharing the information and status of the risks and their responses among the relevant stakeholders, and for escalating or transferring the risks and their responses to the appropriate levels or parties when necessary or required. Developing risk escalation and reporting procedures is important when multiple risk practitioners capture riskscenarios in a single risk register, but it is not the most important consideration, because itdoes not ensure that the risk scenarios are captured and recorded in a uniform and standardized way, and that they are comparable and compatible with each other.
Maintaining up-to-date risk treatment plans means updating and revising the actions or plans that are selected and implemented to address or correct the risks and their responses, based on the changes or developments that may occur in the risk environment or performance. Maintaining up-to-date risk treatment plans is important when multiple risk practitioners capture risk scenarios in a single risk register, but it is not the most important consideration, because it does not ensure that the risk scenarios are captured and recorded in a uniform and standardized way, and that they are comparable and compatible with each other. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 178
CRISC Practice Quiz and Exam Prep
What is the PRIMARY reason to periodically review key performance indicators (KPIs)?
Options:
Ensure compliance.
Identify trends.
Promote a risk-aware culture.
Optimize resources needed for controls
Answer:
BExplanation:
According to the CRISC Review Manual, the primary reason to periodically review key performance indicators (KPIs) is to identify trends, because it helps to monitor the changes and patterns in the performance and effectiveness of the risk management processes and controls. KPIs are metrics that measure the achievement of the objectives and targets of the risk management activities. Periodically reviewing KPIs allows the organization to evaluate the progress and results of the risk management strategies and actions, and to identify any gaps, issues, or opportunities for improvement. The other options are not the primary reason to periodically review KPIs, as they are related to other aspects or outcomes of the risk management process. Ensuring compliance is the reason to review key risk indicators (KRIs), which are metrics that measure the level of risk exposure and the occurrence of risk events.Promoting a risk-aware culture is the reason to review key goal indicators (KGIs), which are metrics that measure the alignment of the risk management with the business goals and values. Optimizing resources needed for controls is the reason to review key control indicators(KCIs), which are metrics that measure the efficiency and adequacy of the risk controls. References = CRISC Review Manual, 7th Edition, Chapter 3, Section 3.3.2, page 143.
A rule-based data loss prevention {DLP) tool has recently been implemented to reduce the risk of sensitive data leakage. Which of the following is MOST likely to change as a result of this implementation?
Options:
Risk likelihood
Risk velocity
Risk appetite
Risk impact
Answer:
AExplanation:
A rule-based data loss prevention (DLP) tool is a software solution that identifies and helps prevent unsafe or inappropriate sharing, transfer, or use of sensitive data. It can help an organization monitor and protect sensitive information across on-premises systems, cloud-based locations, and endpoint devices. It can also help an organization comply with regulations such as the Health Insurance Portability and Accountability Act (HIPAA) and General Data Protection Regulation (GDPR). A rule-based DLP tool works by comparing content to the organization’s DLP policy, which defines how the organization labels, shares, and protects data without exposing it to unauthorized users. The tool can then apply protective actions such as encryption, access restrictions, and alerts. As a result of implementing a rule-based DLP tool, the most likely change is the reduction of risk likelihood, which is the probability of a risk event occurring. By detecting and preventing data breaches, exfiltration, or unwanted destruction of sensitive data, a rule-based DLP tool can lower the chance of such incidents happening and thus decrease the risk likelihood. The other options are less likely to change as a result of implementing a rule-based DLP tool. Risk velocity is the speed at which a risk event impacts an organization, which depends on factors such as the nature of the threat, the response time, and the recovery process. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives, which depends on factors such as the organization’s culture, strategy, and stakeholder expectations. Risk impact is the potential loss or damage that a risk event can cause to an organization, which depends on factors such as the severity of the incident, the extent of theexposure, andthe resilience of the organization. While a rule-based DLP tool may have some influence on these factors, it is not the primary driver of change for them. References = Risk IT Framework, ISACA, 2022, p. 13
Which of the following should be the starting point when performing a risk analysis for an asset?
Options:
Assess risk scenarios.
Update the risk register.
Evaluate threats.
Assess controls.
Answer:
AExplanation:
Assessing risk scenarios is the starting point when performing a risk analysis for an asset. A risk scenario is a description of a possible event or situation that could cause harm or loss to an asset. Assessing risk scenarios involves identifying the sources and causes of risk, the potential impacts and consequences of risk, and the likelihood and frequency of risk occurrence. Assessing risk scenarios can help establish the risk context, scope, and criteria for the asset, and provide the basis for further risk analysis steps, such as evaluating threats, assessing controls, and updating the risk register. According to the CRISC Review Manual 2022, assessing risk scenarios is thefirst step in the IT risk assessment process1. According to the CRISC Review Questions, Answers & Explanations Manual 2022, assessing risk scenarios is the correct answer to this question
The BEST way to mitigate the high cost of retrieving electronic evidence associated with potential litigation is to implement policies and procedures for:
Options:
data classification and labeling.
data logging and monitoring.
data retention and destruction.
data mining and analytics.
Answer:
CImplementing which of the following controls would BEST reduce the impact of a vulnerability that has been exploited?
Options:
Detective control
Deterrent control
Preventive control
Corrective control
Answer:
DExplanation:
A vulnerability is a system flaw or weakness that can be exploited by a threat actor, potentially leading to a security breach or incident. A vulnerability that has been exploited means that a threat actor has successfully taken advantage of the vulnerability and compromised the system or network. Implementing controls can help reduce the impact of a vulnerability that has been exploited, by limiting or preventing the damage or loss caused by the security breach or incident. Controls are the mechanisms or procedures that ensure the security, reliability, and quality of an IT system or process. Controls can be classified into different types, depending on their purpose and function. The four types of controls mentioned in the question are:
Detective control: A control that monitors and detects the occurrence or attempt of a security breach or incident, and alerts the appropriate personnel or system. For example, a log analysis tool that identifies and reports any unauthorized access or activity on the system or network.
Deterrent control: A control that discourages or prevents a threat actor from exploiting a vulnerability or performing a malicious action, by increasing the perceived difficulty, risk, or cost of doing so. For example, a warning message that informs the user of the legal consequences of unauthorized access or use of the system or network.
Preventive control: A control that blocks or stops a threat actor from exploiting a vulnerability or performing a malicious action, by eliminating or reducing the vulnerability or the opportunity.Forexample, a firewall that filters and blocks any unwanted or malicious traffic from entering or leaving the system or network.
Corrective control: A control that restores or repairs the system or network to its normal or desired state, after a security breach or incident has occurred, by fixing or removing the vulnerability or the impact. For example, a backup and recovery tool that restores the data or functionality of the system or network that has been corrupted or lost due to the security breach or incident.
The best type of control for reducing the impact of a vulnerability that has been exploited is the corrective control, because it directly addresses the damage or loss caused by the security breach or incident, and restores the system or network to its normal or desired state. Corrective controls can help minimize the negative consequences of a security breach or incident, such as downtime, data loss, reputational harm, legal liability, or regulatory sanctions. Corrective controls can also help prevent or reduce the recurrence of the security breach or incident, by fixing or removing the vulnerability that has been exploited. References = Types of Security Controls, Security Controls: What They Are and Why You Need Them, Security Controls: Definition, Types & Examples.
Which component of a software inventory BEST enables the identification and mitigation of known vulnerabilities?
Options:
Software version
Assigned software manager
Software support contract expiration
Software licensing information
Answer:
AExplanation:
The software version is the component of a software inventory that best enables the identification and mitigation of known vulnerabilities. The software version is the specific release or update of a software product that has a unique identifier, such as a number or a name. The software version indicates the features, functions, and security patches that are included in the software product. By knowing the software version, the organization can compare it with the latest available version and identify any missing or outdated security fixes. The organization can then mitigate the known vulnerabilities by updating or upgrading the software to the latest version. The other components of a software inventory, such as the assigned software manager, the software support contract expiration, and the software licensing information, are not as directly related tothe identification and mitigation of known vulnerabilities, although they may provide some contextual or administrative information. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.3.2, page 2-25.
An organization recently implemented a machine learning-based solution to monitor IT usage and analyze user behavior in an effort to detect internal fraud. Which of the following is MOST likely to be reassessed as a result of this initiative?
Options:
Risk likelihood
Risk culture
Risk appetite
Risk capacity
Answer:
AExplanation:
Risk likelihood is most likely to be reassessed as a result of implementing a machine learning-based solution to monitor IT usage and analyze user behavior in an effort to detect internal fraud, as it may change the probability of fraud occurrence or detection, and affect the risk assessment and response. Risk culture, risk appetite, and risk capacity are not the most likely to be reassessed, as they are more stable and strategic aspects of risk management, and are not directlyinfluenced by the implementation of a specific solution. References = CRISC Review Manual, 7th Edition, page 108.
Which of the following is the BEST approach when a risk practitioner has been asked by a business unit manager to exclude an in-scope system from a risk assessment?
Options:
Postpone the risk assessment.
Facilitate the exception process.
Accept the manager ' s request.
Reject the manager ' s request.
Answer:
BExplanation:
Facilitating the exception process ensures that any deviations from the standard risk assessment procedures are formally documented, reviewed, and approved by appropriate governance bodies. This approach maintains the integrity of the risk management process while addressing the business unit manager ' s concerns.
Which of the following is the GREATEST concern if user acceptance testing (UAT) is not conducted when implementing a new application?
Options:
The probability of application defects will increase
Data confidentiality could be compromised
Increase in the use of redundant processes
The application could fail to meet defined business requirements
Answer:
DExplanation:
User acceptance testing (UAT) is a type of validation testing that ensures that the product meets the needs and expectations of the end users and the business stakeholders. UAT is usually conducted by the actual or representative users of the product, who perform various scenarios and tasks to verify that the product functions correctly and satisfies the business requirements. UAT is an important step in the software development life cycle, as it helps to identify and resolve any issues or gaps between the product and the requirements before the product is released.
If UAT is not conducted when implementing a new application, the greatest concern is that the application could fail to meet the defined business requirements, which could result in user dissatisfaction, loss of trust,reduced productivity, increased costs, and missed opportunities. The application may have technical defects, security vulnerabilities, or redundant processes, but these are not the primary purpose of UAT. UAT is focused on validating the business value and usability of the product, not the technical quality or security of the product. Therefore, the lack ofUAT could have a significant impact on the alignment of the product with the business objectives and user needs.
A risk practitioner is asked to present the results of the most recent technology risk assessment to executive management in a concise manner. Which of the following is MOST important to include in the presentation?
Options:
Residual risk levels
Compensating controls
Details of vulnerabilities
Failed high-risk controls
Answer:
ACalculation of the recovery time objective (RTO) is necessary to determine the:
Options:
time required to restore files.
point of synchronization
priority of restoration.
annual loss expectancy (ALE).
Answer:
CExplanation:
The recovery time objective (RTO) is a metric that defines the maximum acceptable time frame for restoring a system or service after a disruption. The RTO is determined by the business impact and requirements of the system or service, as well as the risk appetite and tolerance of the organization. The calculation of the RTO is necessary to determine the priority of restoration,which means the order and urgency of recovering the systems or services based on their criticality and dependency. The priority of restoration helps to optimize the use of resources and minimize the downtime and losses during a disaster recovery. The other options are not the correct answers, as they are not the main purpose of calculating the RTO. The time required to restore files is a factor that affects the RTO, but it is not the outcome of the RTO calculation. The point of synchronization is the point in time to which the data must be restored to ensure consistency and accuracy. The point of synchronization is related to the recovery point objective (RPO), not the RTO. The annual loss expectancy (ALE) is a measure of the expected loss peryear due to a specific risk or threat. The ALE is calculated by multiplying the single loss expectancy (SLE) by the annualized rate of occurrence (ARO). The ALE is not directly related to the RTO, although it may influence the RTO determination. References = Recovery Time Objective (RTO) - What Is It, Examples, Calculation; CRISC Review Manual, pages 197-1981; CRISC Review Questions, Answers & Explanations Manual, page 842
Senior management has asked a risk practitioner to develop technical risk scenarios related to a recently developed enterprise resource planning (ERP) system. These scenarios will be owned by the system manager. Which of the following would be the BEST method to use when developing the scenarios?
Options:
Cause-and-effect diagram
Delphi technique
Bottom-up approach
Top-down approach
Answer:
AExplanation:
A cause-and-effect diagram, also known as a fishbone diagram or an Ishikawa diagram, is a graphical tool that helps to identify and analyze the potential causes and effects of a problem or an event. A cause-and-effect diagram can be used to develop technical risk scenarios related to a recently developed ERP system, because it can help to:
Break down the complex problem or event into manageable and measurable categories and subcategories of causes and effects
Visualize the relationships and interactions among the various factors that contribute to the problem or event
Identify the root causes and the most significant effects of the problem or event
Generate ideas and hypotheses for testing and validating the problem or event
Communicate and present the problem or event clearly and logically to the stakeholders1
A cause-and-effect diagram can be constructed by following these steps:
Define the problem or event and write it in a box on the right side of the diagram
Draw a horizontal line from the box to the left side of the diagram, representing the main spine of the fishbone
Identify the major categories of causes that affect the problem or event, such as people, process, technology, environment, etc., and write them on the branches of the spine
For each category, brainstorm and list the possible subcategories and specific causes that influence the problem or event, and write them on the sub-branches of the spine
For each cause, identify and list the possible effects or consequences that result from the problem or event, and write them on the sub-sub-branches of the spine
Analyze the diagram and prioritize the causes and effects based on their frequency, severity, and controllability
Develop technical risk scenarios based on the most critical causes and effects, and describe how they could affect the ERP system and the organization1
Which of the following scenarios is MOST likely to cause a risk practitioner to request a formal risk acceptance sign-off?
Options:
Residual risk in excess of the risk appetite cannot be mitigated.
Inherent risk is too high, resulting in the cancellation of an initiative.
Risk appetite has changed to align with organizational objectives.
Residual risk remains at the same level over time without further mitigation.
Answer:
AExplanation:
Requesting a formal risk acceptance sign-off is the most likely scenario when the residual risk in excess of the risk appetite cannot be mitigated, because it indicates that the organization is willing to tolerate a higher level of risk than it normally would, and that the risk owner has the authority and accountability to accept the risk and its consequences. Risk acceptance is a risk response strategy that involves acknowledging the existence ofa risk and deciding not to take any action to reduce it. Risk acceptance is usually chosen when the cost or effort of mitigating therisk outweighs the potential benefits, or when no feasible mitigation options are available. Residual risk is the risk that remains after applying controls or mitigating factors. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Inherent risk, cancellation of an initiative, change of risk appetite, and constant residual risk are all possible scenarios that may affect the risk management process, but they are not the most likely to cause a risk practitioner to request a formal risk acceptance sign-off, as they do not necessarily involve a risk owner accepting a higher level of risk than the organization’s risk appetite. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.4.2, page 103
An organization is revising its IT security policy. Which of the following should be done FIRST to help ensure the policy is followed?
Options:
Develop a policy socialization and awareness strategy.
Implement technical controls to monitor for policy violations.
Benchmark the policy against industry peers.
Perform a gap analysis of the old and new policy.
Answer:
AExplanation:
The correct answer isAbecause the first thing that should be done to help ensure a revised IT security policy is followed is todevelop a policy socialization and awareness strategy. A policy cannot be followed consistently unless employees and stakeholders understand it, know their responsibilities, and are aware of expected and prohibited behaviors.
The other options are less appropriate as the first step for adoption:
B. Implement technical controls to monitor for policy violationsmay support enforcement later, but awareness must come first.
C. Benchmark the policy against industry peersmay improve policy quality, but it does not ensure internal compliance.
D. Perform a gap analysis of the old and new policymay help assess changes, but it does not directly ensure people will follow the revised policy.
Exact Extracts supporting the answer:
“To make a BYOD policy effective the most enabling approach is educating users on acceptable and unacceptable practices.”
“The best proactive approach for practicing professional ethics within an enterprise is to provide ethics awareness training.”
“The most effective way to support adherence to an enterprise ' s code of ethics is by ensuring periodic training evaluation and attestation of employees.”
“When developing an IT risk awareness program the primary consideration is how technology risk can affect each attendee’s area of business.”
“The BEST approach when conducting an IT risk awareness campaign is to provide common messages tailored for different groups.”
These extracts support that awareness and communication are the most effective first actions to encourage adherence to a revised policy.
===========
A risk register BEST facilitates which of the following risk management functions?
Options:
Analyzing the organization ' s risk appetite
Influencing the risk culture of the organization
Reviewing relevant risk scenarios with stakeholders
Articulating senior management ' s intent
Answer:
CExplanation:
Purpose of a Risk Register:
A risk register consolidates all identified risks, their status, and mitigation actions in one place. It serves as a tool for tracking and managing risks systematically.
Facilitating Risk Management Functions:
By documenting risk scenarios, a risk register provides a comprehensive view of potential threats and their impact on the organization.
It enables effective communication and review of these scenarios with stakeholders, ensuring that all relevant parties are aware of and understand the risks.
Engaging Stakeholders:
Reviewing the risk register with stakeholders helps in validating the risks, assessing their impact, and determining appropriate responses.
It fosters collaboration and ensures that risk management activities are aligned with the stakeholders ' expectations and the organization ' s objectives.
Comparing Other Functions:
Analyzing Risk Appetite:While important, this is not the primary function of a risk register.
Influencing Risk Culture:The risk register contributes to risk culture but is primarily a tracking and communication tool.
Articulating Senior Management ' s Intent:This is more related to policy and strategy documents, whereas the risk register is a practical tool for managing specific risks.
References:
The CRISC Review Manual highlights the role of the risk register in consolidating risk information and facilitating stakeholder engagement (CRISC Review Manual, Chapter 2: IT Risk Assessment, Section 2.6 Risk Register) .
Of the following, who should be responsible for determining the inherent risk rating of an application?
Options:
Application owner
Senior management
Risk practitioner
Business process owner
Answer:
CExplanation:
Inherent risk rating is a measure of the natural level of risk that is part of an application, before any controls are applied1. Inherent risk rating helps to identify and prioritize the applications that pose the highest risk to the organization and require the most attention and resources for risk management2. The responsibility for determining the inherent risk rating of an application should belong to the risk practitioner, as they have the expertise and knowledge to perform a comprehensive and consistent risk assessment of the application, using a standard methodologyand criteria3. The risk practitioner should also communicate and report the inherent risk rating of the application to the relevant stakeholders, such as the application owner, senior management, and business process owner, and provide recommendations for risk mitigation4. The application owner, senior management, and business process owner are not the best choices for determining the inherent risk rating of an application, as they may not have the same level of skill and objectivity as the risk practitioner. The application owner is the person who has the authority and accountability for the application and its performance5. The application owner may be involved in providing input and feedback to the risk practitioner during the risk assessment process, but they may not be able to assess the inherent risk rating of the application independently and impartially, as they may have a vested interest in the application’s success and reputation6. Senior management is the group of executives who set the strategic direction and objectives of the organization and oversee its performance7. Senior management may be involved in approving and endorsing the risk assessment process and its results, but they may not be able to assess the inherent risk rating of the application in detail and depth, as they may have a broader and higher-level perspective of the organization’s risk profile and priorities8. The business process owner is the person who has the authority and accountability for a business process that is supported or enabled by the application. The business process owner may be involved in providing input and feedback to the risk practitioner during the risk assessment process, but they may not be able to assess the inherent risk rating of the application accuratelyand comprehensively, as they may have a limited and specific view of the application’s functionality and value. References = 2: Introduction toapplication risk rating & assessment | Infosec3: Application Security Risk: Assessment and Modeling - ISACA4: Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.1: Inherent Risk Rating - Shared Assessments - Third Party Risk Management5: [Application Owner - Gartner IT Glossary] 6: Perform Inherent Risk Analysis - Oracle7: [Senior Management - Definition, Roles and Responsibilities] 8: Rating Inherent and Residual Risk - Barn Owl : [Business Process Owner - Gartner IT Glossary] : [Business Process Owner - Roles and Responsibilities]
Which of the following is the PRIMARY role of the first line of defense with respect to information security policies?
Options:
Draft the information security policy.
Approve the information security policy.
Audit the implementation of the information security policy.
Implement controls in response to the policy requirements.
Answer:
DAn organization with a large number of applications wants to establish a security risk assessment program. Which of the following would provide the MOST useful information when determining the frequency of risk assessments?
Options:
Feedback from end users
Results of a benchmark analysis
Recommendations from internal audit
Prioritization from business owners
Answer:
BExplanation:
A benchmark analysis is a process of comparing the organization’s performance, practices, and processes with those of other organizations in the same industry or sector. A benchmark analysis can provide the most useful information when determining the frequency of risk assessments, because it can help the organization to identify the best practices, standards, and expectations for security risk management in its industry. A benchmark analysis can also help the organization to assess its current level of maturity, capability, and compliance in relation to security risk management, and to determine the gaps and areas for improvement. By conducting a benchmark analysis, the organization can establish a realistic and appropriate frequency of risk assessments that aligns with its industry norms and its own risk profile. The other options are not as useful as a benchmark analysis, because they do not provide a comprehensive and relevant view of the security risk management landscape, but rather focus on specific or partial aspects of the organization’s situation. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.3.2, page 18.
Which of the following is the MOST important characteristic of an effective risk management program?
Options:
Risk response plans are documented
Controls are mapped to key risk scenarios.
Key risk indicators are defined.
Risk ownership is assigned
Answer:
DExplanation:
The most important characteristic of an effective risk management program is that risk ownership is assigned. Risk ownership is the accountability and authority to manage a risk1. Assigning risk ownership means identifying and assigning the person or entity who is responsible for evaluating, treating, monitoring, and reporting on a specific risk2. Assigning risk ownership is essential for ensuring that the risk management program works effectively and efficiently, as it helps to:
Clarify the roles and responsibilities of the different functions or groups involved in risk management and internal control;
Ensure that the risks are managed in accordance with the organization’s objectives, strategies, and risk appetite;
Provide guidance and support to the risk owners in identifying, assessing, and mitigating the risks;
Monitor and evaluate the performance and effectiveness of the risk owners and the risk response actions;
Communicate and report on the risk status and issues to the relevant stakeholders and authorities. The other options are not the most important characteristic of an effective risk managementprogram, as they are either less relevant or less specific than assigning risk ownership. Risk response plans are documented. This option is a consequence or outcome of an effective risk management program, not a characteristic of it. Risk response plans are the actions or measures that are taken to modify the risk, such as reducing, avoiding, transferring, or accepting the risk3. Documenting risk response plans means recording and maintaining the details and outcomes of the risk responseactions, such as the objectives, scope, resources, timelines, performance indicators, and results4. Documenting risk response plans can help to improve the consistency and transparency of the risk management process, as well as to support the monitoring and evaluation of the risk response actions. However, documenting risk response plans is not the most important characteristic of an effective risk management program, as it does not address the accountability and authority for managing the risk. Controls are mapped to key risk scenarios. This option is a specific or narrow example of an effective risk managementprogram, not a general or broad characteristic of it. Controls are the measures or actions that are taken to reduce the likelihood or impact of a risk, or to increase the likelihood or impact of an opportunity5. Mapping controls to key risk scenarios means linking the controls to the specific situations or events that may affect the organization’s objectives, operations, or performance6. Mapping controls to key risk scenarios can help to enhance the design and implementation of the controls, as well as to evaluate the effectiveness and efficiency of the controls in mitigating the risk. However, mapping controls to key risk scenarios is not the most important characteristic of an effective risk management program, as it does not cover the other aspects of risk management, such as risk identification, assessment, treatment, and monitoring. Key risk indicators are defined. This option is a component or element of an effective risk management program, not a characteristic of it. Key risk indicators are the metrics that measure thelevel and trend of a risk that may affect the organization’s objectives, operations, or performance7. Defining key risk indicators means establishing and maintaining the criteria and methods for measuring and reporting on the risk8. Defining key risk indicators can help to enhance the risk identification, assessment, and reporting processes, as well as to support the risk decision making and prioritization. However, defining key risk indicators is not the most important characteristic of an effective risk management program, as it does not indicate the accountability and authority for managing the risk. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.1.1, Page 85.
A risk practitioner is organizing a training session lo communicate risk assessment methodologies to ensure a consistent risk view within the organization Which of the following i < the MOST important topic to cover in this training?
Options:
Applying risk appetite
Applying risk factors
Referencing risk event data
Understanding risk culture
Answer:
AExplanation:
Applying risk appetite is the most important topic to cover in a training session to communicate risk assessment methodologies. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. It is a key element of the risk management framework and influences the risk assessment process. Applying risk appetite helps to ensure a consistent risk view within the organization by providing a common basis for evaluating and prioritizing risks, aligning risk responses with business goals, and communicating risk information to stakeholders. The other options are not the most important topics to cover in a training session to communicate risk assessment methodologies, although they may be relevant and useful. Applying risk factors is a technique to quantify or qualify the likelihood and impact of risks based on predefined criteria or scales. Referencing risk event data is a source of information to identify and analyze risks based on historical or current incidents. Understanding risk culture is a factor that affectsthe risk behavior and attitude of the organization and its people. References = CRISC Review Manual, pages 40-411; CRISC Review Questions, Answers & Explanations Manual, page 612
An organization has an internal control that requires all access for employees be removed within 15 days of their termination date. Which of the following should the risk practitioner use to monitor
adherence to the 15-day threshold?
Options:
Operation level agreement (OLA)
Service level agreement (SLA)
Key performance indicator (KPI)
Key risk indicator (KRI)
Answer:
CExplanation:
A key performance indicator (KPI) is a metric that measures the achievement of a specific goal or objective. A KPI for the internal control that requires all access for employees be removed within 15 days of their termination date could be the percentage of employees whose access was removed within the specified time frame. This KPI would help the risk practitioner to monitor the compliance and effectiveness of the control and identify any deviations or issues.
References
•Key Performance Indicators (KPIs) - ISACA
•How to Improve Risk Awareness in the Workplace [+ Template] - AlertMedia
•[SITXWHS
Which of the following BEST promotes commitment to controls?
Options:
Assigning control ownership
Assigning appropriate resources
Assigning a quality control review
Performing regular independent control reviews
Answer:
AExplanation:
Commitment to controls is the degree to which the organization and its stakeholders support and adhere to the controls that are designed and implemented to manage or mitigate the risks1. Commitment to controls is essential for ensuring the effectiveness and efficiency of the controls, as well as the achievement of the organization’s objectives and strategies2. The best way to promote commitment to controls is to assign control ownership, which is the process ofidentifying and assigning the person or entity that has the authority and accountability for a control and its management3. By assigning control ownership, the organization can ensure that the controls are properly and promptly designed, implemented, monitored, and maintained, and that the issues or gaps in the controls are identified andresolved4. Assigning control ownership also helps to establish and communicate the roles and responsibilities of the control owners and the other stakeholders, and to enforce the accountability and performance of the control owners5. Assigning appropriate resources, assigning a quality control review, and performing regular independent control reviews are not the best ways to promote commitment to controls, as they donot provide the same level of authority and accountability as assigning control ownership. Assigning appropriate resources is the process of allocating and providing the necessary funds, staff, equipment, or technology that are required to support or enable the controls. Assigning appropriate resources can enhance the quality and performance of the controls, but it does not ensure that the controls are managed or maintained by a specific person or entity. Assigning a quality control review is the process of conducting and documenting a systematic and objective examination and evaluation of the controls, to ensure that they meet the established standards and requirements. Assigning a quality control review can improve the reliability and compliance of the controls, but it does not ensure that the controls are owned or operated by a specific person or entity. Performing regular independent control reviews is the process of performing and reporting an independent and impartial assessment and verification of the controls, to provide assurance and advice on the adequacy and effectiveness of the controls. Performing regular independent control reviews can provide feedback and recommendations for the controls, but it does notensure that the controls are implemented or improved by a specific person or entity. References = 1: Commitment Controls - IMF2: 17 COSO Principles of Effective Internal Control | Weaver3: [Control Ownership - ISACA] 4: [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.1: Control Design, pp. 233-235.] 5: [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.2: Control Implementation, pp. 243-245.] : Resource Allocation - an overview | ScienceDirect Topics : Quality Control Review - an overview | ScienceDirect Topics : IT Risk Resources | ISACA : [Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.1: Risk Identification, pp. 57-59.] : [Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.3: Control Monitoring and Maintenance, pp. 251-253.]
An organization’s expense claim system allows users to split large transactions into smaller ones to bypass limits. What should the risk practitioner do?
Options:
Conduct an audit to determine the frequency of occurrence
Update the probability in the risk register
Create a noncompliance risk scenario
Weigh compliance against the cost-benefit
Answer:
CExplanation:
This behavior representsintentional circumvention of control, requiring formal documentation and assessment as anoncompliance risk scenario.
CRISC principle:
“When control circumvention occurs, the risk practitioner should document the event as a noncompliance risk scenario to evaluate its impact and treatment.”
The other options—auditing, probability updates, or cost analysis—may follow, but the first step isformal recognitionof the risk within the risk register via a new scenario.
CRISC Reference:Domain 2 – IT Risk Assessment, Topic: Scenario Development and Control Evaluation.
Which of the following would require updates to an organization ' s IT risk register?
Options:
Discovery of an ineffectively designed key IT control
Management review of key risk indicators (KRls)
Changes to the team responsible for maintaining the register
Completion of the latest internal audit
Answer:
AExplanation:
An IT risk register is a document that records and tracks the identified IT risks, their likelihood, impact, and mitigation strategies. It is a living document that needs to be updated regularly to reflect the current risk profile of the organization. One of the situations that would require updates to the IT risk register is the discovery of an ineffectively designed key IT control, as this would increase the likelihood or impact of the related IT risk. Management review of key risk indicators (KRIs), changes to the team responsible for maintaining the register, and completion of the latest internal audit are not reasons to update the IT risk register, as they do not affect the identified IT risks or their mitigation strategies. References = [CRISC Review Manual (DigitalVersion)], page 97; CRISC: Certified in Risk & Information Systems Control Sample Questions, question 198.
Which of the following will MOST likely change as a result of the decrease in risk appetite due to a new privacy regulation?
Options:
Key risk indicator (KRI) thresholds
Risk trends
Key performance indicators (KPIs)
Risk objectives
Answer:
AExplanation:
KRI thresholds are the levels or points that trigger an action or a response when a KRI reaches or exceeds them. They reflect the risk appetite of the organization, which is the amount and type of risk that it is willing to accept in pursuit of its objectives. A new privacy regulation may reduce the risk appetite of the organization, as it may impose stricter requirements and penalties for non-compliance. Therefore, the organization may need to adjust its KRI thresholds to lower levels, to ensure that it can identify and manage privacy risks more effectively and proactively
Which of the following is the PRIMARY benefit of integrating risk and security requirements in an organization ' s enterprise architecture (EA)?
Options:
Adherence to legal and compliance requirements
Reduction in the number of test cases in the acceptance phase
Establishment of digital forensic architectures
Consistent management of information assets
Answer:
DExplanation:
Integrating risk and security requirements in an organization’s enterprise architecture (EA) helps to ensure that information assets are consistently managed throughout their life cycle, and that the risks associated with them are identified and mitigated. (Risk and Information Systems Control Review Questions, Answers & Explanations Manual, 5th Edition, page 112)
A risk practitioner is developing a set of bottom-up IT risk scenarios. The MOST important time to involve business stakeholders is when:
Options:
updating the risk register.
validating the risk scenarios.
documenting the risk scenarios.
identifying risk mitigation controls.
Answer:
BExplanation:
According to the CRISC Review Manual, the most important time to involve business stakeholders in the development of bottom-up IT risk scenarios is when validating the risk scenarios, as they can provide valuable input on the relevance, completeness, and accuracy of the scenarios and their impact on the business objectives and processes2
1: CRISC Review Questions, Answers & Explanations Database, Question ID: 100001 2: CRISC Review Manual, 7th Edition, page 97
Which of the following is a KEY responsibility of the second line of defense?
Options:
Implementing control activities
Monitoring control effectiveness
Conducting control self-assessments
Owning risk scenarios
Answer:
BExplanation:
The second line of defense is a group of functions that provide oversight, guidance, and monitoring of the risk management activities of the first line of defense. The second line of defense includes risk management, compliance, and internal control departments. Their key responsibility is to monitor the effectiveness of the control activities implemented by the first line of defense, and to report any issues or gaps to senior management and the board. The second line of defense also supports the first line of defense by providing frameworks, policies, tools,and techniques to identify, measure, and manage risks. The other options are not the key responsibility of the second line of defense, as explained below:
A. Implementing control activities is the responsibility of the first line of defense, which consists of the business units and process owners that own and manage the risks associated with their daily operations.
C. Conducting control self-assessments is a technique used by the first line of defense to evaluate the design and operation of their own controls, and to identify and report any deficiencies or improvement opportunities.
D. Owning risk scenarios is the responsibility of the first line of defense, which is accountable for the risks inherent in their business activities, and for developing and executing risk response strategies. References = Modernizing The Three Lines of Defense Model | Deloitte US, The second line of defence: fit for purpose, not an uncomfortable fit | Knowledge | Linklaters, COSO’s Take on the Three Lines of Defense | ERM - Enterprise Risk Management, Three Lines of Defense | Risk Management - Schneider Downs CPAs, What is the Three Lines of Defense Approach to Risk Management?
After undertaking a risk assessment of a production system, the MOST appropriate action is fcr the risk manager to
Options:
recommend a program that minimizes the concerns of that production system.
inform the process owner of the concerns and propose measures to reduce them.
inform the IT manager of the concerns and propose measures to reduce them.
inform the development team of the concerns and together formulate risk reduction measures.
Answer:
BExplanation:
The most appropriate action for the risk manager to take after undertaking a risk assessment of a production system is to inform the process owner of the concerns and propose measures to reduce them, as the process owner has the authority and responsibility to manage the production system and its associated risks and controls, and to decide on the optimal risk response. Recommending a program that minimizes the concerns of that production system, informing the IT manager of the concerns and proposing measures to reduce them, and informing the development team of the concerns and together formulating risk reduction measures are not the most appropriate actions, as they may not involve the process owner, who is the key stakeholder and decision maker for the production system and its risks. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following BEST facilitates the process of documenting risk tolerance?
Options:
Creating a risk register
Interviewing management
Conducting a risk assessment
Researching industry standards
Answer:
BExplanation:
Interviewing managementis key because risk tolerance reflects leadership’s perspective on acceptable risk levels. ISACA stresses that understanding risk tolerance requires direct input from those responsible for risk decisions and strategic direction.
An unauthorized individual has socially engineered entry into an organization ' s secured physical premises. Which of the following is the BEST way to prevent future occurrences?
Options:
Employ security guards.
Conduct security awareness training.
Install security cameras.
Require security access badges.
Answer:
BExplanation:
Social engineering is a technique that involves manipulating or deceiving people into performing actions or divulging information that may compromise the security of an organization or its data12.
Entry into an organization’s secured physical premises is a form of physical access that allows an unauthorized individual to access, steal, or damage the organization’s assets, such as equipment, documents, or systems34.
The best way to prevent future occurrences of social engineering entry into an organization’s secured physical premises is to conduct security awareness training, which is an educational program that aims to equip the organization’s employees with the knowledge and skills they need to protect the organization’s data and sensitive information from cyber threats, such as hacking, phishing, or other breaches56.
Security awareness training is the best way because it helps the employees to recognize and resist the common and emerging social engineering techniques, such as tailgating,impersonation, or pretexting, that may be used by the attackers to gain physical access to the organization’s premises56.
Security awareness training is also the best way because it fosters a culture of security and responsibility among the employees, and encourages them to follow the best practices andpolicies for physical security, such as locking the doors, verifying the identity of visitors, or reporting any suspicious activities or incidents56.
The other options are not the best way, but rather possible measures or controls that may supplement or enhance the security awareness training. For example:
Employing security guards is a measure that involves hiring or contracting professional personnel who are trained and authorized to monitor, patrol, and protect the organization’s premises from unauthorized access or intrusion78. However, this measure is not the best way because it may not be sufficient or effective to prevent or deter all types of social engineering attacks, especially if the attackers are able to bypass, deceive, or coerce the security guards78.
Installing security cameras is a control that involves using electronic devices that capture and record the visual images of the organization’s premises, and provide evidence or alerts of any unauthorized access or activity . However, this control is not the best way because it is reactive rather than proactive, and may not prevent or stop the social engineering attacks before they cause any harm or damage to the organization .
Requiring security access badges is a control that involves using physical or electronic cards that identify and authenticate the employees or authorized visitors who are allowed to enter the organization’s premises, and restrict or deny the access to anyone else . However, this control is not the best way because it may not be foolproof or reliable to prevent or detect the social engineering attacks, especially if the attackers are able to steal, forge, or clone the security access badges . References =
1: What is Social Engineering? | Types & Examples of Social Engineering Attacks1
2: Social Engineering: What It Is and How to Prevent It | Digital Guardian2
3: What is physical Social Engineering and why is it important? - Integrity3603
4: What Is Tailgating (Piggybacking) In Cyber Security? - Wlan Labs4
5: What Is Security Awareness Training and Why Is It Important? - Kaspersky5
6: Security Awareness Training - Cybersecurity Education Online | Proofpoint US6
7: Security Guard - Wikipedia7
8: Security Guard Services - Allied Universal8
Security Camera - Wikipedia
Security Camera Systems - The Home Depot
Access Badge - Wikipedia
Access Control Systems - HID Global
Which of the following is the PRIMARY purpose of a risk register?
Options:
It guides management in determining risk appetite.
It provides management with a risk inventory.
It aligns risk scenarios to business objectives.
It monitors the performance of risk and control owners.
Answer:
BWhen evaluating enterprise IT risk management it is MOST important to:
Options:
create new control processes to reduce identified IT risk scenarios
confirm the organization’s risk appetite and tolerance
report identified IT risk scenarios to senior management
review alignment with the organization ' s investment plan
Answer:
BExplanation:
Enterprise IT risk management is the process of identifying, analyzing, evaluating, and treating the IT-related risks that may affect the organization’s objectives, operations, or assets1. Enterprise IT risk management should be aligned with the organization’s overall riskmanagement framework and strategy, and support the organization’s value creation and protection2.
When evaluating enterprise IT risk management, it is most important to confirm the organization’s risk appetite and tolerance. Risk appetite is the amount and type of risk that an organization is willing to take in order to meet its strategic objectives3. Risk tolerance is the acceptable level of variation that an organization is willing to accept around its risk appetite4. By confirming the organization’s risk appetite and tolerance, the evaluation can:
Ensure that the enterprise IT risk management is consistent and compatible with the organization’s risk culture and vision
Provide clear and measurable criteria and boundaries for assessing and prioritizing the IT risks and their impacts
Guide the selection and implementation of the appropriate risk responses and controls that balance the costs and benefits of risk mitigation
Enable the monitoring and reporting of the IT risk performance and outcomes, and the adjustment of the IT risk strategy and objectives as needed5
References = Enterprise IT Risk Management - ISACA, Enterprise Risk Management - Wikipedia, Risk Appetite - COSO, Risk Tolerance - COSO, Risk Appetite and Tolerance - IRM
Which of the following is the GREATEST risk to an organization when using a public AI system to process credit card transactions?
Options:
Potential exposure of sensitive information
Use of financial data to train the AI model
Noncompliance with security standards
AI hallucinations and bias
Answer:
AExplanation:
The correct answer isAbecause the greatest risk when using apublic AI systemto process credit card transactions is thepotential exposure of sensitive information. Credit card data is highly sensitive, and use of a public AI platform can introduce serious confidentiality, privacy, and data handling concerns. Exposure of that data can lead to fraud, regulatory issues, contractual violations, and significant business impact.
The other options are important, but not the greatest primary risk:
B. Use of financial data to train the AI modelis a specific form of data misuse, but it falls within the broader and more critical risk of sensitive information exposure.
C. Noncompliance with security standardsis also significant, but it is often a consequence of exposing or improperly handling sensitive payment data.
D. AI hallucinations and biasare important AI risks, but they are not the primary concern in payment card processing.
Exact Extracts supporting the answer:
“The MOST important consideration when transmitting personal information across networks is ensuring the privacy of the personal information.”
“The data security control that BEST protects the confidentiality of data stored on backup media in transit to a third-party storage facility is encryption.”
“The MOST significant risk associated with handling credit card data through a web application is failure to store credit card data in a secure area segregated from the demilitarized zone.”
“To determine the level of protection required for securing personally identifiable information a risk practitioner should PRIMARILY consider the sensitivity property of the information.”
These extracts support that the primary concern with payment-card-related processing is protecting the confidentiality of sensitive data. Therefore, the greatest risk is thepotential exposure of sensitive information.
===========
Which of the following is the MOST important document regarding the treatment of sensitive data?
Options:
Encryption policy
Organization risk profile
Digital rights management policy
Information classification policy
Answer:
DExplanation:
The information classification policy is the most important document regarding the treatment of sensitive data, because it defines the categories and criteria for classifying data according to their sensitivity, confidentiality, and value to the organization, and specifies the appropriate handling and protection measures for each category. Sensitive data are data that contain personal,proprietary, or confidential information that may cause harm or damage to the organization or its stakeholders if disclosed, modified, or destroyed without authorization. An information classification policy helps to ensure that sensitive data are identified and treated in a consistent and secure manner, and that the organization complies with the applicable laws andregulations regarding data protection and privacy. An encryption policy, an organization risk profile, and a digital rights management policy are all useful documents for the treatment of sensitive data, but they are not the most important document, as they do not directly address the classification and handling of sensitive data. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2, page 158
Which of the following is the BEST way for an organization to enable risk treatment decisions?
Options:
Allocate sufficient funds for risk remediation.
Promote risk and security awareness.
Establish clear accountability for risk.
Develop comprehensive policies and standards.
Answer:
CExplanation:
Establishing clear accountability for risk is the best way for an organization to enable risk treatment decisions, as it ensures that the risk owners and stakeholders have the authority and responsibility to manage and mitigate the risks that they are assigned to. Establishing clear accountability for risk also facilitates communication and collaboration among the risk owners and stakeholders, and enables them to monitor and report the risk status and performance. Establishing clear accountability for risk also supports the risk governance and culture of the organization, and aligns the risk management process with the organization’s strategy and objectives. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 250. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 250. CRISC Sample Questions 2024, Question 250. CRISC by Isaca Actual Free Exam Q & As, Question 9.
During an IT risk scenario review session, business executives question why they have been assigned ownership of IT-related risk scenarios. They feel IT risk is technical in nature and therefore should be owned by IT. Which of the following is the BEST way for the risk practitioner to address these concerns?
Options:
Describe IT risk scenarios in terms of business risk.
Recommend the formation of an executive risk council to oversee IT risk.
Provide an estimate of IT system downtime if IT risk materializes.
Educate business executives on IT risk concepts.
Answer:
AExplanation:
IT risk scenarios are hypothetical situations or occurrences that illustrate the potential impact of IT-related threats or opportunities on the organization’s objectives, performance, or value creation12.
Business risk scenarios are hypothetical situations or occurrences that illustrate the potential impact of business-related threats or opportunities on the organization’s objectives, performance, or value creation34.
The best way for the risk practitioner to address the concerns of the business executives who question why they have been assigned ownership of IT-related risk scenarios is to describe IT risk scenarios in terms of business risk, which is a technique that involves translating and communicating the IT risk scenarios into the language and context of the business risk scenarios, and highlighting the linkages and dependencies between them56.
Describing IT risk scenarios in terms of business risk is the best way because it helps the business executives to understand and appreciate the relevance and importance of IT risk scenarios, andhow they affect the achievement of the organization’s goals and the delivery of value to the stakeholders56.
Describing IT risk scenarios in terms of business risk is also the best way because it helps the business executives to accept and fulfill their roles and responsibilities as the owners of IT risk scenarios, and to collaborate and coordinate with the IT team and other stakeholders in the risk management process56.
The other options are not the best ways, but rather possible alternatives or supplements that may support or enhance the description of IT risk scenarios in terms of business risk. For example:
Recommending the formation of an executive risk council to oversee IT risk is a way that involves establishing and empowering a group of senior leaders from different business units and functions to provide the strategic direction, guidance, and oversight for the IT risk managementprocess78. However, this way is not the best way because it does not directlyaddress the concerns of the business executives who question why they have been assigned ownership of IT risk scenarios, and it may not be feasible or effective without a clear and common understanding of IT risk scenarios among the council members78.
Providing an estimate of IT system downtime if IT risk materializes is a way that involves quantifying and communicating the potential loss or disruption of the IT systems or services that support the organization’s operations, if the IT risk scenarios occur9 . However, this way is not the best way because it does not fully capture or convey the impact of IT risk scenarios on the organization’s objectives, performance, or valuecreation, and it may not be relevant or meaningful for some IT risk scenarios that are not related to IT system downtime9 .
Educating business executives on IT risk concepts is a way that involves providing and delivering the knowledge and skills on the principles, frameworks, and techniques of IT risk management, and the roles and responsibilities of the IT risk owners and stakeholders . However, this way is not the best way because it does not specifically address the concerns of the business executives who question why they have been assigned ownership of IT risk scenarios, and it may not be sufficient or effective without a practical and contextual application of IT risk concepts to the organization’s situation and goals . References =
1: IT Scenario Analysis in Enterprise Risk Management - ISACA2
2: New Toolkit and Course From ISACA Help Practitioners Develop Risk Scenarios - ISACA1
3: Business Risk - Investopedia3
4: Business Risk: Definition, Types, Examples & How to Manage4
5: Risk IT Framework, ISACA, 2009
6: IT Risk Management Framework, University of Toronto, 2017
7: Executive Risk Council - ISACA5
8: Executive Risk Council: A Guide to Success6
9: IT System Downtime - ISACA7
IT System Downtime: Causes, Costs, and How to Prevent It8
IT Risk Education - ISACA9
IT Risk Education: A Guide to Success
Which of the following groups represents the first line of defense?
Options:
Internal audit
Compliance committee
External audit
Operational managers
Answer:
DExplanation:
Thefirst line of defenseincludesbusiness and operational managerswho own and manage risks directly. They implement controls as part of their day-to-day duties, making them the first to respond to risk.
Which of the following is the BEST way to detect zero-day malware on an end user ' s workstation?
Options:
An antivirus program
Database activity monitoring
Firewall log monitoring
File integrity monitoring
Answer:
DExplanation:
Zero-day malware is malware that exploits unknown and unprotected vulnerabilities. This novel malware is difficult to detect and defend against, making zero-day attacks a significant threat to enterprise cybersecurity1. The best way to detect zero-day malware on an end user’s workstation is to use file integrity monitoring, which is a technique that monitors and alerts on changes to files and directories that may indicate a malware infection or compromise2. By using fileintegrity monitoring, the end user can detect zero-day malware that may alter or damage the files or directories on their workstation, and take appropriate actions to remove or isolate the malware. File integrity monitoring can also help to prevent the spread of zero-day malware to other systems or networks, and to restore the integrity and availability of the affected files or directories. Antivirus program, database activity monitoring, and firewall log monitoring are not the best ways to detect zero-day malware on an end user’s workstation, as they are not as effective or reliable as file integrity monitoring. Antivirus program is a software that scans and removes known malware from a system or network3. Antivirus program can help to protect the end user’s workstation from common or known malware, but it may not be able to detect zero-day malware that does not have a signature or a pattern that matches the antivirus program’s database. Database activity monitoring is a technique that monitors and audits the activities and transactions on a database, such as queries, updates, or deletions4. Database activity monitoring can help to protect the end user’s database from unauthorized or malicious access or modification, but it may not be able to detect zero-day malware that does not target or affect the database. Firewall log monitoring is a technique that monitors and analyzes the logs generated by a firewall, which is a device or software that filters and controls the incoming and outgoing network traffic based on predefined rules. Firewall log monitoring can help to protect the enduser’s workstation from external or internal network attacks, but it may not be able to detect zero-day malwarethat bypasses or evades the firewall rules or that originates from the workstation itself. References = 1: What is Zero Day Malware? - Check Point Software2: File Integrity Monitoring - an overview | ScienceDirect Topics3: Antivirus Software - an overview | ScienceDirect Topics4: Database Activity Monitoring - an overview | ScienceDirect Topics : [Firewall Log Analysis - an overview | ScienceDirect Topics] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.1: Control Design, pp. 233-235.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.2: Control Implementation, pp. 243-245.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.3: Control Monitoring and Maintenance, pp. 251-253.] : [Zero-day attack detection: a systematic literature review | Artificial Intelligence Review] : [Zero-day Attacks Detection and Prevention Methods | Apriorit]
Which of the following observations from a third-party service provider review would be of GREATEST concern to a risk practitioner?
Options:
Service level agreements (SLAs) have not been met over the last quarter.
The service contract is up for renewal in less than thirty days.
Key third-party personnel have recently been replaced.
Monthly service charges are significantly higher than industry norms.
Answer:
AExplanation:
The observation from a third-party service provider review that would be of greatest concern to a risk practitioner is that the service level agreements (SLAs) have not been met over the last quarter, as it indicates a significant performance issue or breach that may affect the quality, functionality, or security of the outsourced services, and may require a remediation or escalation action. The other options are not the greatest concerns, as they may not indicate a performance issue or breach, but rather a contractual, personnel, or financial issue, respectively, that may not affect the outsourced services directly or significantly. References = CRISC Review Manual, 7th Edition, page 111.
After identifying new risk events during a project, the project manager s NEXT step should be to:
Options:
determine if the scenarios need 10 be accepted or responded to.
record the scenarios into the risk register.
continue with a qualitative risk analysis.
continue with a quantitative risk analysis.
Answer:
BExplanation:
After identifying new risk events during a project, the project manager’s next step should be to record the scenarios into the risk register, which is a document that records and tracks the identified risks, their causes, impacts, likelihood, responses, owners, and status. Recording the scenarios into the risk registerhelps to document and communicate the risks to the project team and stakeholders, and to facilitate the subsequent risk analysis and response processes. The other options are not the next steps, but rather the subsequent steps after recording the scenarios into the risk register. Determining if the scenarios need to be accepted or responded to is part of the risk evaluation and treatment process, which requires a prior risk analysis. Continuing with a qualitative or quantitative risk analysis is part of the risk assessment process, which requires a prior risk identification and documentation. References = Risk Register: A Project Manager’s Guide with Examples [2023] • Asana; Risk Identification in Project Management; 6.3. The 5 Steps of the Risk Management Process
Analyzing trends in key control indicators (KCIs) BEST enables a risk practitioner to proactively identify impacts on an organization ' s:
Options:
risk classification methods
risk-based capital allocation
risk portfolio
risk culture
Answer:
CExplanation:
A risk portfolio is a collection of risks that an organization faces or may face in the future. Analyzing trends in key control indicators (KCIs) best enables a risk practitioner to proactively identify impacts on an organization’s risk portfolio, as KCIs measure and monitor the performance and effectiveness of the risk controls that are implemented to mitigate the risks. By analyzing the trends in KCIs, a risk practitioner can assess the current and potential risk exposure of the organization, and identify any changes or emerging risks that may affect the risk portfolio. Analyzing trends in KCIs can also help to evaluate the cost and benefit of the risk controls, and to determine the need for enhancing, modifying, or implementing new controls. References = CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 246. Most Asked CRISC Exam Questions and Answers, Question 10. ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 246. CRISC by Isaca Actual Free Exam Q & As, Question 9.
An organization ' s stakeholders are unable to agree on appropriate risk responses. Which of the following would be the BEST course of action?
Options:
Escalate to senior management.
Identify a risk transfer option.
Reassess risk scenarios.
Benchmark with similar industries.
Answer:
AExplanation:
Escalating to senior management is the best course of action when an organization’s stakeholders are unable to agree on appropriate risk responses. This is because senior management has the authority and responsibility to make strategic decisions and resolve conflicts regarding risk management. Senior management can also provide guidance and direction on the risk appetite, tolerance, and criteria for the organization, as well as allocate resources and assign roles and responsibilities for risk response. According to the CRISC Review Manual 2022, one of the key risk response techniques is to escalate the risk to senior management when the risk exceeds the acceptable level or when there is a disagreement on the risk response1. According to the CRISC Review Questions, Answers & Explanations Manual 2022, escalating to senior management is the correct answer to this question2.
Identifying a risk transfer option, reassessing risk scenarios, and benchmarking with similar industries are not the best courses of action when an organization’s stakeholders are unable to agree on appropriate risk responses. These are possible actions that can be taken as part of the risk response process, but they do not address the underlying issue of stakeholder disagreement. Identifying a risk transfer option can help reduce or share the risk with a third party, such as an insurance company or a vendor, but it may not be suitable or acceptable for all types of risks or stakeholders. Reassessing risk scenarios can help update the risk analysis and evaluation, but it may not change the risk level or the risk response options. Benchmarking with similar industries can help compare the risk performance and practices of the organization with its peers, but it may not reflect the organization’s specific needs or risks.
Which of the following resources is MOST helpful when creating a manageable set of IT risk scenarios?
Options:
Results of current and past risk assessments
Organizational strategy and objectives
Lessons learned from materialized risk scenarios
Internal and external audit findings
Answer:
CExplanation:
According to the CRISC Review Manual1, lessons learned from materialized risk scenarios are the insights and knowledge gained from analyzing the causes, impacts, and responses of actual risk events that occurred in the past. Lessons learned from materialized risk scenarios are the most helpful resource when creating a manageable set of IT risk scenarios, as they help to identify and prioritize the most relevant and realistic risks that could affect the organization’s objectives, processes, and resources. Lessons learned from materialized risk scenarios also helpto improve the risk management practices and capabilities, and to avoid repeating the same mistakes or gaps in the future. References = CRISC Review Manual1, page 206.
A hospital recently implemented a new technology to allow virtual patient appointments. Which of the following should be the risk practitioner ' s FIRST course of action?
Options:
Reassess the risk profile.
Modify the risk taxonomy.
Increase the risk tolerance.
Review the risk culture.
Answer:
AExplanation:
Reassessing the risk profile is the first course of action that a risk practitioner should take after a hospital recently implemented a new technology to allow virtual patient appointments. This is because reassessing therisk profile can help identify, analyze, and evaluate the new or changed risks that the new technology may introduce or affect, such as data privacy, security, quality, reliability, or compliance risks. Reassessing the risk profile can also help determine the appropriate risk response and mitigation strategies, as well as monitor and report the risk performance and outcomes. According to the CRISC Review Manual 2022, reassessing the risk profile is one of the key steps in the IT risk management process1. According to the web search results, reassessing the risk profile is a common and recommended practice for addressing the risks of virtual patient appointments
Which of the following is the BEST course of action when risk is found to be above the acceptable risk appetite?
Options:
Review risk tolerance levels
Maintain the current controls.
Analyze the effectiveness of controls.
Execute the risk response plan
Answer:
DExplanation:
The best course of action when risk is found to be above the acceptable risk appetite is to execute the risk response plan, which is the set of actions and measures that are designed to reduce, avoid, transfer, or accept the risk. The risk response plan is based on the risk assessment results, the risk appetite and tolerance of the organization, and the cost-benefit analysis of the risk response options. The risk response plan helps to achieve the optimal balance between the potential benefits and threats of the risk, and to align the risk decisions with the organizationalobjectives and context. The other options are not the best courses of action, as they are either too passive or too reactive in dealing with the risk. Reviewing risk tolerance levels may help to adjust the acceptable variation between the risk thresholds and the business objectives, but itdoes not address the actual risk level or impact. Maintaining the current controls may help to prevent the risk from increasing further, but it does not reduce the existing risk exposure or mitigation. Analyzing the effectiveness of controls may help to identify the gaps or weaknesses in the current risk management, but it does not implement the necessary improvements or changes. References = Risk Response Plan in Project Management: Key Strategies & Tips; A Practitioner’s Guide to Ethical Decision Making; How to Manage Project Risk: A 5-Step Guide
An organization ' s chief information officer (CIO) has proposed investing in a new. untested technology to take advantage of being first to market Senior management has concerns about the success of the project and has set a limit for expenditures before final approval. This conditional approval indicates the organization ' s risk:
Options:
capacity.
appetite.
management capability.
treatment strategy.
Answer:
BExplanation:
The conditional approval of the CIO’s proposal indicates the organization’s risk appetite. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. By setting a limit for expenditures before final approval, senior management isexpressing their willingness to take a calculated risk with the new technology, but also their desire to control the potential loss or harm. Risk capacity, management capability, and treatment strategy are other possible factors, but they are not as relevant as risk appetite. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97
An organization has decided to implement an emerging technology and incorporate the new capabilities into its strategic business plan. Business operations for the technology will be outsourced. What will be the risk practitioner ' s PRIMARY role during the change?
Options:
Managing third-party risk
Developing risk scenarios
Managing the threat landscape
Updating risk appetite
Answer:
AExplanation:
The risk practitioner’s primary role during the change is to manage the third-party risk, as this involves identifying, assessing, and mitigating the risks associated with outsourcing the business operations for the emerging technology. The risk practitioner should ensure that the third-party provider has the necessary capabilities, security, and compliance to deliver the expected outcomes and meet the contractual obligations. The risk practitioner should also monitor the performance and service levels of the third-party provider and report any issues or incidents. Developing risk scenarios, managing the threat landscape, and updating risk appetite are all important activities for the risk practitioner, but they are not the primary role during the change. Developing risk scenarios is a technique for identifying and analyzing potential risk events and their impacts. Managing the threat landscape is a process of identifying and responding to the external and internal threats that may affect the organization. Updating risk appetite is a decision that reflects the organization’s willingness to accept or avoid risk in pursuit of its objectives. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 48.
During a data loss incident, which role in the RACI chart would be aligned to the risk practitioner?
Options:
Responsible
Accountable
Informed
Consulted
Answer:
DA multinational company needs to implement a new centralized security system. The risk practitioner has identified a conflict between the organization ' s data-handling policy and local privacy regulations. Which of the following would be the BEST recommendation?
Options:
Request a policy exception from senior management.
Comply with the organizational policy.
Report the noncompliance to the local regulatory agency.
Request an exception from the local regulatory agency.
Answer:
DThe PRIMARY goal of conducting a business impact analysis (BIA) as part of an overall continuity planning process is to:
Options:
obtain the support of executive management.
map the business processes to supporting IT and other corporate resources.
identify critical business processes and the degree of reliance on support services.
document the disaster recovery process.
Answer:
CExplanation:
The primary goal of conducting a business impact analysis (BIA) as part of an overall continuity planning process is to identify critical business processes and the degree of reliance on support services. A BIA is a process of assessing the potential impact and consequences of a disruption or interruption of the business activities, operations, or functions. A continuity planning processis a process of developing, implementing, and maintaining a plan to ensure the continuity and recovery of the business activities, operations, or functions in the event of a disruption or interruption. The primary goal of conducting a BIA is to identify critical business processes and the degree of reliance on support services, which are the business processes that are essential for the survival and success of the business, and the support services that are required to enable or facilitate the critical business processes, such as IT systems, human resources, facilities, or suppliers. Identifying critical business processes and the degree of reliance on support services helps to determine the priorities and requirements for the continuity and recovery of the business activities, operations, or functions, and to select and implement the appropriate continuity andrecovery strategies and solutions. Obtaining the support of executive management, mapping the business processes to supporting IT and other corporate resources, and documenting the disaster recovery process are not the primary goals of conducting a BIA, as they are either the benefits or the outputs of the BIA process, and they do not address the primary need of assessing the impact and consequences of the business disruption or interruption. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 50.
Which of the following provides the MOST important information to facilitate a risk response decision?
Options:
Audit findings
Risk appetite
Key risk indicators
Industry best practices
Answer:
BExplanation:
Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk appetite provides the most important information to facilitate a risk response decision, because it reflects the organization’s risk tolerance, preferences, and expectations, which guide the selection and implementation of the risk response strategies. Risk appetite helps the organization to balance the potential benefits and costs of taking risks, and to align the risk management process with the organizational strategy and culture. The other options are not as important as risk appetite, because they do not indicate the organization’s desired level of risk exposure, but rather provide supplementary or partial information for the risk response decision, as explained below:
A. Audit findings are the results and recommendations of the internal or external audit activities that evaluate the effectiveness and efficiency of the organization’s governance, risk management, and control processes. Audit findings provide useful information to facilitate a risk response decision, because they can identify the gaps or weaknesses in the current risk response strategies, and suggest corrective actions or improvements. However, audit findings do not indicate the organization’s risk appetite, which is the basis for determining the optimal risk response strategies.
C. Key risk indicators (KRIs) are metrics that measure the impact and likelihood of the risks, and provide early warning signs of changes in the risk exposure. KRIs provide useful information to facilitate a risk response decision, because they can monitor and report the performance and effectiveness of the current risk response strategies, and trigger corrective actions or adjustments.However, KRIs do not indicate the organization’s risk appetite, which is the basis for determining the acceptable level of risk exposure and performance.
D. Industry best practices are the standards, norms, and expectations for risk management that are established and followed by the peers or competitors in the same industry or sector. Industry best practices provide useful information to facilitate a risk response decision, because they can benchmark and compare the organization’s risk response strategies with those of the leading or successful organizations, and identify areas for improvement or innovation. However, industry best practices do not indicate the organization’s risk appetite, which is the basis for determining the unique and customized risk response strategies that suit the organization’s needs and goals. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.2, page 40. Risk Appetite: What It Is and How to Use It, Risk Appetite: How Hungry Are You?, Risk Appetite: The Strategic Balancing Act
Which of the following is the BEST way to promote adherence to the risk tolerance level set by management?
Options:
Defining expectations in the enterprise risk policy
Increasing organizational resources to mitigate risks
Communicating external audit results
Avoiding risks that could materialize into substantial losses
Answer:
AExplanation:
According to the Risk Appetite vs. Risk Tolerance: What is the Difference? article, risk tolerance is the acceptable level of variation that an organization is willing to accept around a specific objective. Risk tolerance is usually expressed as a range or a limit, and it helps to guide the decision making and risk taking of the organization. The best way to promote adherence to the risk tolerance level set by management is to define the expectations in the enterprise risk policy, which is a document that establishes the organization’s risk management framework, principles, and objectives. By defining the expectations in the enterprise risk policy, the organization can communicate the risk tolerance level to all the relevant stakeholders, and ensure that they understand and follow the risk management guidelines and standards. This can help to create aconsistent and coherent risk culture across the organization, and to avoid any deviations or violations of the risk tolerance level. References = Risk Appetite vs. Risk Tolerance: What is the Difference?
A risk practitioner is summarizing the results of a high-profile risk assessment sponsored by senior management. The BEST way to support risk-based decisions by senior management would be to:
Options:
map findings to objectives.
provide quantified detailed analysis
recommend risk tolerance thresholds.
quantify key risk indicators (KRls).
Answer:
AExplanation:
The best way to support risk-based decisions by senior management would be to map findings to objectives, because this would help them understand how the identified risks affect theachievement of the organization’s goals and priorities. Mapping findings to objectives would also help senior management evaluate the trade-offs between different risk responses and allocate resources accordingly. By linking risks to objectives, the risk practitioner can communicate the value and impact of risk management in a clear and relevant way. References = Risk IT Framework, ISACA, 2022, p. 17
Which of the following is MOST helpful in developing key risk indicator (KRl) thresholds?
Options:
Loss expectancy information
Control performance predictions
IT service level agreements (SLAs)
Remediation activity progress
Answer:
AExplanation:
Key risk indicator (KRI): A metric that measures the level of risk exposure or the likelihood of a risk event1.
KRI threshold: A predefined value or range that triggers an alert or action when the KRI reaches or exceeds it2.
Loss expectancy: The estimated amount of loss that an organization may incur due to a risk event3.
The most helpful thing in developing KRI thresholds is loss expectancy information. Loss expectancy information provides an estimate of the potential or expected impact of a risk event on the organization’s operations, reputation, or objectives. Loss expectancy information can help an organization to:
Quantify and prioritize the risks that pose the greatest threat to the organization
Determine the acceptable level of risk exposure or tolerance for each risk
Set the appropriate value or range for the KRI threshold that reflects the risk appetite and the risk mitigation strategy
Monitor and measure the performance and effectiveness of the risk management process and controls
Loss expectancy information can be derived from various sources, such as historical data, statistical analysis, expert judgment, or simulation models3.
The other options are not as helpful as loss expectancy information in developing KRI thresholds, because they do not directly address the potential or expected impact of a risk event.Control performance predictions, which are the forecasts or estimates of how well the risk management controls will perform in preventing, detecting, or mitigating risks, may help to evaluate the adequacy and efficiency of the risk management process and controls, but they do not provide a clear and quantifiable measure of the risk impact. IT service level agreements (SLAs), which are the contracts or agreements that define the quality and availability of IT services, may help to establish the standards and expectations for IT service delivery and performance, but they do not provide a comprehensive and current view of the risk exposure or likelihood. Remediation activity progress, which is the status or outcome of the actions taken to address and resolve a risk event, may help to monitor and report the effectiveness and compliance of the risk management process and controls, but it is usually done after the risk event has occurred and resolved, not before.
References = Key Risk Indicators: Definition, Examples, and Best Practices, KRI Framework for Operational Risk Management | Workiva, Loss Expectancy: Definition, Calculation, and Examples
Which of the following BEST measures the impact of business interruptions caused by an IT service outage?
Options:
Sustained financial loss
Cost of remediation efforts
Duration of service outage
Average time to recovery
Answer:
AExplanation:
The best measure of the impact of business interruptions caused by an IT service outage is the sustained financial loss. This is the amount of money that the enterprise loses due to the disruption of its normal operations, such as lost revenue, increased expenses, or reduced profits. Sustained financial loss reflects the extent and severity of the business interruption, and theeffect on the enterprise’s objectives and performance. Sustained financial loss also helps to determine the recovery objectives and priorities, and to justify the investment in risk mitigation and business continuity strategies. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.2.2, page 691
Which of the following is MOST important for management to consider when deciding whether to invest in an IT initiative that exceeds management ' s risk appetite?
Options:
Risk management budget
Risk management industry trends
Risk tolerance
Risk capacity
Answer:
CExplanation:
The most important factor for management to consider when deciding whether to invest in an IT initiative that exceeds management’s risk appetite is C. Risk tolerance1
According to the CRISC Review Manual, risk tolerance is the acceptable level of variation that management is willing to allow for any specific risk as the enterprise pursues its objectives. Risk tolerance reflects the degree of uncertainty that an organization is prepared to accept in relation to achieving its goals2
When an IT initiative exceeds management’s risk appetite, it means that the potential benefits of the initiative are outweighed by the potential negative consequences or losses that could result from the initiative. However, management may still decide to invest in the initiative if the level of uncertainty or variation is within the organization’s risk tolerance. For example, management may accept a higher level of risk for a strategic or innovative initiative that could provide a competitive advantage or a significant return on investment3
Which of the following is the BEST method to maintain a common view of IT risk within an organization?
Options:
Collecting data for IT risk assessment
Establishing and communicating the IT risk profile
Utilizing a balanced scorecard
Performing and publishing an IT risk analysis
Answer:
BExplanation:
The best method to maintain a common view of IT risk within an organization is to establish and communicate the IT risk profile. An IT risk profile is a document that summarizes the key IT risks that the organization faces or accepts, and their likelihood, impact, and priority. An IT risk profile helps to identify and prioritize the most critical or relevant IT risks, and to align them with the organization’s objectives, strategy, and risk appetite. Establishing and communicating the IT risk profile is the best method to maintain a common view of IT risk, because it helps to create a shared understanding and awareness of the IT risks among the organization’s stakeholders, such as the board, management, business units, and IT functions. Establishing andcommunicating the IT risk profile also helps to facilitate the IT risk decision-making and reporting processes, and to monitor and control the IT risk performance and improvement. Theother options are not the best method to maintain a common view of IT risk, although they may be part of or derived from the IT risk profile. Collecting data for IT risk assessment, utilizing a balanced scorecard, and performing and publishing an IT risk analysis are all activitiesthat can help to support or update the IT risk profile, but they are not the best method to maintain a common view of IT risk. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.3.1, page 1-15.
Which of the following situations presents the GREATEST challenge to creating a comprehensive IT risk profile of an organization?
Options:
Manual vulnerability scanning processes
Organizational reliance on third-party service providers
Inaccurate documentation of enterprise architecture (EA)
Risk-averse organizational risk appetite
Answer:
BThe MOST important reason for implementing change control procedures is to ensure:
Options:
only approved changes are implemented
timely evaluation of change events
an audit trail exists.
that emergency changes are logged.
Answer:
AExplanation:
According to the CRISC Review Manual, the most important reason for implementing change control procedures is to ensure that only approved changes are implemented, because it helps to prevent or minimize the risk of unauthorized or unintended changes that may affect the stability, security, or performance of the IT systems and processes. Change control procedures are the steps and activities that are followed to manage the initiation, review, approval, implementation, and verification of changes. Change control procedures also help to ensure that the changes are aligned with the business requirements and objectives, and that the changes are documented and communicated to the stakeholders. The other options are not the most important reason for implementing change control procedures, as they are related to other benefits or outcomes of the change control process. Timely evaluation of change events is the reason for implementing change management, which is the process of identifying, analyzing, and responding to the changes that may affect the IT systems and processes. An audit trail is the outcome of implementing change control procedures, as it provides a record of the changes and their impacts. Logging emergency changes is the exception of implementing change control procedures, as it allows for bypassing the normal approval process in case of urgent or critical changes. References = CRISC Review Manual, 7th Edition, Chapter 4, Section 4.2.1, page 177.
From a data protection and regulatory compliance perspective, which of the following is the MOST important reason for a global organization to use immutable backups?
Options:
Immutable backups can be used for data recovery testing.
Data contains time stamps that indicate when it was backed up.
Immutable backups enable effective disaster recovery response.
Data cannot be tampered with through the use of encryption capabilities
Answer:
DExplanation:
The correct answer isDbecause the most important reason for usingimmutable backupsfrom a data protection and regulatory compliance perspective is that the datacannot be tampered with. The key compliance value of immutability is preserving integrity and protecting records from unauthorized alteration or deletion. This is especially important when proving that protected data and retained records remain trustworthy.
The other options are less important in this context:
A. Immutable backups can be used for data recovery testingis beneficial, but not the main regulatory reason.
B. Data contains time stamps that indicate when it was backed upis useful information, but not the core compliance value.
C. Immutable backups enable effective disaster recovery responseis important operationally, but the question emphasizes data protection and regulatory compliance.
Exact Extracts supporting the answer:
“The BEST method that provides message integrity authentication of the sender ' s identity and nonrepudiation is digital signatures.”
“The MOST important consideration when transmitting personal information across networks is ensuring the privacy of the personal information.”
“The purpose of system certification is to demonstrate that security controls and processes are assessed for effectiveness.”
“The MOST important principle of data protection that a risk practitioner should advocate for is that data should be accurate.”
These extracts support that from a compliance and data protection perspective, preserving integrity and preventing tampering is the highest concern. Therefore,Dis the best answer.
===========
Winch of the following is the BEST evidence of an effective risk treatment plan?
Options:
The inherent risk is below the asset residual risk.
Remediation cost is below the asset business value
The risk tolerance threshold s above the asset residual
Remediation is completed within the asset recovery time objective (RTO)
Answer:
CExplanation:
The best evidence of an effective risk treatment plan is that the risk tolerance threshold is above the asset residual risk, because this means that the risk treatment plan has reduced the risk to a level that is acceptable to the enterprise. The risk tolerance threshold is the maximum amount of risk that the enterprise is willing to accept for a given asset or process. The asset residual risk is the remaining risk after applying the risk treatment plan. The risk treatment plan is effective if the asset residual risk is lower than or equal to the risk tolerance threshold. The other options are not the best evidence, although they may also be indicators of an effective risk treatment plan. The inherent risk being below the asset residual risk, the remediation cost being below the asset business value, and the remediation being completed within the asset recovery time objective (RTO) are examples of desirable or expected outcomes of the risk treatment plan, but they do not directly measure the effectiveness of the risk treatment plan. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
During a review of the asset life cycle process, a risk practitioner identified several unreturned and unencrypted laptops belonging to former employees. Which of the following is the GREATEST concern with this finding?
Options:
Insufficient laptops for existing employees
Abuse of leavers ' account privileges
Unauthorized access to organizational data
Financial cost of replacing the laptops
Answer:
CExplanation:
The greatest concern with finding unreturned and unencrypted laptops belonging to former employees is the risk of unauthorized access to organizational data. The laptops may containsensitive or confidential information that could be compromised if they fall into the wrong hands. This could result in data breaches, reputational damage, legal liabilities, or regulatory penalties for the organization. Therefore, it is important to have proper controls in place to ensure that the laptops are returned, wiped, or encrypted when the employees leave the organization.
Which of the following is the MOST important data source for monitoring key risk indicators (KRIs)?
Options:
Directives from legal and regulatory authorities
Audit reports from internal information systems audits
Automated logs collected from different systems
Trend analysis of external risk factors
Answer:
CExplanation:
Key risk indicators (KRIs) are metrics that help organizations monitor and evaluate the level of risk they are exposed to. They provide early warning signals of potential issues that could affect the achievement of organizational goals12.
The most important data source for monitoring KRIs is automated logs collected from different systems, which are records that capture and store the details and history of the transactions or activities that are performed by the organization’s processes, systems, or controls34.
Automated logs collected from different systems are the most important data source because they provide timely and accurate data and information on the performance and status of the organization’s operations, and enable the detection and reporting of any deviations, anomalies, or issues that may indicate a risk event34.
Automated logs collected from different systems are also the most important data source because they support the accountability and auditability of the organization’s operations, and facilitate the investigation and resolution of any risk event34.
The other options are not the most important data sources, but rather possible inputs or factors that may influence or affect the KRIs. For example:
Directives from legal and regulatory authorities are documents that provide the expectations and obligations of the external authorities or bodies that govern or oversee the organization’s activities and operations, such as laws, regulations, standards, or contracts5 . However, these documents are not the most important data source becausethey do not directly measure or monitor the level of risk exposure, but rather provide the criteria or framework for risk compliance5 .
Audit reports from internal information systems audits are documents that provide the findings and recommendations of the independent and objective assessment of the adequacy and effectiveness of the organization’s information systems, processes, and controls . However, these documents are not the most important data source because they do not directly measure or monitor the level of risk exposure, but rather provide the assurance or improvement for risk management .
Trend analysis of external risk factors is a technique that involves analyzing and forecasting the changes and impacts of the external factors that influence the organization’s operations, such as technology, competition, regulation, or customer behavior . However, this technique is not themost important data source because it does not directly measure or monitor the level of risk exposure, but rather provide the insight or prediction for risk identification . References =
1: Key Risk Indicators: A Practical Guide | SafetyCulture1
2: Key risk indicator - Wikipedia2
3: Database Activity Monitoring - Wikipedia3
4: Database Activity Monitoring (DAM) | Imperva4
5: Regulatory Compliance - Wikipedia5
Regulatory Compliance Management Software | MetricStream
IT Audit and Assurance Standards, ISACA, 2014
IT Audit and Assurance Guidelines, ISACA, 2014
Trend Analysis - Investopedia
Trend Analysis: A Definition and Examples
An organization has experienced a cyber-attack that exposed customer personally identifiable information (Pll) and caused extended outages of network services. Which of the following stakeholders are MOST important to include in the cyber response team to determine response actions?
Options:
Security control owners based on control failures
Cyber risk remediation plan owners
Risk owners based on risk impact
Enterprise risk management (ERM) team
Answer:
CExplanation:
Risk owners based on risk impact are the most important stakeholders to include in the cyber response team, as they are responsible for the business outcomes affected by the cyber attack and can decide on the appropriate response actions. The other options are not the most important stakeholders to include in the cyber response team, although they may be involved in the process.
Which of the following enterprise architecture (EA) controls BEST mitigates the risk of increasingly complex systems becoming compromised by unauthorized network access?
Options:
Requirements to change default settings on network devices
Continuous network vulnerability scanning and remediation
Complex password policy and procedures
Continuous access verification and authentication
Answer:
DWhich of the following would BEST prevent an unscheduled application of a patch?
Options:
Network-based access controls
Compensating controls
Segregation of duties
Change management
Answer:
DExplanation:
Change management is the best way to prevent an unscheduled application of a patch, because it ensures that any changes to the IT environment are planned, approved, tested, and documented. Change management is a process that controls the implementation of changes to IT systems, applications, infrastructure, or processes. It aims to minimize the risk of disruption, errors, or failures caused by changes. Applying a patch is a type of change that may affect the security, functionality, or performance of an IT system or application. Therefore, applying a patch shouldfollow the change management process and schedule, and avoid any unscheduled or unauthorized patching. Network-based access controls, compensating controls, and segregation of duties are all useful controls to protect the IT environment from unauthorized or malicious access, but they do not prevent an unscheduled application of a patch, as they do not address the change management process. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.4.2, page 211
Which of the following is the PRIMARY responsibility of a control owner?
Options:
To make risk-based decisions and own losses
To ensure implemented controls mitigate risk
To approve deviations from controls
To design controls that will eliminate risk
Answer:
BExplanation:
A control owner ' s primary responsibility is to ensure that the controls under their purview are effectively implemented and functioning as intended to mitigate associated risks. This involves regular monitoring, evaluation, and reporting on the performance of controls to maintain the organization ' s risk posture within acceptable limits.
Which of the following practices MOST effectively safeguards the processing of personal data?
Options:
Personal data attributed to a specific data subject is tokenized.
Data protection impact assessments are performed on a regular basis.
Personal data certifications are performed to prevent excessive data collection.
Data retention guidelines are documented, established, and enforced.
Answer:
AExplanation:
Personal data is any information that relates to an identified or identifiable individual, such as name, address, email, phone number, etc. Processing personal data involves collecting, storing, using, disclosing, or deleting it. Processing personal data poses various risks to the privacy and security of the data subjects,such as unauthorized access, disclosure, modification, or loss. Therefore, processing personal data requires appropriate technical and organizational measures to safeguard the data and to comply with the relevant laws and regulations. One of the most effective practices to safeguard the processing of personal data is to use tokenization. Tokenization is a technique that replaces sensitive data elements with non-sensitive equivalents, called tokens, that have no meaning or value outside of a specific system or context. Tokenization reduces the risk of exposing personal data to unauthorized parties, as the tokens cannot be reversed or linked back to the original data without the proper key or algorithm. Tokenization also helps to minimize the amount of personal data that is stored or transmitted, and to limit the scope of compliance requirements. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2.2, p. 196-197
Which of the following BEST facilitates the identification of appropriate key performance indicators (KPIs) for a risk management program?
Options:
Reviewing control objectives
Aligning with industry best practices
Consulting risk owners
Evaluating KPIs in accordance with risk appetite
Answer:
DExplanation:
The best way to facilitate the identification of appropriate key performance indicators (KPIs) for a risk management program is to evaluate KPIs in accordance with risk appetite. KPIs are metrics that measure the performance and effectiveness of the risk management program, and help monitor and report on the achievement of the risk objectives and outcomes. Risk appetite is the amount and type of risk that the organization is willing to accept or pursue in order to achieve its objectives. Evaluating KPIs in accordance with risk appetite helps to identify the appropriate KPIs, because it helps to align the KPIs with the organization’s mission, vision, values, and strategy, and to ensure that the KPIs reflect the organization’s risk tolerance and threshold. Evaluating KPIs in accordance with risk appetite also helps to communicate and coordinate the KPIs with the organization’s stakeholders, such as the board, management, and business units, and to facilitate the risk decision-making and reporting processes. The other options are not as effective as evaluating KPIs in accordance with risk appetite, although they may be part of or derived from the KPI identification process. Reviewing control objectives, aligning with industry best practices, and consulting risk owners are all activities that can help to define or refine the KPIs, but they are not the best way to facilitate the identification of appropriate KPIs. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.5.1, page 4-38.
Which key performance efficiency IKPI) BEST measures the effectiveness of an organization ' s disaster recovery program?
Options:
Number of service level agreement (SLA) violations
Percentage of recovery issues identified during the exercise
Number of total systems recovered within tie recovery point objective (RPO)
Percentage of critical systems recovered within tie recovery time objective (RTO)
Answer:
DExplanation:
The key performance indicator (KPI) that best measures the effectiveness of an organization’s disaster recovery program is the percentage of critical systems recovered within the recovery time objective (RTO). The RTO is the acceptable timeframe within which a business process or system must be restored after a disruption. The percentage of critical systems recovered within the RTO indicates how well the disaster recovery program can meet the business continuity requirements and minimize the impact of the disruption. The other options are not as good as the percentage of critical systems recovered within the RTO, as they are related to the efficiency, quality, or scope of the disaster recovery program, not the effectiveness of the disaster recovery program. References = Risk and Information Systems Control StudyManual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Key Performance Indicators, page 183.
Which of the following is the MOST useful information for prioritizing risk mitigation?
Options:
Cost of risk mitigation
Asset criticality
Acceptable risk level
Business impact assessment
Answer:
DExplanation:
Business Impact Assessment (BIA):
BIA identifies and evaluates the potential effects of interruptions to critical business operations. It helps determine the priority of risk mitigation efforts based on the potential impact on business functions.
BIA provides detailed information on which processes and systems are most critical to the organization ' s operations and their respective impact levels.
Prioritizing Risk Mitigation:
The results of a BIA guide decision-makers in prioritizing which risks to address first based on their potential to disrupt critical business operations.
Risks that could cause significant operational, financial, or reputational damage are prioritized higher.
Comparing Other Factors:
Cost of Risk Mitigation:Important but secondary to understanding the impact on business operations.
Asset Criticality:Relevant but typically part of the BIA process.
Acceptable Risk Level:Defines the threshold but does not prioritize specific risks.
References:
The CRISC Review Manual discusses how BIA facilitates risk prioritization by identifying critical processes and their impacts (CRISC Review Manual, Chapter 2: IT Risk Assessment, Section 2.7 Business Impact Analysis).
The risk associated with a high-risk vulnerability in an application is owned by the:
Options:
security department.
business unit
vendor.
IT department.
Answer:
BExplanation:
A high-risk vulnerability in an application is a system flaw or weakness in the application’s code that can be exploited by a malicious actor, potentially leading to a security breach. The risk associated with a high-risk vulnerability in an application is the possibility and impact of such a breach occurring. The risk owner of a high-risk vulnerability in an application is the person or entity who has the authority and responsibility for managing the risk. The risk owner should be able to define the risk appetite, assess the risk level, select and implement the risk response, monitor and report the risk status, and ensure the risk alignment with the business objectives and strategy. The risk owner of a high-risk vulnerability in an application is the business unit, which is the organizational unit that operates the application and derives value from it. The businessunit understands the business needs and expectations of the application, and the potential consequences of a security breach. The business unit also has the resources and incentives to address the risk effectively and efficiently. Therefore, the business unit is the most appropriate risk owner of a high-risk vulnerability in an application. References = Why Assigning a Risk Owner is Important and How to Do It Right, CRISC 351-400 topic3, Foundations of Project Management : Week 2.
Which of the following BEST facilitates the mitigation of identified gaps between current and desired risk environment states?
Options:
Develop a risk treatment plan.
Validate organizational risk appetite.
Review results of prior risk assessments.
Include the current and desired states in the risk register.
Answer:
AExplanation:
Developing a risk treatment plan is the best way to facilitate the mitigation of identified gaps between current and desired risk environment states. A risk treatment plan is a document that outlines the actions and resources needed to implement the chosen risk response strategy for each risk scenario. A risk treatment plan should include the following elements:
Risk scenario description and risk ID
Risk owner and other stakeholders
Risk response strategy and objectives
Risk response actions and tasks
Resources, costs, and benefits
Roles and responsibilities
Timeline and milestones
Performance indicators and monitoring mechanisms
Contingency plans and triggers
A risk treatment plan helps to close the gaps between the current and desired risk environment states by providing a clear and comprehensive roadmap for risk mitigation. It also helps to ensure that the risk response actions are aligned with the organizational risk appetite, objectives, and priorities. A risk treatment plan also facilitates the communication, coordination, and collaboration among the risk owners and other stakeholders involved in the risk mitigation process.
The other options are not the best ways to facilitate the mitigation of identified gaps between current and desired risk environment states. Validating organizational risk appetite is an important step in establishing the risk criteria and thresholds for the risk assessment process, but it does not directly address the gaps between the current and desired risk environment states. Reviewing results of prior risk assessments can provide useful insights and lessons learned for the current risk assessment process, but it does not necessarily lead to the development and implementation of effective risk response actions. Including the current and desired states in the risk register can help to document and monitor the risk scenarios and their status, but it does not provide the details and guidance for risk mitigation. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4: Risk Response, Section 4.2: Risk Treatment, p. 189-191.
Which of the following conditions presents the GREATEST risk to an application?
Options:
Application controls are manual.
Application development is outsourced.
Source code is escrowed.
Developers have access to production environment.
Answer:
DExplanation:
The production environment is the environment where the application is deployed and used by the end users. The production environment should be protected from unauthorized or unintended changes that could compromise the availability, integrity, or confidentiality of the application and its data. Developers have access to the production environment presents the greatest risk to an application, as it could allow them tobypass the change management process, introduce errors or vulnerabilities, or manipulate the application or its data for malicious purposes. The other options are not as risky as developers having access to the production environment, as they involve different aspects of the application lifecycle:
Application controls are manual means that the application relies on human intervention to perform some functions or validations, such as data entry, reconciliation, or authorization. This could increase the risk of human error, fraud, or inefficiency, but it does not directly affect the production environment.
Application development is outsourced means that the application is developed by a third party, such as a vendor or a contractor. This could increase the risk of quality issues, contractual disputes, or intellectual property rights, but it does not directly affect the production environment.
Source code is escrowed means that the source code of the application is deposited with a trusted third party, such as a lawyer or a bank. This could provide assurance and continuity in case the original developer is unable or unwilling to maintain or support the application, but it does not directly affect the production environment. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.1.1.1, pp. 144-145.
Which of the following is the PRIMARY reason for sharing risk assessment reports with senior stakeholders?
Options:
To support decision-making for risk response
To hold risk owners accountable for risk action plans
To secure resourcing for risk treatment efforts
To enable senior management to compile a risk profile
Answer:
AExplanation:
The primary reason for sharing risk assessment reports with senior stakeholders is to support decision-making for risk response. Risk assessment reports are documents that summarize the results of the risk assessment process, such as the risk sources, causes, impacts, likelihood, and levels. Risk assessment reports also provide recommendations for risk response options, such as avoiding, reducing, transferring, or accepting the risk. Sharing risk assessment reports with senior stakeholders helps to inform them of the current risk situation, and to solicit their input, feedback, or approval for the risk response actions. The other options are not the primary reason for sharing risk assessment reports, although they may be secondary reasons or outcomes. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 4-13.
Which of the following should be a risk practitioner ' s GREATEST concern upon learning of failures in a data migration activity?
Options:
Availability of test data
Integrity of data
Cost overruns
System performance
Answer:
BExplanation:
The integrity of data should be the greatest concern for a risk practitioner upon learning of failures in a data migration activity, because it affects the accuracy, completeness, and consistency of the data that are transferred from one system or format to another. Data integrity is a property of data that ensures that the data are valid, reliable, and trustworthy, and that they have not been altered or corrupted by unauthorized or accidental means. Data migration is a process of moving or copying data from one system or format to another, usually as part of a system upgrade, consolidation, or transformation. Data migration can pose risks to the integrity of data, such as data loss, duplication, inconsistency, or corruption, due to factors such as incompatible formats, human errors, technical glitches, or malicious attacks. Therefore, the integrity of data should be the greatest concern, as it impacts the quality and usability of the data, and the performance and functionality of the system. The availability of test data, the cost overruns, and the system performance are all possible concerns for a risk practitioner, but they are not the greatest concern, as they do not directly affect the integrity of data. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.2, page 158
Which of the following is the BEST recommendation to senior management when the results of a risk and control assessment indicate a risk scenario can only be partially mitigated?
Options:
Implement controls to bring the risk to a level within appetite and accept the residual risk.
Implement a key performance indicator (KPI) to monitor the existing control performance.
Accept the residual risk in its entirety and obtain executive management approval.
Separate the risk into multiple components and avoid the risk components that cannot be mitigated.
Answer:
AExplanation:
Implementing controls to bring the risk to a level within appetite and accept the residual risk is the best recommendation to senior management when the results of a risk and control assessment indicate a risk scenario can only be partially mitigated, as it helps to balance the costs and benefits of the risk management and control processes, and to align them with the organizational strategy and objectives. A risk and control assessment is a process of identifying, analyzing, and evaluating the risks and controls associated with a specific activity, process, or objective. A risk scenario is a description of a possible event or situation that could cause harm or loss to the organization or its stakeholders. A risk scenario can only be partially mitigated when the existing or proposed controls are not sufficient or effective to reduce the risk to an acceptable level. A risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. A residual risk is the risk that remains after the implementation of controls or risk treatments.
Implementing controls to bring the risk to a level within appetite and accept the residual risk helps to provide the following benefits:
It enables a data-driven and evidence-based approach to risk management and reporting, rather than relying on subjective or qualitative judgments.
It facilitates a consistent and standardized way of measuring and communicating risk levels and exposure across the organization and to the external stakeholders.
It supports the development and implementation of effective and efficient risk response and mitigation strategies and actions that are aligned with the business risk appetite and objectives.
It provides feedback and learning opportunities for the risk management and control processes, and helps to foster a culture of continuous improvement and innovation.
The other options are not the best recommendations to senior management when the results of a risk and control assessment indicate a risk scenario can only be partially mitigated. Implementing a key performance indicator (KPI) to monitor the existing control performance is a useful method to measure and monitor the effectiveness and efficiency of the controls, but it does not address the residual risk or the risk appetite. Accepting the residual risk in its entirety andobtaining executive management approval is a possible option to deal with the risk scenario, but it may expose the organization to excessive or unacceptable risk, and it may not comply with the legal or regulatory obligations or requirements. Separating the risk into multiple components and avoiding the risk components that cannot be mitigated is a possible option to deal with the risk scenario, but it may not be feasible or practical, and it may create new or additional risks or challenges. References = Risk and Control Self-Assessment (RCSA) - Management Study Guide, IT Risk Resources | ISACA, Risk Mitigation: What It Is and How to Implement It (Free Templates …
A risk practitioner notes control design changes when comparing risk response to a previously approved action plan. Which of the following is MOST important for the practitioner to confirm?
Options:
Appropriate approvals for the control changes
The reason the action plan was modified
The risk owner ' s approval of the revised action plan
The effectiveness of the resulting control
Answer:
AExplanation:
The MOST important aspect for the risk practitioner to confirm is:
A. Appropriate approvals for the control changes
Ensuring that the control design changes have the appropriate approvals is crucial. This confirms that the changes are recognized and sanctioned by the necessary authority within the organization, aligning with governance practices and maintaining the integrity of the risk management process.
Which of the following is the BEST way to quantify the likelihood of risk materialization?
Options:
Balanced scorecard
Threat and vulnerability assessment
Compliance assessments
Business impact analysis (BIA)
Answer:
BExplanation:
A threat and vulnerability assessment is a process that identifies and evaluates the potential sources and impacts of risk events on an organization’s assets, processes, and objectives. It also estimates the probability of occurrence and the severity of consequences for each risk event. A threat and vulnerability assessment is the best way to quantify the likelihood of risk materialization, as it provides a numerical or qualitative measure of the risk exposure and the level of uncertainty associated with the risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.2, p. 68-69
Numerous media reports indicate a recently discovered technical vulnerability is being actively exploited. Which of the following would be the BEST response to this scenario?
Options:
Assess the vulnerability management process.
Conduct a control serf-assessment.
Conduct a vulnerability assessment.
Reassess the inherent risk of the target.
Answer:
CExplanation:
A technical vulnerability is a weakness or flaw in the design or implementation of an information system or resource that can be exploited or compromised by a threat or source of harm that may affect the organization’s objectives or operations. A technical vulnerability may be caused byvarious factors, such as human error, system failure, process inefficiency, resource limitation, etc.
A vulnerability assessment is a process of identifying and evaluating the technical vulnerabilities that exist or may arise in the organization’s information systems or resources, and determining their severity and impact. A vulnerability assessment can help the organization to assess and prioritize the risks, and to design and implement appropriate controls or countermeasures to mitigate or prevent the risks.
The best response to the scenario of a recently discovered technical vulnerability being actively exploited is to conduct a vulnerability assessment, because it can help the organization to address the following questions:
What is the nature and extent of the technical vulnerability, and how does it affect the functionality or security of the information system or resource?
How is the technical vulnerability being exploited or compromised, and by whom or what?
What are the potential consequences or impacts of the exploitation or compromise of the technical vulnerability for the organization and its stakeholders?
How can the technical vulnerability be detected and reported, and what are the available or feasible options or solutions to address or correct it?
Conducting a vulnerability assessment can help the organization to improve and optimize the information system or resource quality and performance, and to reduce or eliminate the technicalvulnerability. It can also help the organization to align the information system or resource with the organization’s objectives and requirements, and to comply with the organization’s policies and standards.
The other options are not the best responses to the scenario of a recently discovered technical vulnerability being actively exploited, because they do not address the main purpose and benefit of conducting a vulnerability assessment, which is to identify and evaluate the technical vulnerability, and to determine its severity and impact.
Assessing the vulnerability management process is a process of evaluating and verifying the adequacy and effectiveness of the process that is used to identify, analyze, evaluate, and communicate the technical vulnerabilities, and to align them with the organization’s objectives and requirements. Assessing the vulnerability management process can help the organization to improve and optimize the process, and to reduce or eliminate the gaps or weaknesses in the process, but it is not the best response to the scenario, because it does not indicate the nature and extent of the technical vulnerability, and how it affects the organization and its stakeholders.
Conducting a control self-assessment is a process of evaluating and verifying the adequacy and effectiveness of the controls that are intended to ensure the confidentiality, integrity, availability, and reliability of the information systems and resources, using the input and feedback from the individuals or groups that are involved or responsible for the information systems activities or functions. Conducting a control self-assessment can help the organization to identify and document the control deficiencies, and to align them with the organization’s objectives and requirements, but it is not the best response to the scenario, because it does not indicate thenature and extent of the technical vulnerability, and how it affects the organization and its stakeholders.
Reassessing the inherent risk of the target is a process of reevaluating and recalculating the amount and type of risk that exists in the absence of any controls, and that is inherent to the nature or characteristics of the target, which is the information system or resource that is affected by the technical vulnerability. Reassessing the inherent risk of the target can help the organization to understand and document the risk exposure or level, and to align it with the organization’s risk appetite and tolerance, but it is not the best response to the scenario, because it does not indicate the nature and extent of the technical vulnerability, and how it affects the organization and its stakeholders. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 195
CRISC Practice Quiz and Exam Prep
Options:
Recovery point objective (RPO) of 48 hours
Recovery time objective (RTO) of 48 hours
Mean time between failures (MTBF) of 48 hours
Mean time to recover (MTTR) of 48 hours
Answer:
BExplanation:
Recovery Time Objective (RTO) defines the maximum acceptable length of time that an application can be unavailable after a disruption before impacting business operations. Thus, specifying an RTO of 48 hours means the application must be restored and operational within that timeframe. RPO refers to data loss tolerance, MTBF relates to reliability and failure intervals, and MTTR is a technical measure of repair time but less commonly used in BCP metrics【5:223, 5:224†CRISC_SentenceinNOTE30.pptx】.
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor ' s control environment?
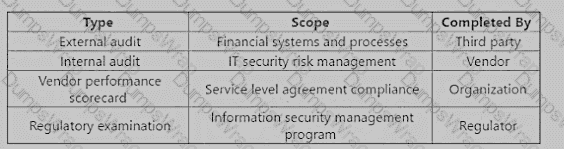
Options:
External audit
Internal audit
Vendor performance scorecard
Regulatory examination
Answer:
AExplanation:
An external audit is the most reliable input to evaluate residual risk in the vendor’s control environment, as it provides an independent and objective assessment of the vendor’s financial systems and processes. An external audit is conducted by a third party, such as a certified public accountant (CPA) or a professional auditing firm, that follows the generally accepted auditing standards (GAAS) and the generally accepted accounting principles (GAAP). An external audit can help to verify the accuracy and completeness of the vendor’s financial statements, identify any material misstatements or errors, and evaluate the effectiveness and efficiency of the vendor’s internal controls. An external audit can also provide assurance and confidence to the organization and other stakeholders that the vendor is complying with the relevant laws, regulations, and contractual obligations.
The other options are not the most reliable inputs to evaluate residual risk in the vendor’s control environment. An internal audit is conducted by the vendor itself, which may introduce bias or conflict of interest. An internal audit may also have a different scope, methodology, or quality than an external audit. A vendor performance scorecard is completed by the organization, which may not have the sufficient access, expertise, or authority to assess the vendor’s control environment. A vendor performance scorecard may also focus more on the service level agreement (SLA) compliance, rather than the financial systems and processes. A regulatory examination is conducted by a regulator, such as a government agency or a standard-settingbody, which may have a different purpose, criteria, or perspective than the organization. A regulatory examination may also have a limited scope, frequency, or transparency. References = Guide to VendorRisk Assessment | Smartsheet, Understanding Inherent Vs. Residual Risk Assessments - Resolver, Assessing Internal Controls over Compliance - HCCA Official Site
A business unit has implemented robotic process automation (RPA) for its
repetitive back-office tasks. Which of the following should be the risk
practitioner ' s GREATEST concern?
Options:
The security team is unaware of the implementation.
The organization may lose institutional knowledge.
The robots may fail to work effectively.
Virtual clients are used for implementation.
Answer:
AWhich of the following BEST indicates the effectiveness of anti-malware software?
Options:
Number of staff hours lost due to malware attacks
Number of downtime hours in business critical servers
Number of patches made to anti-malware software
Number of successful attacks by malicious software
Answer:
DExplanation:
The effectiveness of anti-malware software is the degree to which it can detect, prevent, and remove malicious software (malware) from the system or network. Malware is any software that is designed to harm, exploit, or compromise the functionality, security, or privacy of the system or network1. Some common types of malware are viruses, worms, Trojans, ransomware, spyware, adware, and rootkits2.
One of the best indicators of the effectiveness of anti-malware software is the number of successful attacks by malicious software, which means the number of times that malware has managed to bypass, evade, or disable the anti-malware software and cause damage or disruption to the system or network. The lower the number of successful attacks, the higher the effectiveness of the anti-malware software. This indicator can measure the ability of the anti-malware software to protect the system or network from known and unknown malware threats, and to respond and recover from malware incidents34.
The other options are not the best indicators of the effectiveness of anti-malware software, because:
Number of staff hours lost due to malware attacks is a measure of the impact or consequence of malware attacks on the productivity or performance of the staff. It does not directly reflect the ability of the anti-malware software to detect, prevent, or remove malware, as there may be other factors that affect the staff hours lost, such as the severity of the attack, the availability of backup or recovery systems, or the skills and awareness of the staff5.
Number of downtime hours in business critical servers is a measure of the impact or consequence of malware attacks on the availability or reliability of the servers. It does notdirectly reflect the ability of the anti-malware software to detect, prevent, or remove malware, as there may be other factors that affect the downtime hours, such as the type of the server, the configuration of the network, or the maintenance of the hardware6.
Number of patches made to anti-malware software is a measure of the maintenance or improvement of the anti-malware software. It does not directly reflect the ability of the anti-malware software to detect, prevent, or remove malware, as there may be other factors that affect the number of patches, such as the frequency of the updates, the quality of the software, or the compatibility of the system7.
References =
What is Malware? - Definition from Techopedia
Common Types of Malware and Their Impact - Techopedia
What is Anti-Malware? Everything You Need to Know (2023) - SoftwareLab
The 10 Best Malware Protection Solutions Compared for 2024 - Techopedia
The Cost of Malware Attacks - Security Boulevard
The Impact of Malware on Business - Kaspersky
What is Patch Management? - Definition from Techopedia
An organization ' s risk register contains a large volume of risk scenarios that senior management considers overwhelming. Which of the following would BEST help to improve the risk register?
Options:
Analyzing the residual risk components
Performing risk prioritization
Validating the risk appetite level
Conducting a risk assessment
Answer:
BExplanation:
Performing risk prioritization would best help to improve the risk register, which is a document that records and summarizes the key information and data about the identified risks and the risk responses1. Risk prioritization is the process of ranking the risks according to their significance and urgency, based on their probability and impact2. By performing risk prioritization, the organization can:
Reduce the complexity and volume of the risk register, and focus on the most important and relevant risks that require immediate attention and action3.
Enhance the communication and understanding of the risks among the senior management and other stakeholders, and facilitate the decision-making and resource allocation for the risk responses4.
Improve the efficiency and effectiveness of the risk management process, and ensure that the risk register is aligned with the organization’s risk strategy, objectives, and appetite5.
The other options are not the best ways to improve the risk register, because:
Analyzing the residual risk components is not the best way, as it may not address the issue of the large volume of risk scenarios. Residual risk is the level of risk that remains after the implementation of risk responses6. Analyzing the residual risk components can help to measure the exposure or uncertainty of the assets, and to determine the need and extent of the risk responses. However, it may not reduce the complexity or volume of the risk register, as it may add more information or data to the risk register.
Validating the risk appetite level is not the best way, as it may not address the issue of the overwhelming risk scenarios. Risk appetite is the amount and type of risk that the organization is willing to accept or pursue in order to achieve its objectives7. Validating the risk appetite levelcan help to ensure that the risk register is consistent and proportional to the risk level, and that the risk responses are suitable and feasible. However, it may not reduce the complexity or volume of the risk register, as it may require more information or data to validate the risk appetite level.
Conducting a risk assessment is not the best way, as it may not address the issue of the existing risk scenarios. Risk assessment is the process of estimating the probability and impact of the risks, and prioritizing the risks based on their significance and urgency. Conducting a risk assessment can help to identify and analyze new or emerging risks, and to update or revise the risk register accordingly. However, it may not reduce the complexity or volume of the risk register, as it may introduce more information or data to the risk register.
References =
Risk Register - CIO Wiki
Risk Prioritization - CIO Wiki
Risk Prioritization: A Guide for Project Managers - ProjectManager.com
Risk Prioritization: How to Prioritize Risks in Project Management - Clarizen
Risk Prioritization: A Key Step in Risk Management - ISACA
Residual Risk - CIO Wiki
Risk Appetite - CIO Wiki
[Risk Assessment - CIO Wiki]
Which of the following is the PRIMARY reason for a risk practitioner to use global standards related to risk management?
Options:
To build an organizational risk-aware culture
To continuously improve risk management processes
To comply with legal and regulatory requirements
To identify gaps in risk management practices
Answer:
BExplanation:
Global standards related to risk management are documents that provide the principles, guidelines, and best practices for managing risk in a consistent, effective, and efficient manner across different organizations, sectors, and regions12.
The primary reason for a risk practitioner to use global standards related to risk management is to continuously improve risk management processes, which are the activities and tasks that enable the organization to identify, analyze, evaluate, treat, monitor, and communicate the risks that may affect its objectives, performance, and value creation34.
Continuously improving risk management processes is the primary reason because it helps the organization to enhance its risk management capabilities and maturity, and to adapt to the changing risk environment and stakeholder expectations34.
Continuously improving risk management processes is also the primary reason because it supports the achievement of the organization’s goals and the delivery of value to the stakeholders, which are the ultimate purpose and outcome of risk management34.
The other options are not the primary reason, but rather possible benefits or objectives that may result from using global standards related to risk management. For example:
Building an organizational risk-aware culture is a benefit of using global standards related to risk management that involves creating and maintaining a shared understanding, attitude, and behavior towards risk among the organization’s employees and leaders, and fostering a culture of accountability, transparency, and learning34. However, this benefit is not the primary reason because it is an enabler and a consequence of continuously improving risk management processes, rather than a driver or a goal34.
Complying with legal and regulatory requirements is an objective of using global standards related to risk management that involves meeting and exceeding the expectations and obligations of the external authorities or bodies that govern or oversee the organization’s activities and operations, such as laws, regulations, standards, or contracts34. However, thisobjective is not theprimary reason because it is a constraint and a challenge of continuously improving risk management processes, rather than a motivation or a benefit34.
Identifying gaps in risk management practices is an objective of using global standards related to risk management that involves assessing and comparing the current and desiredstate of the organization’s risk management processes, and identifying the areas or aspects that need to be improved or addressed34. However, this objective is not the primary reason because it is a step and a tool of continuously improving risk management processes, rather than a reason or a result34. References =
1: ISO - ISO 31000 — Risk management1
2: Risk Management Standards2
3: Risk IT Framework, ISACA, 2009
4: IT Risk Management Framework, University of Toronto, 2017
Which of the following would be a weakness in procedures for controlling the migration of changes to production libraries?
Options:
The programming project leader solely reviews test results before approving the transfer to production.
Test and production programs are in distinct libraries.
Only operations personnel are authorized to access production libraries.
A synchronized migration of executable and source code from the test environment to the production environment is allowed.
Answer:
AExplanation:
The programming project leader solely reviewing test results before approving the transfer to production would be a weakness in procedures for controlling the migration of changes to production libraries, because it violates the principle of segregation of duties, and it exposes the production libraries to the risk of unauthorized or erroneous changes. The programming project leader is responsible for developing and testing the changes, but not for approving and deploying them. The approval and deployment of the changes should be done by an independent and authorized party, such as the change control board or the operations manager. The other options are not weaknesses, but rather good practices, because:
Option B: Test and production programs being in distinct libraries is a good practice, because it prevents the accidental or intentional overwriting or mixing of the test and production programs, and it ensures the integrity and security of the production libraries.
Option C: Only operations personnel being authorized to access production libraries is a good practice, because it restricts the access and modification of the production libraries to the qualified and accountable staff, and it prevents the unauthorized or inappropriate access or modification of the production libraries by other parties.
Option D: A synchronized migration of executable and source code from the test environment to the production environment being allowed is a good practice, because it ensures the consistency and completeness of the changes, and it avoids the potential errors or discrepancies that may arise from the manual or partial migration of the changes. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 215.
When using a third party to perform penetration testing, which of the following is the MOST important control to minimize operational impact?
Options:
Perform a background check on the vendor.
Require the vendor to sign a nondisclosure agreement.
Require the vendor to have liability insurance.
Clearly define the project scope
Answer:
DExplanation:
When using a third party to perform penetration testing, the most important control to minimize operational impact is to clearly define the project scope. This means specifying the objectives,boundaries, methods, and deliverables of the testing, as well as the roles and responsibilities of the parties involved. A clear project scope helps to avoid misunderstandings, conflicts, and disruptions that could compromise the security, availability, or integrity of the systems undertest. It also helps to ensure that the testing is aligned with the organization’s risk appetite and compliance requirements. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.2.3.2, Page 137.
Which of the following is MOST important for a risk practitioner to ensure once a risk action plan has been completed?
Options:
The risk owner has validated outcomes.
The risk register has been updated.
The control objectives are mapped to risk objectives.
The requirements have been achieved.
Answer:
AExplanation:
The most important thing for a risk practitioner to ensure once a risk action plan has been completed is that the risk owner has validated the outcomes, as this means that the risk owner has confirmed that the risk response has been implemented and that the risk level has been reduced to an acceptable level. The risk owner is the person or entity with the authority and responsibility to manage a particular risk, and they should evaluate the effectiveness and efficiency of the risk action plan, and report any issues or changes. The risk action plan is a document that outlines the specific actions, resources, responsibilities, and timelines for implementing a risk response. The other options are not the most important things for a risk practitioner to ensure once a risk action plan has been completed, although they may be useful or necessary steps. Updating the risk register is a good practice, but it should be done after the risk owner hasvalidated the outcomes and with the consent of the risk owner. Mapping the control objectives to the risk objectives is a part of the risk response design, but it does not measure the actual achievement of the risk objectives. Achieving the requirements is a desired result, but it does not guarantee that the risk owner has validated the outcomes or that the risk level has been reduced to an acceptable level. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk Response, page 146.
Which of the following BEST enables an organization to address new risk associated with an Internet of Things (IoT) solution?
Options:
Transferring the risk
Introducing control procedures early in the life cycle
Updating the risk tolerance to include the new risk
Implementing IoT device monitoring software
Answer:
BExplanation:
Introducing control procedures early in the IoT solution life cycle ensures proactive identification and mitigation of risks. This approach aligns withSecure System Development PracticesandRisk Mitigation Strategies, reducing exposure as the solution evolves.
Which of the following is the MOST important characteristic when designing a key risk indicator (KRI)?
Options:
It is linked to a key performance indicator (KPI)
It is linked to a key control indicator (KCI)
It contains an objective alert threshold
It aligns with industry benchmarks
Answer:
CExplanation:
For a KRI to be actionable and effective, it must haveobjective thresholds. These thresholds act as triggers for decision-making and allow for timely response before risk materializes.
An organization has allowed several employees to retire early in order to avoid layoffs Many of these employees have been subject matter experts for critical assets Which type of risk is MOST likely to materialize?
Options:
Confidentiality breach
Institutional knowledge loss
Intellectual property loss
Unauthorized access
Answer:
BExplanation:
The type of risk that is most likely to materialize as a result of allowing several employees to retire early in order to avoid layoffs is institutional knowledge loss, as it represents the loss of valuable information, experience, and expertise that the employees have accumulated over time, and that may not be easily transferred or replaced. Confidentiality breach, intellectual property loss, and unauthorized access are not the most likely types of risk, as they are more related to the security, ownership, or access of information, respectively, rather than the retention or transfer of knowledge. References = CRISC Review Manual, 7th Edition, page 100.
When testing the security of an IT system, il is MOST important to ensure that;
Options:
tests are conducted after business hours.
operators are unaware of the test.
external experts execute the test.
agreement is obtained from stakeholders.
Answer:
DExplanation:
According to the CRISC Review Manual1, stakeholders are the individuals or groups that have an interest or stake in the outcome of the IT system and its risks. Stakeholders include the system owners, users, operators, developers, managers, auditors, regulators, and customers. It is most important to ensure that agreement is obtained from stakeholders when testing the security of an IT system, as this helps to define the scope, objectives, and expectations of the test, and to obtain the necessary authorization, support, and resources for the test. Agreement from stakeholders also helps to avoid any conflicts, disruptions, or misunderstandings that may arise during or after the test, and to ensure the validity and acceptance of the test results and recommendations. References = CRISC Review Manual1, page 198, 224.
An organization is planning to acquire a new financial system. Which of the following stakeholders would provide the MOST relevant information for analyzing the risk associated with the new IT solution?
Options:
Project sponsor
Process owner
Risk manager
Internal auditor
Answer:
BExplanation:
The process owner is the stakeholder who is responsible for the business process that will be supported by the new IT solution. The process owner has the best knowledge of the businessrequirements, objectives, and risks associated with the process. The process owner can provide the most relevant information for analyzing the risk associated with the new IT solution, such as the expected benefits, costs, performance, functionality, security, and compliance of the solution. The process owner can also help to identify and evaluate the potential impact and likelihood of the risk scenarios related to the new IT solution. The other stakeholders may have some information or insights, but they are not as directly involved or affected by the new IT solution as the process owner. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.3.1.1, pp. 58-59.
Which of the following is the MOST cost-effective way to test a business continuity plan?
Options:
Conduct interviews with key stakeholders.
Conduct a tabletop exercise.
Conduct a disaster recovery exercise.
Conduct a full functional exercise.
Answer:
BExplanation:
A business continuity plan (BCP) is a document that describes the procedures and actions that an organization will take to ensure the continuity of its critical functions and operations in the event of a disruption or disaster12.
Testing a business continuity plan is a method of evaluating the effectiveness and readiness of the BCP, and identifying and addressing any gaps or weaknesses in the plan34.
The most cost-effective way to test a business continuity plan is to conduct a tabletop exercise, which is a type of simulation that involves gathering the key stakeholders and participants of the BCP, and discussing and reviewing the roles, responsibilities, and actions that they will take in response to a hypothetical scenario of a disruption or disaster56.
A tabletop exercise is the most cost-effective way because it requires minimal resources and time, and can be conducted in a regular meeting room or online platform56.
A tabletop exercise is also the most cost-effective way because it provides a high-level overview and assessment of the BCP, and can identify and address the major issues or challenges that may arise in the implementation of the plan56.
The other options are not the most cost-effective ways, but rather possible alternatives or supplements that may have different levels of complexity or cost. For example:
Conducting interviews with key stakeholders is a way of testing a business continuity plan that involves asking and answering questions about the BCP, and collecting feedback and suggestions from the people who are involved or affected by the plan78. However, this way is not the most cost-effective because it may not cover all the aspects or scenarios of the BCP, and may not facilitate the interaction or collaboration among the stakeholders78.
Conducting a disaster recovery exercise is a way of testing a business continuity plan that involves activating and executing the BCP in a realistic and controlled environment, and measuring the outcomes and impacts of the plan . However, this way is not the most cost-effective because it requires a lot of resources and time, and may disrupt or interfere with the normal operations of the organization .
Conducting a full functional exercise is a way of testing a business continuity plan that involves simulating and testing the BCP in a live and dynamic environment, and involving the external entities and stakeholders that are part of the plan . However, this way is not the most cost-effective because it requires the most resources and time, and may pose the highest risk or challenge to the organization . References =
1: Business Continuity Plan (BCP) Definition1
2: Business Continuity Planning - Ready.gov2
3: Testing, testing: how to test your business continuity plan4
4: Comprehensive Guide to Business Continuity Testing | Agility5
5: How to Conduct a Tabletop Exercise for Business Continuity3
6: Tabletop Exercises: A Guide to Success6
7: How to Conduct Testing of a Business Continuity Plan7
8: Business Continuity Plan Testing: Interviewing Techniques8
Disaster Recovery Testing: A Step-by-Step Guide
Disaster Recovery Testing Scenarios: A Guide to Success
Functional Exercises: A Guide to Success
Functional Exercise Toolkit
Which of the following is the ULTIMATE objective of utilizing key control indicators (KCIs) in the risk management process?
Options:
To provide a basis for determining the criticality of risk mitigation controls
To provide early warning signs of a potential change in risk level
To provide benchmarks for assessing control design effectiveness against industry peers
To provide insight into the effectiveness of the intemnal control environment
Answer:
DExplanation:
Key control indicators (KCIs) are metrics that measure the performance of a control in reducing the causes, consequences, or likelihood of a risk. They help to evaluate the adequacy and efficiency of the internal control environment, which is the set of policies, procedures, and practices that support the achievement of organizational objectives and the management of risks. By monitoring KCIs, organizations can identify and address any gaps or weaknesses in their internal controls and ensure that they are operating as intended.
References
•ISACA CRISC Review Manual, 7th Edition, Domain 3: Risk Response, Section 3.2.2: Control Design and Implementation
•KRI Framework for Operational Risk Management | Workiva
•What is the difference between key risk indicators and key control indicators?
A PRIMARY objective of disaster recovery is to:
Options:
Improve infrastructure of physical locations
Restore critical business and IT services
Recover financial data and statements
Maintain operational processes and connectivity
Answer:
BExplanation:
Disaster Recovery (DR)focuses onrestoring IT and business servicesto support essential operations after a disruption.
ISACA defines:
“The primary objective of disaster recovery is the timely restoration of critical IT systems and services necessary to support business operations.”
Recovery of financial records or facilities are secondary components.
Therefore,B. Restore critical business and IT servicesis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Business Continuity and Disaster Recovery Planning.
To enable effective integration of IT risk scenarios and enterprise risk management (ERM), it is MOST important to have a consistent approach to reporting:
Options:
Key risk indicators (KRIs).
Risk velocity.
Risk response plans and owners.
Risk impact and likelihood.
Answer:
DExplanation:
A consistent approach to reporting risk impact and likelihood is crucial for integrating IT risk scenarios into the broader enterprise risk management framework. Standardizing these metrics ensures that risks are assessed and compared uniformly across the organization, facilitating informed decision-making and prioritization of risk responses.
Which of the following presents the GREATEST risk to change control in business application development over the complete life cycle?
Options:
Emphasis on multiple application testing cycles
Lack of an integrated development environment (IDE) tool
Introduction of requirements that have not been approved
Bypassing quality requirements before go-live
Answer:
CExplanation:
The greatest risk to change control in business application development over the complete life cycle is the introduction of requirements that have not been approved. Requirements are the specifications or expectations of the business users or stakeholders for the application, such as the features, functions, or performance1. Change control is the process of identifying, evaluating, approving, and implementing changes to the application, such as the design, code, or configuration2. By introducing requirements that have not been approved, the organization can face significant risks, such as:
Scope creep, which is the uncontrolled or unauthorized expansion of the project scope, and can result in increased costs, delays, or errors3.
Quality issues, which can affect the reliability, usability, or security of the application, and can lead to defects, failures, or breaches4.
Stakeholder dissatisfaction, which can arise from the mismatch or inconsistency between the delivered application and the expected application, and can cause complaints, disputes, or litigation5.
The other options are not the greatest risk to change control, because:
Emphasis on multiple application testing cycles is not a risk, but rather a benefit or a best practice for change control, as it can help to ensure that the application meets the requirements and standards, and that the changes are effective and efficient.
Lack of an integrated development environment (IDE) tool is a challenge, but not a risk, for change control, as it can affect the productivity, collaboration, or integration of the developers, and can cause difficulties or inefficiencies in the development process. However, it does not directly affect the requirements or the quality of the application, and it can be overcome by using other tools or methods.
Bypassing quality requirements before go-live is a risk, but not the greatest risk, for change control, as it can compromise the quality or performance of the application, and can expose the organization to errors, failures, or breaches. However, it is less likely or frequent than introducing requirements that have not been approved, and it can be detected or prevented by using quality assurance or quality control techniques.
References =
Requirements - CIO Wiki
Change Control - CIO Wiki
Scope Creep - CIO Wiki
Quality - CIO Wiki
Stakeholder Management - CIO Wiki
[Software Testing - CIO Wiki]
[Integrated Development Environment (IDE) - CIO Wiki]
[Quality Requirements - CIO Wiki]
[Software Development Life Cycle - CIO Wiki]
Which of the following is the MOST appropriate action when a tolerance threshold is exceeded?
Options:
Communicate potential impact to decision makers.
Research the root cause of similar incidents.
Verify the response plan is adequate.
Increase human resources to respond in the interim.
Answer:
AExplanation:
The most appropriate action when a tolerance threshold is exceeded is to communicate the potential impact to the decision makers. A tolerance threshold is the acceptable level of variation or deviation from the expected or planned performance or outcome of a risk response. When a tolerance threshold is exceeded, it means that the risk response is not effective or efficient enough to reduce the risk to an acceptable level, and that the enterprise is exposed to unacceptable levels of risk that could impair its ability to achieve its objectives. Therefore, the potential impact of the risk should be communicated to the decision makers, such as senior management, risk owners, or risk committee, who have the authority and responsibility to decide on the appropriate actions to address the risk situation. Communicating the potential impact can help to raise the awareness and urgency of the risk issue, and to facilitate the risk-based decision making process. Researching the root cause of similar incidents, verifying the response plan isadequate, and increasing human resources to respond in the interim are not as appropriate as communicating the potential impact, as they do not address the primary need of informing and involving the decision makers, and may not be feasible or effective in resolving the risk issue. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 41.
A service provider is managing a client’s servers. During an audit of the service, a noncompliant control is discovered that will not be resolved before the next audit because the client cannot afford the downtime required to correct the issue. The service provider’s MOST appropriate action would be to:
Options:
develop a risk remediation plan overriding the client ' s decision
make a note for this item in the next audit explaining the situation
insist that the remediation occur for the benefit of other customers
ask the client to document the formal risk acceptance for the provider
Answer:
DExplanation:
A noncompliant control is a control that does not meet the requirements or standards of an audit, regulation, or policy. A noncompliant control can expose the organization to risks such as errors, fraud, or breaches. When a noncompliant control is identified, the service provider and the client should work together to resolve the issue as soon as possible. However, sometimes the resolution may not be feasible or cost-effective, and the client may decide to accept the risk associated with the noncompliant control.
In this case, the service provider’s most appropriate action would be to ask the client to document the formal risk acceptance for the provider. This means that the client should acknowledge the existence and consequences of the noncompliant control, and provide a written justification for accepting the risk. The risk acceptance document should also specify the roles and responsibilities of the service provider and the client, and the duration and conditions of the risk acceptance. The risk acceptance document should be signed by the client’s senior management and the service provider’s management, and kept as part of the audit evidence.
The other options are not appropriate actions for the service provider. Developing a risk remediation plan overriding the client’s decision would be disrespectful and unprofessional, as it would ignore the client’s authority and preference. Making a note for this item in the next audit explaining the situation would be insufficient and misleading, as it would imply that the issue is still unresolved and that the service provider is responsible for it. Insisting that the remediation occur for the benefit of other customers would be unreasonable and impractical, as it woulddisregard the client’s business needs and constraints, and potentially harm the relationship between the service provider and the client. References =
Risk Acceptance - Institute of Internal Auditors
New Guidance on the Evaluation of Non-compliance with the Risk Assessment Standard and its Peer Review Impact - REVISED
The Impact of Non-compliance: Understanding The Risks And Consequences
Which of the following is a detective control?
Options:
Limit check
Periodic access review
Access control software
Rerun procedures
Answer:
BExplanation:
A detective control is a type of internal control that seeks to uncover problems in a company’s processes once they have occurred. Examples of detective controls include physical inventory checks, reviews of account reports and reconciliations, as well as assessments of current controls1. A periodic access review is a detective control that involves verifying the access rightsand privileges of users to ensure that they are appropriate and authorized. A periodic access review can help to detect any unauthorized or inappropriate access, such as excessive or redundant permissions, segregation of duties violations, or dormant ororphaned accounts23. The other options are not detective controls, but rather preventive controls, which are designed to prevent errors or fraud from occurring in the first place. A limit check is a preventive control that validates the input data against a predefined range or limit, and rejects any data that falls outside the acceptable range4. Access control software is a preventive control that restricts the access to information systems or resources based on the identity, role, or credentials of the user5. Rerun procedures are preventive controls that ensure the accuracy and completeness of data processing by repeating the same process and comparing the results6. References = Detective Control: Definition, Examples, Vs. Preventive Control; Detective Control - What Is It, Examples, Vs Preventive Control; Limit Check - an overview |ScienceDirect Topics; Access Control Software - an overview | ScienceDirect Topics; Rerun Procedures - an overview | ScienceDirect Topics
Which of the following will BEST help mitigate the risk associated with malicious functionality in outsourced application development?
Options:
Perform an in-depth code review with an expert
Validate functionality by running in a test environment
Implement a service level agreement.
Utilize the change management process.
Answer:
AExplanation:
The risk associated with malicious functionality in outsourced application development is that the vendor may introduce unauthorized or harmful code into the enterprise’s system, which could compromise its security, integrity, or performance.
To mitigate this risk, the enterprise should perform an in-depth code review with an expert who can verify that the code meets the specifications, standards, and quality requirements, and that it does not contain any malicious or unwanted functionality.
A code review is a systematic examination of the source code of a software program, which can identify errors, vulnerabilities, inefficiencies, or deviations from best practices. A code review can also ensure that the code is consistent, readable, maintainable, and well-documented.
An expert is someone who has the knowledge, skills, and experience to perform the code review effectively and efficiently. An expert may be an internal or external resource, depending on the availability, cost, and independence of the reviewer.
A code review should be performed before the code is deployed to the production environment, and preferably at multiple stages of the development life cycle, such as design, testing, and integration.
A code review can also be complemented by other techniques, such as automated code analysis, testing, and scanning tools, which can detect common or known issues in the code. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, p. 143
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 143
Which of the following is the MOST effective control to ensure user access is maintained on a least-privilege basis?
Options:
User authorization
User recertification
Change log review
Access log monitoring
Answer:
BExplanation:
User recertification is the most effective control to ensure user access is maintained on a least-privilege basis, as it involves a periodic review and validation of user access rights and privileges by the appropriate authority. User recertification helps to identify and remove any unnecessary, excessive, or obsolete access rights and privileges that may pose a security risk or violate the principle of least privilege. User recertification also helps to ensure that user access rights and privileges are aligned with the current business needs, roles, and responsibilities of the users.
The other options are not the most effective controls to ensure user access is maintained on a least-privilege basis. User authorization is the process of granting or denying access rights and privileges to users based on their identity, role, and credentials, but it does not verify or update the existing access rights and privileges of the users. Change log review is the process of examining and analyzing the records of changes made to the system, configuration, or data, but it does not directly address the user access rights and privileges. Access log monitoring is the process of tracking and auditing the user activities and actions on the system or network, but it does not validate or modify the user access rights and privileges. References = What Is the Principle of Least Privilege and Why is it Important?, Principle of Least Privilege: Definition, Methods & Examples, IT Risk Resources | ISACA
A risk assessment has identified increased losses associated with an IT risk scenario. It is MOST important for the risk practitioner to:
Options:
update the risk rating.
reevaluate inherent risk.
develop new risk scenarios.
implement additional controls.
Answer:
AExplanation:
The most important action for the risk practitioner to take when a risk assessment has identified increased losses associated with an IT risk scenario is to update the risk rating. A risk rating is a measure of the overall level of risk, based on the combination of the probability and impact of the risk scenario. A risk rating helps to prioritize the risks, communicate the risk exposure, and monitor the risk response. Updating the risk rating is the most important action, because it reflects the current state and magnitude of the risk, and it triggers the review and revision of the risk response plan, if needed. Updating the risk rating also ensures that the risk register and the risk profile are accurate and complete, and that the risk management process is consistent and effective. The other options are not the most important action, although they may be related or subsequent steps in the risk management process. Reevaluating inherent risk is a part of the risk analysis process, which estimates the probability and impact of the risk scenario before considering the existing controls. Reevaluating inherent risk can help to identify the root causes and drivers of the risk, and to assess the effectiveness and efficiency of the controls, but it does not change the overall level of risk or the risk response plan. Developing new risk scenarios is a part of the risk identification process, which identifies and describes the potential events or situations that could affect the achievement of the objectives. Developing new risk scenarios can help to expand the scope and coverage of the risk management process, and to address the emerging or changing risks, but it does not update the existing risk scenarios or the risk response plan. Implementing additional controls is a part of the risk response process, which selects and executes the appropriate actions to reduce, avoid, share, or exploit the risk. Implementing additional controls can help to mitigate the risk and achieve the desired risk level, but it is not the first or the only option, as it depends on the risk appetite, tolerance, and capacity of the organization, and the cost-benefit analysis of the controls. References = Risk Register Template and Examples | Prioritize and Manage Risk, How to Write Strong Risk Scenarios and Statements - ISACA, IT Risk Resources | ISACA
Which of the following is MOST important to the effectiveness of key performance indicators (KPIs)?
Options:
Management approval
Annual review
Relevance
Automation
Answer:
CExplanation:
The most important factor to the effectiveness of key performance indicators (KPIs) is relevance. KPIs are metrics that measure the achievement of the objectives or the performance of the processes. Relevance means that the KPIs are aligned with and support the strategic goals and priorities of the organization, and that they reflect the current and desired state of the outcomes or outputs. Relevance also means that the KPIs are meaningful and useful for the decision makers and stakeholders, and that they provide clear and actionable information for improvement or optimization. The other options are not as important as relevance, as they arerelated to the approval, review, or automation of the KPIs, not the quality or value of the KPIs. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Key Performance Indicators, page 183.
When creating a program to manage data privacy risk, which of the following is MOST important to ensure that the program is successful?
Options:
Compliance with industry frameworks
Alignment with applicable legal and regulatory requirements
Approval of mitigating and compensating controls
Adoption of mission and vision statements
Answer:
BExplanation:
Privacy risk management programs must align withspecific regulatory obligations(e.g., GDPR, HIPAA) to be effective and compliant. Legal alignment defines scope, control requirements, and accountability.
As part of an overall IT risk management plan, an IT risk register BEST helps management:
Options:
align IT processes with business objectives.
communicate the enterprise risk management policy.
stay current with existing control status.
understand the organizational risk profile.
Answer:
DExplanation:
An IT risk register is a document that is used as a risk management tool to identify, analyze, and track the potential risks related to the use of information technology within an organization. An IT risk register helps management to understand the organizational risk profile, which is a comprehensive and structured representation of the risks that the organization faces. The risk profile helps the organization to understand its risk exposure, appetite, and tolerance, and to align its risk management strategy with its business objectives and context. The risk register is an essential input for creating and updating the risk profile, as it provides the data and analysis ofthe risks that need to be prioritized and addressed12. The other options are not the best answers, as they are either not directly shown or derived from the IT risk register. Aligning IT processes with business objectives is a goal of IT governance, which may be influenced by the IT risk register, but not solely determined by it. Communicating the enterprise risk management policy is a responsibility of the senior management and the board of directors, which may use the IT risk register as a reference, but not as the main source. Staying current with existing control status is a function of IT audit and assurance, which may rely on the IT risk register as a basis, but not as the only evidence. References = Risk Register: A Project Manager’s Guide with Examples [2023] • Asana; Complete Guide to IT Risk Management | CompTIA
Which of the following is the GREATEST benefit when enterprise risk management (ERM) provides oversight of IT risk management?
Options:
Aligning IT with short-term and long-term goals of the organization
Ensuring the IT budget and resources focus on risk management
Ensuring senior management ' s primary focus is on the impact of identified risk
Prioritizing internal departments that provide service to customers
Answer:
AExplanation:
Enterprise risk management (ERM) is a holistic and strategic approach to managing the risks that an organization faces across its various functions, processes, and activities. ERM aims to align the organization’s risk appetite and tolerance with its objectives and vision, and to optimize the value and performance of the organization1.
IT risk management is a subset of ERM that focuses on identifying, assessing, and mitigating the risks related to the use of information technology (IT) in the organization. IT risk management aims to ensure the confidentiality, integrity, and availability of IT resources and information, and to support the IT governance and strategy of the organization2.
The greatest benefit when ERM provides oversight of IT risk management is aligning IT with short-term and long-term goals of the organization, because it can help to:
Integrate IT risk management with the overall business strategy and risk management, and ensure that IT risks are considered and addressed at the enterprise level
Align IT risk appetite and tolerance with the business risk appetite and tolerance, and ensure that IT risks are balanced with the expected benefits and opportunities
Enhance IT risk awareness and communication among the stakeholders, and ensure that IT risks are reported and escalated appropriately
Optimize IT risk response and control, and ensure that IT risks are managed efficiently and effectively
Demonstrate IT risk value and impact, and ensure that IT risks are measured and monitored against the business objectives and performance34
The other options are not the greatest benefit when ERM provides oversight of IT risk management, but rather some of the outcomes or consequences of it. Ensuring the IT budget and resources focus on risk management is a benefit that can help to allocate and prioritize the IT resources and funds according to the IT risk level and the business needs. Ensuring senior management’s primary focus is on the impact of identified risk is a benefit that can help to increase the senior management’s involvement and accountability in IT risk management, and to support the IT risk decision making and reporting. Prioritizing internal departments that provide service to customers is a benefit that can help to improve the quality and efficiency of the IT service delivery and customer satisfaction. References =
Enterprise Risk Management - ISACA
IT Risk Management - ISACA
Aligning IT risks with Enterprise Risk Management (ERM)
Five Benefits of Enterprise Risk Management : Articles : Resources …
[CRISC Review Manual, 7th Edition]
Which of the following scenarios presents the GREATEST risk of noncompliance with data privacy best practices?
Options:
Making data available to a larger audience of customers
Data not being disposed according to the retention policy
Personal data not being de-identified properly
Data being used for purposes the data subjects have not opted into
Answer:
DExplanation:
Data Privacy Principles:
Consent and Purpose Limitation: According to data privacy regulations like GDPR, data subjects must provide explicit consent for specific purposes. Using data for purposes beyond what was consented to violates these principles, posing significant compliance risks.
Transparency and Accountability: Organizations must be transparent about how they use personal data and ensure accountability in data processing. Using data without consent undermines this transparency and accountability.
Greatest Risk of Noncompliance:
Legal and Regulatory Risks: Using personal data without consent can lead to severe penalties under laws like GDPR and CPRA. These laws impose heavy fines for noncompliance, making this scenario the highest risk.
Reputational Damage: Unauthorized use of personal data can severely damage an organization’s reputation, leading to loss of customer trust and potential financial losses.
Operational Impact: Ensuring compliance with consent requirements is fundamental to an organization ' s data processing activities. Failure to do so can disrupt business operations and necessitate significant remediation efforts.
Comparison with Other Options:
Making Data Available to a Larger Audience of Customers: While potentially risky, this does not inherently violate data privacy principles if done within consented uses.
Data Not Being Disposed According to the Retention Policy: This poses risks related to data minimization and retention principles but is less severe than unauthorized data use.
Personal Data Not Being De-identified Properly: This is a significant risk but typically involves fewer direct legal and regulatory implications compared to using data without consent.
Which of the following is the BEST way to determine whether system settings are in alignment with control baselines?
Options:
Configuration validation
Control attestation
Penetration testing
Internal audit review
Answer:
AExplanation:
The best way to determine whether system settings are in alignment with control baselines is to perform configuration validation. Configuration validation is the process of verifying that the system settings and parameters are consistent with the predefined standards and requirements, and that they reflect the current and desired state of the system. Configuration validation helps to ensure that the system is configured correctly and securely, and that it complies with the relevant policies, regulations, and bestpractices. Configuration validation also helps to identify and correct any deviations or errors in the system settings, and to prevent or mitigate any potential risks or issues. The other options are not as effective as configuration validation, although they may provide some input or information for the system alignment. Control attestation, penetration testing, and internal audit review are all activities that can help to assess or evaluate the system alignment, but they do not necessarily determine or validate the system settings. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.1, page 3-11.
Which of the following would MOST likely cause a risk practitioner to change the likelihood rating in the risk register?
Options:
Risk appetite
Control cost
Control effectiveness
Risk tolerance
Answer:
CExplanation:
The likelihood rating in the risk register is a measure of how probable it is that a risk event will occur, given the current conditions and controls. The risk practitioner should change the likelihood rating if there is a significant change in the effectiveness of the controls that are implemented to prevent or reduce the risk. For example, if a control becomes obsolete, ineffective, or bypassed, the likelihood rating should increase, as the risk event becomes more likely to happen. Conversely, if a control becomes more efficient, reliable, or robust, the likelihood rating should decrease, as the risk event becomes less likely to happen. The other options are not likely to cause a change in the likelihood rating, as they are not directly related to the probability of the risk event. Risk appetite is the amount of risk that an organization is willing to accept in pursuit of its objectives. Control cost is the amount of resources that are required to implement and maintain a control. Risk tolerance is the acceptable level of variation that an organization is willing to allow for a risk to deviate from its desired level or expected outcome. These factors may influence the risk response or the risk acceptance, but not the likelihood rating. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.4: Risk Register, p. 25-26.
An organization is adopting block chain for a new financial system. Which of the following should be the GREATEST concern for a risk practitioner evaluating the system ' s production readiness?
Options:
Limited organizational knowledge of the underlying technology
Lack of commercial software support
Varying costs related to implementation and maintenance
Slow adoption of the technology across the financial industry
Answer:
AExplanation:
The greatest concern for a risk practitioner when an organization is adopting blockchain for a new financial system is the limited organizational knowledge of the underlying technology. Blockchain is a distributed ledger technology that enables secure and transparent transactions among multiple parties without the need for intermediaries or central authorities. Blockchain technology has many potential benefits for the financial sector, such as reducing costs, increasing efficiency, enhancing security, and improving trust. However, blockchain technology also poses many challenges and risks for the organization, such as technical complexity, interoperability issues, regulatory uncertainty, and cultural resistance. The limited organizational knowledge of the underlying technology is the greatest concern, because it affects the ability and readiness of the organization to adopt, implement, use, and maintain the blockchain system effectively and securely. The limited organizational knowledge could also result in poor decision-making, inadequate governance, insufficient training, and increased vulnerability to errors, fraud, or attacks. The other options are not as concerning as the limited organizational knowledge, although they may also pose some difficulties or limitations for the blockchain adoption. Lack of commercial software support, varying costs related to implementation and maintenance, and slow adoption of the technology across the financial industry are all factors that could affect the feasibility and sustainability of the blockchain system, but they do not directly affect the capability and maturity of the organization. References = 5
Which of the following should be the GREATEST concern for an organization that uses open source software applications?
Options:
Lack of organizational policy regarding open source software
Lack of reliability associated with the use of open source software
Lack of monitoring over installation of open source software in the organization
Lack of professional support for open source software
Answer:
AExplanation:
Lack of organizational policy regarding open source software should be the greatest concern for an organization that uses open source software applications, as it may expose the organization to legal, security, and operational risks. Open source software is software that is freely available and can be modified and distributed by anyone, subject to certain conditions and licenses. An organizational policy regarding open source software should define the criteria and procedures for selecting, acquiring, using, and maintaining open source software, as well as the roles and responsibilities of the stakeholders involved. Lack of reliability, lack of monitoring, and lack of professional support are not the greatest concerns, as they can be addressed by implementing quality assurance, configuration management, and community engagement practices for open source software. References = CRISC by Isaca Actual Free Exam Q & As, question 214; CRISC: Certified in Risk & Information Systems Control Sample Questions, question 214.
Which of the following presents the GREATEST challenge for an IT risk practitioner who wants to report on trends in historical IT risk levels?
Options:
Qualitative measures for potential loss events
Changes in owners for identified IT risk scenarios
Changes in methods used to calculate probability
Frequent use of risk acceptance as a treatment option
Answer:
CExplanation:
Changes in methods used to calculate probability present the greatest challenge for an IT risk practitioner who wants to report on trends in historical IT risk levels, as they may introduce inconsistency and incomparability in the risk assessment results over time. Probability is a key factor in determining the level and priority of IT risks, and different methods may produce different values for the same risk scenario. For example, some methods may use historical data, expert judgment, or simulation techniques to estimate the likelihood of a risk event. If the methods used to calculate probability change frequently or vary across different business units or processes, the IT risk practitioner may face difficulty in aggregating, normalizing, and reporting the risk levels and trends. The other options are not the greatest challenges for reporting on trends in historical IT risk levels, although they may pose some difficulties or limitations. Qualitative measures for potential loss events are subjective and imprecise, but they can stillprovide a relative ranking of risks and their impacts. Changes in owners for identified IT risk scenarios may affect the accountability and responsibility for managing the risks, but they do not necessarily affect the risk levels or trends. Frequent use of risk acceptance as a treatment option may indicate a high risk appetite ortolerance, but it does not prevent the IT risk practitioner from reporting on the risk levels or trends. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk and Control Monitoring and Reporting, page 181.
From an IT risk perspective, which of the following has the GREATEST impact on organizational strategy?
Options:
Complexity of IT architecture
Changes in IT risk tolerance
Complexity of recovery plans
Methodology for IT risk identification
Answer:
BExplanation:
The correct answer isBbecause changes inIT risk tolerancehave the strongest influence on organizational strategy. Risk tolerance affects how much uncertainty the enterprise is willing to accept in pursuing objectives, and this directly shapes strategic decisions, priorities, investments, and response choices. In CRISC terms, governance and risk management must align with enterprise goals, objectives, and business requirements; therefore, when risk tolerance changes, organizational strategy is impacted at the highest level.
The other options are less significant from a strategic perspective:
A. Complexity of IT architecturemainly affects implementation and operational management.
C. Complexity of recovery plansis important for resilience and continuity, but it is not the primary strategic driver.
D. Methodology for IT risk identificationis a process consideration and does not influence enterprise strategy as much as a change in tolerance levels.
Exact Extracts supporting the answer:
“When selecting a risk response technique the foremost consideration should be the enterprise goals and objectives.”
“The most important aspect for an effective IT risk management process is aligning with enterprise risk management.”
“The primary goal of an enterprise’s IT risk management process is to protect the enterprise and its ability to perform its mission.”
“For successful IT delivery against business requirements it ' s crucial that risk appetite be aligned with business objectives.”
“Risk tolerance is the permissible deviation from declared risk appetite levels in an enterprise.”
Taken together, these extracts show that risk tolerance and risk appetite are directly linked to business objectives and enterprise decision-making. Because strategy is driven by those objectives, a change in risk tolerance has the greatest impact on organizational strategy.
Which of the following problems is BEST solved by a cloud access security broker (CASB)?
Options:
Lack of expertise to implement single sign-on (SSO)
Cloud access security vendor selection
Inadequate key management policies
Inconsistently applied security policies
Answer:
DExplanation:
ACloud Access Security Broker (CASB)acts as a control point between cloud service users and providers to enforce the organization’s security policies consistently across all cloud applications.
CRISC-aligned cloud risk guidance explains:
“CASBs provide visibility, data security, threat protection, and compliance enforcement by applying consistent security controls across all cloud services.”
Therefore, themain issue CASBs addressisinconsistent security policy enforcementbetween on-premise and multiple cloud environments.
Option details:
AandC(SSO and key management) relate to identity or encryption control tools.
Bis unrelated to CASB’s purpose.
Hence,D. Inconsistently applied security policiesis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Cloud Risk Controls.
Which of the following is the MAIN purpose of monitoring risk?
Options:
Communication
Risk analysis
Decision support
Benchmarking
Answer:
CExplanation:
The main purpose of monitoring risk is to provide decision support for the organization. Risk monitoring is the process of tracking and reviewing the risk management activities, the risk profile, and the risk performance of the organization. By monitoring risk, the organization can obtain timely and relevant information and feedback on the risk situation, and use it to make informed and effective decisions on risk management and business objectives. Communication, risk analysis, and benchmarking are other possible purposes of risk monitoring, but they are not as important as decision support. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 12; CRISC Review Manual, 6th Edition, page 215.
Which of the following BEST enables a risk practitioner to enhance understanding of risk among stakeholders?
Options:
Key risk indicators (KRIs)
Risk scenarios
Business impact analysis (BIA)
Threat analysis
Answer:
BExplanation:
Risk scenarios are descriptions of possible events or situations that could cause or affect a risk. Risk scenarios can help a risk practitioner to enhance understanding of risk among stakeholders, as they can illustrate the causes, consequences, and impacts of the risk in a clear and realistic way. Risk scenarios can also facilitate communication and collaboration among stakeholders, as they can provide a common language and framework for risk identification, analysis, and response. Risk scenarios can also support decision-making and prioritization, as they can show the likelihood and severity of the risk outcomes. References = Most Asked CRISC Exam Questions and Answers. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 237.
Which of the following describes the relationship between Key risk indicators (KRIs) and key control indicators (KCIS)?
Options:
KCIs are independent from KRIs KRIs.
KCIs and KRIs help in determining risk appetite.
KCIs are defined using data from KRIs.
KCIs provide input for KRIs
Answer:
DExplanation:
Key risk indicators (KRIs) are metrics that provide information on the level of exposure to a given risk. Key control indicators (KCIs) are metrics that measure the performance or effectiveness of a control in mitigating a risk. KCIs provide input for KRIs, because they help to assess the residual risk after applying the control. For example, if the KRI is the number of security incidents, and the KCI is the percentage of incidents detected by the intrusion prevention system (IPS), then the KCI provides input for the KRI by showing how well the IPS is reducing the risk of security breaches. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Which of the following methods would BEST contribute to identifying obscure risk scenarios?
Options:
Brainstorming sessions
Control self-assessments
Vulnerability analysis
Monte Carlo analysis
Answer:
AExplanation:
Brainstorming sessions would best contribute to identifying obscure risk scenarios, as they allow participants to generate and share ideas without being constrained by conventional thinking or assumptions. Brainstorming sessions can help to identify risks that are not obvious, not well understood, or not covered by existing controls. Control self-assessments, vulnerability analysis, and Monte Carlo analysis are useful methods for evaluating and quantifying risks, but they are not designed to identify obscure risk scenarios. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 59.
Which of the following should be the PRIMARY focus of an IT risk awareness program?
Options:
Ensure compliance with the organization ' s internal policies
Cultivate long-term behavioral change.
Communicate IT risk policy to the participants.
Demonstrate regulatory compliance.
Answer:
BExplanation:
The primary focus of an IT risk awareness program is to cultivate long-term behavioral change. An IT risk awareness program is a program that educates and informs the stakeholders, such as the employees, managers, customers, or partners, about the IT risks and the IT risk management activities. An IT risk awareness program helps to increase the knowledge and understanding of the IT risks and the IT risk management objectives, strategies, and processes, and to promote the participation and collaboration of the stakeholders in the IT risk management activities. Theprimary focus of an IT risk awareness program is to cultivate long-term behavioral change, which is the change in the attitudes, beliefs, values, and actions of the stakeholders regarding the IT risks and the IT risk management activities. Cultivating long-term behavioral change helps to create and sustain a risk-aware culture, which is a culture that recognizes,respects, and supports the IT risk management activities, and that encourages the stakeholders to take responsibility and ownership of the IT risks and the IT risk management activities. Cultivating long-term behavioral change also helps to improve the effectiveness and efficiency of the IT risk management activities, and to align the IT risk management activities with the business goals and values. Ensuring compliance with the organization’s internal policies, communicating IT risk policy to the participants, and demonstrating regulatory compliance are not the primary focus of an IT risk awareness program, as they are either the benefits or the objectives of the IT risk awareness program, and they do not address the primary need of changing the behavior of the stakeholders. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 36.
Which of the following should be considered FIRST when managing a risk event related to theft and disclosure of customer information?
Options:
Protecting the organization from negative publicity
Performing a root cause analysis to prevent incident recurrence
Containing the impact of the incident to affected customers
Preventing further dissemination of customer information
Answer:
DExplanation:
Thefirst stepis toprevent further disseminationof sensitive data to limit the impact of the breach. ISACA emphasizes that containment is the priority in risk response to minimize harm before addressing other aspects like root cause analysis or reputational management.
===========
Which of the following is the GREATEST concern associated with business end users developing their own applications on end user spreadsheets and database programs?
Options:
An IT project manager is not assigned to oversee development.
Controls are not applied to the applications.
There is a lack of technology recovery options.
The applications are not captured in the risk profile.
Answer:
BExplanation:
The GREATEST concern associated with business end users developing their own applications on end user spreadsheets and database programs is:
B. Controls are not applied to the applications.
When end users create their own applications, there is often a lack of formal controls that would typically be applied in a structured development environment. This can lead to issues with data integrity, security vulnerabilities, and non-compliance with organizational policies and standards.
Options:
Internal email communications are not encrypted.
Data transmission within the corporate network is not encrypted.
Internally created documents are not automatically classified.
Data transmission across public networks is not encrypted.
Answer:
DExplanation:
Data transmission across public networks is the greatest risk because public networks are inherently insecure and vulnerable to interception. Encryption is critical to protecting data confidentiality during transmission over such networks. Lack of encryption internally is less risky due to controlled environments. Classification helps but does not protect data in transit. Email encryption is important but less critical compared to public network transmission risks.
Which of the following statements BEST describes risk appetite?
Options:
The amount of risk an organization is willing to accept
The effective management of risk and internal control environments
Acceptable variation between risk thresholds and business objectives
The acceptable variation relative to the achievement of objectives
Answer:
AExplanation:
Risk appetite is defined as " the amount of risk that an organization is willing to accept in pursuit of its objectives, before action is deemed necessary to reduce the risk. " 1 It represents a balance between the potential benefits of innovation and the threats that change inevitably brings. Risk appetite reflects the organization’s risk attitude and its willingness to accept risk in specific scenarios, with a governance model in place for risk oversight. Risk appetite helps to guide the organization’s approach to risk and risk management, and to align its risk decisions with its business objectives and context. The other options are not the best descriptions of risk appetite, as they are either too vague (the effective management of risk and internal control environments), too narrow (acceptable variation between risk thresholds and business objectives), or confusing (the acceptable variation relative to the achievement of objectives). References = Risk Appetite vs. Risk Tolerance: What is the Difference?
The following is the snapshot of a recently approved IT risk register maintained by an organization ' s information security department.
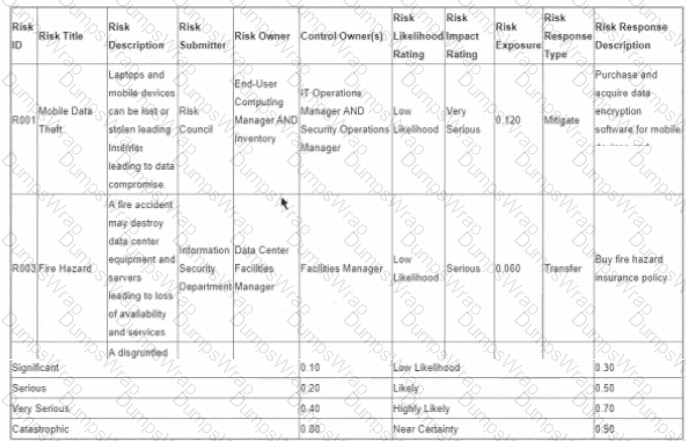
After implementing countermeasures listed in ‘’Risk Response Descriptions’’ for each of the Risk IDs, which of the following component of the register MUST change?
Options:
Risk Impact Rating
Risk Owner
Risk Likelihood Rating
Risk Exposure
Answer:
DExplanation:
Risk exposure is the product of risk likelihood and risk impact ratings. It represents the potential loss or damage that may result from a risk event. After implementing countermeasures, the risk likelihood and/or impact ratings may change, depending on the effectiveness of the countermeasures. Therefore, the risk exposure must also change to reflect the updated risk ratings. The other components of the register, such as risk owner, risk impact rating, and risk likelihood rating, may or may not change depending on the nature and scope of the countermeasures. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Response, page 87.
Which of the following is the MOST important course of action to foster an ethical, risk-aware culture?
Options:
Implement a fraud detection and prevention framework.
Ensure the alignment of the organization ' s policies and standards to the defined risk appetite.
Establish an enterprise-wide ethics training and awareness program.
Perform a comprehensive review of all applicable legislative frameworks and requirements.
Answer:
CExplanation:
According to the CRISC Review Manual, an enterprise-wide ethics training and awareness program is one of the key elements of a strong risk culture, as it helps to promote ethical behavior, raise awareness of risk management principles and practices, and foster a culture of accountability and transparency2
1: Developing Collective Risk Leadership Through CRISC - ISACA 2: CRISC Review Manual, 7th Edition, page 23
Which of the following indicates an organization follows IT risk management best practice?
Options:
The risk register template uses an industry standard.
The risk register is regularly updated.
All fields in the risk register have been completed.
Controls are listed against risk entries in the register.
Answer:
BExplanation:
According to the IT Risk Management - Basics and Best Practices article, one of the best practices for IT risk management is to keep the risk register up to date. A risk register is a document that records the identified risks, their causes, impacts, likelihood, responses, andstatus. A risk register is a vital tool for IT risk management, as it helps to track and monitor the risks throughout their lifecycle, and to communicate the risks to the relevant stakeholders. However, a risk register is only useful if it reflects the current situation and environment of the organization. Therefore, the risk register should be regularly updated to capture any changes in the risk profile, such as new risks, resolved risks, modified risks, or escalated risks. Updating the risk register will help to ensure that the risk management process is effective and efficient, and that the risk responses are appropriate and timely. References = IT Risk Management - Basics and Best Practices
Which of the following is the BEST key control indicator (KCI) for risk related to IT infrastructure failure?
Options:
Number of times the recovery plan is reviewed
Number of successful recovery plan tests
Percentage of systems with outdated virus protection
Percentage of employees who can work remotely
Answer:
BExplanation:
A key control indicator (KCI) is a metric that provides information on the extent to which a given control is meeting its intended objectives in terms of loss prevention, reduction, etc. A KCI should have an explicit relationship to both the specific control and the specific risk against which the control has been implemented. For risk related to IT infrastructure failure, a possible control is to have a recovery plan that can restore the critical IT services and minimize the impact of the failure. A KCI that can measure the effectiveness of this control is the number of successful recovery plan tests, which indicates how well the recovery plan can be executed in a real scenario. The higher the number of successful tests, the lower the risk of IT infrastructure failure. Therefore, this is the best KCI among the given options. References =
Integrating KRIs and KPIs for Effective Technology Risk Management
Key Control Indicator (KCI) - CIO Wiki
Infrastructure Issues: Understanding and Mitigating Risks
A risk practitioner recently discovered that sensitive data from the production environment is required for testing purposes in non-production environments. Which of the following i the BEST recommendation to address this situation?
Options:
Enable data encryption in the test environment
Implement equivalent security in the test environment.
Prevent the use of production data for test purposes
Mask data before being transferred to the test environment.
Answer:
DExplanation:
Masking data before being transferred to the test environment is the best recommendation to address the situation where sensitive data from the production environment is required for testing purposes in non-production environments. Data masking is a technique that replaces sensitive data elements with realistic but fictitious data, preserving the format, structure, and meaning of the original data. Data masking ensures that the test data is sufficiently anonymized and de-identified, while still maintaining its functionality and validity for testing purposes. Data masking also reduces the risk of data leakage, exposure, or breach in the test environment, which may have lower security controls than the production environment. The other options are not the best recommendations, as they do not adequately protect the sensitive data or meet the testingrequirements. Enabling data encryption in the test environment may protect the data from unauthorized access, but it does not prevent the data from being decrypted by authorized users who may misuse or mishandle it. Implementing equivalent security in the test environment may be costly, complex, or impractical, and it may not be feasible to replicate the same level of security controls as in the production environment. Preventing the use of production data for test purposes may not be possible or desirable, as production data may be required to ensure the accuracy, reliability, and quality of the testing results. References = P = NP: Cloud dataprotection in vulnerable non-production environments …; Data masking secures sensitive data in non-production environments …; CRISC EXAM TOPIC 2 LONG Flashcards | Quizlet
A root because analysis indicates a major service disruption due to a lack of competency of newly hired IT system administrators Who should be accountable for resolving the situation?
Options:
HR training director
Business process owner
HR recruitment manager
Chief information officer (CIO)
Answer:
DExplanation:
The person who should be accountable for resolving the situation where a root cause analysis indicates a major service disruption due to a lack of competency of newly hired IT system administrators is the chief information officer (CIO). The CIO is the senior executive who is responsible for the overall management and governance of the IT function within the organization, including the IT strategy, objectives, policies, processes, and resources. The CIO is also accountable for the performance and value of the IT services and systems, and for ensuring that they meet the needs and expectations of the business and its stakeholders. The CIO should be accountable for resolving the situation, because it involves a major IT service disruption that could affect the organization’s operations and reputation, and because it is related to the IT staff competency and capability, which are under the CIO’s authority and responsibility. The other options are not as accountable as the CIO, although they may have some roles or involvement inthe situation. The HR training director, the business process owner, and the HR recruitment manager are not directly responsible for the IT function or the IT service delivery, and they may not have the authority or the expertise to resolve the situation. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.1.1, page 2-3.
Which of the following activities would BEST contribute to promoting an organization-wide risk-aware culture?
Options:
Performing a benchmark analysis and evaluating gaps
Conducting risk assessments and implementing controls
Communicating components of risk and their acceptable levels
Participating in peer reviews and implementing best practices
Answer:
CExplanation:
A risk-aware culture is a culture that recognizes, understands, and values the importance of risk management in achieving the organization’s objectives and goals. A risk-aware culture is also a culture that supports and encourages the identification, assessment, response, and monitoring of risks across the organization, as well as the sharing and learning of risk information and best practices. One of the activities that would best contribute to promoting an organization-wide risk-aware culture is communicating components of risk and their acceptable levels. This is a technique to inform and educate the stakeholders and decision makers about the nature and scope of the risks that the organization faces, as well as the criteria and standards that the organization uses to measure and manage the risks. Communicating components of risk and their acceptable levels can help to increase the awareness and understanding of the risks and their impact on the organization’s performance and value, as well as to align the expectations and behaviors of the stakeholders and decision makers with the organization’s risk appetite and tolerance. Communicating components of risk and their acceptable levels can also help to foster a transparent and collaborative environment for risk management, where the stakeholders and decision makers can openly discuss and address the risks and their implications, as well as to provide and receive feedback and support. The other options are not the best activities to promote an organization-wide risk-aware culture, although they may be relevant and useful. Performing a benchmark analysis and evaluating gaps is a technique to compare and improve the organization’s risk management process and performance with the industry standards or best practices, as well as to identify and close the gaps or weaknesses in the organization’s risk management capabilities or maturity. However, this technique does not necessarily promote a risk-aware culture, as it focuses on the process and performance of risk management, not the attitude and behavior of risk management. Conducting risk assessments and implementing controls is a technique to identify and analyze the risks that the organization faces, as well as to select and execute the appropriate actions to address the risks, such as avoiding, transferring, mitigating, or accepting the risks. However, this technique does not directly promote a risk-aware culture, as it focuses on the actions and outcomes of risk management, not the values and beliefs of risk management. Participating in peer reviews and implementing best practices is a technique to evaluate and enhance the quality and effectiveness of the organization’s risk management activities anddeliverables, as well as to adopt and apply the proven and successful methods or solutions for risk management. However, this technique does not effectively promote a risk-aware culture, as it focuses on the improvement and optimization of risk management, not the communication and collaboration of risk management. References = CRISC Review Manual, pages 22-231; CRISC Review Questions, Answers & Explanations Manual, page 982; The 6 keyelements to creating and maintaining a good risk culture3; How to increase risk awareness - Project Management Institute4
To implement the MOST effective monitoring of key risk indicators (KRIs), which of the following needs to be in place?
Options:
Threshold definition
Escalation procedures
Automated data feed
Controls monitoring
Answer:
AExplanation:
Key risk indicators (KRIs) are the metrics or measures that provide information and insight on the level and trend of the risks that may affect the organization’s objectives and operations. KRIscan help the organization to monitor and communicate the risks, and to support the decision making and planning for the risk management.
To implement the most effective monitoring of KRIs, one of the essential elements that needs to be in place is threshold definition, which is the process of establishing and specifying the acceptable or tolerable ranges or limits for the KRIs, based on the organization’s risk appetite and tolerance. Threshold definition can help the organization to monitor KRIs by providing the following benefits:
It can enable the comparison and evaluation of the actual or current values of the KRIs with the expected or desired values of the KRIs, and to identify and quantify the deviations or variations that may indicate the changes or developments in the risk level or performance.
It can trigger the alerts or notifications when the values of the KRIs exceed or fall below the thresholds, and to initiate the appropriate actions or responses to address or correct the risks and their impacts.
It can provide useful references and benchmarks for the alignment and integration of the KRIs with the organization’s risk management function, and for the compliance with the organization’s risk policies and standards.
The other options are not the essential elements that need to be in place to implement the most effective monitoring of KRIs, because they do not address the main purpose and benefit of threshold definition, which is to establish and specify the acceptable or tolerable ranges or limits for the KRIs.
Escalation procedures are the processes and guidelines for communicating and sharing the information and status of the risks and their responses among the relevant stakeholders, and for escalating or transferring the risks and their responses to the appropriate levels orparties when necessary or required. Escalation procedures can help the organization to monitor KRIs by ensuring the awareness and involvement of the stakeholders, but they are not the essential elements that need to be in place, because they do not establish and specify the acceptable or tolerable ranges or limits for the KRIs.
Automated data feed is the process of using a software tool or system to collect and transmit the data or information that are related or relevant to the KRIs, and to ensure the accuracy, reliability, and timeliness of the data or information. Automated data feed can help the organization to monitor KRIs by providing the data or information that are necessary and relevant for the KRIs, but they are not the essential elements that need to be in place, because they do not establish and specify the acceptable or tolerable ranges or limits for the KRIs.
Controls monitoring is the process of verifying and validating the adequacy and effectiveness of the controls that are intended to ensure the confidentiality, integrity, availability, and reliabilityof the information systems and resources that are affected by the risks. Controls monitoring can help the organization to monitor KRIs by providing the assurance and evidence on the performance and compliance of the controls, but they are not the essential elements that need to be in place, because they do not establish and specify the acceptable or tolerable ranges or limits for the KRIs. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 206
CRISC Practice Quiz and Exam Prep
Which of the following is a PRIMARY benefit of creating an organizational code of conduct?
Options:
Clear expectations for employee behavior
Identification of ethical risk facing the organization
Improvement in workforce productivity
Enhanced integrity of management
Answer:
AExplanation:
The correct answer isAbecause the primary benefit of an organizationalcode of conductis to establishclear expectations for employee behavior. A code of conduct communicates the standards of ethical and professional behavior expected within the organization and provides a common basis for decision-making, accountability, and awareness.
The other options are less appropriate:
B. Identification of ethical risk facing the organizationmay result indirectly, but this is not the primary purpose of a code of conduct.
C. Improvement in workforce productivitycould occur as a secondary effect, but it is not the main benefit.
D. Enhanced integrity of managementmay be supported, but the code of conduct applies across the organization and primarily clarifies expected behavior.
Exact Extracts supporting the answer:
“The most effective way to support adherence to an enterprise ' s code of ethics is by ensuring periodic training evaluation and attestation of employees.”
“The most significant benefit when stakeholders promote and follow professional ethics is that it increases risk management effectiveness within an enterprise.”
“The best proactive approach for practicing professional ethics within an enterprise is to provide ethics awareness training.”
“Developing and practicing ethical behavior within an enterprise contributes the most to building the risk culture.”
These extracts support that ethics-related governance mechanisms such as a code of conduct are intended to guide and reinforce expected behavior throughout the enterprise. Therefore, the primary benefit isclear expectations for employee behavior.
===========
Which of the following is MOST helpful in defining an early-warning threshold associated with insufficient network bandwidth’’?
Options:
Average bandwidth usage
Peak bandwidth usage
Total bandwidth usage
Bandwidth used during business hours
Answer:
BExplanation:
Peak bandwidth usage is the most helpful in defining an early-warning threshold associated with insufficient network bandwidth. Peak bandwidth usage is the maximum amount of data that istransferred over a network connection at a given time. It indicates the highest demand and stress on the network resources and capacity. By monitoring the peak bandwidth usage, the organization can identify the potential bottlenecks, slowdowns, and disruptions that may occur due to insufficient network bandwidth. The organization can also plan and allocate the network bandwidth accordingly to meet the peak demand and avoid service degradation. The other options are not as helpful as peak bandwidth usage, as they do not reflect the actual or potential network performance issues that may arise due to insufficient network bandwidth. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.3: Key Risk Indicators, page 197.
Which of the following has the MOST validity for conducting risk assessments?
Options:
Internal control effectiveness measured through inference from external assessment
Control effectiveness determined through subject matter expertise estimation
Inferences of internal control effectiveness from peer reports
Internal control effectiveness measured through direct testing
Answer:
DExplanation:
The correct answer isDbecauseinternal control effectiveness measured through direct testingprovides the most valid basis for conducting risk assessments. Direct testing produces objective evidence about whether controls are designed appropriately and operating effectively. It is stronger and more reliable than estimates, external inference, or peer-based assumptions because it evaluates the actual control environment of the organization.
The other options are less valid:
A. Internal control effectiveness measured through inference from external assessmentmay provide useful insight, but it is indirect and may not reflect the organization’s actual internal control performance.
B. Control effectiveness determined through subject matter expertise estimationcan support assessment, but it remains judgment-based rather than evidence-based.
C. Inferences of internal control effectiveness from peer reportsare indirect and may not be relevant to the organization’s own environment, systems, or risk exposure.
Exact Extracts supporting the answer:
“To best identify information systems control deficiencies gap analysis is used. It highlights the discrepancies between desired control objectives and actual control design and operational effectiveness.”
“The MOST important criterion when reviewing information security controls is ensuring that the controls are effectively addressing risk.”
“The BEST way to ensure that an information systems control is appropriate and effective is to verify that the risk associated with the control is mitigated.”
“To determine control effectiveness it ' s essential to verify that the control meets the test results of intended objectives.”
“Testing the control to ensure that the risk has been adequately mitigated is the best action to take once a new control has been implemented validating that the control effectively addresses the identified risk.”
These extracts support that the most valid evidence of control effectiveness comes from actual verification and testing, not from assumptions or indirect sources. Therefore,direct testingprovides the strongest validity for risk assessments.
===========
An organization automatically approves exceptions to security policies on a recurring basis. This practice is MOST likely the result of:
Options:
a lack of mitigating actions for identified risk
decreased threat levels
ineffective service delivery
ineffective IT governance
Answer:
DExplanation:
IT governance is the process of ensuring that IT supports the organization’s objectives and strategies, and that IT risks are managed appropriately. IT governance involves defining the roles, responsibilities, and accountabilities of the IT stakeholders, establishing the IT policies, standards, and procedures, and monitoring and evaluating the IT performance and outcomes1.
An organization that automatically approves exceptions to security policies on a recurring basis is most likely the result of ineffective IT governance, because it indicates that the organization:
Lacks a clear and consistent IT strategy and direction, and does not align IT with the business goals and needs
Fails to implement and enforce the IT policies, standards, and procedures, and does not ensure the compliance and accountability of the IT users and providers
Neglects to identify and assess the IT risks, and does not implement the appropriate risk responses and controls
Does not monitor and measure the IT performance and outcomes, and does not review and improve the IT processes and practices23
The other options are not the most likely results of ineffective IT governance, but rather some of the possible causes or consequences of it. A lack of mitigating actions for identified risk is a possible consequence of ineffective IT governance, as it implies that the organization does not have a systematic and proactiveapproach to IT risk management, and does not address the IT risks in a timely and effective manner. Decreased threat levels is a possible cause of ineffective IT governance, as it may create a false sense of security and complacency, and reduce the motivation and urgency to implement and follow the IT policies, standards, and procedures. Ineffective service delivery is a possible consequence of ineffective IT governance, as it means that the organization does not deliver the IT services that meet the expectations and requirements of the customers and stakeholders, and does not ensure the quality and reliability of the IT services. References =
IT Governance - ISACA
IT Governance: What It Is and Why You Need It
IT Governance: The Benefits of an Effective Enterprise IT Governance Framework
[CRISC Review Manual, 7th Edition]
Which of the following provides the MOST insight into an organization ' s IT threat exposure?
Options:
Industry benchmarks
Risk assessment reports
External audit results
Tabletop exercises
Answer:
BExplanation:
Risk assessment reports are tailored to the organization and identify specific vulnerabilities, threats, and potential impacts. They provide actionable insights into IT risk exposure that can be used for prioritization and mitigation.
Which of the following BEST enables effective risk reporting to the board of directors?
Options:
Presenting case studies of breaches from other similar organizations
Mapping risk scenarios to findings identified by internal audit
Communicating in terms that correlate to corporate objectives and business value
Reporting key metrics that indicate the efficiency and effectiveness of risk governance
Answer:
CExplanation:
Effective risk reporting to the board of directors requires communication that aligns with the organization ' s strategic goals and business value. By correlating risk information to corporate objectives, the board can better understand the implications of risks on the organization ' s performance and make informed decisions. This approach ensures that risk discussions are relevant and meaningful at the executive level.
Which of the following presents the GREATEST concern associated with the
use of artificial intelligence (Al) systems?
Options:
Al systems need to be available continuously.
Al systems can be affected by bias.
Al systems are expensive to maintain.
Al systems can provide false positives.
Answer:
BWhich of the following is the BEST key performance indicator (KPI) to measure the effectiveness of IT policies? The number of:
Options:
IT policy exceptions granted.
Senior management approvals.
Key technology controls covered by IT policies.
Processes covered by IT policies.
Answer:
CWhile reviewing a contract of a cloud services vendor, it was discovered that the vendor refuses to accept liability for a sensitive data breach. Which of the following controls will BES reduce the risk associated with such a data breach?
Options:
Ensuring the vendor does not know the encryption key
Engaging a third party to validate operational controls
Using the same cloud vendor as a competitor
Using field-level encryption with a vendor supplied key
Answer:
AExplanation:
Encryption is a technique that transforms data into an unreadable format using a secret key, so that only authorized parties can access and decrypt the data. Encryption can help to protectsensitive data from unauthorized access or disclosure, especially when the data is stored or transmitted in the cloud1.
Ensuring the vendor does not know the encryption key is a control that will best reduce the risk associated with a data breach, because it can help to:
Prevent the vendor from accessing or disclosing the sensitive data, intentionally or unintentionally
Limit the exposure or impact of the data breach, even if the vendor’s systems or networks are compromised by hackers or malicious insiders
Maintain the confidentiality and integrity of the sensitive data, regardless of the vendor’s liability or responsibility
Enhance the trust and confidence of the customers and stakeholders, who may be concerned about the vendor’s refusal to accept liability for a data breach23
The other options are not as effective as ensuring the vendor does not know the encryption key for reducing the risk associated with a data breach. Engaging a third party to validate operational controls is a control that can help to verify and improve the vendor’s security practices and processes, but it does not guarantee that the vendor will prevent or respond to a data breach adequately or timely. Using the same cloud vendor as a competitor is not a control, but rather a business decision that may increase the risk associated with a data breach, as the vendor may have access to or disclose the sensitive data of both parties, or may favor one party over the other. Using field-level encryption with a vendor supplied key is a control that can help to encrypt specific fields or columns of data, such as names, addresses, or credit card numbers, but it does not prevent the vendor from accessing or disclosing the data, as the vendor has the encryption key4. References =
Encryption - ISACA
Cloud Encryption: Using Data Encryption in The Cloud
Cloud Encryption: Why You Need It and How to Do It Right
Field-Level Encryption - ISACA
[CRISC Review Manual, 7th Edition]
The maturity of an IT risk management program is MOST influenced by:
Options:
the organization ' s risk culture
benchmarking results against similar organizations
industry-specific regulatory requirements
expertise available within the IT department
Answer:
AExplanation:
The maturity of an IT risk management program is most influenced by the organization’s risk culture, as this reflects the shared values, beliefs, and attitudes that shape how the organization perceives and responds to risk. The risk culture determines the level of awareness, commitment, and involvement of the stakeholders in the IT risk management process, as well as the degree of integration and alignment with the enterprise’s objectives and strategy. A mature IT risk management program requires a strong and positive risk culture that fosters trust, collaboration, and accountability among the stakeholders, and supports continuous improvement and learning. The other options are not the most influential factors for the maturity of an IT risk management program, although they may have some impact or relevance. Benchmarking results against similar organizations can provide useful insights and comparisons, but they do not necessarily reflect the organization’s own risk culture or context. Industry-specific regulatory requirements can impose certain standards and expectations, but they do not guarantee the effectiveness or efficiency of the IT risk management program. Expertise available within the IT department can enhance the technical and operational aspects of the IT risk management program, but it does not ensure the strategic and cultural alignment with the enterprise. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, page 23.
Who is MOST important lo include in the assessment of existing IT risk scenarios?
Options:
Technology subject matter experts
Business process owners
Business users of IT systems
Risk management consultants
Answer:
BExplanation:
Business process owners are the most important to include in the assessment of existing IT risk scenarios, as they have the authority and responsibility to manage the business processes and their associated risks and controls, and to provide the business perspective and requirements for the IT risk scenarios. Technology subject matter experts, business users of IT systems, and risk management consultants are not the most important to include, as they may have different roles and responsibilities related to the technical, operational, or advisory aspects of IT risk scenarios, respectively, but they do not own the business processes or the IT risk scenarios. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following is a crucial component of a key risk indicator (KRI) to ensure appropriate action is taken to mitigate risk?
Options:
Management intervention
Risk appetite
Board commentary
Escalation triggers
Answer:
DExplanation:
The best answer is D. Escalation triggers. Escalation triggers are predefined thresholds or conditions that indicate when a key risk indicator (KRI) has reached a critical level that requires immediate attention or action. Escalation triggers can be based on quantitative or qualitative measures, such as percentages, scores, ratings, or colors. Escalation triggers can help to ensure appropriate action is taken to mitigate risk, because they provide clear and timely signals that alert the risk owners, managers, and other stakeholders of the need to review and revise the risk response plan, or to implement additional or alternative controls. Escalation triggers can also help to communicate and report the risk status and the risk response actions to the senior management and the board, and to obtain their support and approval, if needed. The otheroptions are not the best answer, although they may be related or influential to the KRI and the risk mitigation. Management intervention is a part of the risk response process, which involves the actions and decisions taken by the management to address the risk, such as approving, implementing, or monitoring the controls. Management intervention can help to mitigate risk, but it is not a component of the KRI, rather it is a consequence or a result of the escalation triggers. Risk appetite is the amount and type of risk that an organization is willing to accept or pursue in order to achieve its objectives. Risk appetite can help to define and align the KRI and the escalation triggers with the organizational strategy and culture, but it is not a component of the KRI, rather it is a factor or a driver of the KRI. Board commentary is a part of the risk reporting process, which involves the feedback and guidance provided by the board on the risk management process and performance. Board commentary can help to improve and enhance the KRI and the risk mitigation, but it is not a component of the KRI, rather it is a source or a resource of the KRI. References = Key Risk Indicators: A Practical Guide | SafetyCulture, KRI Framework for Operational Risk Management | Workiva
Which of the following scenarios is MOST important to communicate to senior management?
Options:
Accepted risk scenarios with detailed plans for monitoring
Risk scenarios that have been shared with vendors and third parties
Accepted risk scenarios with impact exceeding the risk tolerance
Risk scenarios that have been identified, assessed, and responded to by the risk owners
Answer:
CExplanation:
The scenario that is most important to communicate to senior management is the accepted risk scenarios with impact exceeding the risk tolerance, as it indicates a significant risk issue or breach that may affect the achievement of the organizational objectives, and may require a review or escalation action. The other options are not the most important scenarios, as they may not indicate a risk issue or breach, but rather a risk monitoring, sharing, or management activity, respectively, that may not affect the organizational objectives directly or significantly. References = CRISC Review Manual, 7th Edition, page 109.
An organization has decided to postpone the assessment and treatment of several risk scenarios because stakeholders are unavailable. As a result of this decision, the risk associated with these new entries has been;
Options:
mitigated
deferred
accepted.
transferred
Answer:
CExplanation:
The result of postponing the assessment and treatment of several risk scenarios is that the risk associated with these new entries has been accepted. Risk acceptance is a risk response strategy that involves acknowledging the existence of a risk and deciding not to take any action to reduce its likelihood or impact. By postponing the assessment and treatment of the risk scenarios, the organization is implicitly accepting the risk and its consequences. Risk mitigation, deferral, and transfer are other possible risk response strategies, but they are not applicable in this case. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 9; CRISC Review Manual, 6th Edition, page 137.
An identified high probability risk scenario involving a critical, proprietary business function has an annualized cost of control higher than the annual loss expectancy. Which of the following is the BEST risk response?
Options:
Mitigate
Accept
Transfer
Avoid
Answer:
BExplanation:
The best risk response for an identified high probability risk scenario involving a critical, proprietary business function with an annualized cost of control higher than the annual loss expectancy is to accept the risk. Accepting the risk means acknowledging the risk but choosing not to take any specific action to address it. This strategy is suitable when the cost of implementing controls exceeds the potential loss, as in this scenario. The organization recognizes the risk, but the cost-benefit analysis suggests that the potential loss is acceptable given the higher cost of control. The other options are not the best risk responses, as they may not befeasible, practical, or cost-effective in this scenario. Mitigating the risk means reducing the risk by implementing controls or measures to minimize its potential impact, but this would increase the cost of control, which is already higher than the annual loss expectancy. Transferring the risk means shifting the risk to another party, typically through insurance or contracts, but this may not be possible or advisable for a critical, proprietary business function, and it may also increase the overall cost burden. Avoiding the risk means eliminating the risk entirely by not engaging in the activity that poses the risk, but this may disrupt essential business operations and potentially result in other adverse consequences. References = CRISC Exam:Best Risk Response for High Probability Risk Scenario; Risk Response Plan in Project Management: Key Strategies & Tips; Chapter 19: Summarizing Risk Management Concepts
Which of the following would BEST help an enterprise define and communicate its risk appetite?
Options:
Gap analysis
Risk assessment
Heat map
Risk register
Answer:
DExplanation:
The best way to help an enterprise define and communicate its risk appetite is to use a risk register, which is a document that records and summarizes the key information and data about the identified risks and the risk responses1. A risk register can help to:
Define the risk appetite, which is the amount and type of risk that the enterprise is willing to accept or pursue in order to achieve its objectives2. The risk register can include the risk appetite statement, which is a clear and concise expression of the enterprise’s risk preferences and boundaries3.
Communicate the risk appetite, which is the process of sharing and informing the risk appetite to the relevant stakeholders, such as the board, the management, the employees, or the customers4. The risk register can be used as a communication tool, which can provide a consistent and transparent view of the enterprise’s risk profile and performance5.
The other options are not the best ways to help an enterprise define and communicate its risk appetite, because:
Gap analysis is a technique that compares the current state and the desired state of a process, system, or organization, and identifies the gaps or differences between them6. Gap analysis can help to assess the alignment or misalignment of the enterprise’s risk appetite with its risk level, but it does not help to define or communicate the risk appetite itself.
Risk assessment is a process that estimates the probability and impact of the risks, and prioritizes the risks based on their significance and urgency. Risk assessment can help to identify andanalyze the risks that may affect the enterprise’s objectives, but it does not help to define or communicate the risk appetite itself.
Heat map is a graphical representation that uses colors to indicate the level or intensity of a variable, such as risk. Heat map can help to visualize and compare the risks based on their probability and impact, but it does not help to define or communicate the risk appetite itself.
References =
Risk Register - CIO Wiki
Risk Appetite - CIO Wiki
Risk Appetite Statement - CIO Wiki
Risk Communication - CIO Wiki
Risk Reporting - CIO Wiki
Gap Analysis - CIO Wiki
[Risk Assessment - CIO Wiki]
[Heat Map - CIO Wiki]
[Risk and Information Systems Control documents and learning resources by ISACA]
A recent risk workshop has identified risk owners and responses for newly identified risk scenarios. Which of the following should be the risk practitioner s NEXT step? r
Options:
Prepare a business case for the response options.
Identify resources for implementing responses.
Develop a mechanism for monitoring residual risk.
Update the risk register with the results.
Answer:
DExplanation:
The risk practitioner’s next step after identifying risk owners and responses for newly identified risk scenarios in a recent risk workshop is to update the risk register with the results, as it involves documenting and communicating the risk information and decisions, and maintaining the accuracy and completeness of the risk register. Preparing a business case for the response options, identifying resources for implementing responses, and developing a mechanism for monitoring residual risk are possible steps, but they are not the next step, as they require the prior update of the risk register with the new risk information and decisions. References = CRISC Review Manual, 7th Edition, page 109.
The implementation of a risk treatment plan will exceed the resources originally allocated for the risk response. Which of the following should be the risk owner ' s NEXT action?
Options:
Perform a risk assessment.
Accept the risk of not implementing.
Escalate to senior management.
Update the implementation plan.
Answer:
CExplanation:
A risk treatment plan is a document that outlines the actions and resources required to implement the chosen risk response for a specific risk1. A risk response is a strategy or action that is taken or planned tomitigate or eliminate the risk, such as avoiding, transferring, reducing, or accepting the risk2. A risk owner is a person or entity that has the authority and accountability for a risk and its management3. If the implementation of a risk treatment plan will exceed the resources originally allocated for the risk response, the risk owner’s next action should be to escalate to senior management, which is the group of senior leaders who have the authority and accountability for the organization’s performance and governance4. By escalating to senior management, the risk owner can inform and consult them about the situation and the implications, and seek their guidance and approval for the necessary adjustments or alternatives. Escalating to senior management can also help to ensure that the risk treatment plan is aligned with the organization’s strategy, vision, and mission, and that the risk response is consistent with the organization’s risk appetite and tolerance5. Performing a risk assessment, accepting the risk of not implementing, and updating the implementation plan are not the best choices for the risk owner’s next action, as they do not provide the same level of communication and consultation as escalating to senior management. Performing a risk assessment is a process that involves identifying, analyzing, and evaluating the risks and their potential impacts on the organization’s objectives and performance6. Performing a risk assessment can help to update and validate the risk information and the risk treatment plan, but it does not address the issue of the resource shortfall or the stakeholder expectations. Acceptingthe risk of not implementing is a decision that involves acknowledging and tolerating the risk or its impact without taking anyaction to reduce or eliminate it7. Accepting the risk of not implementing can help to avoid the additional cost and effort of the risk treatment plan, but it does not consider the potential consequences or the stakeholder interests. Updating the implementation plan is a process that involves revising and modifying the plan for executing the risk treatment plan, such as the scope,schedule, budget, or quality8. Updating the implementation plan can help to reflect the changes and updates in the risk treatment plan, but it does not resolve the problem of the resource gap or the stakeholder approval. References = 1: Risk Treatment and Response Plans - UNECE2: Risk Response Strategy and Contingency Plans - ProjectManagement.com3: [Risk Ownership - Risk Management] 4: [Senior Management - Definition, Roles and Responsibilities] 5: [Risk Appetite and Tolerance - ISACA] 6: [Risk Assessment - an overview | ScienceDirect Topics] 7: [Risk Acceptance - an overview | ScienceDirect Topics] 8: [Implementation Plan - an overview | ScienceDirect Topics] : [Risk and Information Systems Control Study Manual, Chapter 3: Risk Response, Section 3.1: Risk Response Options, pp. 113-115.] : [Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.1: Control Design, pp. 233-235.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.2: Control Implementation, pp. 243-245.] : [Risk and Information Systems Control Study Manual, Chapter 5: Information Systems Control Design and Implementation, Section 5.3: Control Monitoring and Maintenance, pp. 251-253.]
An organization outsources the processing of us payroll data A risk practitioner identifies a control weakness at the third party trial exposes the payroll data. Who should own this risk?
Options:
The third party ' s IT operations manager
The organization ' s process owner
The third party ' s chief risk officer (CRO)
The organization ' s risk practitioner
Answer:
BExplanation:
The organization’s process owner should own the risk of exposing the payroll data due to a control weakness at the third party, because the process owner is the person who is responsible for the business process that generates, uses, or transfers the payroll data. The process owner should also ensure that the third party complies with the contractual obligations and service level agreements that define the expected performance and security standards of the payroll data processing. The other options are not the correct answers, because they are not the primary owners of the risk, although they may also be involved in the risk management process. The third party’s IT operations manager, the third party’s chief risk officer (CRO), and the organization’s risk practitioner are examples of secondary owners or stakeholders of the risk, who may provide support, guidance, or oversight to the risk owner, but they are not accountable for the risk or the risk response strategy. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
The MAIN reason for prioritizing IT risk responses is to enable an organization to:
Options:
determine the risk appetite.
determine the budget.
define key performance indicators (KPIs).
optimize resource utilization.
Answer:
DExplanation:
Optimizing resource utilization is the main reason for prioritizing IT risk responses, as it helps to allocate resources to the most critical and urgent risks. The other options are not the main reasons for prioritizing IT risk responses, although they may be related to the process.
An organization is participating in an industry benchmarking study that involves providing customer transaction records for analysis Which of the following is the MOST important control to ensure the privacy of customer information?
Options:
Nondisclosure agreements (NDAs)
Data anonymization
Data cleansing
Data encryption
Answer:
BExplanation:
Data anonymization is the most important control to ensure the privacy of customer information when participating in an industry benchmarking study that involves providing customer transaction records for analysis. Data anonymization is the process of removing or modifying personally identifiable information (PII) from data sets, such as names, addresses, phone numbers, email addresses, etc., so that the data cannot be traced back to specific individuals.Data anonymization protects the confidentiality and privacy of customers, while still allowing for meaningful analysis and comparison of data. Nondisclosure agreements (NDAs), data cleansing, and data encryption are also useful controls, but they do not eliminate the risk of data breaches or unauthorized access to PII. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.3.1, page 3-21.
An organization is unable to implement a multi-factor authentication requirement until the next fiscal year due to budget constraints. Consequently, a policy exception must be submitted. Which of the following is MOST important to include in the analysis of the exception?
Options:
Sections of the policy that may justify not implementing the requirement
Risk associated with the inability to implement the requirement
Budget justification to implement the new requirement during the current year
Industry best practices with respect to implementation of the proposed control
Answer:
BExplanation:
The most important factor to include in the analysis of the policy exception is the risk associated with the inability to implement the multi-factor authentication requirement. A policy exception is a temporary orpermanent deviation from the established policies or standards of the organization, due to various reasons, such as budget constraints, technical limitations, or business needs. A policy exception must be submitted and approved by the appropriate authority, and it must include a clear and comprehensive analysis of the rationale, impact, and mitigation of the exception. The risk associated with the inability to implement the multi-factor authentication requirement is the most important factor to include in the analysis, because it evaluates the probability and severity of potential threats or incidents that could exploit the lack of multi-factor authentication, such as unauthorized access, data breach, or identity theft. The risk analysis also helps to justify the need and urgency of the policy exception, and to propose alternative or compensating controls to reduce or transfer the risk, such as password policies, access restrictions, or encryption. The other options are not the most important factor, although they may be relevant or supportive to the policy exception analysis. Sections of the policy that may justify not implementing the requirement are the clauses or provisions in the policy that allow or enable the policy exception, such as exemptions, waivers, or variances. These sections can help to validate the legitimacy and feasibility of the policy exception, but they do not assess the risk or the impact of the exception. Budget justification to implement the new requirement during the current year is the explanation and evidence of the financial resources and constraints that affect the implementation of the multi-factor authentication requirement. This justification can help to demonstrate the cost-benefit and return on investment of the requirement, but it does not measure the risk or the mitigation of the exception. Industry best practices with respect to implementation of the proposed control are the proven methods and standards that are adopted by the leading organizations in a specific field or sector for implementing the multi-factor authentication requirement. These best practices can help to benchmark and improve the quality and effectiveness of the requirement, but they do not quantify the risk or the impact of the exception. References = Policy Exception Management - ISACA, Multi-Factor Authentication Policy - University of Arkansas, Common Conditional Access policy: Require MFA for all users
Which of the following is the MOST important factor when deciding on a control to mitigate risk exposure?
Options:
Relevance to the business process
Regulatory compliance requirements
Cost-benefit analysis
Comparison against best practice
Answer:
CExplanation:
The most important factor when deciding on a control to mitigate risk exposure is the cost-benefit analysis. This is a process that compares the costs and benefits of implementing a control, and determines whether the control is worth the investment. A cost-benefit analysis helps to ensure that the control is efficient and effective in reducing the risk to an acceptable level, and that it does not introduce new risks or adversely affect other objectives. A cost-benefit analysis also helps to prioritize the controls based on their value and feasibility, and to allocate the resources accordingly. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.2.5, page 1861
Which of the following is necessary to enable an IT risk register to be consolidated with the rest of the organization’s risk register?
Options:
Risk taxonomy
Risk response
Risk appetite
Risk ranking
Answer:
AExplanation:
According to the CRISC Review Manual, risk taxonomy is the system of classification and categorization of risks based on common characteristics and attributes. Risk taxonomy is necessary to enable an IT risk register to be consolidated with the rest of the organization’s risk register, because it helps to ensure consistency, comparability, and alignment of the risks across the organization. Risk taxonomy also helps to facilitate the communication, reporting, and aggregation of the risks. The other options are not the correct answers, because they are not essential for consolidating the risk registers. Risk response is the action taken to address the risk, which may vary depending on the risk level and strategy. Risk appetite is the amount and type of risk that an organization is willing to accept, which may differ across the organization’s units and functions. Risk ranking is the process of prioritizing the risks based on their impact and likelihood, which may change over time and context. References = CRISC Review Manual, 7th Edition, Chapter 2, Section 2.1.2, page 69.
An organization has committed to a business initiative with the knowledge that the risk exposure is higher than the risk appetite. Which of the following is the risk practitioner ' s MOST important action related to this decision?
Options:
Recommend rejection of the initiative.
Change the level of risk appetite.
Document formal acceptance of the risk.
Initiate a reassessment of the risk.
Answer:
CExplanation:
Formal acceptance of the risk is critical when the risk exposure exceeds the risk appetite, as it ensures accountability and acknowledges the decision at the appropriate level. Documenting acceptance involves communicating the potential impacts and obtaining agreement from senior stakeholders. This process aligns with theRisk Response and Reportingdomain in CRISC, emphasizing clear documentation and communication of risks for decision-making.
It is MOST important that entries in an organization’s risk register be updated:
Options:
when the key risk indicator (KRI) threshold has been reached.
when required by internal audit.
prior to a risk review.
when aspects of the risk scenario change.
Answer:
DExplanation:
The risk register is a living document. CRISC states it should be maintained so that it accurately reflects current risk conditions, including changes in threats, vulnerabilities, impacts, controls, and ownership. Therefore, it is most important to update entrieswhen aspects of the risk scenario change—for example, when a new control is implemented, business processes change, threat activity increases, or the magnitude of impact alters. Waiting until KRI thresholds are reached may delay updating until risk is already elevated. Updating only when internal audit requires it or just before a periodic review undermines real-time visibility and decision-making. Timely updates when the scenario changes support effective monitoring, reporting, and governance, ensuring that management decisions are based on current, not outdated, risk information.
A failure in an organization s IT system build process has resulted in several computers on the network missing the corporate endpoint detection and response (EDR) software. Which of the following should be the risk practitioner’s IMMEDIATE concern?
Options:
Multiple corporate build images exist.
The process documentation was not updated.
The IT build process was not followed.
Threats are not being detected.
Answer:
DWhich of the following BEST indicates that security requirements have been incorporated into the system development life cycle (SDLC)?
Options:
Comprehensive security training of developers
Validated security requirements and design documents
Completed user acceptance testing (UAT)
Compliance with laws and regulatory requirements
Answer:
BExplanation:
Validated security requirements and design documents demonstrate that security considerations have been integrated into the SDLC from the outset. This proactive approach ensures that security is embedded into system architecture and design, reducing vulnerabilities and enhancing overall system resilience.
Which of the following is MOST critical to the design of relevant risk scenarios?
Options:
The scenarios are based on past incidents.
The scenarios are linked to probable organizational situations.
The scenarios are mapped to incident management capabilities.
The scenarios are aligned with risk management capabilities.
Answer:
DExplanation:
Risk scenarios are hypothetical situations that describe potential events or actions that could affect the achievement of enterprise objectives. The design of relevant risk scenarios should consider the following factors: the risk appetite and tolerance of the enterprise, the key risk indicators and risk drivers, the potential impact and likelihood of the scenarios, and the alignment with the risk management capabilities of the enterprise. The scenarios should be realistic, plausible, and consistent with the enterprise’s context and objectives. The scenarios should also be reviewed and updated periodically to reflect changes in the internal and external environment. The alignment with the risk management capabilities is the most critical factor, as it ensures that the scenarios are relevant for the decision making and risk response processes of the enterprise. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.3.3.2, pp. 67-69.
What would be the MAIN concern associated with a decentralized IT function maintaining multiple risk registers?
Options:
Risk treatment efforts within the IT function may overlap one another.
Duplicate IT risk scenarios may be documented across the organization.
Aggregate risk within the IT function may exceed the organization ' s appetite.
Related IT risk scenarios in the IT function may be updated at different times.
Answer:
DA risk practitioner has been tasked with conducting a risk identification workshop with stakeholders to compile an IT risk profile. Which of the following would be MOST helpful in the brainstorming phase of this exercise?
Options:
List of issues and events from the risk register.
Internal audit reports with adverse findings.
IT control assessment results and trends.
Key risk indicators (KRIs) outside of appetite.
Answer:
AExplanation:
The BEST answer is A because a risk register is the direct repository of identified risk, issues, scenarios, impact, probability, mitigation action, and ownership. For a brainstorming workshop to compile an IT risk profile, previous issues and events from the risk register provide the most relevant starting point for identifying and discussing risk scenarios. The uploaded CRISC notes state that the risk register includes “risk scenario, date, description, impact, probability, risk score, mitigation action and owner,” and that preparation of a risk register begins in the risk identification process. They also state that the risk register is maintained as a repository of identified risk for decision-making.
ISACA’s CRISC outline places Risk Events , Risk Scenario Development and Evaluation , and Risk Register under Domain 2: Risk Assessment, supporting that this is a risk identification/risk assessment activity.
B, C, and D are useful inputs, but they are narrower. Audit findings and control assessment results focus mainly on control weaknesses, while KRIs outside appetite indicate monitored risk conditions. The risk register is broader and more directly aligned to brainstorming an IT risk profile.
===========
Where should a risk practitioner document the current state and desired future state of organizational risk?
Options:
Risk register
Risk action plan
Risk management strategy
Business continuity plan (BCP)
Answer:
CA business is conducting a proof of concept on a vendor ' s Al technology. Which of the following is the MOST important consideration for managing risk?
Options:
Use of a non-production environment
Adequate vendor support
Third-party management plan
Regular security updates
Answer:
AWhich of the following would be a risk practitioner ' s MOST important action upon learning that an IT control has failed?
Options:
Implement a replacement control.
Adjust residual risk rating.
Escalate to senior management.
Review compensating controls.
Answer:
DExplanation:
Upon discovering that an IT control has failed, the risk practitioner ' s most important action is to review compensating controls. This involves assessing whether other existing controls can mitigate the risk associated with the failed control. Evaluating compensating controls helps determine the immediate impact of the control failure and guides decisions on necessary remediation steps.
Which of the following would present the MOST significant risk to an organization when updating the incident response plan?
Options:
Obsolete response documentation
Increased stakeholder turnover
Failure to audit third-party providers
Undefined assignment of responsibility
Answer:
DExplanation:
The most significant risk to an organization when updating the incident response plan is the undefined assignment of responsibility. An incident response plan is a document that defines the roles, responsibilities, procedures, and resources for responding to an incident that could disrupt the normal operations of the organization, or compromise its assets, reputation, or compliance. An incident response plan should clearly assign the responsibility for each task and activity involved in the incident response process, such as detection, containment, analysis, eradication, recovery, and reporting. Undefined assignment of responsibility could lead to confusion, duplication, conflict, or omission among the stakeholders, and impair the effectiveness and efficiency of the incident response process. Undefined assignment of responsibility could also increase the risk of escalation, recurrence, or impact of the incident, and affect the accountability and performance of the organization. Obsolete response documentation, increased stakeholder turnover, and failure to audit third-party providers are also risks, but they are not as significant as undefined assignment of responsibility, as they do not directly affect the execution and outcome of the incident response process. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 130.
The MAJOR reason to classify information assets is
Options:
maintain a current inventory and catalog of information assets
determine their sensitivity and critical
establish recovery time objectives (RTOs)
categorize data into groups
Answer:
BExplanation:
Information asset classification is the process of assigning a level of sensitivity and criticality to an information asset based on its value, importance, and impact to the organization. The major reason to classify information assets is to determine their sensitivity and criticality, which are the measures of how confidential, proprietary, or sensitive the information is, and how essential, urgent, or time-sensitive the information is for the business operations. By determining the sensitivity and criticality of information assets, the organization can prioritize the protection and recovery of the information assets, implement the appropriate security controls and safeguards, comply with the regulatory and contractual requirements, and manage the information lifecycle and disposal. References = CRISC Review Manual, 7th Edition, page 74.
An effective control environment is BEST indicated by controls that:
Options:
minimize senior management ' s risk tolerance.
manage risk within the organization ' s risk appetite.
reduce the thresholds of key risk indicators (KRIs).
are cost-effective to implement
Answer:
BExplanation:
According to the CRISC Review Manual (Digital Version), an effective control environment is best indicated by controls that manage risk within the organization’s risk appetite, as this reflects the alignment of thecontrol objectives and activities with the organization’s strategic goals and risk preferences. The risk appetite is the amount and type of risk that the organization is willing to accept in pursuit of its objectives. Managing risk within the organization’s risk appetite helps to:
Balance the potential benefits and costs of risk-taking and risk response
Optimize the use of the organization’s resources and capabilities
Enhance the value and performance of the organization
Foster a risk-aware culture that supports the organization’s vision and mission
References = CRISC Review Manual (Digital Version), Chapter 2: IT Risk Assessment, Section 2.3: IT Risk Assessment Process, pp. 93-941
Which of the following should be the MOST important consideration when determining controls necessary for a highly critical information system?
Options:
The number of threats to the system
The organization ' s available budget
The number of vulnerabilities to the system
The level of acceptable risk to the organization
Answer:
DExplanation:
Determining Controls:
Acceptable Risk Level: The level of acceptable risk to the organization is the most important consideration because it directly influences the type and extent of controls implemented. Controls must be designed to keep risk within acceptable levels.
Risk Management Strategy: Aligning controls with the organization ' s risk appetite ensures that resources are used effectively and that critical information systems are adequately protected.
Comparison with Other Options:
Number of Threats: Important for understanding risk exposure but secondary to determining acceptable risk levels.
Available Budget: Budget constraints are important but should not compromise the implementation of necessary controls.
Number of Vulnerabilities: Identifying vulnerabilities is part of the risk assessment process, but controls are prioritized based on the acceptable risk level.
Best Practices:
Risk Assessment: Conduct thorough risk assessments to understand the potential impact of threats and vulnerabilities.
Control Effectiveness: Implement controls that are both cost-effective and capable of reducing risk to acceptable levels.
Continuous Monitoring: Regularly monitor and review controls to ensure they remain effective and aligned with the organization ' s risk tolerance.
Which of the following is the PRIMARY reason for a risk practitioner to review an organization ' s IT asset inventory?
Options:
To plan for the replacement of assets at the end of their life cycles
To assess requirements for reducing duplicate assets
To understand vulnerabilities associated with the use of the assets
To calculate mean time between failures (MTBF) for the assets
Answer:
CExplanation:
Understanding vulnerabilities associated with the use of the assets is the primary reason for a risk practitioner to review an organization’s IT asset inventory, as it helps to identify and assess the potential threats and risks to the assets. The other options are not the primary reasons for a risk practitioner to review an organization’s IT asset inventory, although they may be related to the process.
Which of the following is MOST important to determine as a result of a risk assessment?
Options:
Process ownership
Risk appetite statement
Risk tolerance levels
Risk response options
Answer:
DExplanation:
Risk response options are the most important factor to determine as a result of a risk assessment, as they involve selecting the optimal strategy and actions to address the identified and assessed risks, and align them with the risk tolerance and appetite of the organization. Process ownership, risk appetite statement, and risk tolerance levels are not the most important factors, as they are more related to the governance, definition, or communication of the risk, respectively, rather than the response to the risk. References = CRISC Review Manual, 7th Edition, page 108.
Which of the following is the BEST method to identify weaknesses in an organization ' s technical environment that could be leveraged by an attacker to gain access?
Options:
Threat modeling
Red team exercises
System testing
Control self-assessments (CSAs)
Answer:
BExplanation:
The correct answer isBbecausered team exercisesare the best method to identify weaknesses in the technical environment that an attacker could exploit to gain access. A red team exercise simulates realistic attacker behavior and therefore provides a direct and practical way to discover exploitable security weaknesses across systems, defenses, and operational response capabilities.
The other options are not as effective:
A. Threat modelingis useful for identifying possible attack paths and design weaknesses, but it is more analytical than practical.
C. System testingis broad and may not focus specifically on adversarial exploitation.
D. Control self-assessments (CSAs)rely on internal review and are less effective for uncovering attacker-leveraged technical weaknesses.
Exact Extracts supporting the answer:
“To detect vulnerabilities in Internet-facing systems penetration testing is primarily used as it simulates real attacker actions to test security defenses.”
“For a system owner penetration testing offers the greatest level of assurance regarding the effectiveness of implemented security controls.”
“For an Internet-facing application penetration testing is the most effective control assessment type.”
“The BEST way to ensure a corporate network ' s security against external attacks is to perform periodic penetration testing.”
“After various infrastructure changes are made is the best time to perform a penetration test as changes are likely to introduce new exposures.”
These extracts support the principle that simulated attacker activity is the strongest way to identify technical weaknesses exploitable by attackers. Among the given choices,red team exercisesare the closest and best match to that objective.
===========
An organization recently received an independent security audit report of its cloud service provider that indicates significant control weaknesses. What should be done NEXT in response to this report?
Options:
Migrate all data to another compliant service provider.
Analyze the impact of the provider ' s control weaknesses to the business.
Conduct a follow-up audit to verify the provider ' s control weaknesses.
Review the contract to determine if penalties should be levied against the provider.
Answer:
BExplanation:
An independent security audit report is a document that provides an objective and comprehensive assessment of the security posture and practices of a cloud service provider (CSP), based on a set of standards, criteria, or frameworks1. An independent security audit report can help an organization to evaluate the risks and benefits of using a CSP, and to ensure that the CSP meets the organization’s security and compliance requirements2.
If an organization receives an independent security audit report of its CSP that indicates significant control weaknesses, the next step that should be done in response to this report is to analyze the impact of the provider’s control weaknesses to the business. This means that the organization should:
Identify and prioritize the business processes, functions, or objectives that depend on or are affected by the CSP’s services
Assess the potential consequences and likelihood of the control weaknesses leading to security incidents, breaches, or losses
Estimate the financial, operational, reputational, or legal impacts of the security incidents, breaches, or losses
Compare the impacts with the organization’s risk appetite and tolerance, and determine the level of risk exposure and acceptance
Communicate the results of the analysis to the relevant stakeholders and decision-makers3
References = What is a Security Audit?, Cloud Security Audit: A 10-Step Checklist, Independent security audits are essential for cloud service providers. Here’s why
Which of the following is an IT business owner ' s BEST course of action following an unexpected increase in emergency changes?
Options:
Evaluating the impact to control objectives
Conducting a root cause analysis
Validating the adequacy of current processes
Reconfiguring the IT infrastructure
Answer:
BExplanation:
Conducting a root cause analysis is the best course of action for an IT business owner following an unexpected increase in emergency changes, as it helps to identify and address the underlying cause(s) of the problem and prevent it from recurring in the future. A root cause analysis is a systematic process of finding and resolving the fundamental factors that contribute to a specific issue or event. A root cause analysis can help to improve the quality and reliability of the IT services and processes, reduce the costs and risks associated with emergency changes, and enhance the customer satisfaction and trust.
The other options are not the best courses of action for an IT business owner following an unexpected increase in emergency changes. Evaluating the impact to control objectives is an important step to assess the potential consequences of the emergency changes on the IT governance and risk management, but it does not provide a solution or mitigation strategy for the problem. Validating the adequacy of current processes is a good practice to ensure that the IT processes are aligned with the business needs and objectives, but it does not address the specific cause(s) of the emergency changes. Reconfiguring the IT infrastructure is a possible action to implement the emergency changes, but it does not prevent the occurrence or recurrence of the problem. References = IT Business Owner’s Best Course of Action Following Unexpected Increase …, ITIL Change Types: Standard vs Normal vs Emergency - Freshworks, Emergency Change Management: Please Stop The Drama
Which of the following provides The BEST information when determining whether to accept residual risk of a critical system to be implemented?
Options:
Single loss expectancy (SLE)
Cost of the information system
Availability of additional compensating controls
Potential business impacts are within acceptable levels
Answer:
DExplanation:
The BEST information when determining whether to accept residual risk of a critical system to be implemented is the potential business impacts are within acceptable levels, because it indicates that the residual risk, which is the risk that remains after the risk response actions, does not exceed the risk tolerance and appetite of the organization, and that it does not pose a significant threat or disruption to the business objectives and processes. The potential business impacts are the consequences or outcomes of the residual risk on the organization’s performance, reputation, and value. The other options are not as informative as the potential business impacts, because:
Option A: Single loss expectancy (SLE) is a measure of the monetary loss that is expected from a single occurrence of a risk event, but it does not provide the best information when determining whether to accept residual risk, because it does not consider the frequency or probability of the risk event, or the qualitative aspects of the risk impact, such as customer satisfaction, employee morale, or regulatory compliance.
Option B: Cost of the information system is a measure of the total expenditure that is required to acquire, develop, operate, and maintain the information system, but it does not provide the best information when determining whether to accept residual risk, because it does not reflect the value or benefit of the information system, or the risk exposure or variation that the information system may introduce or encounter.
Option C: Availability of additional compensating controls is a measure of the alternative or supplementary controls that can be implemented to reduce the residual risk, but it does not provide the best information when determining whether to accept residual risk, because it does not indicate the effectiveness or efficiency of the compensating controls, or the cost-benefitanalysis of implementing them. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 122.
Which of the following would provide executive management with the BEST information to make risk decisions as a result of a risk assessment?
Options:
A companion of risk assessment results to the desired state
A quantitative presentation of risk assessment results
An assessment of organizational maturity levels and readiness
A qualitative presentation of risk assessment results
Answer:
AExplanation:
Risk assessment is the process of analyzing and evaluating the likelihood and consequences of the identified risks, and comparing them with the risk criteria and appetite. Risk assessment results can provide valuable information to support risk decisions, such as selecting and implementing the appropriate risk response strategies. The best way to provide executive management with the best information to make risk decisions as a result of a risk assessment is to present a comparison of risk assessment results to the desired state. The desired state is the optimal level of risk exposure that the organization wants to achieve, based on its risk objectives, goals, and strategy. A comparison of risk assessment results to the desired state can help executive management understand the current and potential gap between the actual and target risk levels, and prioritize the most critical and relevant risks that need attention and action. Acomparison of risk assessment results to the desired state can also help executive management evaluate the effectiveness and efficiency of the existing risk response, and identify the opportunities and challenges for improvement. A comparison of risk assessment results to the desired state can also help communicate and justify the risk decisions to other stakeholders, and obtain their feedback and approval. References = Risk Assessment and Analysis Methods: Qualitative and Quantitative - ISACA, Risk Management Essentials: How to Develop a Risk Profile (TRN2-J07), Risk Response Strategies: Avoid, Transfer, Mitigate, Accept.
An organization uses a vendor to destroy hard drives. Which of the following would BEST reduce the risk of data leakage?
Options:
Require the vendor to degauss the hard drives
Implement an encryption policy for the hard drives.
Require confirmation of destruction from the IT manager.
Use an accredited vendor to dispose of the hard drives.
Answer:
DExplanation:
Data leakage is the unauthorized or accidental disclosure of sensitive or confidential data to unauthorized parties. Data leakage can cause serious damages or losses to the organization, such as data breaches, fines, lawsuits, reputational harm, or loss of customer trust. Data leakage can occur due to various reasons, such as human errors, malicious attacks, or inadequate controls1.
An organization that uses a vendor to destroy hard drives faces a risk of data leakage, as the vendor may not properly or securely destroy the hard drives, or may access or misuse the data stored on them. The best way to reduce this risk is to use an accredited vendor to dispose of the hard drives, because it means that the vendor:
Has been certified or verified by a reputable or recognized authority or organization, such as ISACA, NAID, or R2, to provide hard drive destruction services
Follows the industry standards and best practices for hard drive destruction, such as NIST 800-88 or DoD 5220.22-M, and ensures the compliance with the legal and regulatory requirements, such as HIPAA, PCI DSS, or GDPR
Provides a secure and transparent process for hard drive destruction, such as using a specialized shredder, issuing a certificate of destruction, or allowing the customer to witness the destruction
Maintains a high level of professionalism and integrity, and does not compromise the confidentiality or security of the customer’s data234
The other options are not the best ways to reduce the risk of data leakage, but rather some of the steps or aspects of hard drive destruction. Require the vendor to degauss the hard drives is a step that can help to erase the data on the hard drives by using a strong magnetic field. However,degaussing may not be effective or reliable for some types of hard drives, such as solid state drives (SSDs), and it may not prevent the vendor from accessing or misusing the data before degaussing5. Implement an encryption policy for the hard drives is an aspect that can help to protect the data on the hard drives by using a cryptographic algorithm to make it unreadable without a key. However, encryption may not be sufficient or applicable for some types of data, such as metadata, and it may not prevent the vendor from accessing or misusing the key or the encrypted data6. Require confirmation of destruction from the IT manager is a step that can help to verify that the hard drives have been destroyed by the vendor, and to document the process and the outcome. However, confirmation of destruction may not be accurate or authentic, and it may not prevent the vendor from accessing or misusing the data before destruction7. References =
Data Leakage - ISACA
Hard Drive Shredding Services | Hard Drive Destruction & Disposal
Hard Drive Shredding and Destruction Service | CompuCycle
Electronic Destruction & Recycling | Shred Nations
Degaussing - ISACA
Encryption - ISACA
Certificate of Destruction - ISACA
[CRISC Review Manual, 7th Edition]
Which of the following is MOST important to the effective monitoring of key risk indicators (KRIS)?
Options:
Updating the threat inventory with new threats
Automating log data analysis
Preventing the generation of false alerts
Determining threshold levels
Answer:
DExplanation:
Key risk indicators (KRIs) are metrics that provide information about the level of exposure to a specific risk or a group of risks.
The most important factor to the effective monitoring of KRIs is determining threshold levels. This means that the acceptable or unacceptable values or ranges of the KRIs are defined and agreed upon by the relevant stakeholders.
Determining threshold levels helps to evaluate the actual performance and impact of the risks, compare them with the risk appetite and tolerance of the organization, identify any deviations or breaches that may require attention or action, and report them to the appropriate parties for decision making or improvement actions.
The other options are not the most important factors to the effective monitoring of KRIs. They are either secondary or not essential for KRIs.
The references for this answer are:
Risk IT Framework, page 15
Information Technology & Security, page 9
Risk Scenarios Starter Pack, page 7
A monthly payment report is generated from the enterprise resource planning (ERP) software to validate data against the old and new payroll systems. What is the BEST way to mitigate the risk associated with data integrity loss in the new payroll system after data migration?
Options:
Compare new system reports with functional requirements.
Compare encrypted data with checksums.
Compare results of user acceptance testing (UAT) with the testing criteria.
Compare processing output from both systems using the previous month ' s data.
Answer:
DExplanation:
According to the CRISC Review Manual (Digital Version), the best way to mitigate the risk associated with data integrity loss in the new payroll system after data migration is to compare the processing output from both systems using the previous month’s data, as this ensures that thenew system produces the same results as the old system for the same input data. Comparing the processing output from both systems using the previous month’s data helps to:
Verify the accuracy and completeness of the data migration process and identify any errors or discrepancies in the data transfer
Validate the functionality and performance of the new system and confirm that it meets the business requirements and expectations
Evaluate the consistency and reliability of the data processing and reporting in the new system and detect any anomalies or deviations
Recommend and implement appropriate actions or measures to address any issues or findings in the data migration and the new system
Communicate and coordinate the data migration and the new system testing with the relevant stakeholders, such as the data owners, the users, and the senior management
References = CRISC Review Manual (Digital Version), Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Scenarios, pp. 107-1081
The BEST use of key risk indicators (KRIs) is to provide:
Options:
Early indication of increasing exposure to a specific risk.
Lagging indication of major information security incidents.
Early indication of changes to required risk response.
Insight into the performance of a monitored process.
Answer:
AExplanation:
Key risk indicators are designed to provide early warnings about increasing risk exposure, enabling timely risk mitigation efforts. This supports proactive risk management, as outlined in theRisk Monitoring and Reportingdomain of CRISC.
Which of the following is the PRIMARY consideration when establishing an organization ' s risk management methodology?
Options:
Business context
Risk tolerance level
Resource requirements
Benchmarking information
Answer:
AExplanation:
The primary consideration when establishing an organization’s risk management methodology is the business context, which includes the internal and external factors that influence the organization’s objectives, strategies, scope, and boundaries. The business context helps to define the risk criteria, the risk appetite, the risk identification, the risk analysis, and the risk treatment. The other options are not the primary consideration, but rather the outcomes or inputs of the risk management methodology. References = ISO 31000 Risk Management – Principles andGuidelines; ISO 31000 Principles of Risk Management; The risk management process: What is the best structure and administration?
Which of the following is the MOST effective way to integrate risk and compliance management?
Options:
Embedding risk management into compliance decision-making
Designing corrective actions to improve risk response capabilities
Embedding risk management into processes that are aligned with business drivers
Conducting regular self-assessments to verify compliance
Answer:
CExplanation:
Embedding risk management into processes that are aligned with business drivers is the most effective way to integrate risk and compliance management, as it ensures that the risk management objectives and activities are consistent and supportive of the enterprise’s strategic goals and values. It also enables the identification and management of risks and compliance requirements across the enterprise, and the optimization of risk and compliance resources and performance. Embedding risk management into compliance decision-making, designingcorrective actions to improve risk response capabilities, and conducting regular self-assessments to verify compliance are not ways to integrate risk and compliance management, but rather components or outcomes of the risk and compliance management process. References = CRISC Practice Quiz and Exam Prep; CRISC: Certified in Risk & Information Systems Control Sample Questions, question 202.
Which of the following presents the GREATEST security risk to an organization with a large number of Internet of Things (IoT) devices within its network?
Options:
Inadequate network bandwidth
Lack of interoperability between IoT devices
Insufficient IoT policies and procedures
Increased maintenance costs for IoT devices
Answer:
CExplanation:
The correct answer isCbecauseinsufficient IoT policies and procedurescreate the greatest security risk. In an environment with many IoT devices, governance and control are essential. Without clear policies and procedures, the organization may fail to define security requirements, ownership, configuration standards, patching responsibilities, access restrictions, monitoring expectations, and acceptable use requirements. This creates widespread unmanaged exposure across the network.
The other choices are less significant from a security-risk perspective:
A. Inadequate network bandwidthis mainly a performance issue.
B. Lack of interoperability between IoT devicesis primarily an operational or compatibility issue.
D. Increased maintenance costs for IoT devicesis a financial concern, not the greatest direct security risk.
Exact Extracts supporting the answer:
“When evaluating risks related to Internet of Things (IoT) devices used on enterprise networks the first recommendation should address IoT devices with hard-coded passwords.”
“Enterprise policies are the most influential factor in determining an enterprise’s approach to risk management.”
“The BEST way to identify IS control deficiencies is through defined control objectives.”
“The MOST important criterion when reviewing information security controls is ensuring that the controls are effectively addressing risk.”
These extracts show that IoT risk must be addressed through governance, defined requirements, and effective controls. Since policies and procedures establish how IoT devices are secured and managed, insufficient IoT policies and procedures present the greatest security risk.
===========
A risk practitioner shares the results of a vulnerability assessment for a critical business application with the business manager. Which of the following is the NEXT step?
Options:
Develop a risk action plan to address the findings.
Evaluate the impact of the vulnerabilities to the business application.
Escalate the findings to senior management and internal audit.
Conduct a penetration test to validate the vulnerabilities from the findings.
Answer:
AExplanation:
According to the CRISC Review Manual1, a risk action plan is a document that defines the specific actions, resources, responsibilities, and timelines for implementing the risk responses. A risk action plan should be developed after the results of a vulnerability assessment are shared with the relevant stakeholders, such as the business manager, to address the identified vulnerabilities and mitigate the associated risks. Developing a risk action plan is the next step in the risk management process, as it helps to ensure that the risk responses are executed effectively and efficiently, and that the residual risks are within the acceptable levels. References = CRISC Review Manual1, page 201.
What should be the PRIMARY consideration related to data privacy protection when there are plans for a business initiative to make use of personal information?
Options:
Do not collect or retain data that is not needed.
Redact data where possible.
Limit access to the personal data.
Ensure all data is encrypted at rest and during transit.
Answer:
DWhich of the following controls are BEST strengthened by a clear organizational code of ethics?
Options:
Detective controls
Administrative controls
Technical controls
Preventive controls
Answer:
BExplanation:
Administrative controls are the best controls to be strengthened by a clear organizational code of ethics, because they are the policies, procedures, standards, and guidelines that define the expected behavior and conduct of the employees and management. A code of ethics is an example of an administrative control that sets the ethical principles and values of the organization and helps to prevent or deter unethical or illegal actions. The other options are not the best controls to be strengthened by a clear organizational code of ethics, because they are not directly related to the ethical culture or governance of the organization. Detective controls are the controls that monitor and report the occurrence of unwanted events or incidents. Technical controls are the controls that use hardware, software, or network devices to protect the information systems and data. Preventive controls are the controls that prevent or avoid the occurrence of unwanted events or incidents. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers
Which of the following provides the MOST reliable evidence of a control ' s effectiveness?
Options:
A risk and control self-assessment
Senior management ' s attestation
A system-generated testing report
detailed process walk-through
Answer:
CExplanation:
The most reliable evidence of a control’s effectiveness is a system-generated testing report. A system-generated testing report is a document that shows the results of automated tests performed by the system to verify that the control is functioning as intended and producing the expected outcomes. A system-generated testing report is reliable, because it is objective, consistent, accurate, and timely, and because it can provide a high level of assurance and confidence in the control’s effectiveness. The other options are not as reliable as a system-generated testing report, although they may provide some evidence of the control’s effectiveness. A risk and control self-assessment, senior management’s attestation, and a detailed process walk-through are all examples of manual or subjective evidence, which may be prone to errors, biases, or inconsistencies, and which may provide a lower level of assurance and confidence in the control’s effectiveness. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.4.1, page 3-32.
Which of the following is the BEST indication that key risk indicators (KRIs) should be revised?
Options:
An increase in the number of risk threshold exceptions
An increase in the number of change events pending management review
A decrease in the number of key performance indicators (KPIs)
A decrease in the number of critical assets covered by risk thresholds
Answer:
AExplanation:
Risk threshold exceptions are instances when a KRI exceeds or falls below a predefined level or point that triggers an action or a warning. An increase in the number of risk threshold exceptions indicates that the KRIs are not reflecting the current risk exposure or environment accurately oreffectively. This may suggest that the KRIs are outdated, irrelevant, or poorly defined. Therefore, the KRIs should be revised to ensure that they are aligned with the organizational objectives, risk appetite, and risk management strategy.
References
•Key Risk Indicators: A Practical Guide | SafetyCulture
•Key Risk Indicators: Examples & Definitions - SolveXia
•Choosing and Using Key Risk Indicators - Institute of Risk Management
A risk practitioner is assisting with the preparation of a report on the organization s disaster recovery (DR) capabilities. Which information would have the MOST impact on the overall recovery profile?
Options:
The percentage of systems meeting recovery target times has increased.
The number of systems tested in the last year has increased.
The number of systems requiring a recovery plan has increased.
The percentage of systems with long recovery target times has decreased.
Answer:
DExplanation:
According to the CRISC Review Manual (Digital Version), the percentage of systems with long recovery target times has decreased is the information that would have the most impact on the overall recovery profile, as it indicates that the organization has improved its ability to restore its critical systems and processes within the acceptable time frames after a disaster. The recovery target time, also known as the recovery time objective (RTO), is the maximum acceptable time that an application, computer, network, or system can be down after an unexpected disaster, failure, or comparable event takes place. The recovery profile, also known as the recovery point objective (RPO), is the maximum acceptable amount of data loss measured in time. A lower percentage of systems with long recovery target times means that the organization has:
Reduced the gap between the business requirements and the IT capabilities for disaster recovery
Enhanced the resilience and availability of its critical systems and processes
Minimized the potential losses and damages caused by prolonged downtime
Increased the confidence and satisfaction of its stakeholders and customers
References = CRISC Review Manual (Digital Version), Chapter 3: IT Risk Response, Section 3.3: Risk Response Options, pp. 174-1751
Management has noticed storage costs have increased exponentially over the last 10 years because most users do not delete their emails. Which of the following can BEST alleviate this issue while not sacrificing security?
Options:
Implementing record retention tools and techniques
Establishing e-discovery and data loss prevention (DLP)
Sending notifications when near storage quota
Implementing a bring your own device 1BVOD) policy
Answer:
AExplanation:
According to the Risk and Information Systems Control documents, implementing record retention tools and techniques is the best solution in this scenario. Record retention involves managing the lifecycle of records, including their creation, usage, storage, and disposal. By implementing record retention policies, organizations can define how long emails and other data should be retained before being deleted. This helps in efficiently managing storage space and reducing unnecessary storage costs.
Establishing e-discovery and data loss prevention (DLP) (Option B) focuses more on legal and compliance aspects and may not directly address the issue of reducing storage costs. Sending notifications when near storage quota (Option C) is a reactive approach and may not prevent the exponential increase in storage costs. Implementing a bring your own device (BYOD) policy (Option D) is unrelated to the issue of email storage costs.
References = Risk and Information Systems Control Study Manual
For a large software development project, risk assessments are MOST effective when performed:
Options:
before system development begins.
at system development.
at each stage of the system development life cycle (SDLC).
during the development of the business case.
Answer:
CExplanation:
Risk assessments are most effective when performed at each stage of the system development life cycle (SDLC). The SDLC is a framework that defines the phases and activities of developing, implementing, and maintaining a system. The SDLC typically consists of the following stages: initiation, planning, analysis, design, development, testing, implementation, and maintenance. Performing risk assessments at each stage of the SDLC helps to identify, analyze, and evaluate the risks that could affect the system objectives, requirements, functionality, quality, or performance. Performing risk assessments at each stage of the SDLC also helps to select and implement the appropriate risk responses, such as avoiding, transferring, mitigating, or accepting the risks. Performing risk assessments at each stage of the SDLC also helps to monitor and report the risk status and performance, and to update and adjust the risk assessment and response as the system changes or evolves. Performing risk assessments before system development begins, at system development, or during the development of the business case are not as effective as performing risk assessments at each stage of the SDLC, as they are either too early or too late, and they do not capture the full scope and complexity of the system risks. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 49.
Which of the following is the PRIMARY reason for a risk practitioner to examine a post-implementation review report for a control automation tool?
Options:
To verify that budget for the project is managed effectively
To confirm compliance with project management methodology
To ensure the risk is managed to an acceptable level
To ensure audit findings are addressed in a timely manner
Answer:
CExplanation:
The main purpose of implementing controls is to reduce risk to an acceptable level. Reviewing the effectiveness of the new tool post-implementation ensures the control objective has been achieved.
When reviewing a business continuity plan (BCP). which of the following would be the MOST significant deficiency?
Options:
BCP testing is net in conjunction with the disaster recovery plan (DRP)
Recovery time objectives (RTOs) do not meet business requirements.
BCP is often tested using the walk-through method.
Each business location has separate, inconsistent BCPs.
Answer:
BExplanation:
According to the CRISC Review Manual, recovery time objectives (RTOs) are the maximum acceptable time that an IT system can be inoperable without causing significant damage to the business operations and objectives. RTOs are determined by the business impact analysis (BIA) and are used to define the recovery strategies and priorities. Therefore, if the RTOs do not meet the business requirements, it would be themost significant deficiency in the BCP, as it would imply that the recovery plan is not aligned with the business needs and expectations. The other options are not the most significant deficiencies, as they do not directly affect the recovery time and the business continuity. BCP testing is not necessarily done in conjunction with the DRP, as they have different scopes and objectives. BCP testing can use different methods, such as walk-through, simulation, or full interruption, depending on the purpose and scope of the test. Each business location can have separate BCPs, as long as they are consistent with the enterprise-wide BCP and the business requirements. References = CRISC Review Manual, 7th Edition, Chapter 5, Section 5.2.2, page 240.
Which of the following controls will BEST detect unauthorized modification of data by a database administrator?
Options:
Reviewing database access rights
Reviewing database activity logs
Comparing data to input records
Reviewing changes to edit checks
Answer:
BExplanation:
Unauthorized modification of data by a database administrator is a security risk that involves altering, deleting, or inserting data on a database without proper authorization or approval, by a person who has privileged access to the database, such as a database administrator12.
The best control to detect unauthorized modification of data by a database administrator is to review database activity logs, which are records that capture and store the details and history ofthe transactions or activities that are performed on the database, such as who, what, when, where, and how34.
Reviewing database activity logs is the best control because it provides evidence and visibility of the database operations, and enables the detection and reporting of any deviations, anomalies, or issues that may indicate unauthorized modification of data by a database administrator34.
Reviewing database activity logs is also the best control because it supports the accountability and auditability of the database operations, and facilitates the investigation and resolution of any unauthorized modification of data by a database administrator34.
The other options are not the best controls, but rather possible measures or techniques that may supplement or enhance the review of database activity logs. For example:
Reviewing database access rights is a measure that involves verifying and validating the permissions and privileges that are granted or revoked to the users or roles who can access or modify the data on the database56. However, this measure is not the best control because it does not directly detect unauthorized modification of data by a database administrator, especially if the database administrator has legitimate access rights to the data56.
Comparing data to input records is a technique that involves matching and reconciling the data on the database with the original or source data that are entered or imported into the database, and identifying and correcting any discrepancies or errors78. However, this technique is not the best control because it does not directly detect unauthorized modification of data by a database administrator, especially if the input records are also modified or compromised78.
Reviewing changes to edit checks is a technique that involves examining and evaluating the modifications or updates to the edit checks, which are rules or validations that are applied to the data on the database to ensure their accuracy, completeness, andconsistency9 . However, this technique is not the best control because it does not directly detect unauthorized modification of data by a database administrator, especially if the edit checks are bypassed or disabled9 . References =
1: Database Security: Attacks and Solutions | SpringerLink2
2: Unauthorised Modification of Data With Intent to Cause Impairment3
3: Database Activity Monitoring - Wikipedia4
4: Database Activity Monitoring (DAM) | Imperva5
5: Database Access Control - Wikipedia6
6: Database Access Control: Best Practices for Database Security7
7: Data Reconciliation - Wikipedia8
8: Data Reconciliation and Gross Error Detection9
9: Edit Check - Wikipedia
Edit Checks: A Data Quality Tool
Who should be responsible (of evaluating the residual risk after a compensating control has been
Options:
Compliance manager
Risk owner
Control owner
Risk practitioner
Answer:
CExplanation:
The control owner should be responsible for evaluating the residual risk after a compensating control has been implemented. A compensating control is a control that provides an alternative or additional measure of protection when the primary or preferred control is not feasible or effective. A residual risk is the risk that remains after the risk response or mitigation has beenapplied. The control owner is the person who has the authority and responsibility for designing, implementing, and monitoring the controls that enforce the policy. The control owner can assess the impact and effectiveness of the compensating control on the residual risk, and report the results and recommendations to the risk owner or the risk practitioner. The other options are not as responsible as the control owner, as they are related to the compliance, ownership, or management of the risk, not the evaluation of the control. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.4: Key Control Indicators, page 211.
Options:
Implement a new risk assessment process.
Revalidate the corporate risk appetite.
Review and adjust key risk indicators (KRIs).
Communicate the new risk profile.
Answer:
BExplanation:
Changes in organizational structure often affect risk appetite, which defines the amount and type of risk an organization is willing to accept. Revalidating the corporate risk appetite ensures that the organization’s risk-taking aligns with its new structure, strategic goals, and culture. While reviewing KRIs and communicating the risk profile are important, they follow after confirming risk appetite alignment. Implementing a new assessment process is not always necessary unless structural changes fundamentally affect risk assessment scope【5:83, 5:104†CRISC_SentenceinNOTE30.pptx】.
Which of the following is the MOST important reason to revisit a previously accepted risk?
Options:
To update risk ownership
To review the risk acceptance with new stakeholders
To ensure risk levels have not changed
To ensure controls are still operating effectively
Answer:
CExplanation:
The most important reason to revisit a previously accepted risk is to ensure that the risk levels have not changed. A previously accepted risk is a risk that the organization has decided to tolerate or retain without taking any further action, because the risk is either low or unavoidable, or the cost or effort of mitigation outweighs the potential benefit. However, risk acceptance is not a static or permanent decision, as the risk levels may change over time due to various factors, such as new threats, vulnerabilities, impacts, or opportunities. Therefore, it is essential to revisit a previously accepted risk periodically or when there is a significant change in the internal or external environment, to verify that the risk is still within the acceptable range and that the risk acceptance rationale is still valid. If the risk levels have increased or decreased, the organization may need to revise the risk acceptance decision and consider other risk response options, such as avoidance, reduction, sharing, or exploitation. The other options are not the most important reason to revisit a previously accepted risk, although they may be relevant or necessary depending on the context and nature of the risk. Updating risk ownership is a part of the risk governance process, which ensures that the roles and responsibilities for managing the risk are clearly defined and assigned, but it does not affect the risk levels or the risk acceptance decision. Reviewing the risk acceptance with new stakeholders is a part of the risk communication process, which ensures that the risk information and the risk acceptance rationale are shared and understood by the relevant parties, but it does not change the risk levels or the risk acceptance decision. Ensuring that the controls are still operating effectively is a part of the risk monitoring and review process, which ensures that the risk response actions are implemented and maintained properly, but it does not apply to the accepted risks, as they do not have any additionalcontrols. References = Understanding Accepted Risk - SC Dashboard | Tenable®, Risk Acceptance — ENISA, Accepting Risk - Overview, Advantages, Disadvantages, Alternatives
Which of the following would prompt changes in key risk indicator {KRI) thresholds?
Options:
Changes to the risk register
Changes in risk appetite or tolerance
Modification to risk categories
Knowledge of new and emerging threats
Answer:
BExplanation:
Key risk indicators (KRIs) are metrics that provide information on the level of exposure to a given operational risk1. KRIs have upper and lower acceptable risk limits (warning thresholds) that trigger actions when exceeded2. These thresholds are based on the organization’s risk appetite or tolerance, which is the amount and type of risk that the organization is willing to accept in pursuit of its objectives3. Therefore, changes in risk appetite or tolerance would prompt changes in KRI thresholds, as the organization would need to adjust its risk monitoring and response accordingly. The other options are not the primary factors that would prompt changes in KRI thresholds, although they may have some influence on the risk management process. References = Risk IT Framework; IT Risk Resources; ISACA Risk Starter Kit; Key Risk Indicators; Key Risk Indicators: A Practical Guide
The risk to an organization ' s reputation due to a recent cybersecurity breach is PRIMARILY considered to be:
Options:
financial risk.
data risk.
operational risk.
strategic risk.
Answer:
DExplanation:
Understanding Strategic Risk:
Strategic risk refers to the potential losses that can arise from adverse business decisions, improper implementation of decisions, or lack of responsiveness to changes in the business environment.
Reputational Impact of Cybersecurity Breaches:
A cybersecurity breach can severely damage an organization ' s reputation, affecting customer trust, investor confidence, and market value.
Such impacts go beyond immediate financial losses and can have long-term strategic implications for the organization ' s competitive position and strategic objectives.
Classification of Risk:
Financial Risk:Direct financial losses due to a breach (e.g., fines, legal costs) but does not cover reputational impacts.
Data Risk:Focuses on the loss or compromise of data but not the broader strategic impact.
Operational Risk:Pertains to disruptions in business operations, while reputational damage influences the organization’s strategic direction and goals.
Strategic Risk and Reputation:
Reputational damage from a cybersecurity breach can lead to a loss of customer base, reduced market share, and difficulties in strategic partnerships, all of which are strategic concerns.
Addressing reputational risk requires strategic planning, proactive communication, and long-term efforts to rebuild trust and credibility.
References:
The CRISC Review Manual highlights that reputational risk is a significant aspect of strategic risk, especially following cybersecurity incidents (CRISC Review Manual, Chapter 1: Governance, Section 1.1.3 Importance and Value of IT Risk Management).
Which of the following BEST prevents control gaps in the Zero Trust model when implementing in the environment?
Options:
Relying on multiple solutions for Zero Trust
Utilizing rapid development during implementation
Establishing a robust technical architecture
Starting with a large initial scope
Answer:
CWhich of the following is MOST important to consider when determining risk appetite?
Options:
Service level agreements (SLAs)
Risk heat map
IT capacity
Risk culture
Answer:
DExplanation:
Risk culture encompasses the values, beliefs, and attitudes towards risk within an organization. It significantly influences how risk appetite is defined and communicated. Understanding the organization ' s risk culture ensures that the established risk appetite aligns with stakeholder expectations and supports effective risk management practices.
What is the PRIMARY reason an organization should include background checks on roles with elevated access to production as part of its hiring process?
Options:
To eliminate risk associated with personnel
To reduce internal threats
To ensure new hires have the required skills
To reduce exposure to vulnerabilities
Answer:
BExplanation:
The correct answer is B because the primary reason for conducting background checks on individuals who will have elevated access to production systems is to reduce internal threats . Personnel with privileged access can significantly affect confidentiality, integrity, and availability. Background screening is a preventive governance and personnel security control intended to lower the likelihood of insider misuse, fraud, abuse of privilege, or other harmful actions.
The other options are less appropriate:
A. To eliminate risk associated with personnel is incorrect because risk cannot be fully eliminated.
C. To ensure new hires have the required skills is handled more directly through recruitment, vetting, and qualification review, not primarily through background checks.
D. To reduce exposure to vulnerabilities is too indirect; vulnerabilities are weaknesses in systems or controls, while this question is about personnel risk.
Exact Extracts supporting the answer:
“The MOST effective measure against insider threats to confidential information is role-based access control.”
“The PRIMARY reason that an enterprise would establish segregation of duties controls is to prevent errors or fraudulent activity on high-risk transactions.”
“The control that focuses directly on preventing the risk of collusion is mandatory job rotation.”
“The MOST concern to the risk practitioner regarding applications running in production is backdoors.”
These extracts support that elevated access roles create significant internal threat exposure and require preventive controls focused on reducing insider risk. Therefore, the primary reason for background checks is to reduce internal threats .
===========
QUESTION NO: 91 [Risk Assessment]
Which of the following would be MOST helpful to review when prioritizing the implementation of multiple IT-related initiatives?
A. Risk awareness program objectives
B. Risk assessment results
C. Risk profile
D. Risk policy
Answer: C
The correct answer is C because the risk profile provides the most useful enterprise-level view when prioritizing multiple IT-related initiatives. It reflects the aggregated level of risk facing the organization, helps identify which exposures are most significant, and supports comparison across initiatives based on business impact, likelihood, and current exposure.
The other options are less useful for prioritization at this level:
A. Risk awareness program objectives relate to culture and communication, not implementation prioritization.
B. Risk assessment results are important, but the risk profile is more useful when consolidating and prioritizing across multiple initiatives.
D. Risk policy sets direction and expectations, but it does not provide the comparative view needed for prioritization.
Exact Extracts supporting the answer:
“The most important aspect to consider in relation to a risk profile is the aggregated risk to the enterprise.”
“The main purpose of risk monitoring is to provide timely information on the actual status of the enterprise with regard to risk with the risk profile offering an overall risk status.”
“When reporting the status of the IT control environment to management the most important component is the risk profile of the enterprise.”
“The PRIMARY result of a risk assessment process is input for risk-aware decisions.”
These extracts show that the risk profile is the best consolidated basis for prioritizing multiple IT-related initiatives.
===========
QUESTION NO: 92 [Risk and Control Monitoring and Reporting]
Which of the following attributes of data provided to an automated log analysis tool is MOST important for effective risk monitoring?
A. Confidentiality
B. Scalability
C. Retention
D. Relevancy
Answer: D
The correct answer is D because the most important attribute of data fed into an automated log analysis tool is relevancy . For effective risk monitoring, the tool must receive data that is meaningful, useful, and directly related to the risks, events, controls, and activities being monitored. Irrelevant data reduces signal quality, obscures important indicators, and weakens timely detection.
The other options are less important for monitoring effectiveness itself:
A. Confidentiality is important for protecting the data, but it does not by itself make the monitoring effective.
B. Scalability is a system capability, not a core attribute of the data itself.
C. Retention is important for historical review and forensics, but not the most important factor for effective real-time or ongoing monitoring.
Exact Extracts supporting the answer:
“If the correct information was not received by the necessary recipients in time to allow proper action this can be categorized as relevance risk.”
“The most important consideration when implementing key risk indicators is linking the metric to a specific risk.”
“The MOST essential criterion for the effectiveness of operational metrics is relevance to the recipient.”
“The main purpose of continuous monitoring is detecting changes to the enterprise’s risk environment.”
These extracts directly support that relevant information is essential for useful monitoring and effective action. Therefore, relevancy is the most important attribute.
===========
QUESTION NO: 93 [Risk Assessment]
In the context of a business impact analysis (BIA) which of the following activities would be MOST complex and time-consuming for a risk practitioner in a large global organization?
A. Calculating recovery time objectives (RTOs)
B. Analyzing the financial impact of a disruption
C. Analyzing the interdependences between business departments
D. Identifying critical IT business processes and procedures
Answer: C
The correct answer is C because in a large global organization, the most complex and time-consuming BIA activity is analyzing the interdependencies between business departments . Large enterprises have numerous cross-functional, regional, operational, legal, and technical dependencies. Understanding how disruption in one area affects another is often the most difficult and resource-intensive part of a business impact analysis.
The other options are important, but generally less complex in a large global environment:
A. Calculating recovery time objectives (RTOs) is important, but it is usually derived after understanding process criticality and dependencies.
B. Analyzing the financial impact of a disruption can be difficult, but interdependency mapping is often broader and more complicated.
D. Identifying critical IT business processes and procedures is foundational, but in a global organization the network of dependencies is typically the harder task.
Exact Extracts supporting the answer:
“The objective of a business impact analysis is best described as the identification of time-sensitive critical business functions and interdependencies.”
“The most useful process in developing a series of recovery time objectives is business impact analysis.”
“A business impact analysis is primarily used to evaluate the impact of disruption on an enterprise’s ability to operate over time.”
“The main outcome of a business impact analysis (BIA) is the criticality of business processes.”
These extracts show that identifying interdependencies is central to BIA. In a large global organization, that makes it the most complex and time-consuming activity.
===========
QUESTION NO: 94 [Risk and Control Monitoring and Reporting]
Which of the following criteria is MOST important to include in an agreement with a penetration testing vendor?
A. Details of testing methods to be used
B. Expectations of code escrow safeguards
C. Scope of the systems to be assessed
D. Steps to remediate identified vulnerabilities
Answer: C
The correct answer is C because the most important criterion to include in an agreement with a penetration testing vendor is the scope of the systems to be assessed . Clear scope is essential to define what is authorized, what assets may be tested, what environments are in scope, and what boundaries apply. Without a clearly defined scope, testing could miss key assets or unintentionally affect systems that were not authorized for assessment.
The other options are less important as the primary agreement requirement:
A. Details of testing methods to be used are useful, but they come after scope is clearly established.
B. Expectations of code escrow safeguards are unrelated to most penetration testing agreements.
D. Steps to remediate identified vulnerabilities may follow from the test results, but they are not the most important initial contractual criterion.
Exact Extracts supporting the answer:
“Prior to conducting a penetration test the most important step is obtaining senior management approval of exercise parameters.”
“Before beginning a black box penetration test it ' s crucial to have a clearly stated definition of scope in place.”
“To best preserve service availability during a penetration test it ' s essential to schedule testing of critical systems during maintenance windows.”
“For an Internet-facing application penetration testing is the most effective control assessment type.”
These extracts directly support that clear scope is the most important criterion in an agreement with a penetration testing vendor.
What should be the PRIMARY objective for a risk practitioner performing a post-implementation review of an IT risk mitigation project?
Options:
Documenting project lessons learned
Validating the risk mitigation project has been completed
Confirming that the project budget was not exceeded
Verifying that the risk level has been lowered
Answer:
DExplanation:
A post-implementation review (PIR) is a process to evaluate whether the objectives of the project were met and whether the project delivered the expected benefits and outcomes1. The primary objective of a risk practitioner performing a PIR of an IT risk mitigation project is to verify that the risk level has been lowered as a result of the project implementation2. This can be done by comparing the actual risk level with theexpected risk level, assessing the effectiveness and efficiency of the risk mitigation controls, and identifying any residual or emergingrisks3. Documenting project lessons learned, validating the project completion, and confirming the project budget are important aspects of a PIR, but they are not the primary objective for a risk practitioner, as they do not directly measure the impact of the project on the risk level4. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk Response and Mitigation, Section 5.4: Post-Implementation Review, pp. 239-241.
An organization ' s risk management team wants to develop IT risk scenarios to show the impact of collecting and storing credit card information. Which of the following is the MOST comprehensive approach to capture this scenario?
Options:
Top-down analysis
Event tree analysis
Control gap analysis
Bottom-up analysis
Answer:
BExplanation:
According to the ISACA Risk and Information Systems Control study guide and handbook, the most comprehensive approach to capture the risk scenario of collecting and storing credit card information is event tree analysis (ETA). ETA is a forward, top-down, logical modeling technique that explores the responses and outcomes of a single initiating event, such as a data breach or a cyberattack. ETA can help to identify all possible consequences of the scenario, such as financial losses, reputational damages, legal liabilities, regulatory penalties, and customer dissatisfaction. ETA can also help to assess the probabilities of the outcomes and the effectiveness of the controls and mitigation strategies12
1: ISACA Risk and Information Systems Control Study Guide, 4th Edition, page 33 2: ISACA Risk and Information Systems Control Handbook, 1st Edition, page 25
Which of the following BEST supports ethical IT risk management practices?
Options:
Robust organizational communication channels
Mapping of key risk indicators (KRIs) to corporate strategy
Capability maturity models integrated with risk management frameworks
Rigorously enforced operational service level agreements (SLAs)
Answer:
AExplanation:
Robust organizational communication channels are the best way to support ethical IT risk management practices, as they enable transparent and consistent sharing of risk information anddecisions among all stakeholders. Ethical IT risk management requires that the risk management process and outcomes are aligned with the enterprise’s values, objectives, and obligations, and that the risk management activities are conducted with integrity, accountability, and respect. Robust organizational communication channels facilitate these aspects by ensuring that the risk management roles and responsibilities are clearly defined and communicated, that the risk management policies and procedures are widely disseminated and understood, that the risk management performance and results are regularly reported and reviewed, and that the risk management feedback and improvement suggestions are solicited and addressed. Mapping of key risk indicators (KRIs) to corporate strategy, capability maturity models integrated with risk management frameworks, and rigorously enforced operational service level agreements (SLAs) are not directly related to ethical IT risk management practices, but rather to the effectiveness and efficiency of the risk management process. References = CRISC Certified in Risk and Information Systems Control – Question201; ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 201.
Which of the following is the BEST metric to demonstrate the effectiveness of an organization ' s change management process?
Options:
Increase in the frequency of changes
Percent of unauthorized changes
Increase in the number of emergency changes
Average time to complete changes
Answer:
BExplanation:
A change management process is a set of procedures and activities that aim to ensure that changes in an organization’s IT systems and services are implemented in a controlled and coordinated manner. The effectiveness of a change management process can be measured by how well it reduces the risks and costs associated with changes, and how well it supports the business objectives and customer expectations. One of the best metrics to demonstrate the effectiveness of a change management process is the percent of unauthorized changes. Unauthorized changes are changes that are made without following the established change management process, such as obtaining approval, documenting the change, testing the change, and communicating the change. Unauthorized changes can introduce errors, defects, security breaches, and disruptions to the IT systems and services, and can negatively affect the business performance and customer satisfaction. Therefore, a low percent of unauthorized changes indicates that the change management process is effective in ensuring that changes are properly planned, approved, executed, and monitored. The other options are not the best metrics to demonstrate the effectiveness of a change management process, as they do not directly reflect the quality and control of the changes. An increase in the frequency of changes may indicate that the organization is agile and responsive to the changing business needs and customer demands, but it does not necessarily mean that the changes are well-managed and beneficial. An increase in the number of emergency changes may indicate that the organization is able to handle urgent and critical situations, but it may also suggest that the organization is reactive and lacks proper planning and analysis of the changes. The average time to complete changes may indicate the efficiency and speed of the change management process, but it does not measure the effectiveness and value of the changes. References = CRISC Review Manual, pages 156-1571; CRISC Review Questions, Answers & Explanations Manual, page 712
Which of the following controls BEST addresses the risk of unauthorized disclosure of sensitive data as a result of a lost bring your own device (BYOD) tablet?
Options:
Unregistered device detection
Device encryption
Device wiping policy
Mobile device antivirus
Answer:
BUpon learning that the number of failed back-up attempts continually exceeds the current risk threshold, the risk practitioner should:
Options:
inquire about the status of any planned corrective actions
keep monitoring the situation as there is evidence that this is normal
adjust the risk threshold to better reflect actual performance
initiate corrective action to address the known deficiency
Answer:
AExplanation:
The best course of action for the risk practitioner upon learning that the number of failed back-up attempts continually exceeds the current risk threshold is to inquire about the status of any planned corrective actions. This would help the risk practitioner to understand the root causes of the problem, the progress of the remediation efforts, and the expected timeline for resolution. It would also help the risk practitioner to provide guidance and support to the responsible parties, and to escalate the issue if necessary. Inquiring about the status of any planned corrective actions would demonstrate the risk practitioner’s proactive and collaborative approach to riskmanagement, and ensure that the risk exposure is reduced to an acceptable level as soon as possible. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.2.3, page 2371
Which of the following should be the risk practitioner s PRIMARY focus when determining whether controls are adequate to mitigate risk?
Options:
Sensitivity analysis
Level of residual risk
Cost-benefit analysis
Risk appetite
Answer:
BExplanation:
The risk practitioner’s primary focus when determining whether controls are adequate to mitigate risk should be the level of residual risk, because this indicates the amount and type of risk that remains after applying the controls, and whether it is acceptable or not. Residual risk is the risk that is left over after the risk responseactions have been taken, such as implementing or improving controls. Controls are the measures or actions that are designed and performed to reduce the likelihood and/or impact of a risk event, or to exploit the opportunities that a risk event may create. The adequacy of controls to mitigate risk depends on how well they address the root causes or sources of the risk, and how effectively and efficiently they reduce the risk exposure and value. The level of residual risk reflects the adequacy of controls to mitigate risk, as it shows the gap between the inherent risk and the actual risk, and whether it is within the organization’s risk appetite and tolerance. The risk practitioner should focus on the level of residual risk when determining whether controls are adequate to mitigate risk, as it helps to evaluate and compare the benefits and costs of the controls, and to decide on the best risk response strategy, such as accepting, avoiding, transferring, or further reducing the risk. The other options are less important or relevant to focus on when determining whether controls are adequate to mitigate risk. Sensitivity analysis is a technique that measures how the risk value changes when one or more input variables are changed, such as the probability, impact, or control effectiveness. Sensitivity analysis can help to identify and prioritize the most influential or critical variables that affect the risk value, and to test the robustness or reliability of the risk assessment. However, sensitivity analysis does not directly indicate the adequacy of controls to mitigate risk, as it does not measure the level of residual risk or the risk acceptance criteria. Cost-benefit analysis is a technique that compares the expected benefits and costs of a control or a risk response action, and determines whether it is worthwhile or not. Cost-benefit analysis can help to justify and optimize the investment or resource allocation for the control or the risk response action, and to ensure that it is aligned with the organization’s objectives and value. However, cost-benefit analysis does not directly indicate the adequacy of controls to mitigate risk, as it does not measure the level of residual risk or the risk acceptance criteria. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk appetite can help to define and communicate the organization’s risk preferences and boundaries, and to guide the risk decision-making and behavior. However, risk appetite does not directly indicate the adequacy of controls to mitigate risk, as it does not measure the level of residual risk or the actual risk performance. References = Risk IT Framework, ISACA, 2022, p. 131
Which of the following is the PRIMARY reason for managing emerging risk?
Options:
The organization is likely to become prone to continuous disruptive events.
Risk assessment methodologies cannot be applied to emerging risk.
Assumptions about the future state are likely to become invalid.
The number of risk scenarios may become uncontrollably high.
Answer:
CA department has been granted an exception to bypass the existing approval process for purchase orders. The risk practitioner should verify the exception has been approved by which of the following?
Options:
Internal audit
Control owner
Senior management
Risk manager
Answer:
CExplanation:
A purchase order approval process is a set of procedures that companies use to authorize the purchase of goods or services from suppliers1. This process typically involves multiple levels of approvals, ensuring that purchases are compliant with company regulations and policies, and within budget limitations1. Sometimes, a department may be granted an exception to bypass the existing approval process for purchase orders, for example, due to urgency, emergency, or special circumstances2. However, such exceptions should not compromise the effectiveness and integrity of the purchase order approval process, and should be properly documented and justified2. Therefore, the risk practitioner should verify that the exception has been approved by senior management, as they are ultimately responsible for setting and overseeing the purchase order approval process, and for ensuring that the exceptions are reasonable and aligned with the company’s objectives and risk appetite3. Internal audit is not the correct answer, as they are not involved in approving the purchase order approval process or its exceptions. Internal audit’s role is to provide independent assurance and advice on the adequacy and effectiveness of thepurchase order approval process and its controls, and to report any issues or recommendations for improvement4. Control owner is not the correct answer, as they are not involved in approving the purchase order approval process or its exceptions. Control owner’s role is to design, implement, and operate the controls that support the purchase order approval process, and to monitor and report on the performance and compliance of the controls5. Risk manager is not the correct answer, as they are not involved in approving the purchase order approval process or its exceptions. Risk manager’s role is to identify, assess, and mitigate the risks associated with the purchase order approval process, and to communicate and report on the risk status and issues6. References = 1: A Step-by-Step Guide to a Purchase Order Approval Process2: Purchase Order Exceptions | Fordham3: Purchase Order (PO) Approval Process and Approval Workflow - ProcureDesk4: IT Risk Resources | ISACA5: CRISC Resources [updated 2021] | Infosec6: Riskand Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.
A risk owner has accepted a high-impact risk because the control was adversely affecting process efficiency. Before updating the risk register, it is MOST important for the risk practitioner to:
Options:
ensure suitable insurance coverage is purchased.
negotiate with the risk owner on control efficiency.
reassess the risk to confirm the impact.
obtain approval from senior management.
Answer:
DExplanation:
A risk owner is the individual who is accountable for the management of a specific risk. A risk owner can decide to accept a high-impact risk if the control that mitigates the risk is adversely affecting the process efficiency. However, before updating the risk register, which is a document that records and tracks the identified risks and their responses, it is most important for the risk practitioner to obtain approval from senior management. Senior management is the group of executives who have the authority and responsibility for the strategic direction and performance of the organization. Obtaining approval from senior management can help ensure that the risk acceptance decision is aligned with the organization’s risk appetite and policies, and that the potential consequences of the high-impact risk are understood and accepted by the top-level decision makers. Obtaining approval from senior management can also help communicate and justify the risk acceptance decision to other stakeholders, such as regulators, auditors, customers, etc., and avoid any conflicts or misunderstandings that may arise from the risk acceptance decision. References = Why Assigning a Risk Owner is Important and How to Do It Right, Risk Ownership: A brief guide, Creating a Risk Register: All You Need to Know.
Which of the following is the PRIMARY purpose of analyzing control effectiveness during risk analysis?
Options:
To enable a control cost-benefit analysis
To evaluate the risk impact
To determine the likelihood of occurrence
To determine the current risk level
Answer:
DExplanation:
During risk analysis, CRISC distinguishes between inherent risk (without controls) and residual or current risk (with controls). Analyzingcontrol effectiveness—both in design and operation—is central to determining thecurrent risk level. Effective controls reduce either the likelihood of occurrence, the impact, or both. The assessment of their strength, coverage, and reliability allows the practitioner to adjust the initial inherent risk estimate down to a realistic residual risk figure and compare this to appetite and tolerance. Cost-benefit analysis of controls is a later step in risk response decision-making. Impact evaluation depends more on the nature of assets and processes than on controls. Likelihood is influenced by controls, but the primary purpose of control effectiveness analysis is to calculate the updated (residual) risk level, not just likelihood independently.
When determining which control deficiencies are most significant, which of the following would provide the MOST useful information?
Options:
Risk analysis results
Exception handling policy
Vulnerability assessment results
Benchmarking assessments
Answer:
AExplanation:
A control deficiency is a weakness or flaw in the design or implementation of a control that reduces its effectiveness or efficiency in achieving its intended objective or mitigating the risk that it is designed to address. A control deficiency may be caused by various factors, such as human error, system failure, process inefficiency, resource limitation, etc.
When determining which control deficiencies are most significant, the most useful information would be the risk analysis results, which are the outcomes or outputs of the risk analysis process that measures and compares the likelihood and impact of various risk scenarios, and prioritizes them based on their significance and urgency. The risk analysis results can help to determine which control deficiencies are most significant by providing the following information:
The level and priority of the risks that are associated with the control deficiencies, and the potential consequences or impacts that they may cause for the organization if they materialize.
The gap or difference between the current and desired level of risk, and the extent or degree to which the control deficiencies contribute to or affect the gap or difference.
The cost-benefit or feasibility analysis of the possible actions or plans to address or correct the control deficiencies, and the expected or desired outcomes or benefits that they may provide for the organization.
The other options are not the most useful information when determining which control deficiencies are most significant, because they do not provide the same level of detail and insight that the risk analysis results provide, and they may not be relevant or actionable for the organization.
An exception handling policy is a policy that defines and describes the procedures and guidelines for dealing with the situations or circumstances that deviate from the normal or expected operation or functionality of a control, and that may require special or alternative actions or measures to address or resolve them. An exception handling policy can provide useful information on how to handle or manage the control deficiencies, but it is not the most usefulinformation when determining which control deficiencies are most significant, because it does not indicate the level and priority of the risks that are associated with the control deficiencies, and the potential consequences or impacts that they may cause for the organization.
A vulnerability assessment is an assessment that identifies and evaluates the weaknesses or flaws in the organization’s assets, processes, or systems that can be exploited or compromised by the threats or sources of harm that may affect the organization’s objectives or operations. A vulnerability assessment can provide useful information on the existence and severity of the control deficiencies, but it is not the most useful information when determining which control deficiencies are most significant, because it does not indicate the likelihood and impact of the risk scenarios that are associated with the control deficiencies, and the potential consequences or impacts that they may cause for the organization.
A benchmarking assessment is an assessment that compares and contrasts the organization’s performance, practices, or processes with those of other organizations or industry standards, and identifies the strengths, weaknesses, opportunities, or threats that may affect the organization’s objectives or operations. A benchmarking assessment can provide useful information on the best practices or improvement areas for the organization, but it is not the most useful information when determining which control deficiencies are most significant, because it does not indicate the level and priority of the risks that are associatedwith the control deficiencies, and the potential consequences or impacts that they may cause for the organization. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 176
CRISC Practice Quiz and Exam Prep
Which of the following is the PRIMARY role of a data custodian in the risk management process?
Options:
Performing periodic data reviews according to policy
Reporting and escalating data breaches to senior management
Being accountable for control design
Ensuring data is protected according to the classification
Answer:
CIn an organization that allows employee use of social media accounts for work purposes, which of the following is the BEST way to protect company sensitive information from being exposed?
Options:
Educating employees on what needs to be kept confidential
Implementing a data loss prevention (DLP) solution
Taking punitive action against employees who expose confidential data
Requiring employees to sign nondisclosure agreements
Answer:
DExplanation:
The best way to protect company sensitive information from being exposed when an organization allows employee use of social media accounts for work purposes is to require employees to sign nondisclosure agreements. Nondisclosure agreements are legal contracts that prohibit the employees from disclosing or sharing the company sensitive information with unauthorized parties, such as competitors, media, or regulators. Nondisclosure agreements also specify the scope, duration, and conditions of the nondisclosure obligation, and the penalties or remedies for breaching the agreement. Requiring employees to sign nondisclosure agreements is the best way to protect company sensitive information, as it helps to prevent or deter the employees from exposing or leaking the company sensitive information on social media, and to hold the employees accountable and liable for their actions. Requiring employees to signnondisclosure agreements also helps to comply with the legal and regulatory requirements for data protection and privacy. Educating employees on what needs to be kept confidential, implementing a data loss prevention (DLP) solution, and taking punitive action against employees who expose confidential data are also useful ways, but they are not as effective as requiring employees to sign nondisclosure agreements, as they are either dependent on the employees’ awareness or behavior, or reactive or corrective measures, rather than proactive or preventive measures. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 217.
IT disaster recovery point objectives (RPOs) should be based on the:
Options:
maximum tolerable downtime.
maximum tolerable loss of data.
need of each business unit.
type of business.
Answer:
BExplanation:
IT disaster recovery point objectives (RPOs) should be based on the:
B. maximum tolerable loss of data.
RPOs are determined by how much data loss an organization can withstand in the event of a disaster. It’s a measure of the maximum age of files that an organization must recover from backup storage for normal operations to resume after a disaster. Therefore, RPOs are directly related to the maximum tolerable loss of data.
Which of the following activities is a responsibility of the second line of defense?
Options:
Challenging risk decision making
Developing controls to manage risk scenarios
Implementing risk response plans
Establishing organizational risk appetite
Answer:
AExplanation:
The second line of defense is responsible for challenging the risk decision making of the first line of defense, which is the business process owners and managers. The second line of defense also provides oversight, guidance, and support to the first line of defense in implementing andmaintaining effective risk management practices. The second line of defense includes functions such as risk management, compliance, quality assurance, and internal audit. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.2: IT Risk Management Roles and Responsibilities, Page 14.
Which of the following would be the result of a significant increase in the motivation of a malicious threat actor?
Options:
Increase in mitigating control costs
Increase in risk event impact
Increase in risk event likelihood
Increase in cybersecurity premium
Answer:
CExplanation:
The result of a significant increase in the motivation of a malicious threat actor would be an increase in risk event likelihood. The likelihood of a risk event is influenced by the factors of threat, vulnerability, and exposure. The motivation of a threat actor is a key component of the threat factor, as it reflects the intent and capability of the actor to exploit a vulnerability. Therefore, a higher motivation would imply a higher probability of an attack. An increase in mitigating control costs, risk event impact, or cybersecurity premium are possible consequences of a risk event, but they are not directly affected by the motivation of the threat actor. References = ISACA Certified in Risk and Information Systems Control (CRISC)Certification Exam Question and Answers, question 6; CRISC Review Manual, 6th Edition, page 67.
A large organization recently restructured the IT department and has decided to outsource certain functions. What action should the control owners in the IT department take?
Options:
Conduct risk classification for associated IT controls.
Determine whether risk responses still effectively address risk.
Perform vulnerability and threat assessments.
Analyze and update IT control assessments.
Answer:
BExplanation:
According to the ISACA Risk and Information Systems Control study guide and handbook, the control owners in the IT department should determine whether risk responses still effectively address risk after a restructuring and outsourcing of certain functions. This is because the restructuring and outsourcing may have changed the risk profile, the control environment, and the control activities of the IT department. The control owners should review the existing risk responses and evaluate if they are still appropriate, adequate, and efficient in mitigating the risks associated with the outsourced functions. The control owners should also monitor the performance and compliance of the service providers and ensure that the contractual obligations and service level agreements are met12
1: ISACA Risk and Information Systems Control Study Guide, 4th Edition, page 33 2: ISACA Risk and Information Systems Control Handbook, 1st Edition, page 25
A control for mitigating risk in a key business area cannot be implemented immediately. Which of the following is the risk practitioner ' s BEST course of action when a compensating control needs to be applied?
Options:
Obtain the risk owner ' s approval.
Record the risk as accepted in the risk register.
Inform senior management.
update the risk response plan.
Answer:
AExplanation:
A compensating control is a temporary or alternative control that is implemented when the primary control for mitigating a risk is not feasible or available. A compensating control should provide a similar level of protection and assurance as the primary control, and should be aligned with the risk appetite and tolerance of the organization. The risk practitioner’s best course of action when a compensating control needs to be applied is to obtain the risk owner’s approval. The risk owner is the person who has the authority and accountability for managing a specific risk, and who is responsible for ensuring that the risk is within the acceptable level. The risk practitioner should consult with the risk owner to explain the situation, proposethe compensating control, and seek their approval before implementing it. This way, the risk practitioner can ensure that the compensating control is appropriate, effective, and acceptable for the risk owner, and that the risk owner is aware of and agrees with the change in the risk treatment. The other options are not the best course of action, as they do not involve the risk owner’s approval or input. Recording the risk as accepted in the risk register implies that the risk is not treated or reduced, which may not be the case with a compensating control. Informing senior management may be a good practice, but it does not ensure that the risk owner is involved or agrees with the compensating control. Updating the risk response plan may be a necessary step after implementing the compensating control, but it does not require the risk owner’s approval or consultation. References = 5 Key Risk Mitigation Strategies (With Examples), Risk Management 101: Process, Examples, Strategies
A risk assessment has identified that an organization may not be in compliance with industry regulations. The BEST course of action would be to:
Options:
conduct a gap analysis against compliance criteria.
identify necessary controls to ensure compliance.
modify internal assurance activities to include control validation.
collaborate with management to meet compliance requirements.
Answer:
AExplanation:
According to the CRISC Review Manual (Digital Version), the best course of action when a risk assessment has identified that an organization may not be in compliance with industry regulations is to conduct a gap analysis against compliance criteria, which is a method of comparing the current state of compliance with the desired or required state of compliance. Conducting a gap analysis against compliance criteria helps to:
Identify and evaluate the differences or discrepancies between the compliance requirements and the actual compliance practices and capabilities
Assess the impact and severity of the compliance gaps on the organization’s objectives and performance
Prioritize the compliance gaps based on their urgency and importance
Develop and implement appropriate actions or measures to close or reduce the compliance gaps
Monitor and measure the effectiveness and efficiency of the actions or measures taken to address the compliance gaps
References = CRISC Review Manual (Digital Version), Chapter 1: IT Risk Identification, Section 1.5: IT Risk Identification Methods and Techniques, pp. 34-351
Which of the following is MOST useful when performing a quantitative risk assessment?
Options:
RACI matrix
Financial models
Management support
Industry benchmarking
Answer:
BWhich of the following BEST enables detection of ethical violations committed by employees?
Options:
Transaction log monitoring
Access control attestation
Periodic job rotation
Whistleblower program
Answer:
DExplanation:
Whistleblower Program:
Definition: A whistleblower program allows employees to report unethical or illegal activities within the organization anonymously.
Detection of Ethical Violations: Employees are often in the best position to observe unethical behavior. A well-structured whistleblower program encourages them to report such behavior without fear of retaliation.
Anonymity and Protection: Providing anonymity and protection to whistleblowers increases the likelihood that employees will report violations, thus enabling the organization to detect and address ethical issues more effectively.
Comparison with Other Options:
Transaction Log Monitoring: While useful for detecting anomalies and potential fraud, it is not specifically focused on ethical violations and may not capture all types of unethical behavior.
Access Control Attestation: This ensures that users have the correct access permissions but does not directly detect unethical behavior.
Periodic Job Rotation: This can help prevent fraud by reducing the risk of collusion and providing fresh perspectives on processes, but it does not directly detect ethical violations.
Best Practices:
Clear Reporting Channels: Ensure that the whistleblower program has clear and accessible reporting channels.
Training and Awareness: Regularly train employees on the importance of reporting unethical behavior and the protections offered by the whistleblower program.
Follow-up and Action: Ensure that reports are investigated thoroughly and appropriate actions are taken to address verified violations.
Warning banners on login screens for laptops provided by an organization to its employees are an example of which type of control?
Options:
Corrective
Preventive
Detective
Deterrent
Answer:
DExplanation:
Warning banners on login screens serve as deterrent controls. Deterrent controls are designed to discourage individuals from attempting unauthorized actions by warning them of potential consequences.
Purpose of Warning Banners
Warning banners provide clear notice to users, both authorized and unauthorized, that their activities may be monitored and that unauthorized access is prohibited.
They serve as a legal disclaimer, which can be crucial in prosecuting unauthorized access attempts.
Effectiveness as a Deterrent Control
The primary function of a warning banner is to deter potential intruders by making them aware of the surveillance and legal implications of unauthorized access.
For authorized users, it reinforces awareness of the organization ' s security policies and acceptable use agreements.
Comparison with Other Control Types
A. Corrective: These controls are used to correct or restore systems after an incident.
B. Preventive: These controls are designed to prevent security incidents from occurring.
C. Detective: These controls are used to detect and alert about security incidents.
D. Deterrent: These controls are intended to discourage individuals from performing unauthorized activities.
References
Sybex-CISSP-Official-Study-Guide-9-Edition.pdf, p. 829, detailing the role of warning banners as deterrent controls.
A cote data center went offline abruptly for several hours affecting many transactions across multiple locations. Which of the to " owing would provide the MOST useful information to determine mitigating controls?
Options:
Forensic analysis
Risk assessment
Root cause analysis
Business impact analysis (BlA)
Answer:
CExplanation:
The most useful information to determine mitigating controls when a core data center went offline abruptly for several hours affecting many transactions across multiple locations is the root cause analysis. Root cause analysis is a technique that identifies the underlying factors or reasons that caused the problem or incident. Root cause analysis can help to understand the nature, scope,and impact of the problem or incident, and to prevent or reduce the recurrence or severity of the problem or incident in the future. Root cause analysis can also help to identify and prioritize the appropriate mitigating controls that address the root causes of the problem or incident. The other options are not as useful as root cause analysis, as they are related to the investigation, evaluation, or measurement of the problem or incident, not the resolution or prevention of the problem or incident. References = Risk and Information Systems ControlStudy Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.4: Key Control Indicators, page 211.
Which of the following BEST enables a risk practitioner to identify the consequences of losing critical resources due to a disaster?
Options:
Risk management action plans
Business impact analysis (BIA)
What-if technique
Tabletop exercise results
Answer:
BExplanation:
Business Impact Analysis (BIA):
Purpose: A BIA is a systematic process to evaluate the potential effects of an interruption to critical business operations as a result of a disaster, accident, or emergency.
Identification of Consequences: It identifies critical resources and the consequences of their loss, allowing an organization to determine the operational and financial impacts of such losses.
Steps Involved in BIA:
Identify Critical Functions: Determine which business functions and processes are essential to the organization ' s operations.
Assess Impact: Evaluate the impact of losing these functions on the organization’s ability to operate.
Estimate Downtime Tolerance: Determine the maximum allowable downtime for critical functions before significant harm occurs.
Identify Dependencies: Document dependencies between systems, processes, and resources to understand how disruptions to one part affect the whole.
Comparison with Other Options:
Risk Management Action Plans: These are detailed plans developed to address identified risks but do not specifically focus on the impact of losing critical resources.
What-if Technique: This is a brainstorming technique used to explore potential risks and their impacts but is not as structured as a BIA.
Tabletop Exercise Results: These exercises simulate disaster scenarios to test response plans but do not provide the comprehensive impact analysis that a BIA does.
Best Practices:
Regular Updates: Regularly update the BIA to reflect changes in the business environment and operational dependencies.
Integration with DR/BC Plans: Ensure that findings from the BIA are integrated into disaster recovery (DR) and business continuity (BC) plans to enhance overall preparedness.
IT management has deployed a major update to reduce the risk of system compromise. What is the BEST way to validate the effectiveness of this control?
Options:
Conduct social engineering testing.
Perform penetration testing.
Run vulnerability scans.
Review mean time to apply critical patches.
Answer:
BExplanation:
The correct answer is B because penetration testing validates whether the implemented control actually resists realistic compromise attempts. The uploaded CRISC notes state that penetration testing offers the greatest level of assurance regarding the effectiveness of implemented security controls and that penetration testing is the best way to ensure network security against external attacks.
ISACA also states that control testing demonstrates whether controls are mitigating risk as intended, including assessing network security and testing controls designed to prevent or detect unauthorized access, data breaches, and system failures. ISACA further explains that penetration testing evaluates vulnerabilities and supports effective risk response decisions.
C, vulnerability scanning, is useful for identifying known vulnerabilities, and it may be appropriate for validating a patching program. However, the question asks for the BEST way to validate effectiveness of a major update intended to reduce system compromise, making penetration testing stronger. A is too narrow because social engineering tests people rather than the technical control. D is only a metric and does not validate whether the update reduced compromise risk.
Which of the following should be a risk practitioner ' s NEXT step upon learning the impact of an organization ' s noncompliance with a specific legal regulation?
Options:
Identify risk response options.
Implement compensating controls.
Invoke the incident response plan.
Document the penalties for noncompliance.
Answer:
AExplanation:
The next step is toidentify risk response optionsto address the noncompliance and mitigate its impact. This may include corrective actions, implementing controls, or negotiating terms to reduce exposure.
The PRIMARY reason a risk practitioner would be interested in an internal audit report is to:
Options:
plan awareness programs for business managers.
evaluate maturity of the risk management process.
assist in the development of a risk profile.
maintain a risk register based on noncompliance.
Answer:
BExplanation:
According to the CRISC Review Manual (Digital Version), the primary reason a risk practitioner would be interested in an internal audit report is to evaluate the maturity of the risk management process, as it provides an independent and objective assessment of the effectiveness and efficiency of the risk management activities and controls. An internal audit report helps to:
Identify and evaluate the strengths and weaknesses of the risk management process and its alignment with the organization’s objectives and strategy
Detect and report any gaps, errors, or deficiencies in the risk identification, assessment, response, and monitoring processes and controls
Recommend and implement corrective actions or improvement measures to address the issues or findings in the risk management process
Communicate and coordinate the audit results and recommendations with the relevant stakeholders, such as the risk owners, the senior management, and the board
Enhance the accountability and transparency of the risk management process and its outcomes
References = CRISC Review Manual (Digital Version), Chapter 4: IT Risk Monitoring and Reporting, Section 4.2: IT Risk Reporting, pp. 223-2241
Which of the following is MOST essential for an effective change control environment?
Options:
Business management approval of change requests
Separation of development and production environments
Requirement of an implementation rollback plan
IT management review of implemented changes
Answer:
BExplanation:
The most essential factor for an effective change control environment is the separation of development and production environments. This ensures that changes are tested and verified in a controlled environment before being implemented in the live environment, reducing the risk of errors, failures, and unauthorized modifications. Business management approval of change requests, requirement of an implementation rollback plan, and IT management review of implemented changes are important elements of change control, but they are not as essential as the separation of environments. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.2.1.2, page 123.
Which of the following should a risk practitioner review FIRST when evaluating risk events associated with the organization ' s data flow model?
Options:
Results of data classification activities
Recent changes to enterprise architecture (EA)
High-level network diagrams
Notes from interviews with the data owners
Answer:
AWhich of the following BEST enables an organization to increase the likelihood of identifying risk associated with unethical employee behavior?
Options:
Require a signed agreement by employees to comply with ethics policies
Conduct background checks for new employees
Establish a channel to anonymously report unethical behavior
Implement mandatory ethics training for employees
Answer:
CExplanation:
Anonymous reporting mechanisms (e.g., hotlines, web portals) encourage employees to report unethical behavior without fear of retaliation. This increases visibility into otherwise hidden risks and supports early intervention.
Which of the following findings of a security awareness program assessment would cause the GREATEST concern to a risk practitioner?
Options:
The program has not decreased threat counts.
The program has not considered business impact.
The program has been significantly revised
The program uses non-customized training modules.
Answer:
DExplanation:
The greatest concern for a risk practitioner when reviewing the findings of a security awareness program assessment is that the program uses non-customized training modules. Non-customizedtraining modules are generic and may not address the specific security needs, issues, and challenges of the organization. They may also fail to engage and motivate the employees to follow the security policies and procedures, and to enhance their security knowledge and skills. The program not decreasing threat counts, not considering business impact, or being significantly revised are other possible findings, but they are not as concerning as the program using non-customized training modules. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
Which of the following should be the FIRST consideration when a business unit wants to use personal information for a purpose other than for which it was originally collected?
Options:
Informed consent
Cross border controls
Business impact analysis (BIA)
Data breach protection
Answer:
AExplanation:
According to the GDPR, personal data shall be collected for specified, explicit and legitimate purposes and not further processed in a manner that is incompatible with those purposes1. This means that a business unit can only use personal information for a different purpose if it has obtained the consent of the data subject, or if it has a clear legal basis or obligation to do so2. Therefore, informed consent should be the first consideration when a business unit wants to use personal information for a purpose other than for which it was originally collected.
References = GDPR Article 5 (1) (b) and Article 6 (4)1, ICO Principle (b): Purpose limitation2
Which of the following situations would cause the GREATEST concern around the integrity of application logs?
Options:
Weak privileged access management controls
Lack of a security information and event management (SIEM) system
Lack of data classification policies
Use of hashing algorithms
Answer:
AWhat should a risk practitioner do FIRST when a shadow IT application is identified in a business owner ' s business impact analysis (BIA)?
Options:
Include the application in the business continuity plan (BCP).
Determine the business purpose of the application.
Segregate the application from the network.
Report the finding to management.
Answer:
BExplanation:
Determining the business purpose of the application is the first thing that a risk practitioner should do when a shadow IT application is identified in a business owner’s business impactanalysis (BIA), because it helps to understand the rationale and value of the application, and the potential risks and issues that it may introduce or affect. A shadow IT application is an IT system or application that is used by the business units or employees without the knowledge or approval of the IT department or management. A shadow IT application may offer benefits such as convenience, efficiency, or innovation, but it may also pose risks such as security breaches, data loss, compatibility issues, or regulatory non-compliance. A BIA is a process of analyzing the potential impact of disruption to the critical business functions or processes, and identifying the recovery priorities and requirements. A BIA may reveal the existence of ashadow IT application, as it may be used to support or enable a critical business function or process. Determining the business purpose of the application is the first thing to do, as it helps to evaluate the necessity and suitability of the application, and to plan the appropriate actions to address the shadow IT application. Including the application in the business continuity plan (BCP), segregating the application from the network, and reporting the finding to management are all possible things to do after determining the business purpose of the application, but they are not the first thing to do, as they depend on the results of the evaluation of the application. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 143
When confirming whether implemented controls are operating effectively, which of the following is MOST important to review?
Options:
Results of benchmarking studies
Results of risk assessments
Number of emergency change requests
Maturity model
Answer:
CExplanation:
The number of emergency change requests is the most important factor to review when confirming whether implemented controls are operating effectively, as it indicates the frequency and severity of incidents or issues that require urgent changes to the controls, and may reflect the control deficiencies or failures. The results of benchmarking studies, the results of risk assessments, and the maturity model are not the most important factors, as they are more related to the comparison, evaluation, or improvement of the controls, respectively, rather than the confirmation of the control effectiveness. References = CRISC Review Manual, 7th Edition, page 154.
Which of the following is the BEST approach for an organization in a heavily regulated industry to comprehensively test application functionality?
Options:
Use production data in a non-production environment
Use masked data in a non-production environment
Use test data in a production environment
Use anonymized data in a non-production environment
Answer:
DExplanation:
Using anonymized data in a non-production environment is the best approach for an organization in a heavily regulated industry to comprehensively test application functionality. Anonymized data is data that has been stripped of any personally identifiable information (PII) or other sensitive data, such as names, addresses, phone numbers, email addresses, etc. Anonymized data protects the privacy and security of the data, while still preserving the structure and format of the original data. Using anonymized data in a non-production environment allows the organization to test the application functionality without risking data breaches or violating regulations. Using production data, masked data, or test data in either production or non-production environments are not as optimal as using anonymized data, because they may introduce errors, inconsistencies, or vulnerabilities in the data or the application. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.3.1, page 3-21.
When communicating changes in the IT risk profile, which of the following should be included to BEST enable stakeholder decision making?
Options:
List of recent incidents affecting industry peers
Results of external attacks and related compensating controls
Gaps between current and desired states of the control environment
Review of leading IT risk management practices within the industry
Answer:
CExplanation:
The best thing to include when communicating changes in the IT risk profile is the gaps between the current and desired states of the control environment, as this shows the stakeholders the extent and impact of the changes, and the actions and resources needed to address them. The control environment is the set of policies, processes, and systems that provide reasonableassurance that the IT risks are identified, assessed, and treated effectively and efficiently. The current state of the control environment reflects the existing level and performance of the controls, and the residual risk that remains after the controls are applied. The desired state of the control environment reflects the target level and performance of the controls, and the risk appetite and tolerance of the organization. The gaps between the current and desired states of the control environment indicate the areas of improvement or enhancement for the IT risk management process, and the priorities and strategies for risk response. The other options are not the best things to include when communicating changes in the IT risk profile, although they may be useful or relevant information. A list of recent incidents affecting industry peers can provide some context and comparison for the IT risk profile, but it does not measure or explain the changes in the IT risk level or the control environment. Results of external attacks and related compensating controls can demonstrate the security and resilience of the IT systems and networks, but they do not cover the entire scope or spectrum of the IT risk profile or the control environment. A review of leading IT risk management practices within the industry can provide some insights and benchmarks for the IT risk management process, but it does not reflect thespecific situation or needs of the organization or the stakeholders. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk and Control Monitoring and Reporting, page 181.
An organization delegates its data processing to the internal IT team to manage information through its applications. Which of the following is the role of the internal IT team in this situation?
Options:
Data controllers
Data processors
Data custodians
Data owners
Answer:
BExplanation:
Data processing is the activity of collecting, organizing, transforming, and analyzing data to produce useful information for decision making or other purposes12.
The role of the internal IT team in this situation is data processors, which are the people or entities that process data on behalf of the data controllers, who are the people or entities that determine the purposes and means of the data processing34.
Data processors are the role of the internal IT team because they are responsible for managing information through the applications that are used by the organization, and they act under the instructions and authority of the organization, which is the data controller34.
Data processors are also the role of the internal IT team because they have to comply with the data protection laws and regulations that apply to the data processing, and they have to ensure the security and confidentiality of the data34.
The other options are not the role of the internal IT team, but rather possible roles or terms that are related to data processing. For example:
Data custodians are the people or entities that have physical or logical control over the data, and they are responsible for implementing and maintaining the technical and administrative safeguards to protect the data56. However, this role is not the role of theinternal IT team because it is a subset or function of the data processor role, and it does not reflect the full scope of the data processing activities that the internal IT team performs56.
Data owners are the people or entities that have legal rights or authority over the data, and they are responsible for defining and enforcing the policies and rules for the data access, use, and quality . However, this role is not the role of the internal IT team because it is a different or separate role from the data processor role, and it does not reflect the relationship or agreement between the organization and the internal IT team . References =
1: Data Processing - Wikipedia1
2: Data Processing: Definition, Steps, and Types2
3: Data Controller vs Data Processor: What’s the Difference?3
4: Data controller vs data processor: What are the differences and responsibilities?4
5: Data Custodian - Wikipedia5
6: Data Custodian: Definition, Role & Responsibilities6
Data Owner - Wikipedia
Data Owner: Definition, Role & Responsibilities
The MAIN purpose of conducting a control self-assessment (CSA) is to:
Options:
gain a better understanding of the control effectiveness in the organization
gain a better understanding of the risk in the organization
adjust the controls prior to an external audit
reduce the dependency on external audits
Answer:
AExplanation:
A control self-assessment (CSA) is a technique that allows managers and work teams directly involved in business units, functions, or processes to participate in assessing the organization’s risk management and control processes. The main purpose of conducting a CSA is to gain a better understanding of the control effectiveness in the organization, which means how well the controls are designed, implemented, and operated to achieve the desired outcomes and mitigate the risks. A CSA can help to identify the strengths and weaknesses of the existing controls, as well as the gaps and opportunities for improvement. A CSA can also help to enhance the awareness, ownership, and accountability of the control environment among the managers and staff. The other options are not the main purpose of conducting a CSA, although they may be related or beneficial. Gaining a better understanding of the risk in the organization is a result of conducting a CSA, but it is not the primary goal. The primary goal is to evaluate the controls that address the risks, not the risks themselves. Adjusting the controls prior to an external audit is a possible action that may follow a CSA, but it is not the reason for conducting a CSA. The reasonfor conducting a CSA is to improve the control effectiveness, not to prepare for an audit. Reducing the dependency on external audits is a potential benefit of conducting a CSA, but it is not the objective of conducting a CSA. The objective of conducting a CSA is to enhance the internal control assurance, not to replace the external audit assurance. References = CRISC Review Manual, pages 153-1541; CRISC Review Questions, Answers & Explanations Manual, page 802
Which of the following has the GREATEST impact on ensuring the alignment of the risk profile with business objectives?
Options:
An effective enterprise-wide risk awareness program
Senior management approval of risk appetite and tolerance
Stage gate reviews throughout the risk management process
Incorporation of industry best practice benchmarks and standards
Answer:
BWhich of the following is the BEST way to determine software license compliance?
Options:
List non-compliant systems in the risk register.
Conduct periodic compliance reviews.
Review whistleblower reports of noncompliance.
Monitor user software download activity.
Answer:
BExplanation:
According to the 6 Best Practices to Ensure Software License Compliance article, the best way to determine software license compliance is to conduct regular internal compliance audits. These self-assessments can be done with the help of software license management companies. The goal is to see where compliance issues lie and to take corrective actions before they become seriousproblems. Periodic compliance reviews can help to avoid fines, penalties, lawsuits, and reputational damage that may result from software license violations. They can also help to optimize software spending and utilization, and to identify any gaps or opportunities for improvement in the software license management process. References = 6 Best Practices to Ensure Software License Compliance
Which of the following has the GREATEST impact on backup policies for a system supporting a critical process?
Options:
Impact of threats to the process
Resource requirements of the process
Recovery time objective (RTO)
Recovery point objective (RPO)
Answer:
DWhich of the following should be done FIRST when developing an initial set of risk scenarios for an organization?
Options:
Refer to industry standard scenarios.
Use a top-down approach.
Consider relevant business activities.
Use a bottom-up approach.
Answer:
CWhat is the BEST recommendation to reduce the risk associated with potential system compromise when a vendor stops releasing security patches and updates for a business-critical legacy system?
Options:
Segment the system on its own network.
Ensure regular backups take place.
Virtualize the system in the cloud.
Install antivirus software on the system.
Answer:
AExplanation:
The best recommendation to reduce the risk associated with potential system compromise when a vendor stops releasing security patches and updates for a business-critical legacy system is to segment the system on its own network. Network segmentation is the process of dividing a network into smaller subnetworks or segments, based on different criteria, such as function, location, or security level. Network segmentation helps to isolate the system from the rest of the network, and limit the exposure and access to the system. Network segmentation also helps to improve the performance and security of the network, by reducing the network traffic and congestion, and enhancing the monitoring and control capabilities. The other options are not as effective as segmenting the system on its own network, although they may provide some additional protection or recovery options. Ensuring regular backups take place, virtualizing the system in the cloud, and installing antivirus software on the system are all measures that can helpto reduce the risk of data loss or system damage, but they do not address the root cause of the risk, which is the lack of security patches and updates for the system. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.1, page 3-11.
Which of the following should be the MOST important consideration when performing a vendor risk assessment?
Options:
Results of the last risk assessment of the vendor
Inherent risk of the business process supported by the vendor
Risk tolerance of the vendor
Length of time since the last risk assessment of the vendor
Answer:
BExplanation:
The most important consideration when performing a vendor risk assessment is the inherent risk of the business process supported by the vendor, which is the risk that exists before any controls or mitigating factors are applied. The inherent risk reflects the potential impact and likelihood of the vendor’s failure or disruption on the enterprise’s objectives, operations, and reputation. The higher the inherent risk, the more rigorous and frequent the vendor risk assessment should be. The results of the last risk assessment of the vendor, the risk tolerance of the vendor, and the length of time since the last risk assessment of the vendor are not the most important considerations, as they do not directly measure the level of exposure and dependency that the enterprise has on the vendor. References = CRISC Certified in Risk and Information Systems Control – Question204; ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 204.
Which of the following is the BEST control for a large organization to implement to effectively mitigate risk related to fraudulent transactions?
Options:
Segregation of duties
Monetary approval limits
Clear roles and responsibilities
Password policies
Answer:
AExplanation:
Segregation of duties is a key control for preventing and detecting fraudulent transactions, especially in a large organization where there are many employees and transactions involved. Segregation of duties means that no single person has the authority or ability to initiate, approve, execute, and record a transaction without the involvement or oversight of another person. This reduces the opportunity and incentive for fraud, as well as the risk of errors or omissions. Segregation of duties also facilitates the detection of fraud by creating an audit trail and increasing the likelihood of whistleblowing.
The other options are not as effective as segregation of duties for mitigating risk related to fraudulent transactions. Monetary approval limits (B) are useful for controlling the amount and frequency of transactions, but they do not prevent unauthorized or fraudulent transactions from occurring. Clear roles and responsibilities © are important for defining the expectations and accountabilities of employees, but they do not ensure that employees comply with them or that their actions are monitored and verified. Password policies (D) are essential for securing access to systems and data, but they do not prevent fraudsters from exploiting weak or compromised passwords or from using legitimate passwords for fraudulent purposes.
A cloud service provider has completed upgrades to its cloud infrastructure to enhance service availability. Which of the following is the MOST important key risk indicator (KRI) for management to monitor?
Options:
Peak demand on the cloud service during business hours
Percentage of technology upgrades resulting in security breaches
Number of incidents with downtime exceeding contract threshold
Percentage of servers not patched per policy
Answer:
CExplanation:
Monitoring the number of incidents with downtime exceeding the contract threshold is a critical KRI for assessing the effectiveness of infrastructure upgrades aimed at enhancing service availability. This metric directly reflects the provider ' s ability to meet agreed-upon service levels and helps identify areas requiring further improvement.
An organization wants to grant remote access to a system containing sensitive data to an overseas third party. Which of the following should be of GREATEST concern to management?
Options:
Transborder data transfer restrictions
Differences in regional standards
Lack of monitoring over vendor activities
Lack of after-hours incident management support
Answer:
AWhich of the following is MOST important to identify when developing top-down risk scenarios?
Options:
Key procedure control gaps
Business objectives
Senior management ' s risk appetite
Hypothetical scenarios
Answer:
BExplanation:
The most important factor to identify when developing top-down risk scenarios is B. Business objectives12
Top-down risk scenarios are based on the organization’s strategic goals, objectives, and key performance indicators (KPIs), and they aim to identify the potential events or situations that could prevent or hinder the achievement of those goals and objectives12
By identifying the business objectives, the risk practitioner can align the risk scenarios with the organization’s mission, vision, and values, and ensure that the risk scenarios are relevant, realistic, and meaningful for the senior management and other stakeholders12
The other factors are not as important as the business objectives when developing top-down risk scenarios, because they are either more relevant for bottom-up risk scenarios (A and D), or they are derived from the business objectives and the risk scenarios ©12
Which of the following is MOST helpful in aligning IT risk with business objectives?
Options:
Introducing an approved IT governance framework
Integrating the results of top-down risk scenario analyses
Performing a business impact analysis (BlA)
Implementing a risk classification system
Answer:
BExplanation:
Integrating the results of top-down risk scenario analyses is the most helpful in aligning IT risk with business objectives, as it helps to identify and prioritize the IT-related risks that could affect the achievement of the business goals and strategies. A top-down risk scenario analysis is a method of risk assessment that starts from the business perspective and considers the potential impact and likelihood of various risk events on the business outcomes and performance. A top-down risk scenario analysis can help to align IT risk with business objectives by providing the following benefits:
It ensures that the IT risk assessment is driven by the business needs and priorities, rather than by the IT technical details or assumptions.
It enables a holistic and comprehensive view of the IT risk landscape and its interdependencies with the business processes and functions.
It facilitates the communication and collaboration among the business and IT stakeholders and enhances their understanding and awareness of the IT risk exposure and control environment.
It supports the development and implementation of effective and efficient IT risk response and mitigation strategies that are aligned with the business risk appetite and objectives.
The other options are not the most helpful in aligning IT risk with business objectives. Introducing an approved IT governance framework is a good practice to establish the principles, policies, and processes for the governance of IT, but it does not directly address the IT riskalignment with the business objectives. Performing a business impact analysis (BIA) is an important step to assess the potential consequences of IT disruptions on the business operations and continuity, but it does not provide information on the likelihood or sources of the IT risk events. Implementing a risk classification system is a useful tool to categorize and organize the IT risks based on their characteristics and attributes, but it does not link the IT risks with the business objectives or outcomes. References = Risk Scenarios Toolkit - ISACA, IT Risk Resources | ISACA, How to reduce risk by aligning business strategy and IT strategy - QuoStar
Which of the following will BEST support management reporting on risk?
Options:
Control self-assessment (CSA)
Risk policy requirements
A risk register
Key performance indicators (KPIs)
Answer:
DExplanation:
Key performance indicators (KPIs) will best support management reporting on risk, as they help to measure and monitor the effectiveness and efficiency of the risk management and control processes. KPIs are metrics or measures that provide information on the current or potentialperformance of a specific activity, process, or objective. KPIs can be classified into two types: leading and lagging. Leading KPIs are predictive indicators that provide early warning signals or trends of future performance. Lagging KPIs are outcome indicators that reflect the actual or historical performance.
KPIs help to support management reporting on risk by providing the following benefits:
They enable a data-driven and evidence-based approach to risk management and reporting, rather than relying on subjective or qualitative judgments.
They facilitate a consistent and standardized way of measuring and communicating risk performance across the organization and to the external stakeholders.
They support the alignment of risk management and control activities with the organizational strategy and objectives, and help to evaluate the achievement of the desired outcomes.
They help to identify and prioritize the areas for improvement and enhancement of the risk management and control processes, and guide the development and implementation of corrective or preventive actions.
They provide feedback and learning opportunities for the risk management and control processes, and help to foster a culture of continuous improvement and innovation.
The other options are not the best choices to support management reporting on risk. Control self-assessment (CSA) is a process that involves the participation and involvement of the staff and managers in assessing the effectiveness and efficiency of the internal controls within their areas of responsibility, but it does not provide a comprehensive or objective view of the risk performance. Risk policy requirements are the documents that define the principles, rules, and guidelines for the risk management and control processes, but they do not provide actual or potential information on the risk performance. A risk register is a tool that records and tracks the information and status of the identified risks and their responses, but it does not measure or monitor the risk performance. References = Key Performance Indicators (KPIs) for Risk Management - Resolver, IT Risk Resources | ISACA, Risk Reporting - Open Risk Manual
Which of the following is the PRIMARY objective of aggregating the impact of IT risk scenarios and reflecting the results in the enterprise risk register?
Options:
To ensure IT risk appetite is communicated across the organization
To ensure IT risk impact can be compared to the IT risk appetite
To ensure IT risk ownership is assigned at the appropriate organizational level
To ensure IT risk scenarios are consistently assessed within the organization
Answer:
BExplanation:
The primary objective of aggregating the impact of IT risk scenarios and reflecting the results in the enterprise risk register is to ensure IT risk impact can be compared to the IT risk appetite, as it enables the organization to measure and evaluate the overall level and exposure of the IT risk, and to align and prioritize the IT risk response and strategy with the organizational objectives and regulations. The other options are not the primary objectives, as they are more related to the communication, assignment, or assessment of the IT risk scenarios, respectively, rather than the aggregation or reflection of the IT risk scenarios. References = CRISC Review Manual, 7th Edition, page 109.
In an organization with a mature risk management program, which of the following would provide the BEST evidence that the IT risk profile is up to date?
Options:
Risk questionnaire
Risk register
Management assertion
Compliance manual
Answer:
BExplanation:
A risk register is a tool that records and tracks the risks that may affect the organization, as well as the actions that are taken or planned to manage them1. A risk register provides the best evidence that the IT risk profile is up to date, because it reflects the current and potential IT risks that the organization faces, as well as their likelihood, impact, severity, owner, status, and response2. An IT risk profile is a document that describes the types, amounts, and priority of ITrisk that the organization finds acceptable and unacceptable3. An IT risk profile is developed collaboratively with various stakeholders within the organization, including business leaders, data and process owners, enterprise risk management, internal and external audit, legal, compliance, privacy, and IT risk management and security4. By maintaining and updating the risk register regularly, the organization can ensure that the IT risk profile is aligned with the changing IT risk environment, and that the IT risk management activities and performance are consistent and effective. The other options are not the best evidence that the IT risk profile is up to date, as they are either less comprehensive or less relevant than the risk register. A risk questionnaire is a tool that collects and analyzes the opinions and perceptions of the stakeholders about the risks that may affect the organization5. A risk questionnaire can help to identify and assess the risks, as well as to communicate and report on the risk status and issues. However, a risk questionnaire is not the best evidence that the IT risk profile is up to date, as it may not capture all the IT risks that the organization faces, or reflect the actual or objective level and nature of the IT risks. A management assertion is a statement or declaration made by the management about the accuracy and completeness of the information or data that they provide or report. A management assertion can help to increase the confidence and trust of the stakeholders and auditors in the information or data, as well as to demonstrate the accountability and responsibility of the management. However, a management assertion is not the best evidence that the IT risk profile is up to date, as it does not provide the details or outcomes of the IT risk management activities or performance, or verify the validity and reliability of the IT risk information or data. A compliance manual is a document that contains the policies, procedures, and standards that the organization must follow to meet the legal, regulatory, or contractual requirements that apply to its activities or operations. A compliance manual can help to ensure the quality and consistency of the organization’s compliance activities or performance, as well as to avoid or reduce the penalties or sanctions for non-compliance. However, a compliance manual is not the best evidence that the IT risk profile is up to date, as it does not address the IT risks that the organization faces, or the IT risk management activities or performance. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.5, Page 55.
An enterprise has taken delivery of software patches that address vulnerabilities in its core business software. Prior to implementation, which of the following is the MOST important task to be performed?
Options:
Assess the impact of applying the patches on the production environment.
Survey other enterprises regarding their experiences with applying these patches.
Seek information from the software vendor to enable effective application of the patches.
Determine in advance an off-peak period to apply the patches.
Answer:
AExplanation:
Assessing the impact of applying the patches on the production environment is the most important task to be performed prior to implementation, because it helps to identify and mitigate any potential risks or issues that may arise from the patching process. Patching is a process ofapplying updates or fixes to software or hardware to address vulnerabilities, bugs, or performance issues. Patching is essential for maintaining the security and functionality of IT systems, but it also introduces the risk of introducing new problems or breaking existing features. Therefore, before applying patches, the organization should assess the impact of the patches on the production environment, such as compatibility, performance, availability, functionality, and security. Surveying other enterprises regarding their experiences with applying these patches, seeking information from the software vendor to enable effective application of the patches, and determining in advance an off-peak period to apply the patches are all helpful tasks to be performed prior to implementation, but they are not the most important task, as they do not directly address the impact of the patches on the production environment. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.4.2, page 211
Which of the following BEST facilitates the development of relevant risk scenarios?
Options:
Perform quantitative risk analysis of historical data.
Adopt an industry-recognized risk framework.
Use qualitative risk assessment methodologies.
Conduct brainstorming sessions with key stakeholders.
Answer:
DExplanation:
Brainstorming sessions with key stakeholders are the best way to facilitate the development of relevant risk scenarios, as they can generate diverse and creative ideas, perspectives, and insights about the potential risks and their impact on the organization’s objectives and operations. Brainstorming sessions can also foster collaboration, communication, and engagement among the stakeholders, and help to identify and prioritize the most significant and realistic risk scenarios. Brainstorming sessions can be guided by an industry-recognized risk framework, such as ISACA’s Risk IT, and supported by qualitative or quantitative risk assessment methodologies, but they are not sufficient by themselves to develop relevant risk scenarios.
Which of the following is the BEST way for a risk practitioner to help management prioritize risk response?
Options:
Align business objectives to the risk profile.
Assess risk against business objectives
Implement an organization-specific risk taxonomy.
Explain risk details to management.
Answer:
BExplanation:
The best way for a risk practitioner to help management prioritize risk response is to assess risk against business objectives. This means comparing the level and nature of the risks with the goals and strategies of the organization, and determining which risks pose the most significant threat or opportunity to the achievement of those objectives. By assessing risk against business objectives, the risk practitioner can help management identify the most critical and relevant risks, and prioritize the risk response actions accordingly. The risk response actions should be aligned with the organization’s risk appetite, which is the amount and type of risk that the organization is willing to take in order to meet its strategic goals1. The other options are not the best ways for a risk practitioner to help management prioritize risk response, as they are either less effective orless specific than assessing risk against business objectives. Aligning business objectives to the risk profile is a way of ensuring that the organization’s objectives are realistic and achievable, given the current and potential risks that the organization faces. However, this is not the same as prioritizing risk response, as it does not indicate which risks should be addressed first or howtheyshould be managed. Implementing an organization-specific risk taxonomy is a way of creating a common language and classification system for describing and categorizing risks. This can help improve the consistency and clarity of risk communication and reporting across the organization. However, this is not the same as prioritizing risk response, as it does not measure the likelihood and impact of the risks, or their relation to the organization’s objectives. Explaining risk details to management is a way of providing information and insight on the sources, drivers, consequences, and responses of the risks. This can help increase the awareness and understanding of the risks among the decision makers and stakeholders. However, this is not the same as prioritizing risk response, as it does not suggest or recommend the best course of action for managing the risks. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.6, Page 57.
Which of the following is MOST important to consider when determining key performance indicators (KPIs) for a process?
Options:
Historical trends in process-related incidents
Known problems with the process
Success criteria for the process
Alignment with established industry frameworks
Answer:
CRisk acceptance of an exception to a security control would MOST likely be justified when:
Options:
automation cannot be applied to the control
business benefits exceed the loss exposure.
the end-user license agreement has expired.
the control is difficult to enforce in practice.
Answer:
BExplanation:
The most likely justification for risk acceptance of an exception to a security control is when the business benefits exceed the loss exposure. Risk acceptance is a risk response strategy that involves acknowledging and tolerating the risk, without taking any action to reduce or transfer the risk. An exception to a security control is a deviation or non-compliance from the established security policy or standard, due to a valid business reason or circumstance. Risk acceptance of an exception to a security control may be justified when the business benefits exceed the loss exposure, which means that the value or advantage of the exception outweighs the potential cost or harm of the risk. For example, an exception to a security control may enable faster or easier access to the system or data, which may improve the productivity, efficiency, or satisfaction of the users or customers, and generate more revenue or profit for the business. The business benefits of the exception may exceed the loss exposure of the risk, which may be low or negligible, or may be mitigated by other controls or factors. Therefore, risk acceptance of an exception to a security control may be a reasonable and rational decision, based on the cost-benefit analysis of the exception and the risk. Automation cannot be applied to the control, the end-user license agreement has expired, and the control is difficult to enforce in practice are not the most likely justifications for risk acceptance of an exception to a security control, as they are either irrelevant or insufficient reasons, and they do not consider the business benefits or the loss exposure of the exception and the risk. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 50.
Which of the following is the MOST important consideration for the board and senior leadership
regarding the organization ' s approach to risk management for emerging technologies?
Options:
Ensuring the organization follows risk management industry best practices
Ensuring IT risk scenarios are updated and include emerging technologies
Ensuring the risk framework and policies are suitable for emerging technologies
Ensuring threat intelligence services are used to gather data about emerging technologies
Answer:
CExplanation:
The most important consideration is that the risk framework and policies are adaptable and suitable for emerging technologies. This ensures that the organization ' s approach to risk management remains effective and relevant as new technologies are adopted, helping to mitigate potential risks associated with these technologies.
Which of the following is the PRIMARY benefit of using a risk map with stakeholders?
Options:
Consolidates risk response options by severity
Aligns risk appetite with business objectives
Correlates risk scenarios to risk appetite
Defines an organizational risk taxonomy
Answer:
CExplanation:
Arisk maphelps stakeholders understand how risk scenarios align with the organization’srisk appetite. This visualization facilitates informed decision-making and ensures risk responses are consistent with organizational priorities.
===========
Which of the following is MOST helpful in identifying gaps between the current and desired state of the IT risk environment?
Options:
Analyzing risk appetite and tolerance levels
Assessing identified risk and recording results in the risk register
Evaluating risk scenarios and assessing current controls
Reviewing guidance from industry best practices and standards
Answer:
CExplanation:
Evaluating risk scenarios and assessing current controls is the most helpful in identifying gaps between the current and desired state of the IT risk environment, because it allows the risk practitioner to compare the actual and expected outcomes of the IT processes and activities under different situations. A risk scenario is a hypothetical situation that describes a possible event or sequence of events that may affect the IT objectives and performance. A risk scenario can be based on various factors, such as the sources of risk, the risk drivers, the risk events, the risk impacts, and the risk responses. A risk scenario can also include the likelihood and severity of the risk, as well as the assumptions and uncertainties involved. Evaluating risk scenarios helps the risk practitioner to understand the nature and extent of the IT risks, as well as the potential consequences and opportunities that may arise from them. Assessing current controls is the process of examining and testing the existing controls that are implemented to manage the IT risks. A control is a measure or action that reduces the likelihood or impact of a risk, or enhances the benefits or opportunities of a risk. Assessing current controls helps the risk practitioner to determine the effectiveness and efficiency of the controls, as well as their alignment with the IT objectives and requirements. By evaluating risk scenarios and assessing current controls, the risk practitioner can identify the gaps between the current and desired state of the IT risk environment. The gaps can be related to the following aspects: - The IT objectives and performance: The gaps can indicate the difference between the actual and expected results of theIT processes and activities, as well as the deviation from the IT goals and targets. - The IT risk exposure and appetite: The gaps can indicate the difference between the actualand acceptable level of risk that the organization faces or is willing to take in pursuit of the IT objectives. - The IT risk management process and practices: The gaps can indicate the difference between the actual and expected performance of the IT risk management process, as well as the compliance with the IT risk management policies and standards. - The IT risk culture and awareness: The gaps can indicate the difference between the actual and desired level of risk awareness,understanding, and communication among the IT stakeholders, as well as the alignment with the organizational values and culture. Identifying the gaps between the current and desired state of the IT risk environment is important for the risk practitioner, as it can help to prioritize and address the IT risks, as well as to improve and optimize the IT risk management process and practices. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: Risk Scenarios, pp. 63-681
The MOST important reason to monitor key risk indicators (KRIs) is to help management:
Options:
identity early risk transfer strategies.
lessen the impact of realized risk.
analyze the chain of risk events.
identify the root cause of risk events.
Answer:
BExplanation:
Key risk indicators (KRIs) are metrics used by organizations to monitor and assess potential risks that may impact their objectives and performance. KRIs also provide early warning signals that help organizations identify, analyze, and address risks before they escalate into significant issues1. The most importantreason to monitor KRIs is to help management lessen the impact of realized risk, which is the actual or expected negative consequence of a risk event2. By monitoring KRIs, management can gain insight into the current and emerging risk exposures and trends, and evaluate their alignment with the organization’s risk appetite and tolerance3. This enables management to make informed and timely decisions and actions to mitigate or eliminate the risks, and to allocate resources and prioritize efforts where they are most needed. By lessening the impact of realized risk, management can also protect and enhance the organization’s reputation, performance, and value. Identifying early risk transfer strategies, analyzing the chain of risk events, and identifying the root cause of risk events are not the most important reasons to monitor KRIs, as they do not provide the same level of benefit and value as lessening the impact of realized risk. Identifying early risk transfer strategies is a process that involves finding and implementing ways to shift or share the risk or its impact to another party, such as through insurance, outsourcing, or hedging4. Identifying early risk transfer strategies can help to reduce the organization’s risk exposure and liability, but it does not necessarily lessen the impact of realized risk, as the risk or its impact may still occur or affect the organization indirectly. Analyzing the chain of risk events is a process that involves tracing and understanding the sequence and interconnection of the risk events that lead to a specific outcome or consequence5. Analyzing the chain of risk events can help to identify and address the root causes and contributing factors of the risk events, but it does not necessarily lessen the impact of realized risk, as the outcome or consequence may have already occurred or be unavoidable. Identifying the root cause of risk events is a process that involves finding and determining the underlying or fundamental source or reason of the risk events. Identifying the root cause of risk events can help to prevent or correct the recurrence or escalation of the risk events, but it does not necessarily lessen the impact of realized risk, as the impact may have already happened or be irreversible. References = 1: Key Risk Indicators: A Practical Guide | SafetyCulture2: Risk Impact - an overview | ScienceDirect Topics3: KRI Framework for Operational Risk Management | Workiva4: Risk Transfer - an overview | ScienceDirect Topics5: EventChainMethodology - Wikipedia : [Root Cause Analysis - an overview | ScienceDirect Topics] : [Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.1: Key Risk Indicators, pp. 181-185.]
Which of the following is the BEST criterion to determine whether higher residual risk ratings in the risk register should be accepted?
Options:
Risk maturity
Risk policy
Risk appetite
Risk culture
Answer:
CExplanation:
Risk appetite is the best criterion to determine whether higher residual risk ratings in the risk register should be accepted, as it reflects the amount and type of risk that an organization is willing to take in pursuit of its objectives. Residual risk is the level of risk that remains after applying controls or other risk treatments. By comparing the residual risk ratings against the risk appetite, an organization can decide whether to accept, reduce, transfer, or avoid the risk. If the residual risk is within or below the risk appetite, the organization may accept the risk as tolerable. If the residual risk is above the risk appetite, the organization may not accept the risk as acceptable, and may seek further risk treatments or escalation.
Which of the following is the MOST critical consideration when awarding a project to a third-party service provider whose servers are located offshore?
Options:
Difficulty of monitoring compliance due to geographical distance
Cost implications due to installation of network intrusion detection systems (IDSs)
Delays in incident communication
Potential impact on data governance
Answer:
DWhich of the following is the PRIMARY benefit of stakeholder involvement in risk scenario development?
Options:
Ability to determine business impact
Up-to-date knowledge on risk responses
Decision-making authority for risk treatment
Awareness of emerging business threats
Answer:
DExplanation:
Risk scenario development is a process that involves identifying and describing the potential risk events that can affect an organization’s objectives and operations. Risk scenario development requires the input and participation of various stakeholders, such as the management, the staff, the customers, the suppliers, the regulators, and the competitors. The primary benefit of stakeholder involvement in risk scenario development is that it increases the awareness of emerging business threats, meaning that it helps to identify and anticipate the new or changingsources and impacts of risk that may not be captured by theexisting risk assessment methods or tools. Stakeholder involvement can also help to improve the quality and completeness of the risk scenarios, as well as to enhance the communication and collaborationamong the stakeholders regarding the risk management process. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1.1, p. 66-67
Which of the following is MOST important for a multinational organization to consider when developing its security policies and standards?
Options:
Regional competitors ' policies and standards
Ability to monitor and enforce compliance
Industry-standard templates
Differences in regulatory requirements
Answer:
DExplanation:
Differences in regulatory requirements are the most important factor for a multinational organization to consider when developing its security policies and standards. This is because different countries or regions may have different laws, regulations, or standards that govern the protection of information and data, such as the General Data Protection Regulation (GDPR) in the European Union, the Health Insurance Portability and Accountability Act (HIPAA) in the United States, or the Personal Information Protection and Electronic Documents Act (PIPEDA) in Canada. A multinational organization must comply with the applicable regulatoryrequirements in each jurisdiction where it operates, or it may face legal, financial, or reputational risks. Therefore, the organization should develop its security policies and standards in a way that meets or exceeds the minimum regulatory requirements, and also aligns with its business objectives and risk appetite. According to the CRISC Review Manual 2022, one of the key elements of IT governance is to ensure compliance withexternal laws and regulations1. According to the CRISC Review Questions, Answers & Explanations Manual 2022, differences in regulatory requirements is the correct answer to this question2.
Regional competitors’ policies and standards, ability to monitor and enforce compliance, and industry-standard templates are not the most important factors for a multinational organization to consider when developing its security policies and standards. These factors may be useful or relevant, but they are not as critical or mandatory as the differences in regulatory requirements. Regional competitors’ policies and standards may provide some insights or benchmarks, but theymay not reflect the organization’s specific needs or risks. Ability to monitor and enforce compliance is an important aspect of implementing and maintaining security policies and standards, but it does not determine the content or scope of the policies and standards. Industry-standard templates may offer some guidance or best practices, but they may not cover all the regulatory requirements or the organization’s unique circumstances.
Which of the following is the PRIMARY benefit of using an entry in the risk register to track the aggregate risk associated with server failure?
Options:
It provides a cost-benefit analysis on control options available for implementation.
It provides a view on where controls should be applied to maximize the uptime of servers.
It provides historical information about the impact of individual servers malfunctioning.
It provides a comprehensive view of the impact should the servers simultaneously fail.
Answer:
DExplanation:
Using an entry in the risk register to track the aggregate risk associated with server failure provides a comprehensive view of the impact should the servers simultaneously fail, as it considers the combined effect of the server failure on the enterprise’s objectives and operations. The risk register is a document that records and tracks the identified risks, their likelihood, impact, and mitigation strategies. By aggregating the risk associated with server failure, the risk register can help to estimate the worst-case scenario and to prioritize the risk response accordingly. It provides a cost-benefit analysis on controloptions available for implementation, it provides a view on where controls should be applied to maximize the uptime of servers, and it provides historical information about the impact of individual servers malfunctioning are not the primary benefits of using an entry in the risk register to track the aggregate risk associated with server failure, but rather the possible outcomes or actions of using the risk register. References = CRISC Certified in Risk and Information Systems Control –Question220; ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 220.
Which of the following is MOST useful input when developing risk scenarios?
Options:
Common attacks in other industries.
Identification of risk events.
Impact on critical assets.
Probability of disruptive risk events.
Answer:
BExplanation:
Identifying specific risk events provides the foundational input for creating relevant and actionable risk scenarios. These scenarios form the basis of assessing potential impacts and determining effective controls. This is a key step in theRisk Identification and Assessmentprocess.
An information security audit identified a risk resulting from the failure of an automated control Who is responsible for ensuring the risk register is updated accordingly?
Options:
The risk practitioner
The risk owner
The control owner
The audit manager
Answer:
CExplanation:
A control is a measure or action that is implemented to reduce the likelihood or impact of a risk event, or to enhance the benefits or opportunities of a risk event. A control owner is a person who is assigned the responsibility and authority for the design, implementation, operation, and maintenance of a control. A risk register is a tool that records and tracks the information about the identified risks, such as the risk description, category, owner, probability, impact, response strategy, status, and action plan. When an information security audit identified a risk resulting from the failure of an automated control, the person who is responsible for ensuring the risk register is updated accordingly is the control owner. The control owner should update the risk register with the information about the failed control, such as the cause, consequence, status, and action plan. The control owner should also monitor the performance and compliance of the control, and recommend any improvements or adjustments as needed.
A risk practitioner has been asked to advise management on developing a log collection and correlation strategy. Which of the following should be the MOST important consideration when developing this strategy?
Options:
Ensuring time synchronization of log sources.
Ensuring the inclusion of external threat intelligence log sources.
Ensuring the inclusion of all computing resources as log sources.
Ensuring read-write access to all log sources
Answer:
AExplanation:
Ensuring time synchronization of log sources is the most important consideration when developing a log collection and correlation strategy, as it enables the accurate and consistent analysis and correlation of log data from different sources and systems. Time synchronization can help to identify the sequence and causality of events, and to detect and respond to any anomalies or incidents. Time synchronization can also facilitate the compliance and audit of the log data, and support the forensic investigation and legal action if needed. References = Most Asked CRISC Exam Questions and Answers, Question 10. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 248. ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 248. CRISC by Isaca Actual Free Exam Q & As, Question 9.
Which of the following is MOST helpful to understand the consequences of an IT risk event?
Options:
Fault tree analysis
Historical trend analysis
Root cause analysis
Business impact analysis (BIA)
Answer:
DExplanation:
Business impact analysis (BIA) is a process that involves analyzing the potential consequences of an IT risk event on the organization’s critical business functions and processes. BIA can help to understand the severity and duration of the disruption, the financial and operational losses, the recovery time objectives, and the recovery point objectives. BIA can also help to prioritize the recovery activities and resources, as well as to determine the acceptable level of risk and the risk mitigation strategies. BIA is the most helpful tool to understand the consequences of an IT risk event, as it provides a comprehensive and quantitative assessment of the impact and the recovery requirements. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.2, p. 206-207
The BEST metric to monitor the risk associated with changes deployed to production is the percentage of:
Options:
changes due to emergencies.
changes that cause incidents.
changes not requiring user acceptance testing.
personnel that have rights to make changes in production.
Answer:
BExplanation:
Changes deployed to production are those that affect the functionality, performance, or security of the system in a way that is visible or accessible to the end users1. These changes can introduce new risks or vulnerabilities, such as errors, bugs, compatibility issues, or unauthorized access2. Therefore, it is important to monitor the risk associated with these changes and measure how often they cause incidents in production.
One metric that can be used to monitor this risk is the percentage of changes that cause incidents in production. This metric indicates how effective the change management process is and how well the organization can prevent or mitigate potential problems caused by changes3. A high percentage of incidents indicates a high level of risk and a need for improvement in the change management process.
References = IT Change Management for SOC: Process and Best Practices, Determining and Managing Risk when Deploying Code, 6 Deployment Risks and How To Mitigate Them
Which of the following MOST effectively limits the impact of a ransomware attack?
Options:
Cyber insurance
Cryptocurrency reserve
Data backups
End user training
Answer:
CExplanation:
The most effective way to limit the impact of a ransomware attack is to have data backups. Data backups are copies of the data that are stored in a separate location or device, and can be used to restore the data in case of a loss or corruption. Data backups can help to recover the data that is encrypted or deleted by the ransomware, and to avoid paying the ransom to the attackers. Data backups also help to reduce the downtime and disruption caused by the ransomware attack, and to maintain the business continuity and availability of the data. Cyber insurance, cryptocurrency reserve, and end user training are not the most effective ways to limit the impact of a ransomware attack, as they may not prevent or recover the data loss, and may incur additional costs or risks for the enterprise. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 5, Section 5.1.1.1, page 2281
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 657.
A highly regulated organization acquired a medical technology startup company that processes sensitive personal information with weak data protection controls. Which of the following is the BEST way for the acquiring company to reduce its risk while still enabling the flexibility needed by the startup company?
Options:
Identify previous data breaches using the startup company’s audit reports.
Have the data privacy officer review the startup company’s data protection policies.
Classify and protect the data according to the parent company ' s internal standards.
Implement a firewall and isolate the environment from the parent company ' s network.
Answer:
CExplanation:
Data protection is the process of safeguarding sensitive personal information from unauthorized access, use, disclosure, modification, or destruction. Data protection can help to ensure the privacy and security ofthe data subjects, and to comply with the legal and regulatory requirements that apply to the data processing activities1.
A highly regulated organization that acquired a medical technology startup company that processes sensitive personal information with weak data protection controls faces a high risk of data breaches, fines, lawsuits, reputational damage, or loss of customer trust. The best way for the acquiring company to reduce its risk while still enabling the flexibility needed by the startupcompany is to classify and protect the data according to the parent company’s internal standards, because it can help to:
Identify and categorize the sensitive personal information based on its value, sensitivity, and criticality, such as confidential, restricted, internal, or public
Apply and enforce the appropriate data protection policies, procedures, and controls for each data category, such as encryption, access control, backup, retention, or disposal
Align and integrate the data protection practices and processes of the startup company with those of the parent company, and ensure the consistency and compliance across the organization
Balance and optimize the trade-off between data protection and data usability, and allow the startup company to leverage the data for innovation and growth, as long as it meets the data protection standards of the parent company23
The other options are not the best ways for the acquiring company to reduce its risk while still enabling the flexibility needed by the startup company, but rather some of the steps or aspects of data protection. Identify previous data breaches using the startup company’s audit reports is a step that can help to assess the current data protection status and gaps of the startup company, and to learn from the past incidents and mistakes, but it does not address the future data protection needs and challenges of the startup company. Have the data privacy officer review the startup company’s data protection policies is an aspect that can help to ensure the legal and regulatory compliance of the data protection activities of the startup company, and to provide guidance and oversight for the data protection issues and risks, but it does not ensure the technical and operational effectiveness and efficiency of the data protection controls of the startup company. Implement a firewall and isolate the environment from the parent company’s network is a control that can help to prevent or limit the external or internal attacks or threats to the data of the startup company, and to reduce the exposure or impact of a data breach, but it does not ensure the availability or accessibility of the data for the legitimate and authorized purposes of the startup company. References =
Data Protection - ISACA
Data Classification - ISACA
Data Protection Best Practices - ISACA
[CRISC Review Manual, 7th Edition]
Which of the following is MOST important for a project steering committee to consider when deciding to release a new system into production?
Options:
Dynamic application security testing (DAST) results
Project implementation plan
Project risk register
User acceptance testing (UAT) results
Answer:
DExplanation:
The correct answer isDbecauseuser acceptance testing (UAT) resultsare the most important consideration when deciding whether to release a new system into production. UAT confirms that the system meets business requirements and is ready for operational use. Since the steering committee is making a go/no-go decision for production release, the most critical question is whether users have validated that the solution is fit for purpose.
The other options are important, but not the most important for final release approval:
A. Dynamic application security testing (DAST) resultsare valuable for identifying security weaknesses, but by themselves they do not confirm that the system satisfies business and user requirements.
B. Project implementation plansupports deployment readiness, but it does not prove that the system is acceptable to the business.
C. Project risk registerprovides visibility into project risk, but it is not the strongest direct indicator that the system is ready for production.
Exact Extracts supporting the answer:
“To ensure that an application is ready to be implemented the best test is the user acceptance test.”
“Before moving on to the system design phase it MUST be accomplished that the risk associated with the proposed system and controls is accepted by management.”
“Business stakeholders and decision makers primarily validate the effectiveness of IT risk responses by checking if IT controls achieve the desired objectives.”
“The PRIMARY result of a risk assessment process is input for risk-aware decisions.”
These extracts show that readiness for implementation and final business validation are best demonstrated throughuser acceptance testing. Therefore, UAT results are the most important factor for the steering committee when deciding to release a new system into production.
A risk practitioner has observed that there is an increasing trend of users sending sensitive information by email without using encryption. Which of the following would be the MOST effective approach to mitigate the risk associated with data loss?
Options:
Implement a tool to create and distribute violation reports
Raise awareness of encryption requirements for sensitive data.
Block unencrypted outgoing emails which contain sensitive data.
Implement a progressive disciplinary process for email violations.
Answer:
CExplanation:
According to the CRISC Review Manual (Digital Version), the most effective approach to mitigate the risk associated with data loss due to users sending sensitive information by email without using encryption is to block unencrypted outgoing emails which contain sensitive data. This is an example of a risk avoidance strategy, which aims to eliminate the risk by removing the source of the risk or the activity that causes the risk. Blocking unencrypted outgoing emails which contain sensitive data can prevent unauthorized access, disclosure, modification or destruction of the sensitive information, and thus protect the confidentiality, integrity and availability of the data. This approach can also deter users from violating the encryption policy and enforce compliance with the security standards and regulations.
References = CRISC Review Manual (Digital Version), Chapter 3: IT Risk Response, Section 3.3: Risk Response Options, pp. 167-1681
Options:
Key performance indicators (KPIs)
Key risk indicator (KRI) thresholds
Risk trends
Risk objectives
Answer:
BExplanation:
A decrease in risk appetite typically results in tighter tolerances and thresholds for KRIs, as the organization becomes less willing to accept certain levels of risk. KPIs and risk objectives may also be impacted but are less directly tied to appetite shifts. Risk trends reflect historical data rather than appetite settings
Options:
Strategic investment portfolio.
Business impact analysis (BIA) results.
Alignment with risk appetite.
Key risk indicator (KRI) trends.
Answer:
CExplanation:
Senior management’s primary consideration in selecting risk response strategies is alignment with the organization’s risk appetite, ensuring that responses are consistent with the levels of risk the organization is willing to accept. While BIA results, KRIs, and investment portfolios inform decisions, risk appetite provides the guiding framework for prioritization and decision-making
An organization has opened a subsidiary in a foreign country. Which of the following would be the BEST way to measure the effectiveness of the subsidiary ' s IT systems controls?
Options:
Implement IT systems in alignment with business objectives.
Review metrics and key performance indicators (KPIs).
Review design documentation of IT systems.
Evaluate compliance with legal and regulatory requirements.
Answer:
BExplanation:
The best way to measure the effectiveness of the subsidiary’s IT systems controls is to review metrics and key performance indicators (KPIs), as they provide quantitative and qualitative measures of the performance and outcomes of the IT systems and processes, and how well they meet the predefined standards and expectations. Metrics and KPIs can help to evaluate the efficiency, reliability, security, and quality of the IT systems and controls, and to identify any gaps, weaknesses, or issues that need to be addressed. Metrics and KPIs can also help to compare and benchmark the subsidiary’s IT systems and controls with those of the parent organization or other similar entities. The other options are not the best ways to measure the effectiveness of the subsidiary’s IT systems controls, although they may be useful or complementary methods. Implementing IT systems in alignment with business objectives is a good practice, but it does not measure the effectiveness of the IT systems controls, as it focuses on the alignment andintegration of the IT systems with the business strategy and goals. Reviewing design documentation of IT systems can provide some information on the specifications and requirements of the IT systems, but it does not measure the effectiveness of the IT systems controls, as it does not reflect the actual implementation and operation of the IT systems. Evaluating compliance with legal and regulatory requirements can ensure that the subsidiary’s IT systems and controls meet the minimum standards and obligations of the foreign country, but it does not measure the effectiveness of the IT systems controls, as it does not consider the performance and outcomes of the IT systems and processes. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk and Control Monitoring and Reporting, page 187.
Which of the following management actions will MOST likely change the likelihood rating of a risk scenario related to remote network access?
Options:
Creating metrics to track remote connections
Updating remote desktop software
Implementing multi-factor authentication (MFA)
Updating the organizational policy for remote access
Answer:
CExplanation:
Implementing multi-factor authentication (MFA) directly reduces the likelihood of unauthorized access by adding an extra layer of verification to remote network access. ISACA and CRISC materials emphasize that technical controls (e.g., MFA) meaningfully reduce the probability of threat scenarios involving remote access
Which of the following BEST describes the role of the IT risk profile in strategic IT-related decisions?
Options:
It compares performance levels of IT assets to value delivered.
It facilitates the alignment of strategic IT objectives to business objectives.
It provides input to business managers when preparing a business case for new IT projects.
It helps assess the effects of IT decisions on risk exposure
Answer:
DExplanation:
An IT risk profile is a document that summarizes the IT-related risks that an organization faces, as well as the information and actions related to those risks, such as the risk description, assessment, response, status, and owner. An IT risk profile is a valuable tool for managing and communicating IT risks and their impact on the organization’s objectives and operations. The best description of the role of the IT risk profile in strategic IT-related decisions is that it helps assess the effects of IT decisions on risk exposure. This means that the IT risk profile can help toevaluate the potential consequences and implications of different IT choices or actions on the level and nature of the IT risks that the organization faces. The IT risk profile can also help to identify and address the gaps or opportunities for improvement in the IT risk management process and performance. The other options are not the best descriptions of the role of the IT risk profile in strategic IT-related decisions, although they may be related or beneficial. Comparing performance levels of IT assets to value delivered is a technique to measure and optimize the efficiency and effectiveness of the IT resources and activities that support the organization’s goals and needs. However, this technique does not necessarily involve the IT risk profile, as it focuses on the output and outcome of the IT assets, not the input and impact of the IT risks. Facilitating the alignment of strategic IT objectives to business objectives is a technique toensure that the IT strategy and plans are consistent and compatible with the organization’s vision, mission, strategy, and objectives. However, this technique does not depend on the IT risk profile, as it focuses on the direction and purpose of the IT objectives, not the probability and threat of the IT risks. Providing input to business managers when preparing a business case for new IT projects is a technique to support and justify the initiation and implementation of new IT initiatives that can create value or solve problems for the organization. However, this technique does not require the IT risk profile, as it focuses on the cost and benefit of the IT projects, not the risk and response of the IT risks. References = CRISC Review Manual, pages 38-391; CRISC Review Questions, Answers & Explanations Manual, page 962; IT Risk Management Guide for 2022 | CIO Insight3; IT Risk Management Process, Frameworks & Templates4
Which of the following provides the MOST comprehensive information when developing a risk profile for a system?
Options:
Results of a business impact analysis (BIA)
Risk assessment results
A mapping of resources to business processes
Key performance indicators (KPIs)
Answer:
BExplanation:
The most comprehensive information for developing a risk profile for a system is the risk assessment results. A risk assessment is a process that identifies, analyzes, and evaluates the risks that could affect the system’s objectives or operations. A risk assessment provides comprehensive information for developing a risk profile, because it helps to determine the likelihood and impact of the risks, and to prioritize them based on their severity and relevance. Arisk assessment also helps to select the most appropriate and effective controls to minimize the risks, such as avoiding, reducing, transferring, or accepting the risks. A risk profile is a document that summarizes the key risks that the system faces or accepts, and their likelihood, impact, and priority. A risk profile helps to identify and prioritize the most critical or relevant risks, and to align them with the system’s objectives, strategy, and risk appetite. The other options are not as comprehensive as the risk assessment results, although they may be part of or derived from the risk profile. Results of a business impact analysis (BIA), a mapping of resources to business processes, and key performance indicators (KPIs) are all factors that could affect the system’s performance and improvement, but they do not necessarily identify, analyze, or evaluate the risks that could affect the system. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 4-13.
The BEST indicator of the risk appetite of an organization is the
Options:
regulatory environment of the organization
risk management capability of the organization
board of directors ' response to identified risk factors
importance assigned to IT in meeting strategic goals
Answer:
CExplanation:
The board of directors’ response to identified risk factors is the best indicator of the risk appetite of an organization. The board of directors is the highest governing body of the organization, and it is responsible for setting the strategic direction, objectives, and risk appetite of the organization. The board of directors should also oversee the risk management process, and ensure that the risks are aligned with the organization’s goals and values. The board of directors’ response to identified risk factors reflects how much and what type of risk the organization is willing to pursue, retain, or take in order to achieve its objectives. The regulatory environment, the risk management capability, and the importance assigned to IT are not direct indicators of the risk appetite, although they may influence or constrain it. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.2.1, page 1-8.
Which risk response strategy could management apply to both positive and negative risk that has been identified?
Options:
Transfer
Accept
Exploit
Mitigate
Answer:
BExplanation:
Accepting risk is the only risk response strategy that could be applied to both positive and negative risk that has been identified. Accepting risk means taking no action to change the likelihood or impact of the risk, but being prepared to deal with the consequences if the risk occurs. Accepting risk is usually chosen when the risk is low, unavoidable, or outweighed by the benefits. For positive risks, accepting risk means taking advantage of the opportunities if they arise. For negative risks, accepting risk means setting aside contingency reserves or plans to copewith the threats. The other risk response strategies are specific to either positive or negative risks. Transfer, exploit, and mitigate are strategies for negative risks, while share, enhance, and avoid are strategies for positive risks. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.3.1, page 4-23.
When a high-risk security breach occurs, which of the following would be MOST important to the person responsible for managing the incident?
Options:
An analysis of the security logs that illustrate the sequence of events
An analysis of the impact of similar attacks in other organizations
A business case for implementing stronger logical access controls
A justification of corrective action taken
Answer:
AExplanation:
An analysis of the security logs that illustrate the sequence of events is the most important information for the person responsible for managing the incident, as it can help to identify the source, scope, and impact of the security breach, and to determine the appropriate response actions. An analysis of the security logs can also provide evidence for forensic investigation and legal action, and help to prevent or mitigate future incidents by identifying the root causes and vulnerabilities. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 235. CRISC by Isaca Actual FreeExam Q & As, Question 9. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 235. CRISC Sample Questions 2024, Question 235.
An online payment processor would be severely impacted if the fraud detection system has an outage. Which of the following is the BEST way to address this risk?
Options:
Implement continuous control monitoring.
Communicate the risk to management.
Introduce recovery control procedures.
Document a risk response plan.
Answer:
CExplanation:
Introducing recovery control procedures is the best way to address the risk of an outage of the fraud detection system for an online payment processor, because it helps to restore the functionality and availability of the system as quickly and effectively as possible, and to minimize the impact and disruption to the business operations and customers. A fraud detection system is a system that monitors and analyzes the transactions and activities of an online payment processor, and detects and prevents any fraudulent or suspicious behavior, such as identity theft, money laundering, or chargebacks. An outage is a situation where the system is unavailable or inaccessible, due to factors such as technical failure, human error, or malicious attack. An outage of the fraud detection system may have severe consequences for the online payment processor, such as financial losses, reputational damage, customer dissatisfaction, or regulatory penalties. A recovery control procedure is a procedure that defines the steps and actions to be taken to recover the system from an outage, such as identifying the root cause, isolating the affected components, restoring the data and functionality, testing the system, and reporting the incident. Introducing recovery control procedures is the best way to address the risk, as it helps to ensure that the system is back online and operational as soon as possible, and that the risk exposure and impact are reduced and contained. Implementing continuous control monitoring, communicating the risk to management, and documenting a risk response plan are all possible ways to address the risk, but they are not the best way, as they do not directly address the recovery of the system from an outage, and they may not be sufficient or effective to mitigate the risk. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.4.1, page 208
Which of the following should be management ' s PRIMARY consideration when approving risk response action plans?
Options:
Ability of the action plans to address multiple risk scenarios
Ease of implementing the risk treatment solution
Changes in residual risk after implementing the plans
Prioritization for implementing the action plans
Answer:
CExplanation:
The management’s primary consideration when approving risk response action plans should be the changes in residual risk after implementing the plans. Residual risk is the level of risk that remains after the implementation of risk responses1. It indicates the degree of exposure or uncertainty that the organization still faces, and the potential impact or consequences of the risk events. The management should evaluate the effectiveness and adequacy of the risk responses, and decide whether the residual risk is acceptable or not2. The management should also compare the residual risk with the risk appetite, which is the amount and type of risk that the organization is willing to accept or pursue in order to achieve its objectives3. The management should ensure that the residual risk is aligned with the risk appetite, and that the risk responses are consistent and proportional to the risk level4.
The other options are not the primary consideration when approving risk response action plans, because:
Ability of the action plans to address multiple risk scenarios is a desirable but not essential criterion for approving risk response action plans. Risk scenarios are hypothetical situations that describe how a risk event could occur and what the consequences could be5. They can help to understand and communicate the nature and impact of the risks, and to design and evaluate the risk responses6. However, not all risk scenarios are equally likely or relevant, and some risk scenarios may be too complex or improbable to address. Therefore, the ability of the action plansto address multiple risk scenarios is not the primary consideration, but rather a secondary or supplementary one.
Ease of implementing the risk treatment solution is a practical but not critical criterion for approving risk response action plans. Risk treatment is the process of selecting and applying appropriate measures to modify the risk7. It can involve different strategies, such as avoid, reduce, transfer, or accept the risk8. The ease of implementing the risk treatment solution depends on various factors, such as the availability of resources, the feasibility of the solution, or the cooperation of the stakeholders. However, the ease of implementation is not the primary consideration, but rather a supporting or facilitating one.
Prioritization for implementing the action plans is a useful but not vital criterion for approving risk response action plans. Prioritization is the process of ranking the action plans according to their importance, urgency, or impact. It can help to allocate the resources, schedule the activities, and monitor the progress of the action plans. However, prioritization is not the primary consideration, but rather a subsequent or follow-up one.
References =
Residual Risk - CIO Wiki
What is Residual Risk? - Definition from Techopedia
Risk Appetite - CIO Wiki
Risk Appetite: What It Is and Why It Matters - Gartner
Risk Scenarios Toolkit - ISACA
Risk Scenarios Starter Pack - ISACA
Risk Treatment - CIO Wiki
Risk Treatment Plan - CIO Wiki
[Prioritization - CIO Wiki]
An organization has received notification that it is a potential victim of a cybercrime that may have compromised sensitive customer data. What should be The FIRST course of action?
Options:
Invoke the incident response plan.
Determine the business impact.
Conduct a forensic investigation.
Invoke the business continuity plan (BCP).
Answer:
AExplanation:
The first course of action for an organization that has received notification that it is a potential victim of a cybercrime that may have compromised sensitive customer data is to invoke the incident response plan. An incident response plan is a set of procedures and guidelines that defines the roles and responsibilities of the incident response team, the communication and escalation channels, the incident identification and classification criteria, the incident containment and eradication strategies, the incident recovery and restoration activities, and the incident documentation and reporting requirements. Invoking the incident response plan as soon as possible is crucial to minimize the damage and disruption caused by the cybercrime, to preserve the evidence and facilitate the investigation, and to comply with the legal andregulatory obligations. The other options are not the first course of action, although they may be subsequent or concurrent steps in the incident response process. Determining the business impact is a part of the incident assessment and prioritization phase, which helps to evaluate the severity and scope of the incident and to allocate the appropriate resources and actions. Conducting a forensic investigation is a part of the incident analysis and evidence collection phase, which helps to identify the source and cause of the incident and to support the legal and disciplinary actions. Invoking the business continuity plan (BCP) is a part of the incident recovery and restoration phase, which helps to resume the normal operations and services and to mitigate the adverse effects of the incident. References = The National Cyber Incident Response Plan (NCIRP), Cyber Incident Response Plan | Cyber.gov.au, [Cyber Incident Response: A Framework for Preparation and Success] , [Cyber Incident Response Plan: How to Create One for Your Business]
Which of the following should be of MOST concern to a risk practitioner reviewing the system development life cycle (SDLC)?
Options:
Testing is completed in phases, with user testing scheduled as the final phase.
Segregation of duties controls are overridden during user testing phases.
Data anonymization is used during all cycles of end-user testing.
Testing is completed by IT support users without input from end users.
Answer:
DExplanation:
Testing is completed by IT support users without input from end users should be of most concern to a risk practitioner reviewing the system development life cycle (SDLC). This is because testing without input from end users can result in poor quality, usability, and functionality of the system, as well as increased errors, defects, and rework. Testing without input from end users can also lead to user dissatisfaction, resistance, and non-compliance, as well as misalignment with the business requirements and objectives. According to the CRISC Review Manual 2022, one of the key risk identification techniques for IT projects is to involve the end users and other relevant parties in the testing process1. According to the CRISC Review Questions, Answers & Explanations Manual 2022, testing without input from end users is the correct answer to this question2.
Testing in phases, overriding segregation of duties controls, and using data anonymization are not the most concerning issues for a risk practitioner reviewing the SDLC. These are possible practices or techniques that can be used in the testing process, but they do not necessarily pose significant risks or problems. Testing in phases can help ensure that the system meets the technical and functional specifications, as well as the user acceptance criteria, at each stage of the development. Overriding segregation of duties controls can be justified and authorized during the testing phases, as long as the controls are restored and verified before the system goes live. Using data anonymization can help protect the privacy and security of the data used in the testing process, as well as comply with the relevant regulations and standards.
Which of the following, who should be PRIMARILY responsible for performing user entitlement reviews?
Options:
IT security manager
IT personnel
Data custodian
Data owner
Answer:
DExplanation:
The person or entity who should be primarily responsible for performing user entitlement reviews is the data owner. A user entitlement review is a process that verifies and validates the access rights and privileges of the users to the data and resources in the IT environment. A user entitlement review helps to ensure that the users have the appropriate and necessary access to perform their roles and functions, and to prevent or detect any unauthorized or inappropriate access. A data owner is the person or entity that has the authority and responsibility to define, classify, and protect the data and resources in the IT environment. A data owner helps to perform user entitlement reviews, because they help to establish and enforce the access policies and standards for the data and resources, and to approve or revoke the access requests and changes for the users. A data owner also helps to monitor and report on the access performance and compliance for the data and resources, and to identify and address any issues or gaps in the access management activities. The other options are not the primary responsible party for performing user entitlement reviews, although they may be involved in the process. IT security manager, IT personnel, and data custodian are all examples of roles or functions that can help tosupport or implement the user entitlement reviews, but they do not necessarily have the authority or responsibility to define, classify, or protect the data and resources. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.2.1, page 5-14.
The MAIN purpose of a risk register is to:
Options:
document the risk universe of the organization.
promote an understanding of risk across the organization.
enable well-informed risk management decisions.
identify stakeholders associated with risk scenarios.
Answer:
CExplanation:
The main purpose of a risk register is to enable well-informed risk management decisions by providing a comprehensive and up-to-date record of all the identified risks, their analysis, and their responses. A risk register is a tool that helps to document, monitor, and communicate the status and outcome of risk management activities. A risk register also facilitates the review and evaluation of the effectiveness of risk management processes and controls. Documenting the risk universe, promoting an understanding of risk,and identifying stakeholders are possible benefits of a risk register, but they are not the main purpose. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.1.3, page 531
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 640.
During a risk assessment, a risk practitioner learns that an IT risk factor is adequately mitigated by compensating controls in an associated business process. Which of the following would enable the MOST effective management of the residual risk?
Options:
Schedule periodic reviews of the compensating controls ' effectiveness.
Report the use of compensating controls to senior management.
Recommend additional IT controls to further reduce residual risk.
Request that ownership of the compensating controls is reassigned to IT
Answer:
AExplanation:
A compensating control is a control that is implemented to reduce the risk exposure when the primary control is not feasible or cost-effective. A compensating control may not directly address the root cause of the risk, but it can provide an alternative or supplementary way of mitigating the risk. A residual risk is the risk that remains after the risk response has been implemented. A residual risk can be accepted, monitored, or further reduced depending on the risk tolerance and appetite of the organization. During a risk assessment, a risk practitioner is a person who is responsible for identifying and analyzing the potential sources and consequences of risk events. When a risk practitioner learns that an IT risk factor is adequately mitigated by compensating controls in an associated business process, the action that would enable the most effective management of the residual risk is to schedule periodic reviews of the compensating controls’ effectiveness, which means to measure and evaluate the performance and compliance of the compensating controls on a regular basis. By scheduling periodic reviews of the compensating controls’ effectiveness, the risk practitioner can ensure that the compensating controls are stilloperating as intended, and that they are delivering the expected results. The risk practitioner can also identify any gaps or weaknesses in the compensating controls, and recommend any improvements or adjustments as needed. References = CRISC Review Manual, 7th Edition, page 177.
A MAJOR advantage of using key risk indicators (KRIs) is that they:
Options:
Identify scenarios that exceed defined risk appetite.
Help with internal control assessments concerning risk appetite.
Assess risk scenarios that exceed defined thresholds.
Identify when risk exceeds defined thresholds.
Answer:
DExplanation:
KRIs provide measurable indicators that flag when risks exceed predefined thresholds, enabling swift and effective risk response. This supports theMonitoring and Reportingfunction in risk management, ensuring risks are managed proactively.
Which of the following provides the MOST useful information when determining if a specific control should be implemented?
Options:
Business impact analysis (BIA)
Cost-benefit analysis
Attribute analysis
Root cause analysis
Answer:
BExplanation:
A cost-benefit analysis is a tool that compares the costs and benefits of different alternatives, such as implementing or not implementing a specific control. A cost-benefit analysis provides the most useful information when determining if a specific control should be implemented, as it can show the potential savings, benefits, and risks of each option, and help the decision-makers choose the best course of action. A cost-benefit analysis can also include qualitative factors, such as security, compliance, performance, and customer satisfaction, that may be affected by thecontrol implementation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 256. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 256. Most Asked CRISC Exam Questions and Answers, Question 10. CRISC by Isaca Actual Free Exam Q & As, Question 9.
Which of the following is the BEST risk management approach for the strategic IT planning process?
Options:
Key performance indicators (KPIs) are established to track IT strategic initiatives.
The IT strategic plan is reviewed by the chief information security officer (CISO) and enterprise risk management (ERM).
The IT strategic plan is developed from the organization-wide risk management plan.
Risk scenarios associated with IT strategic initiatives are identified and assessed.
Answer:
DExplanation:
Identifying and assessing the risk scenarios associated with IT strategic initiatives is the best risk management approach for the strategic IT planning process, because it helps to understand and evaluate the potential or actual threats or opportunities that may affect the achievement or implementation of the IT strategic initiatives, and to determine the appropriate risk responses and controls. A risk scenario is a hypothetical situation or event that describes the source, cause, consequence, and impact of a risk. A risk scenario can be positive or negative, depending on whether it represents an opportunity or a threat. An IT strategic initiative is a project or program that supports or enables the IT strategy, which is a plan that defines how IT supports and aligns with the organization’s vision, mission, and strategy. The strategic IT planning process is a process of developing, implementing, and monitoring the IT strategy and its associated IT strategic initiatives. Identifying and assessing the risk scenarios is the best risk management approach, as it helps to anticipate and prepare for the potential or actual outcomes of the IT strategic initiatives, and to optimize the risk-reward balance and the value delivery of IT. Establishing key performance indicators (KPIs) to track IT strategic initiatives, reviewing the IT strategic plan by the chief information security officer (CISO) and enterprise risk management (ERM), and developing the IT strategic plan from the organization-wide risk management plan are all possible risk management approaches for the strategic IT planning process, but they are not the best approach, as they do not directly address the identification and assessment of the risk scenarios associated with IT strategic initiatives. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.1.1, page 37
An organization plans to provide specific cloud security training for the IT team to help manage risks associated with cloud technology. This response is considered risk:
Options:
Transfer
Mitigation
Acceptance
Deferral
Answer:
BExplanation:
Risk mitigationinvolves implementing measures to reduce either the likelihood or impact of a risk.
By providingtargeted training, the organization increases staff capability, thereby reducing thelikelihoodof misconfigurations or compliance errors in cloud usage.
ISACA defines mitigation as:
“Implementing controls or training to reduce exposure to risk within acceptable levels.”
ATransfer = insurance or outsourcing.
CAcceptance = no action.
DDeferral = postponing response.
Hence,B. Mitigationis correct.
CRISC Reference:Domain 3 – Risk Response and Mitigation, Topic: Risk Response Options.
A data processing center operates in a jurisdiction where new regulations have significantly increased penalties for data breaches. Which of the following elements of the risk register is MOST important to update to reflect this change?
Options:
Risk impact
Risk trend
Risk appetite
Risk likelihood
Answer:
AExplanation:
Risk impact is the potential loss or damage that a risk event can cause to an organization. Risk impact can be expressed in qualitative or quantitative terms, such as financial, reputational, operational, or legal. A risk register is a tool that records and tracks the key information about the identified risks, such as their description, likelihood, impact, response, and status. A risk register helps an organization to monitor and manage its risks effectively and efficiently. When there is a change in the external or internal environment that affects the organization’s risks, such as new regulations, the risk register should be updated to reflect this change. The most important element of the risk register to update in this case is the risk impact, because the new regulations have significantly increased the penalties for data breaches, which means that the potential loss or damage that a data breach can cause to the organization has also increased. By updating the risk impact, the organization can reassess the severity and priority of the data breach risk, and adjust its risk response accordingly. The other elements of the risk register are less important toupdate in this case. The risk trend shows the direction and rate of change of the risk over time, which may or may not be affected by the new regulations. The risk appetite is the amount and type of risk that the organization is willing to accept in pursuit of its objectives, which is unlikely to change due to the new regulations. The risk likelihood is the probability of a risk event occurring, which is also independent of the new regulations. References = Risk IT Framework, ISACA, 2022, p. 131
An organization does not have a defined process to revoke IT access of staff members who have changed roles within the organization. Which of the following is the GREATEST concern associated with this deficiency?
Options:
Noncompliance with the access management policy
Fraudulent insider activities
Misaligned job duties
Inefficient access review processes
Answer:
BExplanation:
CRISC highlights that inadequate termination or role-change procedures for access rights expose the organization to serious insider threats. When users change roles but retain access not needed for their new responsibilities, the risk offraudulent insider activitiesand unauthorized use of systems significantly increases. Excessive privileges can be abused intentionally or misused accidentally, leading to data breaches, financial loss, or regulatory non-compliance. While noncompliance with policy is an issue, it is a secondary, formal concern—the primary risk is actual misuse of privileges. Misaligned job duties and inefficiencies in access review are consequences but not as severe as the potential for fraud, sabotage, or data theft. Therefore, the greatest concern is the exposure to insider risk due to inadequate de-provisioning and access recertification processes.
A risk practitioner has been asked to evaluate the adoption of a third-party blockchain integration platform based on the value added by the platform and the organization ' s risk appetite. Which of the following is the risk practitioner ' s BEST course of action?
Options:
Conduct a risk assessment with stakeholders.
Conduct third-party resilience tests.
Update the risk register with the process changes.
Review risk related to standards and regulations.
Answer:
AExplanation:
Conducting a risk assessment with stakeholders is the best course of action for the risk practitioner to evaluate the adoption of a third-party blockchain integration platform, because it helps to identify, analyze, and evaluate the risks and opportunities associated with the platform, and to compare them with the organization’s risk appetite and value proposition. A risk assessment is a process of systematically identifying and assessing the sources and types of risk that an organization faces, and estimating their likelihood and impact. A risk assessment also involves identifying and evaluating the existing or proposed controls or mitigating factors that can reduce or eliminate the risk. A stakeholder is a person or group that has an interest or influence in the organization or its activities, such as customers, employees, shareholders,suppliers, regulators, or partners. A blockchain integration platform is a software solution that enables the organization to connect and interact with blockchain networks or applications, such as cryptocurrencies, smart contracts, or distributed ledgers. A blockchain integration platform can offer benefits such as transparency, security, efficiency, and innovation, but it can also pose risks such as technical complexity, interoperability issues, regulatory uncertainty, or cyberattacks. Therefore, conducting a risk assessment with stakeholders is the best way to evaluate the adoption of a third-party blockchain integration platform, as it helps to understand the benefits and risks of the platform, and to align them with the organization’s objectives and risk appetite. Conducting third-party resilience tests, updating the risk register with the process changes, and reviewing risk related to standards and regulations are all important tasks to perform after conducting a risk assessment, but they are not the best course of action, as they depend on the results of the risk assessment. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.2, page 87
The BEST key performance indicator (KPI) to measure the effectiveness of a vendor risk management program is the percentage of:
Options:
vendors providing risk assessments on time.
vendor contracts reviewed in the past year.
vendor risk mitigation action items completed on time.
vendors that have reported control-related incidents.
Answer:
CExplanation:
According to the CRISC Review Manual1, vendor risk mitigation action items are the specific tasks and activities that are assigned to the vendors or the organization to address the identified risks and implementthe risk responses. The percentage of vendor risk mitigation action items completed on time is the best key performance indicator (KPI) to measure the effectiveness of a vendor risk management program, as it helps to evaluate the timeliness and quality of the vendor performance, the alignment of the vendor activities with the organization’s risk appetite and objectives, and the achievement of the expected outcomes and benefits of the risk responses. The percentage of vendor risk mitigation action items completed on time also helps to identify andresolve any issues or gaps in the vendor risk management process, and to improve the vendor relationship and communication. References = CRISC Review Manual1, page 230.
An organization has implemented a preventive control to lock user accounts after three unsuccessful login attempts. This practice has been proven to be unproductive, and a change in the control threshold value has been recommended. Who should authorize changing this threshold?
Options:
Risk owner
IT security manager
IT system owner
Control owner
Answer:
DExplanation:
According to the CRISC Review Manual, a control owner is the person who is accountable for ensuring that specific control activities are performed. The control owner is responsible for defining, implementing, monitoring, and improving the control. Therefore, the control ownershould authorize changing the control threshold value, as it is part of their role to ensure that the control is effective and efficient. The other options are not the correct answers, because they are not directly involved in the control activities. The risk owner is the person who is accountable for the risk and its associated mitigation actions. The IT security manager is the person who is responsible for overseeing the IT security function and ensuring that the IT security policy is enforced. The IT system owner is the person who is responsible for the operation andmaintenance of the IT system and its associated data. References = CRISC Review Manual, 7th Edition, Chapter 3, Section 3.1.2, page 108.
Which of the following management actions will MOST likely change the likelihood rating of a risk scenario related to remote network access?
Options:
Creating metrics to track remote connections
Updating the organizational policy for remote access
Updating remote desktop software
Implementing multi-factor authentication
Answer:
DExplanation:
Automated asset management software is the best method to track asset inventory, as it can provide accurate, timely, and comprehensive information about the organization’s IT assets, such as their location, status, configuration, ownership, and value. Automated asset management software can also help to optimize the utilization, performance, and lifecycle of the IT assets, and to reduce the risks of loss, theft, damage, or obsolescence. Automated asset management software can integrate with other systems, such as configuration management database (CMDB), service desk, and security tools, to enable better visibility, control, and governance of the IT assets.
Which of the following should an organization perform to forecast the effects of a disaster?
Options:
Develop a business impact analysis (BIA).
Define recovery time objectives (RTO).
Analyze capability maturity model gaps.
Simulate a disaster recovery.
Answer:
AExplanation:
A business impact analysis (BIA) is a process that identifies and evaluates the potential effects of a disaster on the critical functions and processes of an organization1. A BIA helps to forecast the operational, financial, legal, and reputational impacts of a disaster, as well as the recovery priorities and resources needed to resume normal operations2. A BIA also helps to determine the recovery time objectives (RTO), which are the maximum acceptable time frames for restoring the critical functions and processes after a disaster3. Therefore, developing a BIA is the most important step for an organization to forecast the effects of a disaster and plan for its recovery. Defining RTOs is a part of the BIA process, not a separate activity. Analyzing capability maturity model gaps is a method to assess the effectiveness and efficiency of the organization’s processes and practices, but it does not directly forecast the effects of adisaster4. Simulating a disaster recovery is a way to test and validate the recovery plans and procedures, but it does not forecast the effects of a disaster either5. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk Response and Mitigation, Section 5.3: Business Continuity Planning, pp. 227-238.
An organization has initiated a project to launch an IT-based service to customers and take advantage of being the first to market. Which of the following should be of GREATEST concern to senior management?
Options:
More time has been allotted for testing.
The project is likely to deliver the product late.
A new project manager is handling the project.
The cost of the project will exceed the allotted budget.
Answer:
BExplanation:
Being the first to market is a competitive advantage that can help an organization gain market share, customer loyalty, and brand recognition. However, this advantage can be lost if the projectis delayed and the competitors catch up or surpass the organization. Therefore, the project delivery time is of greatest concern to senior management, as it directly affects the strategic objective of the project. The other options are less critical, as they can be managed or mitigated by the project team. More time for testing can improve the quality and reliability of the product, a new project manager can bring fresh ideas and perspectives, and the cost overrun can be justified by the expected benefits and revenues of the product. References = Project Initiation: The First Step to Project Management [2023] • Asana, 12 Steps to Initiate and Plan a Successful Project
Which of the following would be the GREATEST concern for an IT risk practitioner when an employees.....
Options:
The organization ' s structure has not been updated
Unnecessary access permissions have not been removed.
Company equipment has not been retained by IT
Job knowledge was not transferred to employees m the former department
Answer:
BExplanation:
The greatest concern for an IT risk practitioner when an employee transfers to another department is that unnecessary access permissions have not been removed. Unnecessary access permissions are the access rights or privileges that are no longer needed, relevant, or appropriate for the employee’s new role or responsibility. If these access permissions are not removed, they may pose a significant security risk, as the employee may be able to access, modify, or delete sensitive or critical data and systems that are not related to their current function. This may result in data leakage, fraud, sabotage, or compliance violations. The other options are not as concerning as unnecessary access permissions, as they are related to the organizational, operational, or knowledge aspects of the employee transfer, not the security or risk aspects of the employee transfer. References = Risk and Information Systems Control Study Manual, Chapter 3: IT Risk Response, Section 3.3: IT Risk Response Implementation, page 145.
A risk practitioner notices that a particular key risk indicator (KRI) has remained below its established trigger point for an extended period of time. Which of the following should be done FIRST?
Options:
Recommend a re-evaluation of the current threshold of the KRI.
Notify management that KRIs are being effectively managed.
Update the risk rating associated with the KRI In the risk register.
Update the risk tolerance and risk appetite to better align to the KRI.
Answer:
AExplanation:
The FIRST thing that should be done when a KRI has remained below its established trigger point for an extended period of time is to recommend a re-evaluation of the current threshold of the KRI, because it may indicate that the trigger point is set too high or too low, or that the KRI is not relevant or effective in measuring the risk exposure. A re-evaluation of the current threshold of the KRI may result in adjusting the trigger point, changing the KRI, or removing the KRI. The other options are not the first thing that should be done, because:
Option B: Notifying management that KRIs are being effectively managed is not the first thing that should be done, because it may not reflect the true risk status and performance. A KRI that remains below its trigger point for a long time may not be a valid or reliable indicator of the risk exposure, and it may not capture the changes or trends in the risk environment.
Option C: Updating the risk rating associated with the KRI in the risk register is not the first thing that should be done, because it may not be accurate or consistent. A risk rating is based on the likelihood and impact of the risk, and it should be derived from a comprehensive risk analysis, not just from a single KRI. A KRI that remains below its trigger point for a long time may not reflect the actual likelihood and impact of the risk, and it may not be aligned with the other risk indicators and assessments.
Option D: Updating the risk tolerance and risk appetite to better align to the KRI is not the first thing that should be done, because it may not be appropriate or feasible. Risk tolerance and risk appetite are the acceptable level of risk exposure and variation that the enterprise is willing to accept in pursuit of its objectives, and they are determined by the executive management and the board of directors, based on the enterprise’s strategy and goals. A KRI that remains below its trigger point for a long time may not represent the desired or optimal level of risk exposure and variation, and it may not be aligned with the enterprise’s strategy and goals. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 121.
For no apparent reason, the time required to complete daily processing for a legacy application is approaching a risk threshold. Which of the following activities should be performed FIRST?
Options:
Temporarily increase the risk threshold.
Suspend processing to investigate the problem.
Initiate a feasibility study for a new application.
Conduct a root-cause analysis.
Answer:
DExplanation:
The first activity that should be performed when the time required to complete daily processing for a legacy application is approaching a risk threshold is to conduct a root-cause analysis. This will help to identify the source of the problem and the factors that are contributing to the increased processing time. By conducting a root-cause analysis, the enterprise can determine the most appropriate and effective solution to address the problem and prevent it from recurring. Temporarily increasing the risk threshold, suspending processing to investigate the problem, and initiating a feasibility study for a new application are not the first activities that should be performed, as they may not resolve the underlying issue and may introduce additional risks or costs. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.2.1.2, page 193.
Which of the following BEST facilitates the development of effective IT risk scenarios?
Options:
Utilization of a cross-functional team
Participation by IT subject matter experts
Integration of contingency planning
Validation by senior management
Answer:
AExplanation:
The best way to facilitate the development of effective IT risk scenarios is to utilize a cross-functional team. A cross-functional team is a group of people with different skills, expertise, and perspectives who work together to achieve a common goal. A cross-functional team can help to create realistic, comprehensive, and relevant IT risk scenarios by bringing diverse knowledge, experience, and insights from various domains and functions. A cross-functional team can alsohelp to identify and address the interdependencies, interactions, and impacts of IT risks across the organization. The other options are not the best ways to facilitate the development of effective IT risk scenarios, although they may be useful or necessary depending on the context and nature of the IT risks. Participation by IT subject matter experts is important, but it is notsufficient, as IT risks may affect or be affected by non-IT factors and stakeholders. Integration of contingency planning is a part of the risk response process, which follows the risk scenario development process, but it is not the same as creating the risk scenarios. Validation by senior management is a quality assurance step that ensures the accuracy and completeness of the risk scenarios, but it is not the same as facilitating the development of the risk scenarios. References = Six Steps to Using Risk Scenarios for Improved Risk Management, IT Risk Scenarios - Morland-Austin, IT Risk Resources | ISACA
Which of the following is MOST important to consider when selecting key risk indicators (KRIs)? The ability to:
Options:
Measure changes in the threat landscape.
Refine the organization’s risk appetite.
Monitor the performance of a process.
Assess the risk associated with risk scenarios.
Answer:
DExplanation:
The BEST answer is D because a KRI must be linked to a specific risk or risk scenario and should provide an early warning of increased risk exposure. ISACA’s CRISC exam outline includes defining, implementing, refining, monitoring, and analyzing KRIs, KPIs, and KCIs as supporting CRISC tasks. ISACA’s risk indicator explanation distinguishes indicators clearly: a KRI gives an early signal of increased exposure to risk, while a KPI measures performance over time for a specific objective. The uploaded CRISC notes directly support this: the most important consideration when implementing KRIs is linking the metric to a specific risk, and the most important attribute of an effective KRI is that it is linked to a specific risk.
A is too narrow because KRIs may measure many types of risk exposure, not only threat landscape changes. B is incorrect because risk appetite is normally set by governance/senior leadership; KRIs monitor exposure against appetite/tolerance, not refine appetite themselves. C describes a KPI more than a KRI, because process performance monitoring is performance-focused rather than risk-exposure-focused.
Which of The following should be of GREATEST concern for an organization considering the adoption of a bring your own device (BYOD) initiative?
Options:
Device corruption
Data loss
Malicious users
User support
Answer:
BExplanation:
A bring your own device (BYOD) initiative allows employees to use their personal devices, such as smartphones, tablets, or laptops, for work purposes. This can provide benefits such as increased productivity, flexibility, and employee satisfaction. However, it also introducessignificant risks, such as data loss, data leakage, malware infection, unauthorized access, and compliance violations. Among these risks, data loss is of greatest concern for an organization, as it can have severe consequences, such as reputational damage, legal liability, financial loss, and competitive disadvantage. Data loss can occur due to various reasons, such as device theft, loss, damage, or disposal, accidental deletion, unauthorized transfer, or malicious attack. Therefore, an organization considering the adoption of a BYOD initiative should implement appropriate controls, such as encryption, authentication, remote wipe, backup, and data classification, to protect the data stored or accessed on the personal devices. References = Bring Your Own Device (BYOD) Policy: What You Need to Know, BYOD Risks: What You Need to Know, BYOD Security: 8 Risks and How to Mitigate Them
A risk practitioner observed Vial a high number of pokey exceptions were approved by senior management. Which of the following is the risk practitioner’s BEST course of action to determine root cause?
Options:
Review the risk profile
Review pokey change history
interview the control owner
Perform control testing
Answer:
CExplanation:
The best course of action to determine the root cause of the high number of policy exceptions approved by senior management is to interview the control owner. The control owner is the person who has the authority and responsibility for designing, implementing, and monitoring the controls that enforce the policy. The control owner can provide insight into the reasons, circumstances, and impacts of the policy exceptions, and the effectiveness and efficiency of the controls. The control owner can also suggest possible improvements or alternatives to the policy or the controls. The other options are not as useful as interviewing the control owner, as they are related to the review, analysis, or testing of the policy or the controls, not the investigation or understanding of the policy exceptions. References = Risk and Information Systems Control Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.4: Key Control Indicators, page 211.
Which of the following should be the PRIMARY focus of a disaster recovery management (DRM) framework and related processes?
Options:
Restoring IT and cybersecurity operations
Assessing the impact and probability of disaster scenarios
Ensuring timely recovery of critical business operations
Determining capacity for alternate sites
Answer:
CExplanation:
Ensuring Timely Recovery of Critical Business Operations:
Primary Focus: The primary focus of a Disaster Recovery Management (DRM) framework is to ensure that critical business operations can be recovered and resumed in a timely manner after a disruption.
Business Continuity: Timely recovery of operations is essential for maintaining business continuity and minimizing the impact of disruptions on the organization’s ability to deliver products and services.
Recovery Objectives: Establishing clear recovery time objectives (RTOs) and recovery point objectives (RPOs) ensures that critical operations are prioritized and recovery efforts are aligned with business needs.
Comparison with Other Options:
Restoring IT and Cybersecurity Operations: While important, this is part of the broader goal of recovering critical business operations.
Assessing Impact and Probability of Disaster Scenarios: This is a preparatory step that informs the DRM framework but is not the primary focus.
Determining Capacity for Alternate Sites: This is a component of the DRM strategy but supports the primary focus of ensuring timely recovery.
Best Practices:
Comprehensive Planning: Develop comprehensive disaster recovery plans that prioritize the recovery of critical business operations.
Regular Testing: Regularly test and update disaster recovery plans to ensure they remain effective and aligned with business objectives.
Cross-Functional Collaboration: Involve all relevant business units in disaster recovery planning to ensure a coordinated and effective response.
Which of the following provides the MOST useful information to determine risk exposure following control implementations?
Options:
Strategic plan and risk management integration
Risk escalation and process for communication
Risk limits, thresholds, and indicators
Policies, standards, and procedures
Answer:
CExplanation:
Risk limits, thresholds, and indicators provide the most useful information to determine risk exposure following control implementations, as they help to measure and monitor the current and residual risk levels and compare them with the desired and acceptable risk levels. Risk limits, thresholds, and indicators are defined as follows:
Risk limits are the maximum amount of risk that an organization is willing to accept for a given activity, process, or objective. Risk limits are derived from the organizational risk appetite and tolerance, and they help to guide the risk response and control selection.
Risk thresholds are the points or levels at which the risk or performance is acceptable or unacceptable. Risk thresholds are used to trigger alerts, actions, or escalation when the risk or performance deviates from the expected or planned range.
Risk indicators are metrics or measures that provide information on the current or potential risk exposure or performance. Risk indicators can be classified into key risk indicators (KRIs), whichmeasure the likelihood and impact of risk events, and key performance indicators (KPIs), which measure the effectiveness and efficiency of controls and processes.
Risk limits, thresholds, and indicators help to determine risk exposure following control implementations by providing quantitative and qualitative data and feedback on the risk and control environment. They also help to identify and prioritize the areas for improvement and enhancement of the risk and control environment. Risk limits, thresholds, and indicators also facilitate the communication, collaboration, and accountability among the stakeholders involved in the risk management and control processes.
The other options are not the most useful information to determine risk exposure following control implementations. Strategic plan and risk management integration is the process of aligning the organizational strategy and objectives with the risk management framework and activities, but it does not provide specific information on the risk exposure or control effectiveness. Risk escalation and process for communication is the process of reporting and escalating the risk issues and incidents to the appropriate authority and stakeholders, but it doesnot provide comprehensive information on the risk exposure or control performance. Policies, standards, and procedures are the documents that define the principles, rules, and guidelines for the risk management and control processes, but they do not provide actual information on the risk exposure or control implementation. References = Risk Limits, Thresholds and Indicators - ISACA, IT Risk Resources | ISACA, Risk Management: Risk Indicators and Risk Appetite
Which of the following is the GREATEST benefit of involving business owners in risk scenario development?
Options:
Business owners have the ability to effectively manage risk.
Business owners have authority to approve control implementation.
Business owners understand the residual risk of competitors.
Business owners are able to assess the impact.
Answer:
DWhich of the following is the BEST way to incorporate continuous monitoring in IT risk policies?
Options:
Implement a governance, risk, and compliance (GRC) tool
Establish a cross-functional risk steering committee to oversee risk initiatives.
Define how risk thresholds are aligned with organizational objectives.
Standardize IT risk mitigation for better monitoring of IT risk.
Answer:
CExplanation:
The correct answer is C because the best way to incorporatecontinuous monitoringin IT risk policies is todefine how risk thresholds are aligned with organizational objectives. Continuous monitoring is effective only when it is tied to measurable thresholds that indicate when risk is moving outside acceptable limits. Those thresholds must be aligned with business objectives, risk appetite, and tolerance to make monitoring meaningful.
The other options are less appropriate as the best policy-level approach:
A. Implement a governance, risk, and compliance (GRC) toolmay support monitoring, but a tool is not the policy foundation.
B. Establish a cross-functional risk steering committeeimproves governance, but it does not define how continuous monitoring should operate.
D. Standardize IT risk mitigationhelps consistency, but continuous monitoring depends on thresholds and escalation criteria.
Exact Extracts supporting the answer:
“The main purpose of continuous monitoring is detecting changes to the enterprise’s risk environment.”
“The main purpose of risk monitoring is to provide timely information on the actual status of the enterprise with regard to risk with the risk profile offering an overall risk status.”
“Including thresholds that identify when controls no longer provide the intended value is essential when developing metrics to monitor the control life cycle.”
“The most important consideration when implementing key risk indicators is linking the metric to a specific risk.”
“The best approach for creating key risk indicators for quarterly reporting to senior leadership is identifying the enterprise risk appetite and metrics and measures of current risk.”
These extracts show that continuous monitoring must be based on defined thresholds linked to enterprise objectives and risk levels. Therefore, the best answer isdefine how risk thresholds are aligned with organizational objectives.
===========
Which of the following would BEST help an enterprise prioritize risk scenarios?
Options:
Industry best practices
Placement on the risk map
Degree of variances in the risk
Cost of risk mitigation
Answer:
BExplanation:
A risk map, also known as a risk heat map, is a visual tool that helps an enterprise prioritize risk scenarios by plotting them on a matrix based on their likelihood and impact. A risk map can help to compare and contrast different risk scenarios, as well as to identify the most critical and urgent risks that require attention. A risk map can also help to communicate and report the risk profile and status to the stakeholders and decision makers. Therefore, the placement on the risk map would best help an enterprise prioritize risk scenarios. The other options are not the best ways to help an enterprise prioritize risk scenarios, although they may be relevant and useful. Industry best practices are the standards or guidelines that are widely accepted and followed by the organizations in a specific industry or domain. Industry best practices can help to benchmark and improve the risk management process and performance, but they may not reflect the specific risk context and needs of the enterprise. Degree of variances in the risk is the measure of the variability or uncertainty of the risk, which may affect the accuracy or reliability of the risk assessment and response. Degree of variances in the risk can help to adjust and refine the risk analysis and treatment, but it may not indicate the priority or importance of the risk. Cost of risk mitigation is the amount of resources or expenses that are required or allocated to implement the risk response actions, such as avoiding, transferring, mitigating, or accepting the risk. Cost of risk mitigation can help to evaluate and optimize therisk response options, but it may not determine the priority or urgency of the risk. References = CRISC Review Manual, pages 38-391; CRISC Review Questions, Answers & Explanations Manual, page 892
An organization is moving its critical assets to the cloud. Which of the following is the MOST important key performance indicator (KPI) to include in the service level agreement (SLA)?
Options:
Percentage of standard supplier uptime
Average time to respond to incidents
Number of assets included in recovery processes
Number of key applications hosted
Answer:
AExplanation:
When moving critical assets to the cloud, the most important KPI to include in the SLA is the percentage of standard supplier uptime, which measures the availability and reliability of the cloud service provider. This KPI indicates how often the cloud service is operational and accessible, and how well it meets the agreed service level objectives. A high percentage of standard supplier uptime means that the cloud service provider can deliver the expected performance and functionality of the critical assets, and minimize the risk of service disruptions, downtime, or data loss. The percentage of standard supplier uptime should be aligned with the organization’s business continuity and disaster recovery requirements, and should be monitored and reported regularly by the cloud service provider. The SLA should also specify the compensation or remediation actions in case of any breach of the agreed percentage of standard supplier uptime.
Who is accountable for risk treatment?
Options:
Enterprise risk management team
Risk mitigation manager
Business process owner
Risk owner
Answer:
DExplanation:
Risk treatment is the process of selecting and implementing the appropriate risk response strategy and actions to address the identified risks. Risk treatment can involve different strategies, such as avoiding, reducing, transferring, or accepting the risk. Risk owner is the person or group who has the authority and accountability to manage the risk and its response. Risk owner is accountable for risk treatment, as they are responsible for deciding, approving, and executing the risk treatment plan, and for monitoring and reportingthe results and outcomes of the risk treatment. The other options are not accountable for risk treatment, as they have different roles or responsibilities in the risk management process:
Enterprise risk management team is the group of risk managers and practitioners who support the enterprise-wide risk management program, and provide guidance and direction to the risk owners and stakeholders. Enterprise risk management team may advise or assist the risk owner in risk treatment, but they are not accountable for risk treatment.
Risk mitigation manager is the person who designs, implements, and monitors the risk mitigation actions or measures that reduce the likelihood or impact of the risk to an acceptable level, such as controls, policies, or procedures. Risk mitigation manager may advise or assist the risk owner in risk treatment, but they are not accountable for risk treatment.
Business process owner is the stakeholder who is responsible for the business process that is supported by the IT system or application, such as the CRM system. Business process owner may be affected by or contribute to the risk, and may be involved in the risk treatment, but they are not accountable for risk treatment, unless they are also the risk owner. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.1.1.1, pp. 95-96.
An IT department has provided a shared drive for personnel to store information to which all employees have access. Which of the following parties is accountable for the risk of potential loss of confidential information?
Options:
Risk manager
Data owner
End user
IT department
Answer:
BExplanation:
The data owner is the person who has the authority and responsibility to classify, label, and protect the information assets of the organization. The data owner is accountable for the risk ofpotential loss of confidential information, as they are the ones who determine the level of protection and access required for the data. The risk manager is responsible for identifying, assessing, and mitigating the risks that may affect the organization, but they are not accountable for the data itself. The end user is the person who uses the information assets for their operational tasks, but they are not accountable for the data protection or classification. The IT department is responsible for providing the technical support and infrastructure for the information assets, but they are not accountable for the data ownership or risk management. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: Data Classification, p. 69-70.
Which of the following should be done FIRST when information is no longer required to support business objectives?
Options:
Archive the information to a backup database.
Protect the information according to the classification policy.
Assess the information against the retention policy.
Securely and permanently erase the information
Answer:
CExplanation:
A retention policy is a set of rules and guidelines that define how long and under what conditions the information should be kept or disposed of by the organization, based on its value, sensitivity, and legal or regulatory requirements.
When information is no longer required to support business objectives, the first thing that should be done is to assess the information against the retention policy. This means that the information should be reviewed and evaluated to determine if it should be retained or deleted, and for how long and by whom.
Assessing the information against the retention policy helps to ensure that the information is managed and disposed of in a consistent and compliant manner, that the information is protected from unauthorized access, use, disclosure, modification, or destruction, and that the information is available for future reference or audit purposes if needed.
The other options are not the first things that should be done when information is no longer required to support business objectives. They are either secondary or not essential for information management.
The references for this answer are:
Risk IT Framework, page 28
Information Technology & Security, page 22
Risk Scenarios Starter Pack, page 20
A recent vulnerability assessment of a web-facing application revealed several weaknesses. Which of the following should be done NEXT to determine the risk exposure?
Options:
Code review
Penetration test
Gap assessment
Business impact analysis (BIA)
Answer:
BExplanation:
The next step to determine the risk exposure after a vulnerability assessment of a web-facing application is to perform a penetration test. A penetration test is a simulated attack on the application to exploit the identified vulnerabilities and measure the potential impact and likelihood of a successful breach. A penetration test can help to quantify and prioritize the risks associated with the web-facing application. Code review, gap assessment, and business impact analysis (BIA) are other possible steps, but they are not as effective as a penetration test. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 7; CRISC Review Manual, 6th Edition, page 202.
Recent penetration testing of an organization ' s software has identified many different types of security risks. Which of the following is the MOST likely root cause for the identified risk?
Options:
SIEM software is producing faulty alerts.
Threat modeling was not utilized in the software design process.
The configuration management process is not applied consistently during development.
An identity and access management (IAM) tool has not been properly integrated into the software.
Answer:
BExplanation:
Failure to utilize threat modeling during the design phase results in overlooked vulnerabilities. This highlights the importance ofProactive Threat Identificationin secure software development practices.
An organization is implementing encryption for data at rest to reduce the risk associated with unauthorized access. Which of the following MUST be considered to assess the residual risk?
Options:
Data retention requirements
Data destruction requirements
Cloud storage architecture
Key management
Answer:
DExplanation:
The most important factor to consider when assessing the residual risk of implementing encryption for data at rest is the key management. Key management is the process of generating, storing, distributing, using, and destroying the cryptographic keys that are used to encrypt anddecrypt the data. Key management is essential for ensuring the security, availability, and integrity of the encrypted data, as well as for complying with the legal and regulatory requirements. Poor key management could result in the loss, theft, compromise, or corruption of the keys, which could lead to unauthorized access, data breach, data loss, or data recovery failure. Therefore, key management must be considered to assess the residual risk, which is the risk that remains after the risk treatment, such as encryption, is applied. Data retention requirements, data destruction requirements, and cloud storage architecture are not as important as key management, as they do not directly affect the encryption and decryption of the data, and they may not introduce significant residual risk. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 217.
An organization has adopted an emerging technology without following proper processes. Which of the following is the risk practitioner ' s BEST course of action to address this risk?
Options:
Accept the risk because the technology has already been adopted.
Propose a transfer of risk to a third party with subsequent monitoring.
Conduct a risk assessment to determine risk exposure.
Recommend to senior management to decommission the technology.
Answer:
CExplanation:
Conducting a risk assessment allows the organization to evaluate the exposure created by adopting the technology. This step ensures informed decision-making and aligns with the principles ofRisk Identification and Assessmentfor managing emerging risks effectively.
Which of the following is the MOST important outcome of reviewing the risk management process?
Options:
Assuring the risk profile supports the IT objectives
Improving the competencies of employees who performed the review
Determining what changes should be made to IS policies to reduce risk
Determining that procedures used in risk assessment are appropriate
Answer:
AExplanation:
The most important outcome of reviewing the risk management process is assuring that the risk profile supports the IT objectives, because this ensures that the organization is managing its IT-related risks in alignment with its business goals and priorities. The risk profile is a summary of the key risks that the organization faces, their likelihood, impact, and response strategies. The IT objectives are the specific and measurable outcomes that the organization expects to achieve from its IT investments and activities. Byreviewing the risk management process, the organization can evaluate whether the risk profile is accurate, complete, and up-to-date, and whether the risk responses are effective, efficient, and consistent with the IT objectives. The review can also identify any gaps, issues, or opportunities for improvement in the risk management process, and provide recommendations for enhancing the process and its outcomes. The review can also help to communicate and report the value and performance of the risk management process to the senior management, the board of directors, and other stakeholders. References = Risk IT Framework, ISACA, 2022, p. 17
What is the MOST important consideration when aligning IT risk management with the enterprise risk management (ERM) framework?
Options:
Risk and control ownership
Senior management participation
Business unit support
Risk nomenclature and taxonomy
Answer:
DExplanation:
According to the CRISC Review Manual1, risk nomenclature and taxonomy is the set of terms and definitions that are used to describe and classify risks and their attributes. Risk nomenclature and taxonomy is the most important consideration when aligning IT risk management with the enterprise risk management (ERM) framework, as it helps to ensure a common and consistent understanding and communication of risks across the organization. Risk nomenclature and taxonomy also helps to integrate and harmonize the IT risk management processes and activities with the ERM framework, and to facilitatethe aggregation and reporting of risks at different levels of the organization. References = CRISC Review Manual1, page 197.
The PRIMARY focus of an ongoing risk awareness program should be to:
Options:
enable better risk-based decisions.
define appropriate controls to mitigate risk.
determine impact of risk scenarios.
expand understanding of risk indicators.
Answer:
AExplanation:
The primary focus of an ongoing risk awareness program should be to enable better risk-based decisions, as this can help the organization to achieve its objectives, optimize its performance, and manage its risks effectively. An ongoing risk awareness program is a process of educating, communicating, and engaging the stakeholders about the organization’s risk management framework, methodology, and practices. An ongoing risk awareness program can help the stakeholders to understand the risk context, criteria, appetite, and profile of the organization, and to identify, assess, treat, monitor, and review the risks that may affect their roles and responsibilities. By doing so, an ongoing risk awareness program can empower the stakeholders to make informed and rational decisions that balance the benefits and costs of risk-taking, and that align with the organization’s strategy and goals.
The BEST way to validate that a risk treatment plan has been implemented effectively is by reviewing:
Options:
results of a business impact analysis (BIA).
the original risk response plan.
training program and user awareness documentation.
a post-implementation risk and control self-assessment (RCSA).
Answer:
DExplanation:
A post-implementation RCSA is a process of verifying whether the risk treatment plan has been executed as intended and whether the residual risk is within the acceptable level. It involves testing the effectiveness of the controls that have been implemented to mitigate the risk and identifying any gaps or issues that need to be addressed. A BIA, the original risk response plan, and the training program and user awareness documentationare not sufficient to validate theeffectiveness of the risk treatment plan, as they do not measure the actual performance of the controls or the residual risk.
Which of the following is MOST likely to result in a major change to the overall risk profile of the organization?
Options:
Changes in internal and external risk factors
Changes in internal and external auditors
Changes in risk appetite and risk tolerance
Changes in vulnerability assessment and penetration testing
Answer:
AExplanation:
An organization’s risk profile is primarily shaped byits internal and external environment, including economic, regulatory, operational, and technological conditions. CRISC emphasizes that major shifts—such as new regulations, emerging threats, disruptive technologies, organizational restructuring, or market instability—can significantly alter likelihood and impact across multiple risk scenarios. Changes in auditors do not materially affect the risk profile; they affect assurance perspectives. Adjusting risk appetite influences decision-making but does not alter inherent risk. Changes in assessment tools refine detection capabilities but do not fundamentally change the risks themselves. Therefore, broad environmental changes represent the most impactful drivers of changes to the overall risk profile.
An organization has implemented a cloud-based backup solution to help prevent loss of transactional data from offices in an earthquake zone. This strategy demonstrates risk:
Options:
Avoidance
Mitigation
Transfer
Acceptance
Answer:
BExplanation:
Using cloud-based backup tominimize the impactof a potential data loss event is a classic example ofrisk mitigation, which involves reducing risk to an acceptable level through proactive controls.
Which of the following is the PRIMARY benefit when senior management periodically reviews and updates risk appetite and tolerance levels?
Options:
It ensures compliance with the risk management framework.
It ensures an effective risk aggregation process.
It ensures decisions are risk-informed.
It ensures a consistent approach for risk assessments.
Answer:
CExplanation:
Risk appetite and tolerance reflect strategic priorities. As business and external environments evolve, regular updates ensure that risk responses and decisions remain aligned with organizational goals and acceptable boundaries.
During testing, a risk practitioner finds the IT department ' s recovery time objective (RTO) for a key system does not align with the enterprise ' s business continuity plan (BCP). Which of the following should be done NEXT?
Options:
Report the gap to senior management
Consult with the IT department to update the RTO
Complete a risk exception form.
Consult with the business owner to update the BCP
Answer:
BExplanation:
According to the CRISC Review Manual (Digital Version), the next course of action when a risk practitioner finds the IT department’s recovery time objective (RTO) for a key system does not align with the enterprise’s business continuity plan (BCP) is to consult with the IT department to update the RTO. The RTO is the maximum acceptable time that an application, computer, network, or system can be down after an unexpected disaster, failure, or comparable event takes place. The RTO should be aligned with the BCP, which is a set of policies, procedures, and resources that enable the organization to continue or resume its critical business functions in the event of a disruption. Consulting with the IT department to update the RTO helps to:
Ensure that the RTO reflects the current business requirements and expectations for the availability and recovery of the key system
Evaluate the feasibility and cost-effectiveness of achieving the RTO with the existing IT resources and capabilities
Identify and implement the necessary changes or improvements in the IT infrastructure, processes, and controls to meet the RTO
Test and validate the RTO and the IT recovery procedures and verify their compatibility and consistency with the BCP
Communicate and coordinate the RTO and the IT recovery plan with the relevant stakeholders, such as the business owner, the risk owner, and the senior management
References = CRISC Review Manual (Digital Version), Chapter 3: IT Risk Response, Section 3.3: Risk Response Options, pp. 174-1751
The head of a business operations department asks to review the entire IT risk register. Which of the following would be the risk manager s BEST approach to this request before sharing the register?
Options:
Escalate to senior management
Require a nondisclosure agreement.
Sanitize portions of the register
Determine the purpose of the request
Answer:
DExplanation:
An IT risk register is a document that records and tracks the IT-related risks that an organization faces, as well as the information and actions related to those risks, such as the risk description, assessment, response, status, and owner. An IT risk register is a valuable tool for managing andcommunicating IT risks and their impact on the organization’s objectives and operations. However, an IT risk register may also contain sensitive or confidential information that should not be disclosed or shared with unauthorized or irrelevant parties, as it may compromise the security, privacy, or reputation of the organization or its stakeholders. Therefore, the risk manager’s best approach to the request from the head of a business operations department to review the entire IT risk register is to determine the purpose of the request before sharing the register. This is a technique to understand and evaluate the reason and the need for the request, as well as the scope and the level of access that the requester requires or expects. By determining the purpose of therequest, the risk manager can ensure that the request is legitimate, appropriate, and relevant, and that the requester has a clear and valid interest or stake in the IT risk register. The risk manager can also ensure that the request is aligned with the organization’s policies, procedures, and standards for IT risk management and information sharing. The risk manager can also use the purpose of the request to decide what and how much information to share with the requester, and what conditions or restrictions to apply, such as confidentiality, accuracy, or timeliness. The other options are not the best approaches to the request from the head of a business operations department to review the entire IT risk register, as they may be premature, unnecessary, or ineffective. Escalating to senior management is a technique to involve or inform the higher-level authorities or decision makers about the request, which may be useful or required in some cases, but it may not be the first or the best step to take, as it may delay or complicate the process, or undermine the risk manager’s authority or responsibility. Requiring a nondisclosure agreement is a technique to protect the confidentiality and integrity of the information in the IT risk register by legally binding the requester to not disclose or misuse the information. However, a nondisclosure agreement may not be needed or appropriate in every case, and it may not prevent or address other issues or risks related to the information sharing, such as relevance, accuracy, or timeliness. Sanitizing portions of the register is a technique toremove or redact the sensitive or confidential information from the IT risk register before sharing it with the requester, which may be necessary or prudent in some cases, but it may not be sufficient or satisfactory, as it may affect the completeness, usefulness, or validity of the information, or raise questions or concerns from the requester.
Which of the following is the PRIMARY role of the second line when an IT risk management framework is adopted?
Options:
Overseeing the execution of framework requirements
Implementing the framework requirements
Advising industry standard framework organizations
Auditing the execution of framework requirements
Answer:
AWhich of the following is the MOST important driver of an effective enterprise risk management (ERM) program?
Options:
Risk policy
Risk committee
Risk culture
Risk management plan
Answer:
CExplanation:
Risk culture is the foundation upon which ERM is built. It dictates how employees perceive, communicate, and act on risk. A strong risk culture ensures consistency in risk behaviors, supports governance, and sustains long-term effectiveness of the ERM.
Which of the following is the BEST evidence that risk management is driving business decisions in an organization?
Options:
Compliance breaches are addressed in a timely manner.
Risk ownership is identified and assigned.
Risk treatment options receive adequate funding.
Residual risk is within risk tolerance.
Answer:
CExplanation:
Risk treatment options are the actions or plans that are implemented to modify or reduce the risk exposure of the organization. Risk treatment options receive adequate funding when the organization allocatessufficient resources and budget to support the risk response actions, and to ensure that the risk controls are effective and efficient. This is the best evidence that risk management is driving business decisions in the organization, as it shows that the organizationprioritizes and values the risk management process, and that it aligns its risk strategy and objectives with its business goals and value creation. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 245. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 245. CRISC Sample Questions 2024, Question 245.
When a high number of approved exceptions are observed during a review of a control procedure, an organization should FIRST initiate a review of the:
Options:
Relevant policies.
Threat landscape.
Awareness program.
Risk heat map.
Answer:
AExplanation:
A high number of exceptions often indicate misalignment betweenpoliciesand business needs. Reviewing policies helps determine if they are overly restrictive or need adjustments to reduce exceptions while maintaining security.
Which of the following should be the PRIMARY focus of a risk owner once a decision is made to mitigate a risk?
Options:
Updating the risk register to include the risk mitigation plan
Determining processes for monitoring the effectiveness of the controls
Ensuring that control design reduces risk to an acceptable level
Confirming to management the controls reduce the likelihood of the risk
Answer:
CExplanation:
The primary focus of a risk owner once a decision is made to mitigate a risk is to ensure that the control design reduces the risk to an acceptable level. This means that the risk owner shouldverify that the control objectives, specifications, and implementation are aligned with the risk mitigation plan, and that the control is effective in reducing the risk exposure to within the risk appetite and tolerance of the enterprise. The risk owner should also ensure that the control design is consistent with the enterprise’s policies, standards, and procedures, and that it complies with any relevant laws, regulations, or contractual obligations. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.2.4, page 185.
Which of the following BEST reduces the risk associated with the theft of a laptop containing sensitive information?
Options:
Cable lock
Data encryption
Periodic backup
Biometrics access control
Answer:
BExplanation:
The best way to reduce the risk associated with the theft of a laptop containing sensitive information is to use data encryption. Data encryption is a process that transforms the data into an unreadable or unintelligible format, using a secret key or algorithm, to protect the data from unauthorized access or disclosure. Data encryption helps to reduce the risk of data theft, because even if the laptop is stolen, the data on the laptop cannot be accessed or used by the thief without the proper key or algorithm. Data encryption also helps to comply with the relevant laws, regulations, standards, and contracts that may require the protection of sensitive data. The other options are not as effective as data encryption, although they may provide some protection for the laptop or the data. A cable lock, a periodic backup, and a biometrics access control are allexamples of physical or logical controls, which may help to prevent or deter the theft of the laptop, or to recover or restore the data on the laptop, but they do not necessarily protect the data from unauthorized access or disclosure if the laptop is stolen. References = 8
In order to determining a risk is under-controlled the risk practitioner will need to
Options:
understand the risk tolerance
monitor and evaluate IT performance
identify risk management best practices
determine the sufficiency of the IT risk budget
Answer:
AExplanation:
To determine if a risk is under-controlled, the risk practitioner will need to understand the risk tolerance. Risk tolerance is the acceptable or allowable level of variation or deviation from the expected or desired outcomes or objectives. Risk tolerance reflects the amount and type of risk that the organization is willing and able to take. A risk is under-controlled when the risk exposure exceeds the risk tolerance, meaning that the organization is taking on more risk than it can handle or afford. Therefore, the risk practitioner will need to understand the risk tolerance to compare it with the risk exposure and identify the gap or difference. The other options are not as relevant as understanding the risk tolerance, as they are related to the monitoring, identification, or determination of the risk or the IT performance, not the comparison or evaluation of therisk. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Response, page 87.
Which of the following is the GREATEST concern associated with the lack of proper control monitoring?
Options:
There is potential for an increase in audit findings
Key performance indicators (KPIs) may not be reliable
The potential for risk realization is increased
Control inefficiencies may go undetected
Answer:
CExplanation:
Without monitoring, ineffective or failing controls may go unnoticed, leading to ahigher likelihood of risk eventsmaterializing, potentially with severe impact. This outweighs audit or KPI concerns.
Which of the following is MOST important for a risk practitioner to consider when determining the control requirements for data privacy arising from emerging technologies?
Options:
internal audit recommendations
Laws and regulations
Policies and procedures
Standards and frameworks
Answer:
BExplanation:
The most important factor for a risk practitioner to consider when determining the control requirements for data privacy arising from emerging technologies is the laws and regulations that apply to the organization and the technologies. Laws and regulations are the legal and ethical obligations that the organization must comply with when collecting, processing, storing, and sharing personal data. Laws and regulations can vary depending on the jurisdiction, sector, and type of data involved, and they can impose different requirements and restrictions on the use of emerging technologies that may affect data privacy. For example, the General Data Protection Regulation (GDPR) in the European Union, the California Consumer Privacy Act (CCPA) in the United States, and the Personal Data Protection Act (PDPA) in Singapore are some of the laws and regulations that govern data privacy and protection in different regions and contexts123. A riskpractitioner should consider the laws and regulations when determining the control requirements for data privacy arising from emerging technologies, because they can help to ensure that the organization respects the rights and interests of the data subjects, avoids legal and reputational risks, and maintains trust and accountability. The other options are not the mostimportant factor, although they may be relevant or influential to the control requirements for data privacy arising from emerging technologies. Internal audit recommendations are the suggestions and feedback from the internal audit function, which evaluates and improves the effectiveness of the governance, risk management, and control systems of the organization, but they do not supersede or replace the laws and regulations. Policies and procedures are the rules and guidelines that define how the organization operates and conducts its activities, but they should be aligned and consistent with the laws and regulations. Standards and frameworks are the best practices and benchmarks that are adopted by the organization to guide and support its processes and performance, but they should be compatible and compliant with the laws and regulations. References = Emerging privacy-enhancing technologies: Current regulatory and policy approaches | en | OECD, Data and Cybersecurity: 2023 Regulatory Challenges - KPMG, Ethical Dilemmas and Privacy Issues in Emerging Technologies: A … - MDPI
Which of the following is the ULTIMATE goal of conducting a privacy impact analysis (PIA)?
Options:
To identify gaps in data protection controls
To develop a customer notification plan
To identify personally identifiable information (Pll)
To determine gaps in data identification processes
Answer:
AExplanation:
The ultimate goal of conducting a privacy impact analysis (PIA) is to identify gaps in data protection controls, as it involves assessing the privacy risks and impacts of collecting, using, storing, and disclosing personally identifiable information (PII), and determining the adequacy and effectiveness of the existing or proposed controls to mitigate those risks and impacts. Developing a customer notification plan, identifying PII, and determining gaps in data identification processes are possible steps or outcomes of conducting a PIA, but they are not the ultimate goal, as they do not address the root cause or solution of the privacy issues. References = CRISC Review Manual, 7th Edition, page 155.
When an organization’s disaster recovery plan (DRP) has a reciprocal agreement, which of the following risk treatment options is being applied?
Options:
Acceptance
Mitigation
Transfer
Avoidance
Answer:
CExplanation:
A reciprocal agreement is an agreement made by two or more organizations to use each other’s resources during a disaster1. For example, two organizations with similar IT infrastructure may agree to provide backup servers or data centers for each other in case of a major disruption. By doing so, they transfer the risk of losing their IT capabilities to the other party, who agrees to share the responsibility and cost of recovery.
A reciprocal agreement is a form of risk transfer, which is one of the four risk treatment options according to ISO 270012. Risk transfer means that the organization shifts the potential negative consequences of a risk to another party, such as an insurance company, a vendor, or a partner. This reduces the organization’s exposure and liability to the risk, but it does not eliminate the risk completely, as the other party may fail to fulfill their obligations or charge a high price for their services.
References = Reciprocal Agreement - Risky Thinking, ISO 27001 Risk Assessment & Risk Treatment: The Complete Guide - Advisera
An external data source has released an advisory about a critical vulnerability affecting a widely used software application. Which of the following should the risk practitioner do FIRST?
Options:
Advise application owners to patch affected software
Determine organizational exposure
Notify senior management of the critical vulnerability
Review the incident response plan
Answer:
BExplanation:
Upon receiving an external vulnerability alert, thefirst stepin the CRISC risk process is todetermine organizational exposure— i.e., whether and where the vulnerable software is actually used in the enterprise environment.
ISACA’s CRISC framework states:
“The initial step upon receiving notice of a new vulnerability is to assess the enterprise’s exposure to the threat to determine relevance and potential impact.”
Only after confirming exposure should the practitioner recommend patching, escalation, or other actions. Acting prematurely without confirmation could cause unnecessary disruptions.
Hence,B. Determine organizational exposureis correct.
CRISC Reference:Domain 2 – IT Risk Assessment, Topic: Vulnerability Management and Exposure Analysis.
A risk practitioner is organizing risk awareness training for senior management. Which of the following is the MOST important topic to cover in the training session?
Options:
The organization ' s strategic risk management projects
Senior management roles and responsibilities
The organizations risk appetite and tolerance
Senior management allocation of risk management resources
Answer:
CExplanation:
The organization’s risk appetite and tolerance are the most important topics to cover in a risk awareness training for senior management. Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk tolerance is the level of variation from the risk appetite that the organization is prepared to accept. Senior management plays a key role in defining and communicating the risk appetite and tolerance, as well asensuring that they are aligned with the organization’s strategy, culture, and values. By covering these topics in the training session, the risk practitioner can help senior management understand and articulate the risk preferences and boundaries of the organization, as well as monitor andadjust them as needed. The other options are not the most important topics to cover in a risk awareness training for senior management, although they may be relevant and useful. The organization’s strategic risk management projects are specific initiatives or activities that aim to identify, assess, and treat risks that may affect the organization’s objectives. Senior management roles and responsibilities are the duties and expectations that senior management has in relation to risk management, such as providing leadership, oversight, and support. Senior management allocation of risk management resources is the process of assigning and prioritizing the human, financial, and technical resources that are needed to implement and maintain risk management activities. These topics are more operational and tactical than strategic and may vary depending on the context and scope of the risk management function. References = CRISC Review Manual, pages 40-411; CRISC Review Questions, Answers & Explanations Manual, page 732
Which of the following is the BEST way to ensure ongoing control effectiveness?
Options:
Establishing policies and procedures
Periodically reviewing control design
Measuring trends in control performance
Obtaining management control attestations
Answer:
CExplanation:
The best way to ensure ongoing control effectiveness is to measure trends in control performance. This will help to monitor and evaluate how well the controls are achieving their objectives, and to identify any deviations or anomalies that may indicate control failures or weaknesses. Measuring trends in control performance also helps to provide feedback and assurance to the stakeholders and decision makers, and to support continuous improvement andoptimization of the control environment. Establishing policies and procedures, periodically reviewing control design, and obtaining management control attestations are good practices, but they are not the best way to ensure control effectiveness. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.1.1.2, page 1071
1: ISACA Certified in Risk and Information Systems Control (CRISC®) Exam Guide, Answer to Question 650.
Which of the following is MOST important to include when reporting the effectiveness of risk management to senior management?
Options:
Changes in the organization ' s risk appetite and risk tolerance levels
Impact due to changes in external and internal risk factors
Changes in residual risk levels against acceptable levels
Gaps in best practices and implemented controls across the industry
Answer:
CExplanation:
The most important information to include when reporting the effectiveness of risk management to senior management is the changes in residual risk levels against acceptable levels, as it indicates how well the risk management process and activities have reduced the risk exposure and impact to the level that is aligned with the risk tolerance and appetite of the organization. The other options are not the most important information, as they are more related to thedrivers,factors, or outcomes of risk management, respectively, rather than the effectiveness or value of risk management. References = CRISC Review Manual, 7th Edition, page 109.
Which of the following is the PRIMARY objective of engaging key stakeholders in the IT risk assessment process?
Options:
Reducing the time required for risk analysis
Increasing the quality of analysis
Building a risk aware culture
Ensuring proper budget allocation for risk remediation
Answer:
BExplanation:
The correct answer isBbecause engaging key stakeholders in the IT risk assessment process primarily improves thequality of analysis. Stakeholders provide business context, operational knowledge, and understanding of risk impacts, dependencies, and priorities. This leads to more accurate and relevant risk assessment results.
The other options are less appropriate:
A. Reducing the time required for risk analysisis not the primary objective.
C. Building a risk aware cultureis a valuable secondary benefit, but not the main reason for engagement in the assessment process.
D. Ensuring proper budget allocation for risk remediationmay result later, but not the primary objective of stakeholder involvement.
Exact Extracts supporting the answer:
“To ensure the overall effectiveness of a risk management program it is essential to have the participation of relevant stakeholders.”
“An interdisciplinary team within the enterprise offers the best perspective on risk management to employees and stakeholders.”
“The BEST approach when developing risk scenarios for an enterprise is to use both the top-down and the bottom-up approach because they have different perspectives.”
“The PRIMARY result of a risk assessment process is input for risk-aware decisions.”
These extracts show that stakeholder engagement is primarily valuable because it improves the completeness, relevance, and quality of risk analysis.
===========
Which of the following would be the BEST senior management action to influence a strong risk-aware culture within an organization?
Options:
Initiating disciplinary actions against individuals causing incidents
Identifying the root cause of incidents
Sponsoring changes to prevent recurrence of incidents
Reviewing the risk register and preparing incident reports
Answer:
CWhich of the following is a risk practitioner ' s BEST course of action when a control is not meeting agreed-upon performance criteria?
Options:
Implement additional controls to further mitigate risk
Review performance results with the control owner
Redefine performance criteria based on control monitoring results
Recommend a tool to meet the performance requirements
Answer:
BExplanation:
The best approach is tocollaborate with the control ownerto understand root causes and determine next steps. This respects ownership and enables targeted, informed decision-making before implementing drastic changes.
Which of the following provides the BEST indication that existing controls are effective?
Options:
Control testing
Control logging
Control documentation
Control design
Answer:
AExplanation:
Control effectiveness is best determined throughcontrol testing, which evaluates whether a control operates as intended over time. It includes functional and operational validation under real-world conditions, unlike documentation or design, which only indicate intent.
A Software as a Service (SaaS) company wants to use aggregated data from its clients to improve its services via a machine learning (ML) model. However, its contracts do not clearly allow this use of aggregated data. What should the organization do NEXT?
Options:
Request formal consent from clients to use their data.
Update the organization ' s privacy policy to reflect the use of aggregated data
Request internal risk acceptance from senior management.
Update the organization ' s data processing agreement template.
Answer:
AExplanation:
The correct answer isAbecause when contracts do not clearly permit the use of client data for a new purpose, the organization should first obtainformal client consentbefore using that aggregated data in an ML model. This is the strongest action because it addresses authorization, transparency, and legal/privacy expectations before the data is repurposed.
The other options are weaker as the next step:
B. Update the organization ' s privacy policyis not enough by itself if contractual permission is unclear.
C. Request internal risk acceptance from senior managementdoes not replace client permission or legal authority.
D. Update the organization ' s data processing agreement templateis useful for future contracts, but it does not solve the issue for current clients.
Exact Extracts supporting the answer:
“Upon learning of a new regulation for safeguarding information in specific transactions an IT manager should first assess whether existing controls meet the regulation.”
“For an enterprise expanded into different regions the major concern is that the employee handbook may violate local laws and regulations.”
“To ensure compliance with a new data protection regulation the risk practitioner should gather risk scenarios with a potential impact on compliance.”
“The MOST important consideration when transmitting personal information across networks is ensuring the privacy of the personal information.”
“A privacy impact assessment can help enterprises weigh the benefits of their data processing activities against risk to determine the appropriate response.”
These extracts support the principle that data use must be aligned with privacy, compliance, and authorized processing conditions. Since the contracts do not clearly allow this use, the next action is to seekformal consentfrom clients.
===========
Which of the following is the PRIMARY advantage of having a single integrated business continuity plan (BCP) rather than each business unit developing its own BCP?
Options:
It provides assurance of timely business process response and effectiveness.
It supports effective use of resources and provides reasonable confidence of recoverability.
It enables effective BCP maintenance and updates to reflect organizational changes.
It decreases the risk of downtime and operational losses in the event of a disruption.
Answer:
CA risk practitioners PRIMARY focus when validating a risk response action plan should be that risk response:
Options:
reduces risk to an acceptable level
quantifies risk impact
aligns with business strategy
advances business objectives.
Answer:
AExplanation:
The primary focus of a risk practitioner when validating a risk response action plan should be that the risk response reduces risk to an acceptable level. A risk response action plan is a document that describes the actions or measures that are taken or planned to modify the risk, such as reducing, avoiding, transferring, or accepting the risk1. Validating a risk response action plan means verifying whether the plan is feasible, effective, and efficient in addressing the risk2. The main objective of validating a risk response action plan is to ensure that the risk response reduces risk to an acceptable level, which is the level of risk that the organization is willing to tolerate or bear, based on its risk appetite and risk criteria3. Reducing risk to an acceptable level means that the risk response actions can lower the likelihood or impact of the risk to a point where the risk does not pose a significant threat or challenge to the organization’s objectives, operations, or performance. Reducing risk to an acceptable level also means that the risk response actions can balance the benefits and costs of the risk response, and that they can provide a reasonable assurance of the risk management effectiveness and efficiency4. The other options are not the primary focus of a risk practitioner when validating a risk response action plan, as they are either less relevant or less specific than reducing risk to an acceptable level. Quantifying risk impact is a component or element of validating a risk response action plan, notafocus of it. Quantifying risk impact means measuring or estimating the potential effects or consequences of the risk on the organization5. Quantifying risk impact can help to evaluate the severity and priority of the risk, as well as to compare the risk against the risk criteria and the risk appetite. However, quantifying risk impact is not the primary focus of a risk practitioner when validating a risk response action plan, as it does not address the feasibility, effectiveness, or efficiency of the risk response actions, or the level of risk reduction that they can achieve. Aligning with business strategy is a secondary or incidental benefit of validating a risk response action plan, not a primary or essential focus of it. Aligning with business strategy means ensuring that the risk response actions are consistent and coherent with the organization’s goals and values6. Aligning with business strategy can help to integrate the risk response actions with the organization’s culture and governance, as well as to support and enable the achievement of the organization’s mission and vision. However, aligning with business strategy is not the main focus of a risk practitioner when validating a risk response action plan, as it does not indicate the feasibility, effectiveness, or efficiency of the risk response actions, or the level of risk reduction that they can achieve. Advancing business objectives is a tertiary or indirect outcome of validating a risk response action plan, not a primary or direct focus of it. Advancing business objectives means contributing to the improvement and enhancement of the organization’s performance and results7. Advancing business objectives can help to create value and deliver benefits for the organization and its stakeholders, as well as to optimize the use of the organization’s resources and capabilities. However, advancing business objectives is not the main focus of a risk practitioner when validating a risk response action plan, as it does not address the feasibility, effectiveness, or efficiency of the risk response actions, or the level of risk reduction that they can achieve. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 2, Section 2.1.8, Page 61.
Which of the following is the MOST important consideration when selecting digital signature software?
Options:
Availability
Nonrepudiation
Accuracy
Completeness
Answer:
BExplanation:
Digital Signature Software:
Digital signatures are used to verify the authenticity and integrity of a message, document, or software. They provide cryptographic proof that the information has not been altered and that it comes from a verified source.
Importance of Nonrepudiation:
Nonrepudiation ensures that the sender of the message cannot deny having sent the message and the recipient cannot deny having received it. This is critical for legal and security purposes, as it provides undeniable proof of the origin and integrity of the information.
Selecting Digital Signature Software:
When selecting digital signature software, the most important consideration is that it provides strong nonrepudiation capabilities. This ensures that all parties involved can trust the authenticity and integrity of the signed data.
Comparing Other Considerations:
Availability:Ensures the software is accessible when needed but does not directly impact the trustworthiness of the signatures.
Accuracy:Important but generally inherent in properly functioning digital signature software.
Completeness:Ensures all required information is included but nonrepudiation is the critical factor for security and legal purposes.
References:
The CISSP Study Guide emphasizes the importance of nonrepudiation in digital signature technology to ensure authenticity and accountability (Sybex CISSP Study Guide, Chapter 7: PKI and Cryptographic Applications).
Which of the following criteria associated with key risk indicators (KRIs) BEST enables effective risk monitoring?
Options:
Approval by senior management
Low cost of development and maintenance
Sensitivity to changes in risk levels
Use of industry risk data sources
Answer:
CExplanation:
Key risk indicators (KRIs) are metrics that help organizations monitor and assess potential risks that may impact their operations, financial health, or overall performance1. KRIs should have certain characteristics that make them effective for risk monitoring, such as:
Ability to measure the right thing (e.g., supports the decisions that need to be made)
Quantifiable (e.g., damages in dollars of profit loss)
Capability to be measured precisely and accurately
Relevant (measuring the right thing associated with decisions)2
Among the four options given, only option C (sensitivity to changes in risk levels) best enables effective risk monitoring. This is because KRIs should be able to capture the changes in risk levels over time and alert organizations to emerging or escalating risks3. A high sensitivity to changes in risk levels indicates that theKRI is responsive and timely, and can help organizations take preventive or corrective actions before the risks become too severe.
References = Key Risk Indicators: A Practical Guide, Key Risk Indicators: Examples & Definitions, Key Risk Indicators - Wikipedia
A risk practitioner identifies a database application that has been developed and implemented by the business independently of IT. Which of the following is the BEST course of action?
Options:
Escalate the concern to senior management.
Document the reasons for the exception.
Include the application in IT risk assessments.
Propose that the application be transferred to IT.
Answer:
CExplanation:
The best course of action when a risk practitioner identifies a database application that has been developed and implemented by the business independently of IT is to include the application in IT risk assessments. IT risk assessments are the process of identifying, analyzing, and evaluating the IT-related risks that could affect the achievement of the enterprise’s objectives. By including the application in IT risk assessments, the risk practitioner can identify the potential threats, vulnerabilities, and impacts associated with the application, and recommend the appropriatecontrols and mitigation strategies to reduce the risk to an acceptable level. Escalating the concern to senior management, documenting the reasons for the exception, and proposing that the application be transferred to IT are not the best courses of action, as they do not address the risk exposure and impact of the application, and may not be feasible or desirable for the business. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 47.
Which of the following outcomes of disaster recovery planning is MOST important to enable the initiation of necessary actions during a disaster?
Options:
Definition of disaster recovery plan (DRP) scope and key stakeholders
Recovery time and maximum acceptable data loss thresholds
A checklist including equipment, location of data backups, and backup sites
A list of business areas and critical functions subject to risk analysis
Answer:
BExplanation:
Defining recovery time objectives (RTOs) and acceptable data loss thresholds is critical for effective disaster response, ensuring recovery activities are aligned with business priorities. This supportsBusiness Continuity Planning.
Which of the following is MOST helpful in identifying new risk exposures due to changes in the business environment?
Options:
Standard operating procedures
SWOT analysis
Industry benchmarking
Control gap analysis
Answer:
BExplanation:
New risk exposures due to changes in the business environment are the possibilities and impacts of new or emerging threats or opportunities that may affect the organization’s objectives, performance, or value creation, as a result of changes in the internal or external factors that influence the organization’s operations, such as technology, competition, regulation, or customer behavior12.
The most helpful tool in identifying new risk exposures due to changes in the business environment is a SWOT analysis, which is a technique that involves identifying and analyzing the strengths, weaknesses, opportunities, and threats (SWOT) that are relevant to the organization’s situation, goals, and capabilities34.
A SWOT analysis is the most helpful tool because it helps the organization to scan and assess the business environment, and to identify and prioritize the new or emerging risk exposures that may arise from the changes in the environment34.
A SWOT analysis is also the most helpful tool because it helps the organization to align and adapt its strategy and actions to the changes in the environment, and to leverage its strengths and opportunities, and mitigate its weaknesses and threats34.
The other options are not the most helpful tools, but rather possible sources or inputs that may be used in a SWOT analysis. For example:
Standard operating procedures are documents that describe the routine tasks and processes that are performed by the organization, and the policies and standards that govern them56. However, these documents are not the most helpful tools because they may not reflect or capture the changes in the business environment, and they may need to be revised or updated to address the new or emerging risk exposures56.
Industry benchmarking is a technique that involves comparing and contrasting the performance and practices of the organization with those of the similar or leadingorganizations in the same or related industry, and identifying the gaps or opportunities for improvement78. However, this technique is not the most helpful tool because it may not provide a comprehensive or holistic view of the business environment, and it may not align with the organization’s specific situation, goals, or capabilities78.
Control gap analysis is a technique that involves assessing and evaluating the adequacy and effectiveness of the controls that are designed and implemented to mitigate the risks, and identifying and addressing the areas or aspects that need to be improved or added . However, this technique is not the most helpful tool because it is reactive rather than proactive, and it may not identify or anticipate the new or emerging risk exposures that may result from the changes in the business environment . References =
1: Risk IT Framework, ISACA, 2009
2: IT Risk Management Framework, University of Toronto, 2017
3: SWOT Analysis - ISACA1
4: SWOT Analysis: What It Is and When to Use It2
5: Standard Operating Procedure - Wikipedia3
6: How to Write Effective Standard Operating Procedures (SOP)4
7: Benchmarking - Wikipedia5
8: Benchmarking: Definition, Types, Process, Advantages & Examples6
Control Gap Analysis - ISACA7
Control Gap Analysis: A Step-by-Step Guide8
Following a business continuity planning exercise, an organization decides to accept an identified risk associated with a critical business system. Which of the following should be done next?
Options:
Document the decision-making process and considerations used
Perform a business impact analysis (BIA) to assess the impact of the risk
Develop a disaster recovery plan (DRP) and business continuity plan (BCP) to ensure resiliency
Develop a control to reduce the level of the risk
Answer:
AExplanation:
When a risk is accepted, it must be documented in the risk register—including rationale, alternatives evaluated, decision-makers, and contextual factors. This aligns with governance and audit accountability requirements in ISACA guidance.
Which of the following methods is the BEST way to measure the effectiveness of automated information security controls prior to going live?
Options:
Testing in a non-production environment
Performing a security control review
Reviewing the security audit report
Conducting a risk assessment
Answer:
AExplanation:
Automated information security controls are controls that are implemented or executed by software or hardware, without human intervention, to protect the confidentiality, integrity, and availability of information and systems1. Examples of automated information security controls include firewalls, antivirus software, encryption, authentication, and logging2. The effectiveness of automated information security controls refers to how well they achieve their intended objectives and outcomes, such as preventing, detecting, or responding to security threats or incidents3. The best way to measure the effectiveness of automatedinformation security controls prior to going live is to test them in a non-production environment, which is an environment thatsimulates the production environment, but does not contain real or sensitive data orsystems4. Testing in a non-production environment allows the organization to verify the proper and consistent configuration, functionality, and performance of the automated information security controls, without affecting the normal operations or risking the exposure of the data or systems5. Testing in a non-production environment also enables the organization to identify andresolve any issues or gaps in the automated information security controls, and to evaluate their compatibility and interoperability with other systems or controls6. Performing a security control review, reviewing the security audit report, and conducting a risk assessment are not the best ways to measure the effectiveness of automated information security controls prior to going live, as they do not provide direct and timely information on the configuration, functionality, and performance of the automated information security controls. Performing a security control review is a process that involves checking and verifying that the organization’s security controls are up to date, relevant, and effective7. A security control review can help to identify and address any issues or gaps in the security controls, but it does not show the actual behavior and results of the automated information security controls in a realistic environment. Reviewing the security audit report is a process that involves reading and analyzing the findings and recommendations of an independent examination and evaluation of the organization’s security controls8. A security audit report can help to provide assurance and advice on the adequacy and effectiveness of the security controls, but it does not show the current and dynamic status and performance of the automated information security controls in a changing environment. Conducting a risk assessment is a process that involves identifying, analyzing, and evaluating the risks and their potential impacts on the organization’s objectives and performance. A risk assessment can help to anticipate and prepare for the risks that may affect the organization’s security, but it does not show the actual impact and outcome of the automated information security controls in a specific scenario. References = 1: Automation Support for Security Control Assessments - NIST2: Automated Security Control Assessment: When Self-Awareness Matters3: Technology Control Automation: Improving Efficiency, Reducing … - ISACA4: [What is a Non-Production Environment? | Definition and FAQs] 5: [Why You Need a Non-Production Environment - Plutora] 6: [Testing Automated Security Controls - SANS Institute] 7: A brief guide to assessing risks and controls | ACCA Global8: IT Risk Resources | ISACA : [Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.1: Risk Identification, pp. 57-59.]
Which of the following techniques is MOST helpful when quantifying the potential loss impact of cyber risk?
Options:
Cost-benefit analysis
Penetration testing
Business impact analysis (BIA)
Security assessment
Answer:
CExplanation:
Understanding Business Impact Analysis (BIA):
BIA is a process used to identify and evaluate the potential effects (impact) of interruptions to critical business operations as a result of a disaster, accident, or emergency.
It helps quantify the potential loss impact of cyber risks by assessing the financial and operational consequences of disruptions.
Quantifying Loss Impact:
BIA involves determining the value of business processes and the impact of their loss. This includes evaluating factors such as revenue loss, additional operational costs, legal penalties, and reputational damage.
By analyzing the criticality of business functions and their dependencies, BIA provides a detailed understanding of potential impacts, aiding in the development of risk mitigation strategies.
Comparing Other Techniques:
Cost-Benefit Analysis:Useful for evaluating the cost-effectiveness of controls but does not provide a comprehensive assessment of potential loss impacts.
Penetration Testing:Identifies vulnerabilities but does not quantify the business impact of exploiting those vulnerabilities.
Security Assessment:Evaluates security controls but is not focused on the broader business impact of potential disruptions.
References:
The CRISC Review Manual emphasizes the role of BIA in assessing the impact of risks on business operations and quantifying potential losses (CRISC Review Manual, Chapter 2: IT Risk Assessment, Section 2.7 Business Impact Analysis).
Which of the following BEST helps to identify significant events that could impact an organization?
Options:
Control analysis
Vulnerability analysis
Scenario analysis
Heat map analysis
Answer:
CExplanation:
Scenario analysis is the best method to identify significant events that could impact an organization. Scenario analysis is the process of creating and evaluating hypothetical situations or scenarios that represent plausible outcomes of various events or actions. Scenario analysis helps to anticipate and prepare for potential risks and opportunities, as well as to test the robustness and resilience of the organization’s strategies and plans. Control analysis, vulnerability analysis, and heat map analysis are not as effective as scenario analysis, because they focus on the existing or current state of the organization, rather than the future or alternative states. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 4-13.
Which of the following is the MOST relevant information to include in a risk management strategy?
Options:
Quantified risk triggers
Cost of controls
Regulatory requirements
Organizational goals
Answer:
DExplanation:
The most relevant information to include in a risk management strategy is the organizational goals, because they provide the direction and purpose for the risk management activities. A risk managementstrategy is a document that outlines the objectives, scope, approach, roles, and responsibilities for managing risks in an organization. A risk management strategy should align with the organizational goals, which are the desired outcomes or results that the organization wants to achieve. The organizational goals should be specific, measurable, achievable, relevant, and time-bound (SMART), and they should reflect the organization’s vision, mission, values, and strategy. By including the organizational goals in the risk management strategy, the risk practitioner can ensure that the risk management process supports and enables the achievement of the organizational goals. The risk practitioner can also use the organizational goals as a basis for identifying, assessing, prioritizing, and responding to the risks that may affect theorganization’s performance and success. The risk practitioner can also monitor and measure the progress and effectiveness of the risk management process by comparing the actual results with the expected results based on the organizational goals. Therefore, the organizational goals are themost relevant information to include in a risk management strategy, as they provide the foundation and framework for the risk management process. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.1: IT Risk Management Strategy, pp. 3-61
Which of the following is the PRIMARY objective of establishing an organization ' s risk tolerance and appetite?
Options:
To align with board reporting requirements
To assist management in decision making
To create organization-wide risk awareness
To minimize risk mitigation efforts
Answer:
BExplanation:
Risk tolerance and appetite are the expressions of the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk tolerance is the acceptable level of variation that the organization is willing to allow for the outcome of its risk decisions. Riskappetite is the broad-based amount of risk that the organization is willing to accept in its activities. The primary objective of establishing an organization’s risk tolerance and appetite is to assist management in decision making, as they provide guidance and boundaries for the risk management activities and decisions. By establishing the risk tolerance and appetite, the organization can align its risk exposure with its strategic goals, optimize its risk-return trade-off, and enhance its risk culture and performance. References = CRISC Review Manual, 7th Edition, page 61.
Which of the following is the BEST way to mitigate the risk associated with fraudulent use of an enterprise ' s brand on Internet sites?
Options:
Utilizing data loss prevention (DLP) technology
Monitoring the enterprise ' s use of the Internet
Scanning the Internet to search for unauthorized usage
Developing training and awareness campaigns
Answer:
CExplanation:
Scanning the Internet for unauthorized usage of the enterprise ' s brand proactively identifies fraudulent activities and enables timely response. This aligns withBrand Protection and Risk Mitigationstrategies.
Which of the following is the GREATEST benefit of identifying appropriate risk owners?
Options:
Accountability is established for risk treatment decisions
Stakeholders are consulted about risk treatment options
Risk owners are informed of risk treatment options
Responsibility is established for risk treatment decisions.
Answer:
AExplanation:
The greatest benefit of identifying appropriate risk owners is that accountability is established for risk treatment decisions. Risk owners are the individuals or groups who are responsible and accountable formanaging a specific risk and its associated actions and outcomes. By identifying appropriate risk owners, the organization can ensure that the risk treatment decisions are made by the people who have the authority, knowledge, and interest in the risk. Stakeholders beingconsulted, risk owners being informed, and responsibility being established are other possible benefits, but they are not as great as accountability being established. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
Which of the following would offer the MOST insight with regard to an organization ' s risk culture?
Options:
Risk management procedures
Senior management interviews
Benchmark analyses
Risk management framework
Answer:
BExplanation:
Senior management interviews would offer the MOST insight with regard to an organization’s risk culture, because they can reveal the attitudes, values, beliefs, and behaviors of the seniormanagement towards risk management, and how they influence and support the risk management process and activities in the organization. Senior management interviews can also provide information on the risk appetite, tolerance, and objectives of the organization, and how they are communicated and implemented across the organization. The other options are not as insightful as senior management interviews, because:
Option A: Risk management procedures are the steps and methods that define how the risk management process and activities are performed in the organization, but they do not necessarily reflect the risk culture of the organization, which is more about the human and behavioral aspects of risk management.
Option C: Benchmark analyses are the comparisons of the performance and practices of the organization with those of similar or successful organizations, but they do not necessarily reflect the risk culture of the organization, which is more about the internal and unique aspects of risk management.
Option D: Risk management framework is the set of rules and standards that guide and support the risk management process and activities in the organization, but it does not necessarily reflect the risk culture of the organization, which is more about the leadership and commitment aspects of risk management. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 82.
Reviewing historical risk events is MOST useful for which of the following processes within the risk management life cycle?
Options:
Risk monitoring
Risk mitigation
Risk aggregation
Risk assessment
Answer:
DExplanation:
Reviewing historical risk events is most useful for the risk assessment process within the risk management life cycle. Risk assessment is the process of identifying, analyzing, and evaluating the risks that may affect the project or the organization1. Reviewing historical risk events can help to:
Identify the sources, causes, and consequences of past risks and learn from the successes and failures of previous projects or organizations
Analyze the likelihood and impact of potential risks based on historical data and trends, and use statistical methods or models to estimate the probability and severity of risk scenarios
Evaluate the level of risk exposure and compare it with the risk appetite and tolerance of the project or the organization, and prioritize the risks that need further attention or action
Use historical risk events as inputs or examples for risk identification and analysis techniques, such as brainstorming, checklists, interviews, surveys, SWOT analysis, root cause analysis, or Monte Carlo simulation2
References = Risk and Information Systems Control Study Manual, Chapter 5: Risk Assessment Process3
To define the risk management strategy which of the following MUST be set by the board of directors?
Options:
Operational strategies
Risk governance
Annualized loss expectancy (ALE)
Risk appetite
Answer:
BExplanation:
Risk appetite is the broad-based amount of risk that an organization is willing to accept in pursuit of its objectives. Risk appetite reflects the level of risk that the organization is prepared to take to achieve its strategic goals, and provides guidance and boundaries for the risk management activities and decisions. To define the risk management strategy, which is the plan and approach for managing the risks that may affect the achievement of the organization’s objectives, the factor that must be set by the board of directors is the risk appetite. The board of directors is the highest governing body of the organization, and has the ultimate responsibility and authority for setting the direction and oversight of the organization. By setting the risk appetite, the board of directors can communicate its expectations and preferences for the risk exposure and performance of the organization, and ensure alignment with the business objectives and strategies. References = 3
An organization ' s decision to remain noncompliant with certain laws or regulations is MOST likely influenced by:
Options:
The region in which the organization operates.
Established business culture.
Risk appetite set by senior management.
Identified business process controls.
Answer:
CExplanation:
Risk appetite determined by senior management reflects the enterprise ' s willingness to accept certain levels of risk, including noncompliance. This decision underscores the strategic trade-offs made in risk management, a key element inGovernance and Risk Policy Alignment.
Which of the following is the MOST important outcome of a business impact analysis (BIA)?
Options:
Understanding and prioritization of critical processes
Completion of the business continuity plan (BCP)
Identification of regulatory consequences
Reduction of security and business continuity threats
Answer:
AExplanation:
The most important outcome of a business impact analysis (BIA) is understanding and prioritization of critical processes. A BIA is a process that identifies and evaluates the potential effects of disruptions or disasters on the organization’s business functions and processes. A BIA helps to understand the dependencies, interrelationships, and impacts of the business processes, and to prioritize them based on their importance and urgency. A BIA also helps to determine the recovery objectives, strategies, and resources for the business processes, such as the recovery time objective (RTO), the recovery point objective (RPO), and the minimum operating requirements (MOR). The other options are not as important as understanding and prioritization of critical processes, although they may be part of or derived from the BIA. Completion of thebusiness continuity plan (BCP), identification of regulatory consequences, and reduction of security and business continuity threats are all activities or outcomes that can be supported or facilitated by the BIA, but they are not the primary purpose or result of the BIA. References = CISA Review Manual, 27th Edition, Chapter 5, Section 5.2.1, page 5-9.
A recent internal risk review reveals the majority of core IT application recovery time objectives (RTOs) have exceeded the maximum time defined by the business application owners. Which of the following is MOST likely to change as a result?
Options:
Risk forecasting
Risk tolerance
Risk likelihood
Risk appetite
Answer:
BExplanation:
Recovery time objectives (RTOs) are the maximum acceptable time frames for restoring the critical functions and processes after a disruption1. RTOs are derived from the business impact analysis (BIA) andreflect the organization’s risk appetite, which is the amount of risk that an organization is willing to accept to achieve its objectives2. Risk tolerance is the level of risk a company is willing to tolerate, and it is affected by a number of factors, including how much uncertainty or financial loss can be tolerated and where those losses will impact operations3. Risk tolerance is used to measure if the risk exposure is within the risk appetite and to implement controls to reduce the residual risk to an acceptable level2. If the majority of core IT application RTOs have exceeded the maximum time defined by the business application owners, it means that the organization is not meeting its risk appetite and is exposed to more risk than it can accept. Therefore, the most likely change as a result is to adjust the risk tolerance to reflect the current reality and to take actions to improve the recovery capabilities and reduce the risk exposure4. Risk forecasting is the process of estimating the potential outcomes and impactsof future events that may affect the organization’s objectives5. Risk forecasting may change as aresult of the RTOs exceeding the maximum time, but it is not the most likely change, as it does not directly address the gap between the risk appetite and the risk exposure. Risk likelihood is the probability of a risk event occurring5. Risk likelihood may change as a result of the RTOs exceeding the maximum time, but it is not the most likely change, as it does not directly measure the impact of the risk event on the organization’s objectives. Risk appetite is the amount of risk that an organization is willing to accept to achieve its objectives2. Risk appetite may change as a result of the RTOs exceeding the maximum time, but it is not the most likely change, as it is a strategic decision that reflects the organization’s vision and mission, and not a tactical response to a specific risk event. References = Risk and Information Systems Control Study Manual, Chapter 5: Risk Response and Mitigation, Section 5.3: Business Continuity Planning, pp. 227-238.
What are the MOST essential attributes of an effective Key control indicator (KCI)?
Options:
Flexibility and adaptability
Measurability and consistency
Robustness and resilience
Optimal cost and benefit
Answer:
BExplanation:
Measurability and consistency are the most essential attributes of an effective key control indicator (KCI), because they ensure that the KCI can be quantified, compared, and reported over time. A KCI should be able to measure the performance or effectiveness of a control in mitigating a risk and provide consistent results across different periods, sources, and methods. The other options are not the most essential attributes, although they may also be desirable for a KCI. Flexibility and adaptability are not the most essential attributes, because they may compromise the reliability and comparability of the KCI. Robustness and resilience are not the most essential attributes, because they are more relevant for the control itself, not the KCI. Optimal cost and benefit are not the most essential attributes, because they are more related to the value and feasibility of the KCI, not the quality and accuracy of the KCI. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers
Of the following, who is responsible for approval when a change in an application system is ready for release to production?
Options:
Information security officer
IT risk manager
Business owner
Chief risk officer (CRO)
Answer:
CExplanation:
The business owner is the person who is responsible for approval when a change in an application system is ready for release to production. The business owner is the person who has the authority and accountability for the business process or function that is supported by the application system. The business owner should approve the change to ensure that it meets the business requirements, objectives, and expectations, and that it does not introduce any adverse impacts or risks to the business operations. The information security officer, the IT risk manager, and the chief risk officer (CRO) are not responsible for the approval of the change, although they may provide input, feedback, or oversight. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.4.1, page 3-32.
Which of the following should be the PRIMARY consideration when identifying and assigning ownership of IT-related risk?
Options:
Accountability for control operation
Ability to design controls to mitigate the risk
Accountability for losses due to impact
Span of control within the organization
Answer:
CExplanation:
The correct answer isCbecause the primary consideration when assigning ownership of IT-related risk isaccountability for losses due to impact. Risk ownership should be assigned to the person or function with the authority and accountability for the business consequences if the risk materializes. Ownership should align to business accountability, not just technical control operation.
The other options are less appropriate:
A. Accountability for control operationmay belong to a control owner, but that is not always the same as the risk owner.
B. Ability to design controls to mitigate the riskis relevant to implementation, not primary ownership.
D. Span of control within the organizationmay influence practicality, but it is not the key principle for assigning risk ownership.
Exact Extracts supporting the answer:
“Accountability for business risk related to IT primarily lies with users of IT services.”
“For an IT system supporting a critical business process senior managers should be accountable for the risk.”
“For an organizational business unit the most accurate description of risk-related roles and responsibilities is that the management team owns the risk and is responsible for identifying assessing and mitigating risk and reporting to the appropriate support functions and the board of directors.”
“The best basis for establishing risk ownership is mapping identified risk to a specific business process.”
“During the risk assessment process it is most important to establish a clear line of accountability to ensure that risk ownership is assigned to the appropriate level.”
These extracts show that risk ownership must align with the party accountable for the business impact of the risk. Therefore, the primary consideration isaccountability for losses due to impact.
A control owner has completed a year-long project To strengthen existing controls. It is MOST important for the risk practitioner to:
Options:
update the risk register to reflect the correct level of residual risk.
ensure risk monitoring for the project is initiated.
conduct and document a business impact analysis (BIA).
verify cost-benefit of the new controls being implemented.
Answer:
DExplanation:
The risk practitioner should verify the cost-benefit of the new controls being implemented to ensure that they are aligned with the enterprise’s risk appetite and strategy, and that they provide value to the business. The other options are not as important as verifying the cost-benefit of the new controls, because:
Option A: Updating the risk register is a good practice, but it does not provide assurance that the new controls are effective and efficient.
Option B: Ensuring risk monitoring for the project is initiated is also a good practice, but it is not as urgent as verifying the cost-benefit of the new controls, which should be done before the project is closed.
Option C: Conducting and documenting a BIA is not relevant to the scenario, as the project is already completed and the new controls are implemented. References = Risk and Information Systems Control Study Manual, 7th Edition, ISACA, 2020, p. 184.
Which of the following would BEST enable a risk-based decision when considering the use of an emerging technology for data processing?
Options:
Gap analysis
Threat assessment
Resource skills matrix
Data quality assurance plan
Answer:
AExplanation:
The best way to enable a risk-based decision when considering the use of an emerging technology for data processing is to perform a gap analysis. A gap analysis is a technique that compares the current state and the desired state of a process, system, or capability, and identifies the gaps or differences between them. A gap analysis can help to evaluate the benefits, costs, risks, and opportunities of using an emerging technology for data processing, and to determine the feasibility, suitability, and readiness of adopting the emerging technology. The other options are not as helpful as a gap analysis, as they are related to the specific aspects or components ofthe data processing, not the overall assessment and comparison of the current and desired state of the data processing. References = Risk and Information Systems Control Study Manual, Chapter 1: IT Risk Identification, Section 1.2: IT Risk Identification Methods, page 19.
An organization has been notified that a disgruntled, terminated IT administrator has tried to break into the corporate network. Which of the following discoveries should be of GREATEST concern to the organization?
Options:
Authentication logs have been disabled.
An external vulnerability scan has been detected.
A brute force attack has been detected.
An increase in support requests has been observed.
Answer:
AExplanation:
Authentication logs are records of the attempts and results of logging into an IT system, network, or application, such as the user name, password, date, time, location, or device1. Authentication logs can help to verify and audit the identity and access of the users, and to detect and investigate any unauthorized or suspicious login activities, such as failed or repeated attempts, or unusual patterns or locations2.
Among the four options given, the discovery that authentication logs have been disabled should be of greatest concern to the organization. This is because disabling authentication logs can:
Prevent or hinder the organization from monitoring and controlling the access and activity of the users, especially the disgruntled, terminated IT administrator who may have malicious intentions or insider knowledge
Enable or facilitate the disgruntled, terminated IT administrator or other attackers to bypass or compromise the authentication mechanisms or policies, and gain unauthorized or elevated access to the IT systems, networks, or applications
Conceal or erase the evidence or traces of the login attempts or actions of the disgruntled, terminated IT administrator or other attackers, and make it difficult or impossible to identify, investigate, or prosecute them
Indicate or imply that the disgruntled, terminated IT administrator or other attackers have already breached or compromised the IT systems, networks, or applications, and have disabled the authentication logs to cover their tracks or avoid detection3
References = What is Authentication Logging?, Authentication Logging - Wikipedia, Fired admin cripples former employer’s network using old credentials
Which of the following is the PRIMARY reason to ensure software engineers test patches before release to the production environment?
Options:
To detect incompatibilities that might disrupt the operation
To provide assurance that deployed patches have been properly authorized
To understand how long it will take to deploy the patch
To support availability by authorizing the release of the patch at the appropriate time
Answer:
AExplanation:
Pre-production compatibility testing ensures patches won’t break applications or services, protecting availability—a key control objective outlined in ISACA’s guidance on Change and Configuration Management.
Which of the following is the PRIMARY objective of a risk awareness program?
Options:
To demonstrate senior management support
To enhance organizational risk culture
To increase awareness of risk mitigation controls
To clearly define ownership of risk
Answer:
BExplanation:
A risk awareness program is a set of activities and communication methods that aim to increase the understanding and knowledge of risk among the stakeholders of an organization. The primary objective of a risk awareness program is to enhance the organizational risk culture, which is the shared values, beliefs, and attitudes that influence how risk is perceived and managed in the organization. A risk awareness program can help to promote a risk-aware culture by:
•Educating stakeholders on the concepts and benefits of risk management
•Aligning risk management with the organization’s vision, mission, and objectives
•Encouraging stakeholder participation and collaboration in risk management processes
•Fostering a positive attitude towards risk taking and learning from failures
•Reinforcing risk management roles and responsibilities
•Recognizing and rewarding good risk management practices
What is the BEST approach for determining the inherent risk of a scenario when the actual likelihood of the risk is unknown?
Options:
Use the severity rating to calculate risk.
Classify the risk scenario as low-probability.
Use the highest likelihood identified by risk management.
Rely on range-based estimates provided by subject-matter experts.
Answer:
DExplanation:
When likelihood is unknown, range-based estimates from subject-matter experts provideinformed and realistic insights into potential risk exposure. This approach helps approximate the inherent risk based on experience and expertise, supporting effective decision-making.
Which of the following is the BEST way to maintain a current list of organizational risk scenarios?
Options:
Automate workflow for risk status updates.
Perform regular reviews of key controls.
Conduct periodic risk reviews with stakeholders.
Conduct compliance reviews.
Answer:
CExplanation:
Regular reviews with stakeholders ensure the risk scenarios are current, complete, and relevant. Stakeholders provide operational and strategic insights, enabling the identification of new, evolving, or obsolete risks. Periodic reviews foster dynamic and continuous alignment of risk scenarios with the business context and threat landscape.
Which of the following is the BEST evidence that a user account has been properly authorized?
Options:
An email from the user accepting the account
Notification from human resources that the account is active
User privileges matching the request form
Formal approval of the account by the user ' s manager
Answer:
CExplanation:
According to the CRISC Review Manual, formal approval of the account by the user’s manager is the best evidence that a user account has been properly authorized, because it ensures that the user’s role and access rights are consistent with the business needs and the principle of least privilege. The user’s manager is responsible for verifying the user’s identity, job function, and access requirements, and for approving or rejecting the account request. The other options are not the best evidence of proper authorization, because they do not involve the user’s manager’s approval. An email from the user accepting the account is a confirmation of the account creation, but it does not indicate that the account was authorized by the user’s manager. Notification from human resources that the account is active is an administrative process that does not verify the user’s access rights and role. User privileges matching the request form is a verification of the account configuration, but it does not ensure that the request form was approved by the user’s manager. References = CRISC Review Manual, 7th Edition, Chapter 4, Section 4.1.2, page 163.
Which of the following provides the BEST measurement of an organization ' s risk management maturity level?
Options:
Level of residual risk
The results of a gap analysis
IT alignment to business objectives
Key risk indicators (KRIs)
Answer:
DExplanation:
Risk management maturity level is the degree to which an organization has developed and implemented a systematic and proactive approach to managing the risks that it faces across its various functions, processes, and activities. Risk management maturity level reflects the organization’s risk culture and capability, and its alignment with its objectives and strategies1.
The best measurement of an organization’s risk management maturity level is the key risk indicators (KRIs), which are metrics or measures that provide information on the current or potential exposure and performance of the organization in relation to specific risks. KRIs can help to:
Monitor and track the changes or trends in the risk level and the risk response over time
Identify and alert the risk issues or events that require attention or action
Evaluate and report the effectiveness and efficiency of the risk management processes and practices
Support and inform the risk decision making and improvement23
KRIs can be classified into different types, such as:
Leading KRIs, which are forward-looking and predictive, and indicate the likelihood or probability of a risk event occurring in the future
Lagging KRIs, which are backward-looking and descriptive, and indicate the impact or consequence of a risk event that has already occurred
Quantitative KRIs, which are numerical or measurable, and indicate the magnitude or severity of a risk event or outcome
Qualitative KRIs, which are descriptive or subjective, and indicate the nature or characteristics of a risk event or outcome4
The other options are not the best measurements of an organization’s risk management maturity level, but rather some of the factors or outcomes of it. Level of residual risk is the level of risk that remains after the risk response has been implemented. Level of residual risk reflects the effectiveness and efficiency of the risk response, and the need for further action or monitoring. The results of a gap analysis are the differences between the current and the desired state of the risk management processes and practices. The results of a gap analysis reflect the completeness and coverage of the risk management activities, and the areas for improvement or enhancement. IT alignment to business objectives is the extent to which IT supports and enables the achievement of the organization’s goals and strategies. IT alignment to business objectives reflects the integration and coordination of the IT and business functions, and the optimization of the IT value and performance. References =
Risk Maturity Assessment Explained | Risk Maturity Model
Key Risk Indicators - ISACA
Key Risk Indicators: What They Are and How to Use Them
Key Risk Indicators: Types and Examples
[CRISC Review Manual, 7th Edition]
A risk practitioner can use an organization ' s problem management process to anticipate potential risk within IT systems by:
Options:
conducting regular user satisfaction surveys to gather feedback on system performance.
continuously monitoring system metrics to identify performance issues.
analyzing incident trends to identify underlying issues that could lead to system failures.
implementing security patches and updates to prevent vulnerabilities from being exploited.
Answer:
CExplanation:
The correct answer isCbecause problem management helps anticipate potential risk byanalyzing incident trends to identify underlying issuesbefore they lead to more serious failures. Problem management is concerned with identifying recurring causes and systemic weaknesses, which makes it useful for anticipating future IT risk.
The other options are less accurate:
A. conducting regular user satisfaction surveysprovides feedback, but does not directly anticipate system risk.
B. continuously monitoring system metricsis useful, but that is more aligned with operational monitoring than problem management.
D. implementing security patches and updatesis a treatment activity, not the predictive use of problem management.
Exact Extracts supporting the answer:
“To determine the factors responsible for a loss event a risk professional should use cause-and-effect analysis.”
“After a security incident the first step toward yielding an actionable plan that effectively mitigates the risk is root cause analysis.”
“The risk register is the best tool for identifying changes in an enterprise’s risk profile.”
“The main purpose of continuous monitoring is detecting changes to the enterprise’s risk environment.”
These extracts support that identifying root causes and recurring incident patterns is the best way to anticipate future IT system risk.
===========
Which of the following is the BEST way for a risk practitioner to present an annual risk management update to the board ' '
Options:
A summary of risk response plans with validation results
A report with control environment assessment results
A dashboard summarizing key risk indicators (KRIs)
A summary of IT risk scenarios with business cases
Answer:
CExplanation:
A dashboard summarizing key risk indicators (KRIs) is the best way for a risk practitioner to present an annual risk management update to the board because it provides a concise and visual overview of the current risk status, trends, and performance of the organization. KRIs are metrics that measure the likelihood and impact of risks, and help the board monitor and prioritize the most critical risks. A summary of risk response plans, a report with control environment assessment results, and a summary of IT risk scenarios are all useful information, but they are too detailed and technical for the board, who needs a high-level and strategic view of the risk management program. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.1, page 4-36.
Which of the following is MOST important for maintaining the effectiveness of an IT risk register?
Options:
Removing entries from the register after the risk has been treated
Recording and tracking the status of risk response plans within the register
Communicating the register to key stakeholders
Performing regular reviews and updates to the register
Answer:
DExplanation:
An IT risk register is a document that records the identified IT risks, their analysis, and their responses. It is a useful tool for managing and communicating the IT risks throughout the project or the organization. The most important factor for maintaining the effectiveness of an IT risk register is to perform regular reviews and updates to the register, meaning that the riskpractitioner should periodically check and revise the riskregister to reflect the changes in the IT risk environment, the project status, or the organization’s objectives. Performing regular reviews and updates to the register can help to ensure that the risk register is accurate, complete, and current, and that it provides relevant and reliable information for the risk management decision making and actions. Performing regular reviews and updates to the register can also help to identify any new or emerging IT risks, as well as to monitor and report on the IT risk performance and improvement. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.1, p. 106-107
Which of the following is MOST important to ensure before using risk reports in decision making?
Options:
Root cause analysis is included.
Risk analysis results are validated.
Real-time risk information is provided.
Quantitative risk data is provided.
Answer:
BExplanation:
Validation of risk analysis results ensures the data is accurate, reliable, and can be trusted for making informed decisions. It minimizes the risk of acting on flawed insights.
Which of the following is the PRIMARY risk management responsibility of the second line in the three lines model?
Options:
Applying risk treatments
Implementing internal controls
Monitoring risk responses
Providing assurance of control effectiveness
Answer:
CExplanation:
Thesecond line of defensein the Three Lines Model plays arisk oversightandmonitoringrole rather than operational execution.
According to ISACA’s CRISC framework:
Thefirst line(operational management) owns and manages risk and implements controls.
Thesecond line(risk and compliance functions) providesrisk oversight, guidance, and monitoringof risk responses and ensures adherence to policies and frameworks.
Thethird line(internal audit) providesindependent assuranceregarding the overall effectiveness of controls.
Therefore, theprimary responsibilityof the second line is tomonitor and evaluate risk responsesimplemented by the first line to ensure they are effective and aligned with enterprise risk appetite.
Supporting Extract:
CRISC study notes (Slides 127–134) state:
“The most significant benefit of using the three lines of defense model is that it clarifies essential roles of key stakeholders. The second line of defense provides oversight and monitoring of risk and control activities.”
Hence, the correct answer isC. Monitoring risk responses.
When establishing an enterprise IT risk management program, it is MOST important to:
Options:
review alignment with the organizations strategy.
understand the organization ' s information security policy.
validate the organization ' s data classification scheme.
report identified IT risk scenarios to senior management.
Answer:
AExplanation:
The most important thing to do when establishing an enterprise IT risk management program is to review the alignment with the organization’s strategy. The organization’s strategy is the plan or direction that the organization follows to achieve its vision, mission, and goals. The IT risk management program should be aligned with the organization’s strategy, so that it supports and enables the organization’s strategic objectives, and addresses the IT risks that could affect the organization’s performance and value. Reviewing the alignment with the organization’s strategy helps to ensure that the IT risk management program is relevant, effective, and consistent with the organization’s expectations and needs. The other options are not as important as reviewing the alignment with the organization’s strategy, although they may be useful or necessary steps or components of the IT risk management program. Understanding the organization’s information security policy, validating the organization’s data classification scheme, and reporting identified IT risk scenarios to senior management are all activities that can help to implement and improvethe IT risk management program, but they are not the initial or primary thing todo. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.1, page 2-12.
Which of the following situations would BEST justify escalation to senior management?
Options:
Residual risk exceeds acceptable limits.
Residual risk is inadequately recorded.
Residual risk remains after controls have been applied.
Residual risk equals current risk.
Answer:
AExplanation:
Residual risk exceeds acceptable limits, because it indicates that the risk level is higher than the organization’s risk appetite or tolerance, and that the risk responses and controls are insufficient or ineffective. Residual risk is the level of risk remaining in a process or procedure following the implementation of risk controls to limit or remove it. Escalation is a process that increases theawareness and involvement of higher-level stakeholders or authorities in a risk issue or situation. Escalation is appropriate when the risk issue or situation is outside the scope or authority of the current risk owner or manager, and requires the attention or action of the senior management or the board of directors. Residual risk exceeding acceptable limits is the best situation to justify escalation, as it implies that the current risk owner or manager cannot manage the risk within the predefined boundaries or expectations, and that the senior management or the board of directors need to intervene or approve the risk acceptance or transfer.
Residual risk being inadequately recorded, residual risk remaining after controls have been applied, and residual risk equaling current risk are all possible situations that may require escalation, but they are not the best situations, as they do not necessarily indicate that the risk level is higher than the acceptable limits, and that the senior management or the board of directors need to be involved.
Using key risk indicators (KRIs) to illustrate changes in the risk profile PRIMARILY helps to:
Options:
communicate risk trends to stakeholders.
assign ownership of emerging risk scenarios.
highlight noncompliance with the risk policy
identify threats to emerging technologies.
Answer:
AExplanation:
The primary purpose of using key risk indicators (KRIs) to illustrate changes in the risk profile is to communicate risk trends to stakeholders. KRIs are metrics that provide an early warning of increasing risk exposure in various areas of the organization. By using KRIs to illustrate changes in the risk profile, the organization can communicate the risk trends to the stakeholders, such as the board, senior management, business units, and external parties, and enable them to take appropriate actions to manage the risk. Assigning ownership of emerging risk scenarios, highlighting noncompliance with the risk policy, and identifying threats to emerging technologies are other possible purposes, but they are not as important as communicating risk trends to stakeholders. References = ISACA Certified in Risk and Information Systems Control(CRISC) Certification Exam Question and Answers, question 12; CRISC Review Manual, 6th Edition, page 215.
Which of the following would BEST help secure online financial transactions from improper users?
Options:
Review of log-in attempts
multi-level authorization
Periodic review of audit trails
multi-factor authentication
Answer:
DExplanation:
According to the 10 Tips for Secure Online Transactions - SmartAsset article, multi-factor authentication is a security measure that requires users to provide more than one piece of evidence to verify their identity when logging in to an online account. For example, users may need to enter a password and a code sent to their phone or email, or use a biometric feature such as a fingerprint or a face scan. Multi-factor authentication can help secure online financial transactions from improper users, as it makes it harder for hackers to access the account even if they have the password. Multi-factor authentication can also alertusers to any suspicious login attempts and prevent unauthorized transactions. References = 10 Tips for Secure Online Transactions - SmartAsset
Which of the following BEST contributes to the implementation of an effective risk response action plan?
Options:
An IT tactical plan
Disaster recovery and continuity testing
Assigned roles and responsibilities
A business impact analysis
Answer:
AExplanation:
A governance, risk, and compliance (GRC) solution is an integrated system that supports the management of governance, risk, and compliance activities across the enterprise. A GRC solution can provide benefits such as improved efficiency, consistency, transparency, andaccountability. The best justification to invest in the development of a GRC solution is to facilitate risk-aware decision making by stakeholders. By providing a holistic view of the enterprise’s risk profile, a GRC solution can enable stakeholders to make informed decisions that are aligned with the enterprise’s objectives, risk appetite, and tolerance. A GRC solution can also help to monitor and report on the performance and outcomes of the risk management program, and provide feedback and assurance to the board of directors and senior management. The other options are not as compelling as the facilitation of risk-aware decision making, as they may not directly contribute to the achievement of the enterprise’s objectives or the management of its risks. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.1.2.1, pp. 12-13.
Which of the following is a risk practitioner ' s BEST course of action upon learning that regulatory authorities have concerns with an emerging technology the organization is considering?
Options:
Redesign key risk indicators (KRIs).
Update risk responses.
Conduct a SWOT analysis.
Perform a threat assessment.
Answer:
DExplanation:
Performing a threat assessment is the best course of action for a risk practitioner upon learning that regulatory authorities have concerns with an emerging technology that the organization is considering, because it helps to identify and analyze the sources and types of threats that may exploit the vulnerabilities or weaknesses of the technology, and to estimate their likelihood and impact. A threat is a potential event or action that may cause harm or damage to the organization or its objectives, such as a natural disaster, a cyberattack, or a human error. A threat assessment is a process of systematically identifying and assessing the threats that an organization faces, and estimating their probability and severity. An emerging technology is a new or innovative technology that has the potential to disrupt or transform the existing markets, industries, or practices, such as artificial intelligence, blockchain, or biotechnology. An emerging technology may offer benefits such as competitive advantage, efficiency, or creativity, but it may also pose risks such as technical complexity, interoperability issues, regulatory uncertainty, or ethicaldilemmas. Therefore, performing a threat assessment is the best course of action, as it helps to understand and evaluate the threats and their consequences, and to determine the appropriate controls or mitigating factors to reduce or eliminate them. Redesigning key riskindicators (KRIs), updating risk responses, and conducting a SWOT analysis are all possiblecourses of action to perform after performing a threat assessment, but they are not the best course of action, as they depend on the results and recommendations of the threat assessment. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.2, page 87
To enable effective risk governance, it is MOST important for senior management to:
Options:
Ensure the IT governance framework is up to date.
Communicate the risk management strategy across the organization.
Gain a clear understanding of business risk and related ownership.
Ensure security policies and procedures are documented.
Answer:
DWhich of the following controls BEST helps to ensure that transaction data reaches its destination?
Options:
Securing the network from attacks
Providing acknowledgments from receiver to sender
Digitally signing individual messages
Encrypting data-in-transit
Answer:
BExplanation:
Providing acknowledgments from receiver to sender is a control that helps to ensure that transaction data reaches its destination, as it confirms the successful delivery of the data and allows the sender to resend the data in case of failure. Securing the network from attacks, digitally signing individual messages, and encrypting data-in-transit are controls that help toensure the integrity and confidentiality of the data, but not the availability or delivery of the data. References = CRISC by Isaca Actual Free Exam Q & As, question 199.
Which of the following should be the FIRST step when a company is made aware of new regulatory requirements impacting IT?
Options:
Perform a gap analysis.
Prioritize impact to the business units.
Perform a risk assessment.
Review the risk tolerance and appetite.
Answer:
DExplanation:
New regulatory requirements impacting IT are those that impose new obligations, restrictions, or standards on how an organization uses, manages, or secures its IT systems, data, or services1. Examples of such regulations include the GDPR, the CCPA, the HIPAA, or the PCI-DSS2. New regulatory requirements impacting IT can pose significant challenges and risks for an organization, such as:
Compliance costs and efforts, such as updating policies, procedures, and systems, training staff, or hiring experts
Noncompliance penalties and consequences, such as fines, lawsuits, sanctions, or reputational damages
Operational disruptions or inefficiencies, such as system changes, data migrations, or service interruptions
Competitive disadvantages or opportunities, such as losing or gaining customers, partners, or markets3
The first step that should be done when a company is made aware of new regulatory requirements impacting IT is to review the risk tolerance and appetite. Risk tolerance is the acceptable level of variation that an organization is willing to accept around its risk appetite. Risk appetite is the amount and type of risk that an organization is willing to take in order to meet its strategic objectives. By reviewing the risk tolerance and appetite, the company can:
Establish a clear and consistent understanding of the organization’s goals, values, and expectations regarding the new regulatory requirements impacting IT
Assess the current and potential impacts of the new regulatory requirements impacting IT on the organization’s performance, operations, or assets
Determine the level of risk exposure and acceptance that the organization is comfortable with, and identify the risk thresholds or limits that should not be exceeded
Align the risk management strategies and actions with the organization’s risk tolerance and appetite, and prioritize the most critical and urgent risks to be addressed
Communicate and report the risk tolerance and appetite to the stakeholders and regulators, and ensure transparency and accountability
References = Regulating emerging technology | Deloitte Insights, Ten Key Regulatory Challenges of 2024 - kpmg.com, The Risks of Non-Compliance with Data Protection Laws, [Risk Tolerance - COSO], [Risk Appetite - COSO] , [Risk Appetite and Tolerance - IRM]
An organization ' s recovery team is attempting to recover critical data backups following a major flood in its data center. However, key team members do not know exactly what steps should be taken to address this crisis. Which of the following is the MOST likely cause of this situation?
Options:
Failure to test the disaster recovery plan (DRP)
Lack of well-documented business impact analysis (BIA)
Lack of annual updates to the disaster recovery plan (DRP)
Significant changes in management personnel
Answer:
AExplanation:
The most likely cause of the situation where the recovery team does not know what steps to take to recover critical data backups following a major flood is the failure to test the disaster recovery plan (DRP). A DRP is a document that describes the procedures and resources needed to restore the normal operations of an organization after a disaster. Testing the DRP is essential to ensure that the plan is feasible, effective, and up-to-date. Testing the DRP also helps to train the recovery team members, identify and resolve any issues or gaps, and improve the confidence and readiness of the organization. The lack of a well-documented business impact analysis (BIA), the lack of annual updates to the DRP, and the significant changes in management personnel are also possible factors that could affect the recovery process, butthey are not as likely or as critical as the failure to test the DRP. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.3.1, page 5-19.
Which of the following is MOST important to address for an organization looking to improve its IT asset management processes?
Options:
Lack of predictive analytics for asset failures
Lack of detailed historical asset data
Lack of a centralized asset inventory
Lack of asset valuation mechanisms
Answer:
CExplanation:
The correct answer isCbecause acentralized asset inventoryis the foundation of effective IT asset management. Without a complete and centralized inventory, the organization cannot reliably identify, classify, protect, monitor, or retire assets. Asset ownership, control requirements, lifecycle status, and associated risk cannot be managed consistently if the organization does not first know what assets exist and where they reside.
The other options are less important as a primary improvement area:
A. Lack of predictive analytics for asset failuresis a maturity enhancement, not a foundational requirement.
B. Lack of detailed historical asset datamay affect trend analysis, but current control begins with knowing what assets exist now.
D. Lack of asset valuation mechanismsis helpful for risk analysis, but valuation depends on first having a complete inventory.
Exact Extracts supporting the answer:
“The preparation of a risk register begins in the risk identification process.”
“The PRIMARY advantage of creating and maintaining a risk register is to ensure that an inventory of identified risk is maintained.”
“The FIRST step in identifying and assessing IT risk is to gather information on the current and future environment.”
“To evaluate the effectiveness of a risk mitigation control identifying the current state of existing controls is essential during the risk assessment process.”
These extracts support the principle that effective management starts with accurate identification and inventory. Therefore, the most important issue to address is thelack of a centralized asset inventory.
===========
Which of the following would be a risk practitioner ' s BEST course of action when a project team has accepted a risk outside the established risk appetite?
Options:
Reject the risk acceptance and require mitigating controls.
Monitor the residual risk level of the accepted risk.
Escalate the risk decision to the project sponsor for review.
Document the risk decision in the project risk register.
Answer:
CExplanation:
Risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. Risk appetite can be expressed in qualitative or quantitative terms, and can vary depending on the context and the stakeholder. Risk appetite should be defined and communicated by the senior management or the board of directors, and should guide the risk management decisions and actions throughout the organization. When a project team has accepted a risk outside the established risk appetite, the risk practitioner’s best course of action is to escalate the risk decision to the project sponsor for review, meaning that the risk practitioner should report the risk acceptance and its rationale to the project sponsor, who is the person or group that provides the resources and support for the project, and is accountable for its success. The project sponsor should review the risk decision and determine whether it is aligned with the organization’s objectives and strategy, and whether it requires any further approval oraction. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.3.1, p. 25-26
A failure in an organization’s IT system build process has resulted in several computers on the network missing the corporate endpoint detection and response (EDR) software. Which of the following should be the risk practitioner ' s IMMEDIATE concern?
Options:
Threats are not being detected.
Multiple corporate build images exist.
The IT build process was not followed.
The process documentation was not updated.
Answer:
AExplanation:
The primary concern is the immediate risk of undetected threats due to missing endpoint protection. Addressing this ensures the organization ' s ability to detect and respond to security incidents, aligning withIncident Detection and Responseprinciples.
What is the MAIN benefit of using a top-down approach to develop risk scenarios?
Options:
It describes risk events specific to technology used by the enterprise.
It establishes the relationship between risk events and organizational objectives.
It uses hypothetical and generic risk events specific to the enterprise.
It helps management and the risk practitioner to refine risk scenarios.
Answer:
BExplanation:
The main benefit of using a top-down approach to develop risk scenarios is that it establishes the relationship between risk events and organizational objectives. A top-down approach is a method of risk identification and analysis that starts with the organization’s strategic objectives and then identifies the potential risk events that could affect or prevent the achievement of those objectives. A top-down approach helps to establish the relationship between risk events and organizational objectives, because it links the risk scenarios to the organization’s mission, vision, values, and strategy, and it prioritizes the risk scenarios based on their impact and relevance to the organization’s objectives. A top-down approach also helps to align and communicate the risk scenarios with the organization’s stakeholders, such as the board, management, and business units, and to facilitate the risk response and monitoring activities. The other options are not the main benefit of using a top-down approach, although they may be part of or derived from the top-down approach. Describing risk events specific to technology used by the enterprise, using hypothetical and generic risk events specific to the enterprise, and helping management and the risk practitioner to refine risk scenarios are all activities or outcomes that could be performed or achieved by using a top-down approach, but they are not the primary purpose or result of the top-down approach. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.2.1, page 4-13.
Which of the following occurs during the implementation phase of the system development life cycle (SDLC)?
Options:
Evaluation of updated coding into production
Collaboration with stakeholders to gather system requirements
Development of architectural designs based on system requirements
Formal authorization for deploying the system into production
Answer:
DExplanation:
In the SDLC process, theimplementation phaseculminates withformal authorization to move the system into production. CRISC emphasizes that this phase includes system testing, training, data migration, and readiness assessments. The final output is a formal “go-live” approval. Requirements gathering occurs in the requirements phase, and architectural design belongs to the design phase. Evaluating code updates is part of testing but does not represent the final governance checkpoint. Therefore, the defining characteristic of the implementation phase is the formal approval to deploy the solution into the operational environment.
The PRIMARY benefit associated with key risk indicators (KRls) is that they:
Options:
help an organization identify emerging threats.
benchmark the organization ' s risk profile.
identify trends in the organization ' s vulnerabilities.
enable ongoing monitoring of emerging risk.
Answer:
DExplanation:
Key risk indicators (KRIs) are metrics that provide information on the level of exposure to a given risk. They enable ongoing monitoring of emerging risk by alerting the organization when the risk level exceeds thepredefined threshold or tolerance. By using KRIs, the organization can track the changes in the risk environment and take timely and appropriate actions to mitigate or avoid the risk.
Helping an organization identify emerging threats, benchmarking the organization’s risk profile, and identifying trends in the organization’s vulnerabilities are all possible uses of KRIs, but they are not the primary benefit. The primary benefit is to enable ongoing monitoring of emerging risk, which encompasses all these aspects and more. References = CRISC Review Manual, 7th Edition, ISACA, 2020, page 27-281
Which of the following is the MAIN benefit of involving stakeholders in the selection of key risk indicators (KRIs)?
Options:
Improving risk awareness
Obtaining buy-in from risk owners
Leveraging existing metrics
Optimizing risk treatment decisions
Answer:
AExplanation:
The main benefit of involving stakeholders in the selection of key risk indicators (KRIs) is improving risk awareness, as it helps to communicate the risk exposure, appetite, and tolerance of the organization to the relevant parties. KRIs are metrics that provide information on the level of exposure to a given operational risk1. By involving stakeholders in the selection of KRIs, the risk practitioner can ensure that the KRIs are aligned with the stakeholder expectations, needs, and objectives, and that they reflect the most significant risks that affect the organization. This also helps to foster a risk culture and a shared understanding of risk among the stakeholders, which can enhance the risk management process and performance. The other options are not the main benefit of involving stakeholders in the selection of KRIs, although they may be some of the outcomes or advantages of doing so. Obtaining buy-in from risk owners, leveraging existing metrics, and optimizing risk treatment decisions are all important aspects of risk management, but they are not the primary reason for involving stakeholders in the selection of KRIs. References = Key Risk Indicators; Key Risk Indicators: A Practical Guide; The 10 Types of Stakeholders That You Meet in Business; What are Stakeholders? Stakeholder Definition | ASQ
Options:
Conduct frequent internal audits of IT systems.
Review information from threat intelligence sources.
Define a comprehensive set of key risk indicators (KRIs).
Document thorough IT risk scenarios in the risk register.
Answer:
BExplanation:
The identification of advanced persistent threats (APTs) is best supported by timely and relevant external information. Reviewing information from threat intelligence sources enables the organization to detect emerging threats quickly and accurately, reducing the mean time to identify APTs. While internal audits and KRIs are important, they typically focus on internal controls and risk monitoring rather than external threat detection. Thorough documentation of risk scenarios supports risk assessment but does not directly reduce detection time. Therefore, leveraging threat intelligence is the most effective approach for early identification of sophisticated threats.
An organization requires a third party for processing customer personal data. Which of the following is the BEST approach when sharing data over a public network?
Options:
Include a nondisclosure agreement (NDA) for personal data in the contract.
Implement a digital rights protection tool to monitor data.
Use a virtual private network (VPN) to communicate data.
Transfer a read-only version of the data.
Answer:
CExplanation:
Using a VPN ensures the secure transmission of sensitive data over a public network by encrypting the communication channel. This mitigates risks such as interception or unauthorized access, aligning withData Protection and Privacy Standards.
Which of the following provides the MOST useful information for developing key risk indicators (KRIs)?
Options:
Business impact analysis (BIA) results
Risk scenario ownership
Risk thresholds
Possible causes of materialized risk
Answer:
DExplanation:
Key risk indicators (KRIs) are metrics that provide an early warning of increasing risk exposure in various areas of the organization. They help to monitor changes in the level of risk and enable timely actions to mitigate the risk. The most useful information for developing KRIs is the possible causes of materialized risk, which are the factors or events that trigger or contribute to the occurrence of a risk. By identifying the possible causes of materialized risk, an organization can design KRIs that measure the likelihood and impact of the risk, and alert the management when the risk exceeds the acceptable level. References = CRISC Review Manual, 7th Edition, page 101.
Which of the following is the BEST method to track asset inventory?
Options:
Periodic asset review by management
Asset registration form
Automated asset management software
IT resource budgeting process
Answer:
CExplanation:
Automated asset management software is the best method to track asset inventory because it can provide real-time, accurate, and comprehensive data on the location, condition, value, and usage of assets. It can also help to optimize asset utilization, reduce costs, improve compliance, and enhance security.
References
•Free Asset Tracking Templates | Smartsheet
•5 Best Asset Management Software (2023) – Forbes Advisor
•What Is Asset Tracking? Benefits & How It Works - Forbes
•Inventory and Asset Tracking: Keep it Simple (But Powerful)
An organization recently invested in an identity and access management (IAM) solution to manage user activities across corporate mobile devices. Which of the following is MOST important to update in the risk register?
Options:
Inherent risk
Risk appetite
Risk tolerance
Residual risk
Answer:
DExplanation:
Residual risk is the remaining risk after implementing risk responses, such as controls or mitigation strategies. With the deployment of an IAM solution, the organization has addressed certain access-related risks. Updating the risk register to reflect the new residual risk levels ensures accurate tracking and informs future risk management decisions.
The patch management process is MOST effectively monitored through which of the following key control indicators (KCIs)?
Options:
Number of legacy servers out of support
Percentage of patches deployed within the target time frame
Number of patches deployed outside of business hours
Percentage of patched systems tested
Answer:
BExplanation:
Monitoring the percentage of patches deployed within the target time frame is a critical key control indicator for the patch management process. It reflects the organization ' s ability to apply necessary updates promptly, reducing exposure to known vulnerabilities. Timely patch deployment is essential for maintaining system security and compliance with organizational policies.
Which of the following is MOST helpful when prioritizing action plans for identified risk?
Options:
Comparing risk rating against appetite
Obtaining input from business units
Determining cost of controls to mitigate risk
Ranking the risk based on likelihood of occurrence
Answer:
AExplanation:
Comparing risk rating against appetite is the most helpful criterion when prioritizing action plans for identified risk, as it helps to determine the urgency and importance of addressing the risk. Risk rating is the level of risk after considering the likelihood and impact of a risk event, and risk appetite is the amount and type of risk that an organization is willing to accept in pursuit of its objectives. By comparing risk rating against appetite, an organization can identify which risks are above, within, or below its tolerance level, and prioritize the action plans accordingly. Risks that are above the appetite level should be treated with the highest priority, as they pose asignificant threat to the organization’s objectives and performance. Risks that are within the appetite level should be monitored and controlled regularly, as they are acceptable but still require attention. Risks that are below the appetite level should be reviewed periodically, as they are negligible or insignificant.
Which of the following is MOST important for an organization to have in place to identify unauthorized devices on the network?
Options:
A technology review and approval process
An acceptable use policy
An automated network scanning solution
A bring your own device (BYOD) policy
Answer:
CExplanation:
Automated scanning tools continuously monitor the network, detecting unauthorized devices quickly and reliably.
Which of the following BEST facilities the alignment of IT risk management with enterprise risk management (ERM)?
Options:
Adopting qualitative enterprise risk assessment methods
Linking IT risk scenarios to technology objectives
linking IT risk scenarios to enterprise strategy
Adopting quantitative enterprise risk assessment methods
Answer:
CExplanation:
The best way to facilitate the alignment of IT risk management with enterprise risk management (ERM) is to link IT risk scenarios to enterprise strategy, because this ensures that the IT risks are considered in the context of the enterprise’s mission, vision, and goals. Linking IT risk scenarios to enterprise strategy also helps to prioritize the IT risks based on their impact and relevance to the enterprise’s objectives, and to select the appropriate risk responses and resources. The other options are not the best ways to facilitate the alignment of IT risk management with ERM, because they do not address the integration or alignment of the IT and enterprise perspectives. Adopting qualitative or quantitative enterprise risk assessment methods, and linking IT risk scenarios to technology objectives are examples of techniques or tools that can be used to perform IT risk management or ERM, but they do not ensure the alignment or consistency of the two processes. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.3, p. 22.
Upon learning that the number of failed backup attempts continually exceeds
the current risk threshold, the risk practitioner should:
Options:
initiate corrective action to address the known deficiency.
adjust the risk threshold to better reflect actual performance.
inquire about the status of any planned corrective actions.
keep monitoring the situation as there is evidence that this is normal.
Answer:
AWhich of the following is MOST important requirement to include in a Software as a Service (SaaS) vendor contract to ensure data is protected?
Options:
The vendor must provide periodic independent assurance reports.
The vendor must host data in a specific geographic location.
The vendor must be held liable for regulatory fines for failure to protect data.
The vendor must participate in an annual vendor performance review.
Answer:
BExplanation:
The vendor must host data in a specific geographic location to ensure that the data is protected by the applicable data protection laws of the EU or the country where the data originates. This is especially important for SaaS customers who transfer personal data from the EU to third countries, as they need to comply with the GDPR and the new Standard Contractual Clauses (SCCs) that regulate such transfers. The vendor must also provide adequate security measures and guarantees to protect the data from unauthorized access, disclosure, or loss. References = Risk and Information Systems Control Study Manual, Chapter 5: IT Risk Mitigation, Section 5.3: IT Risk Mitigation Strategies and Approaches, Page 253; Data Protection – New EU Standard Contractual Clauses - Bodle Law.
Which of the following BEST enables an organization to address risk associated with technical complexity?
Options:
Documenting system hardening requirements
Minimizing dependency on technology
Aligning with a security architecture
Establishing configuration guidelines
Answer:
CExplanation:
Addressing Technical Complexity:
Security Architecture Alignment: Aligning with a security architecture helps manage the complexity by providing a structured framework for implementing and managing security controls.
Comprehensive Framework: A security architecture ensures that all security controls are integrated and aligned with the organization’s overall security strategy, reducing the risk associated with technical complexity.
Steps Involved:
Develop or Adopt a Security Architecture: Use established frameworks such as SABSA, TOGAF, or Zachman.
Implementation: Apply the security architecture across all systems and processes to ensure consistency and integration.
Monitoring and Maintenance: Continuously monitor the security architecture and update it as necessary to address new threats and technologies.
Comparison with Other Options:
Documenting System Hardening Requirements: Important but does not address the overall complexity.
Minimizing Dependency on Technology: Not always feasible and does not fully address the inherent complexity.
Establishing Configuration Guidelines: Helpful but should be part of the broader security architecture.
Best Practices:
Continuous Improvement: Regularly update and improve the security architecture to adapt to evolving threats and technologies.
Training and Awareness: Ensure that all relevant personnel understand the security architecture and their role in maintaining it.
Which of the following is the MOST important reason to communicate control effectiveness to senior management?
Options:
To demonstrate alignment with industry best practices
To assure management that control ownership is assigned
To ensure management understands the current risk status
To align risk management with strategic objectives
Answer:
CExplanation:
According to the ISACA Risk and Information Systems Control study guide and handbook, the most important reason to communicate control effectiveness to senior management is to ensure management understands the current risk status. Control effectiveness is a measure of how well a control reduces the likelihood or impact of a risk event. By communicating control effectiveness, risk managers can provide management with relevant and timely information about the residual risk level, the risk appetite and tolerance, and the potential gaps or weaknesses in the control environment. This can help management make informed decisions about risk response strategies, resource allocation, and risk oversight12
1: ISACA Risk and Information Systems Control Study Guide, 4th Edition, page 33 2: ISACA Risk and Information Systems Control Handbook, 1st Edition, page 25
During a risk treatment plan review, a risk practitioner finds the approved risk action plan has not been completed However, there were other risk mitigation actions implemented. Which of the fallowing is the BEST course of action?
Options:
Review the cost-benefit of mitigating controls
Mark the risk status as unresolved within the risk register
Verify the sufficiency of mitigating controls with the risk owner
Update the risk register with implemented mitigating actions
Answer:
CExplanation:
The best course of action for a risk practitioner who finds that the approved risk action plan has not been completed but other risk mitigation actions have been implemented is to verify the sufficiency of mitigating controls with the risk owner. This is because the risk owner is the person who is accountable for the risk and the risk response strategy, and therefore should be consulted to ensure that the alternative actions are adequate and effective in reducing the risk to an acceptable level. The other options are not the best course of action, although they may also be performed after verifying the sufficiency of mitigating controls with the risk owner. Reviewing the cost-benefit of mitigating controls, marking the risk status as unresolved within the risk register, and updating the risk register with implemented mitigating actions are secondary actions that depend on the outcome of the verification process. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 4, Section 4.3.2, p. 193.
Which of the following key performance indicators (KPis) would BEST measure me risk of a service outage when using a Software as a Service (SaaS) vendors
Options:
Frequency of business continuity plan (BCP) lasting
Frequency and number of new software releases
Frequency and duration of unplanned downtime
Number of IT support staff available after business hours
Answer:
CExplanation:
Software as a Service (SaaS) is a cloud computing model that provides software applications over the internet, without requiring the users to install or maintain them on their own devices. SaaS vendors are responsible for hosting, managing, and updating the software applications, and providing technical support and security to the users. The key performance indicator (KPI) that would best measure the risk of a service outage when using a SaaS vendor is the frequency and duration of unplanned downtime, which is the amount and length of time that the software applications are unavailable or inaccessible due to unexpected events, such as network failures, server crashes, power outages, cyberattacks, etc. The frequency and duration of unplanned downtime indicate the reliability and availability of the SaaS vendor, and the potential impact of the service outage on the users’ business operations and productivity. References = 3
Which of the following is the BEST indication of a mature organizational risk culture?
Options:
Corporate risk appetite is communicated to staff members.
Risk owners understand and accept accountability for risk.
Risk policy has been published and acknowledged by employees.
Management encourages the reporting of policy breaches.
Answer:
BExplanation:
Organizational risk culture is the term describing the values, beliefs, knowledge, attitudes and understanding about risk shared by a group of people with a common purpose. Organizationalrisk culture influences how the organization identifies, assesses, and manages risks, and how it aligns its risk appetite and tolerance with its objectives and strategies1.
The best indication of a mature organizational risk culture is that risk owners understand and accept accountability for risk, because it means that the organization:
Clearly defines and assigns the roles and responsibilities of the risk owners, who are the individuals or groups who have the authority and ability to manage the risks within their scope or domain
Empowers and supports the risk owners to perform their risk management duties, such as identifying, assessing, responding, monitoring, and reporting the risks
Holds the risk owners accountable for the outcomes and consequences of the risks, and evaluates their performance and compliance with the risk policies, standards, and procedures
Encourages and rewards the risk owners for demonstrating risk awareness and competence, and for contributing to the risk management improvement and learning23
The other options are not the best indications of a mature organizational risk culture, but rather some of the elements or aspects of it. Corporate risk appetite is the amount and type of risk that the organization is willing to accept in order to achieve its objectives. Corporate risk appetite is communicated to staff members to guide their risk decision making and behavior, and to ensure the consistency and alignment of the risk taking and tolerance across the organization. Risk policy is the document that establishes the principles, framework, and process for managing the risks within the organization. Risk policy is published and acknowledged by employees to ensure their awareness and compliance with the risk management expectations and requirements. Management is the group of individuals who have the authority and responsibility to direct and control the organization’s activities and resources. Management encourages the reporting of policy breaches to ensure the transparency and accountability of the risk management performance and outcomes, and to identify and address the risk management issues and gaps4. References =
Risk culture - Institute of Risk Management
Risk Owner - ISACA
Taking control of organizational risk culture | McKinsey
[CRISC Review Manual, 7th Edition]
Which of the following is the BEST approach when a risk practitioner has been asked by a business unit manager for special consideration during a risk assessment of a system?
Options:
Conduct an abbreviated version of the assessment.
Report the business unit manager for a possible ethics violation.
Perform the assessment as it would normally be done.
Recommend an internal auditor perform the review.
Answer:
CExplanation:
According to the CRISC Review Manual, performing the assessment as it would normally be done is the best approach when a risk practitioner has been asked by a business unit manager for special consideration during a risk assessment of a system, because it ensures that the risk practitioner maintains their objectivity, integrity, and professionalism. The risk practitioner should not compromise the quality or accuracy of the risk assessment, regardless of any external pressure or influence. The risk practitioner should follow the established risk assessment methodology and standards, and report the risk results and recommendations based on the facts and evidence. The other options are not the best approaches, because they may affect the credibility or reliability of the risk assessment. Conducting an abbreviated version of the assessment may result in incomplete or insufficient risk information, which may lead to poor riskdecisions or actions. Reporting the business unit manager for a possible ethics violation may escalate the situation or create a conflict of interest, which may hinder the risk assessment process or outcome. Recommending an internal auditor perform the review may transfer the responsibility or accountability of the risk practitioner, which may undermine their role or authority. References = CRISC Review Manual, 7th Edition, Chapter 2, Section 2.2.1, page 74.
Which of the following is the PRIMARY reason to perform periodic vendor risk assessments?
Options:
To provide input to the organization ' s risk appetite
To monitor the vendor ' s control effectiveness
To verify the vendor ' s ongoing financial viability
To assess the vendor ' s risk mitigation plans
Answer:
BExplanation:
The primary reason to perform periodic vendor risk assessments is to monitor the vendor’s control effectiveness. A vendor risk assessment is a process of evaluating the risks associated with outsourcing a service or function to a third-party vendor. The assessment should be performed periodically to ensure that the vendor is complying with the contractual obligations, service level agreements, and security standards, and that the vendor’s controls are operating effectively to mitigate the risks. Providing input to the organization’s risk appetite, verifying the vendor’s ongoing financial viability, and assessing the vendor’s risk mitigation plans are otherpossible reasons, but they are not as important as monitoring the vendor’s control effectiveness. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 11; CRISC Review Manual, 6th Edition, page 144.
Which of the following stakeholders are typically included as part of a line of defense within the three lines of defense model?
Options:
Board of directors
Vendors
Regulators
Legal team
Answer:
DExplanation:
The three lines of defense model is a framework that describes the roles and responsibilities of different stakeholders in the risk management and internal control processes of an organization. The three lines of defense are:
The first line of defense: the operational management and staff who are responsible for identifying, assessing, and responding to the risks, as well as implementing and maintaining the controls within their areas of activity.
The second line of defense: the risk management, compliance, and security functions who are responsible for establishing the risk policies and standards, providing guidance and support, monitoring and reporting on the risk performance and compliance, and facilitating the risk management and internal control processes across the organization.
The third line of defense: the internal audit function who is responsible for providing independent and objective assurance on the effectiveness and efficiency of the risk management and internal control processes, as well as recommending improvements and best practices. The stakeholders who are typically included as part of a line of defense within the three lines of defense model are the legal team, who belong to the second line of defense. The legal team is responsible for ensuring that the organization complies with the relevant laws and regulations, aswell as for advising and assisting the organization on the legal aspects and implications of the risk management and internal control processes. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.4.1, p. 32-33
An organization recently implemented new technologies that enable the use of robotic process automation. Which of the following is MOST important to reassess?
Options:
Risk profile
Risk tolerance
Risk capacity
Risk appetite
Answer:
AExplanation:
The risk profile is the most important thing to reassess when an organization implements new technologies that enable the use of robotic process automation (RPA). The risk profile is a comprehensive and dynamic view of the organization’s risks, their ratings, responses, and status. RPA can introduce new risks or change the existing risks related to the organization’s objectives, operations, and performance. For example, RPA can create risks such as system failures, databreaches, compliance violations, human errors, or ethical dilemmas. Therefore, the organization should reassess its risk profile to identify, assess, treat, monitor, and review the risks associated with RPA, and to ensure that the risk management strategy is aligned with the business needs and expectations.
A risk practitioner is preparing a report to communicate changes in the risk and control environment. The BEST way to engage stakeholder attention is to:
Options:
include detailed deviations from industry benchmarks,
include a summary linking information to stakeholder needs,
include a roadmap to achieve operational excellence,
publish the report on-demand for stakeholders.
Answer:
BExplanation:
A risk practitioner is preparing a report to communicate changes in the risk and control environment, such as new or emerging risks, changes in risk levels, risk responses, or control effectiveness. The best way to engage stakeholder attention is to include a summary linking information to stakeholder needs, meaning that the report should highlight the key points and findings that are relevant and important for the stakeholder’s role, responsibility, and interest. The summary should also explain how the information affects the stakeholder’s objectives, expectations, and decisions. The summary should be concise, clear, and compelling, and should capture the stakeholder’s attention and interest. The report can also include detailed deviations from industry benchmarks, a roadmap to achieve operational excellence, or an option to publish the report on-demand for stakeholders, but these are not the best ways to engage stakeholder attention, as they may not be directly related to the stakeholder’s needs or may overwhelm the stakeholder with too much information. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.4.1, p. 124-125
Which of the following BEST indicates that risk management is embedded into the responsibilities of all employees?
Options:
The number of incidents has decreased over time
Industry benchmarking is performed on an annual basis
Risk management practices are audited on an annual basis
Risk management practices are incorporated into business processes
Answer:
DExplanation:
Embedding risk management into day-to-day business processes reflects organizational maturity and integration. It ensures employees consider risk in operational decisions and continuously support the risk management framework.
A financial institution has identified high risk of fraud in several business applications. Which of the following controls will BEST help reduce the risk of fraudulent internal transactions?
Options:
Periodic user privileges review
Log monitoring
Periodic internal audits
Segregation of duties
Answer:
DExplanation:
The best control to help reduce the risk of fraudulent internal transactions in several business applications is the segregation of duties. Segregation of duties is the principle of dividing the roles and responsibilities of different individuals or groups involved in a business process or an IT service, so that no one person or group has complete control over the entire process or service. Segregation of duties can help to prevent or detect fraud, errors, conflicts of interest, or misuse of resources, by ensuring that there are checks and balances, and that there is adequate oversight and accountability. Segregation of duties can also help to reduce the risk of collusion, compromise, or coercion among the internal staff, by limiting their access and authority to thebusiness applications and data. Periodic user privileges review, log monitoring, and periodic internal audits are also useful controls, but they are not as effective as segregation of duties, as they are reactive and detective measures, rather than proactive and preventive measures. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 217.
Which of the following is the MOST important key performance indicator (KPI) to establish in the service level agreement (SLA) for an outsourced data center?
Options:
Percentage of systems included in recovery processes
Number of key systems hosted
Average response time to resolve system incidents
Percentage of system availability
Answer:
DExplanation:
The percentage of system availability is the most important key performance indicator (KPI) to establish in the service level agreement (SLA) for an outsourced data center. This KPI measures the uptime or reliability of the systems hosted by the data center provider, and reflects the ability of the provider to meet the customer’s expectations and requirements for system performance and accessibility. A high percentage of system availability indicates that the provider is delivering consistent and quality service, while a low percentage of system availability indicates that the provider is experiencing frequent or prolonged system failures or disruptions, which can negatively affect the customer’s business operations and reputation. Therefore, the percentage ofsystem availability is a critical factor for evaluating the effectiveness and efficiency of the data center provider, and should be clearly defined and monitored in the SLA. The other options are not the most important KPIs to establish in the SLA for an outsourced data center, as they do not directly measure the quality or reliability of the service provided. The percentage of systems included in recovery processes is a measure of the scope or coverage of the disaster recovery plan (DRP) of the data center provider, but it does not indicate how well the provider can execute the DRP or restore the systems in the event of a disaster. The number of key systems hosted is a measure of the capacity or utilization of the data center provider, but it does not indicate how efficiently or securely the provider can manage the systems. The average response time to resolve system incidents is a measure of the responsiveness or agility of the data center provider, but it does not indicate how effectively or proactively the provider can prevent or mitigate system incidents. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3, Section 3.2.3.4, Page 140.
Which of the following is the BEST way to determine the ongoing efficiency of control processes?
Options:
Perform annual risk assessments.
Interview process owners.
Review the risk register.
Analyze key performance indicators (KPIs).
Answer:
DExplanation:
Control processes are the procedures and activities that aim to ensure the effectiveness and efficiency of the organization’s operations, the reliability of its information, and the compliance with its policies and regulations12.
The ongoing efficiency of control processes is the degree to which the control processes achieve their intended results with minimum resources, costs, or waste34.
The best way to determine the ongoing efficiency of control processes is to analyze key performance indicators (KPIs), which are quantifiable measures of progress toward an intended result, such as a strategic objective or a desired outcome56.
Analyzing KPIs is the best way because it provides a systematic and consistent method of evaluating the performance of the control processes, and identifying the areas of improvement or optimization56.
Analyzing KPIs is also the best way because it enables the organization to monitor and report the efficiency of the control processes to the relevant stakeholders, and to take corrective or preventive actions when necessary56.
The other options are not the best way, but rather possible sources of information or inputs that may support or complement the analysis of KPIs. For example:
Performing annual risk assessments is a way to identify and evaluate the risks that may affect the organization’s objectives, and to determine the adequacy and effectiveness ofthe control processes in mitigating those risks12. However, this way is not the best because it is periodic rather than continuous, and may not capture the changes or trends in the efficiency of the control processes12.
Interviewing process owners is a way to collect and verify the information and feedback from the people who are responsible for designing, implementing, and operating the control processes12. However, this way is not the best because it is subjective and qualitative, and may not provide reliable or comparable data on the efficiency of the control processes12.
Reviewing the risk register is a way to examine and update the documentation and status of the risks and the control processes that are associated with them12. However, this way is not the best because it is descriptive rather than analytical, and may not measure or evaluate the efficiency of the control processes12. References =
1: Risk IT Framework, ISACA, 2009
2: IT Risk Management Framework, University of Toronto, 2017
3: The Control Process | Principles of Management4
4: Control Management: What it is + Why It’s Essential | Adobe Workfront5
5: What is a Key Performance Indicator (KPI)? Guide & Examples - Qlik1
6: What is a Key Performance Indicator (KPI)? - KPI.org2
A business is conducting a proof of concept on a vendor’s AI technology. Which of the following is the MOST important consideration for managing risk?
Options:
Use of a non-production environment
Regular security updates
Third-party management plan
Adequate vendor support
Answer:
AExplanation:
Conducting a proof of concept in a non-production environment ensures that any potential issues or vulnerabilities in the AI technology do not affect live systems or data. This approach allows for thorough testing and evaluation without risking operational disruptions or data breaches.
Which of the following s MOST likely to deter an employee from engaging in inappropriate use of company owned IT systems?
Options:
A centralized computer security response team
Regular performance reviews and management check-ins
Code of ethics training for all employees
Communication of employee activity monitoring
Answer:
DExplanation:
Employee activity monitoring is the process of tracking and recording the actions and behaviors of employees on company owned IT systems, such as email, internet, applications, etc. Thepurpose of employee activity monitoring is to ensure compliance with the company’s policies and regulations, prevent data leakage and misuse, detect and deter inappropriate or malicious activities, and improve productivity and performance. The most likely way to deter an employee from engaging in inappropriate use of company owned IT systems is to communicate the employee activity monitoring policy and practice to the employees, and make them aware of the consequences of violating the policy. By doing so, the company can create a deterrent effect and discourage the employees from misusing the IT systems, as they know that their actions are being monitored and recorded, and that they will be held accountable for any misconduct. References = CRISC Review Manual, 7th Edition, page 181.
Which of the following is the MOST efficient method for monitoring control effectiveness?
Options:
Conduct control self-assessments (CSAs)
Review system performance logs
Compare controls to business metrics
Perform independent periodic control testing
Answer:
AExplanation:
Control Self-Assessments (CSAs)provide an efficient way for process owners and staff to assess control effectiveness continuously. ISACA recognizes CSAs as a proactive approach that encourages accountability and early detection of control weaknesses, reducing the need for frequent external testing.
===========
Which of the following provides the MOST useful information when assessing whether an organization has appropriately managed its level of risk compared to its established risk appetite?
Options:
Inherent risk
Risk velocity
Risk trend
Residual risk
Answer:
DExplanation:
The correct answer isDbecauseresidual riskis the remaining risk after controls and risk responses have been implemented, and it is the key measure used to determine whether the organization’s current level of risk is within its establishedrisk appetite. To assess whether risk has been appropriately managed, the organization must compare the remaining exposure, not the untreated exposure, against acceptable thresholds.
The other options are less appropriate:
A. Inherent riskrepresents risk before controls and therefore does not show whether risk has been appropriately managed.
B. Risk velocityindicates speed of impact, but not whether risk is within appetite.
C. Risk trendshows movement over time, but not the actual remaining exposure compared with appetite.
Exact Extracts supporting the answer:
“The most suitable output for justifying an information security program is considering residual risk in terms of acceptable risk.”
“The primary objective of a risk management program is to maintain residual risk at an acceptable level.”
“Residual risk is best reflected as risk remaining after the implementation of new or enhanced controls.”
“Acceptable risk for an enterprise is achieved when residual risk is within tolerance levels.”
“A successful risk management practice is indicated by minimizing residual risk.”
These extracts directly support thatresidual riskis the most useful information when comparing managed risk against established risk appetite.
===========
Which of the following BEST enables a risk practitioner to plan a vulnerability assessment that aligns to detailed organizational requirements?
Options:
Industry best practices
Standards
Policies
Procedures
Answer:
BExplanation:
========================================
Well-developed, data-driven risk measurements should be:
Options:
reflective of the lowest organizational level.
a data feed taken directly from operational production systems.
reported to management the same day data is collected.
focused on providing a forward-looking view.
Answer:
DExplanation:
Well-developed, data-driven risk measurements should be focused on providing a forward-looking view, as they enable the organization to anticipate and prepare for the potential changes and impacts of the risk level and exposure, and to take proactive and appropriate actions toaddress the risk. The other options are not the characteristics of well-developed, data-driven risk measurements, as they may not reflect the strategic, comprehensive, or timely aspects of the risk measurements, respectively. References = CRISC Review Manual, 7th Edition, page 110.
Which of the following is MOST helpful to ensure effective security controls for a cloud service provider?
Options:
A control self-assessment
A third-party security assessment report
Internal audit reports from the vendor
Service level agreement monitoring
Answer:
BExplanation:
A third-party security assessment report is the most helpful to ensure effective security controls for a cloud service provider, because it provides an independent and objective evaluation of the cloud provider’s security posture, policies, and practices. A third-party security assessment report can help to verify and validate the cloud provider’s compliance with the relevant standards, regulations, and best practices, such as ISO 27001, PCI DSS, NIST, or CSA. A third-party security assessment report can also help to identify and address any gaps, weaknesses, or vulnerabilities in the cloud provider’s security controls, and to provide recommendations and guidance for improvement. A third-party security assessment report can also help to increase the trust and confidence of the cloud customers, and to facilitate the due diligence and risk management processes. The other options are less helpful to ensure effective security controls for a cloud service provider. A control self-assessment is a process that enables the cloud provider to assess its own security controls, using a predefined framework or questionnaire. However, a control self-assessment may not be as reliable or comprehensive as a third-party security assessment report, as it may be biased, incomplete, or inaccurate, and it may not cover all the aspects or dimensions of security. Internal audit reports from the vendor are documents that provide the results and findings of the internal audits conducted by the cloud provider’s ownauditors, to verify and validate the effectiveness and efficiency of the securitycontrols. However, internal audit reports from the vendor may not be as credible or trustworthy as a third-party security assessment report, as they may be influenced by the cloud provider’s interests, objectives, or agenda, and they may not follow the same standards or criteria as the external auditors. Service level agreement monitoring is a process that measures and evaluates the performance and availability of the cloud services, based on the predefined metrics and targets agreed between the cloud provider and the cloud customer. However, service level agreement monitoring may not be sufficient or relevant to ensure effective security controls for a cloud service provider, as it may not address the security aspects or requirements of the cloud services, such as confidentiality, integrity, or accountability, and it may not reflect the actual security risks or incidents that may occur in the cloud environment. References = Cloud Security Controls: Key Elements and 4 Control Frameworks 1
What should a risk practitioner do FIRST when an assessment reveals a control is not operating as intended?
Options:
Recommend updates to the control procedures
Determine the root cause of the control issue.
Discuss the status with the control owner.
Recommend compensating controls.
Answer:
CWhich of the following is the BEST way to identify changes to the risk landscape?
Options:
Internal audit reports
Access reviews
Threat modeling
Root cause analysis
Answer:
CExplanation:
The risk landscape is the set of internal and external factors and conditions that may affect the organization’s objectives and operations, and create or influence the risks that the organization faces. The risk landscape is dynamic and complex, and it may change over time due to various drivers or events, such as technological innovations, market trends, regulatory changes, customer preferences, competitor actions, environmental issues, etc.
The best way to identify changes to the risk landscape is threat modeling, which is the process of identifying, analyzing, and prioritizing the potential threats or sources of harm that may exploit the vulnerabilities or weaknesses in the organization’s assets, processes, or systems, and cause adverse impacts or consequences for the organization. Threat modeling can help the organization to anticipate and prepare for the changes in the risk landscape, and to design and implement appropriate controls or countermeasures to mitigate or prevent the threats.
Threat modeling can be performed using various techniques, such as brainstorming, scenario analysis, attack trees, STRIDE, DREAD, etc. Threat modeling can also be integrated with the risk management process, and aligned with the organization’s objectives and risk appetite.
The other options are not the best ways to identify changes to the risk landscape, because they do not provide the same level of proactivity, comprehensiveness, and effectiveness of identifying and addressing the potential threats or sources of harm that may affect the organization.
Internal audit reports are the documents that provide the results and findings of the internal audits that are performed to assess and evaluate the adequacy and effectiveness of the organization’s governance, risk management, and control functions. Internal audit reports can provide useful information and recommendations on the current state and performance of the organization, and identify the issues or gaps that need to be addressed or improved, but they are not the best way to identify changes to the risk landscape, because they areusually retrospective and reactive, and they may not cover all the relevant or emerging threats or sources of harm that may affect the organization.
Access reviews are the processes of verifying and validating the access rights and privileges that are granted to the users or entities that interact with the organization’s assets, processes, orsystems, and ensuring that they are appropriate and authorized. Access reviews can provide useful information and feedback on the security and compliance of the organization’s access management, and identify and revoke any unauthorized or unnecessary access rights or privileges, but they are not the best way to identify changes to the risk landscape, because they are usually periodic and specific, and they may not cover all the relevant or emerging threats or sources of harm that may affect the organization.
Root cause analysis is the process of identifying and understanding the underlying or fundamental causes or factors that contribute to or result in a problem or incident that has occurred or may occur in the organization. Root cause analysis can provide useful insights and solutions on the origin and nature of the problem or incident, and prevent or reduce its recurrence or impact, but it is not the best way to identify changes to the risk landscape, because it is usually retrospective and reactive, and it may not cover all the relevant or emerging threats or sources of harm that may affect the organization. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 19-20, 23-24, 27-28, 31-32, 40-41, 47-48, 54-55, 58-59, 62-63
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 167
CRISC Practice Quiz and Exam Prep
Which of the following is the PRIMARY benefit of consistently recording risk assessment results in the risk register?
Options:
Assessment of organizational risk appetite
Compliance with best practice
Accountability for loss events
Accuracy of risk profiles
Answer:
DExplanation:
A risk profile is a summary of the risks that an organization faces and their likelihood and impact. Consistently recording risk assessment results in the risk register can help improve the accuracy of risk profiles by providing a reliable and up-to-date source of information on the current risk situation, the risk response actions, and the residual risk levels. A risk register is a tool that captures and documents the risk identification, analysis, evaluation, and treatment processes2. A risk register can also facilitate risk communication, monitoring, and reporting2.
Assessment of organizational risk appetite, compliance with best practice, and accountability for loss events are not the primary benefits of consistently recording risk assessment results in the risk register. These are possible outcomes or objectives of risk management, but they do not directly depend on the risk register.
Which of the following is the BEST way to address IT regulatory compliance risk?
Options:
Assign highest priority to remediation of related risk scenarios.
Prevent acceptance of related risk scenarios.
Conduct specialized business impact analyses (BIAs).
Manage risk like other types of operational risk.
Answer:
DExplanation:
Managing IT regulatory compliance risk in the same manner as other operational risks ensures a consistent and integrated approach to risk management. This involves identifying, assessing, mitigating, and monitoring compliance risks using the organization ' s established risk management framework. Such an approach promotes efficiency and ensures that compliance risks are not siloed but are considered within the broader context of enterprise risk management.
Which of the following is the MOST comprehensive resource for prioritizing the implementation of information systems controls?
Options:
Data classification policy
Emerging technology trends
The IT strategic plan
The risk register
Answer:
DExplanation:
The most comprehensive resource for prioritizing the implementation of information systems controls is the risk register. The risk register is a document that records the identified risks, their analysis, and their responses. The risk register provides a holistic and systematic view of the risk profile and the risk treatment of the organization. The risk register can help to prioritize the implementation of information systems controls by providing the information on the likelihood, impact, and exposure of the risks, the effectiveness and efficiency of the controls, and the gaps or issues of the control environment. The other options are not as comprehensive as the risk register, as they are related to the specific aspects or components of the information systems controls, not the overall assessment and evaluation of the information systems controls. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.4: IT Risk Response, page 87.
The PRIMARY objective for selecting risk response options is to:
Options:
reduce risk 10 an acceptable level.
identify compensating controls.
minimize residual risk.
reduce risk factors.
Answer:
AExplanation:
The primary objective for selecting risk response options is to reduce risk to an acceptable level. Risk response options are the possible actions that can be taken to address the risks that have been identified and analyzed in the risk management process. Risk response options can be classified into four categories: avoid, transfer, mitigate, and accept for negative risks (or threats), and exploit, share, enhance, and accept for positive risks (or opportunities). The selection of the risk response options depends on various factors, such as the risk level, the risk appetite and tolerance, the cost and benefit, and the feasibility and availability of the options. The main goal of selecting the risk response options is to reduce the risk to a level that is acceptable to the organization, which means that the risk exposure is within the boundaries of the risk criteria and the risk appetite. The other options are not the primary objective for selecting risk response options, although they may be related or beneficial. Identifying compensating controls is a technique to implement additional or alternative controls when the existing controls are not effective or sufficient to reduce the risk to an acceptable level. Minimizing residual risk is a result of selecting and implementing the risk response options, but it is not the main purpose. Residual risk is the risk that remains after the risk response, and it may or may not be acceptable depending on the risk appetite and tolerance. Reducing risk factors is a method to decrease the likelihood or impact of the risk by addressing the root causes or sources of the risk. However,reducing risk factors does not necessarily mean that the risk is reduced to an acceptable level,as there may be other factors or uncertainties that affect the risk. References = CRISC Review Manual, pages 32-331; CRISC Review Questions, Answers & Explanations Manual, page 862
Which of the following would be MOST useful to management when allocating resources to mitigate risk to the organization?
Options:
Risk assessments
Control self-assessments (CSAs)
Risk-based audits
Vulnerability analysis
Answer:
AExplanation:
Risk assessmentsprovide a prioritized view of potential threats, their likelihood, and impact. This enables management tofocus resourceson high-priority risks, ensuring cost-effective mitigation aligned with organizational goals.
A risk practitioner has identified that the organization ' s secondary data center does not provide redundancy for a critical application. Who should have the authority to accept the associated risk?
Options:
Business continuity director
Disaster recovery manager
Business application owner
Data center manager
Answer:
CExplanation:
The business application owner should have the authority to accept the associated risk, because they are responsible for the performance and outcomes of the critical application, and they understand the business requirements, expectations, and impact of the application. The business application owner can also evaluate the trade-offs between the potential benefits and costs of the application, and the potential risks and consequences of a disruption or failure of the application. The business application owner can also communicate and justify their risk acceptance decision to the senior management and other stakeholders, and ensure that the risk is monitored and reviewed regularly. The other options are less appropriate to have the authority to accept the associated risk. The business continuity director is responsible for overseeing the planning and execution of the business continuity strategy, which includes ensuring the availability andresilience of the critical business processes and applications. However, they are not the owner of the application, and they may not have the full knowledge or authority to accept the risk on behalf of the business. The disaster recovery manager is responsible for managing the recovery and restoration of the IT systems and applications in the event of a disaster or disruption. However, they are not the owner of the application, and they may not have the full knowledge or authority to accept the risk on behalf of the business. The data center manager is responsible for managing the operation and maintenance of the data center infrastructure, which includes providing the physical and environmental security, power, cooling, and network connectivity for the IT systems and applications. However, they are not the owner of the application, and they may not have the full knowledge or authority to accept the risk on behalf of the business. References = Risk IT Framework, ISACA, 2022, p. 181
Which of the following presents the GREATEST challenge to managing an organization ' s end-user devices?
Options:
Incomplete end-user device inventory
Unsupported end-user applications
Incompatible end-user devices
Multiple end-user device models
Answer:
BWhich of the following would MOST effectively reduce the potential for inappropriate exposure of vulnerabilities documented in an organization ' s risk register?
Options:
Limit access to senior management only.
Encrypt the risk register.
Implement role-based access.
Require users to sign a confidentiality agreement.
Answer:
CExplanation:
A risk register is a document that contains information about potential cybersecurity risks that could threaten a project’s success, or even the business itself2. Therefore, it is important to protect the confidentiality and integrity of the risk register from unauthorized or inappropriate access, modification, or disclosure. One way to do this is to implement role-based access, which is a method of restricting access to the risk register based on the roles or responsibilities of the users1. This way, only authorized users who need to view or edit the risk register for legitimate purposes can do so, and the access rights can be revoked or modified as needed. This would most effectively reduce the potential for inappropriate exposure of vulnerabilities documented in the risk register. The other options are not as effective or feasible as option C, as they do not address the need to balance the security and availability of the risk register. Option A, limiting access to senior management only, would compromise the availability and usefulness of the risk register, as other stakeholders such as project managers, risk owners, or auditors may need to access therisk register for risk identification, analysis, response, or monitoring purposes3. Option B, encrypting the risk register, would enhance the security of the risk register, but it would not prevent authorized users from exposing the vulnerabilities to unauthorized parties, either intentionally or unintentionally. Encryption also adds complexity and cost to the risk register management process, and may affect the performance or usability of the risk register4. Option D, requiring users to sign a confidentiality agreement, would rely on the compliance and ethics of the users, but it would not prevent or detect any breaches of the agreement. A confidentiality agreement also does not specify the access rights or roles of the users, and may not be legally enforceable in some cases5.
One of an organization ' s key IT systems cannot be patched because the patches interfere with critical business application functionalities. Which of the following would be the risk practitioner ' s BEST recommendation?
Options:
Additional mitigating controls should be identified.
The system should not be used until the application is changed
The organization ' s IT risk appetite should be adjusted.
The associated IT risk should be accepted by management.
Answer:
AExplanation:
The risk practitioner’s best recommendation when one of an organization’s key IT systems cannot be patched because the patches interfere with critical business application functionalities is to identify additional mitigating controls, as they may reduce the likelihood or impact of the vulnerabilities being exploited, and align the residual risk with the risk tolerance and appetite of the organization. The other options are not the best recommendations, as they may not address the risk adequately, or may introduce unacceptable consequences, such as disrupting the businessoperations, changing the risk strategy, or accepting excessive risk. References = CRISC Review Manual, 7th Edition, page 111.
Which of the following is the MOST important consideration when sharing risk management updates with executive management?
Options:
Including trend analysis of risk metrics
Using an aggregated view of organizational risk
Relying on key risk indicator (KRI) data
Ensuring relevance to organizational goals
Answer:
DExplanation:
The most important consideration when sharing risk management updates with executive management is ensuring relevance to organizational goals. This means that the risk information presented should align with the strategic objectives and priorities of the organization, and demonstrate how risk management supports the achievement of those goals. Executive management is responsible for setting the direction and vision of the organization, and therefore needs to understand how risk management contributes to the value creation and protection of the organization. By ensuring relevance to organizational goals, risk management updates can help executive management make informed decisions, allocate resources, and communicate with stakeholders.
Some of the ways to ensure relevance to organizational goals are:
Linking risk management updates to the organization’s mission, vision, values, and strategy
Highlighting the key risks and opportunities that affect the organization’s performance and competitiveness
Providing clear and concise risk reports that focus on the most critical and material risks
Using a common risk language and framework that is understood by executive management
Providing actionable recommendations and solutions to address the identified risks
Aligning risk management updates with the organization’s reporting cycle and governance structure
References =
The Importance of Integrating Risk Management with Strategy
Four steps for managing risk at the CEO level
5 Key Principles of Successful Risk Management
Which of the following would BEST facilitate the implementation of data classification requirements?
Options:
Assigning a data owner
Implementing technical control over the assets
Implementing a data loss prevention (DLP) solution
Scheduling periodic audits
Answer:
AExplanation:
Assigning a data owner would best facilitate the implementation of data classification requirements. A data owner is responsible for defining the classification of the data, ensuring that the data is properly labeled, and approving access requests. Implementing technical control over the assets, implementing a data loss prevention (DLP) solution, and scheduling periodic audits are important activities, but they are not as effective as assigning a data owner. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 8; CRISC Review Manual, 6th Edition, page 97.
Identifying which of the following would BEST help an organization define an IT asset ' s criticality?
Options:
Data classification policy
Number of business users
The asset ' s end of life status
Business processes
Answer:
DExplanation:
CRISC suggests that asset criticality is determined by thebusiness processes and services the asset enables, and the impact if those processes are disrupted. By mapping IT assets to business processes, the organization can understand which systems support revenue generation, regulatory compliance, safety, or other critical outcomes. The data classification policy helps assess data sensitivity (confidentiality), which is related but not sufficient by itself to determine overall criticality; availability and integrity requirements also matter. The number of business users may indicate importance, but some highly critical systems (e.g., settlement engines, control systems) may have few users yet enormous impact. End-of-life status is relevant for obsolescence risk but does not necessarily correlate with business criticality. Therefore, linking assets to the processes they support is the most reliable basis for defining criticality.
Which of the following is the BEST way to help ensure risk will be managed properly after a business process has been re-engineered?
Options:
Reassessing control effectiveness of the process
Conducting a post-implementation review to determine lessons learned
Reporting key performance indicators (KPIs) for core processes
Establishing escalation procedures for anomaly events
Answer:
AExplanation:
Business process re-engineering is the radical redesign of a business process to achieve significant improvements in performance, quality, cost, or customer satisfaction. Business process re-engineering can introduce new or modified risks to the organization, as well as affectthe existing controls and responses. Therefore, the best way to help ensure risk will be managed properly after a business process has been re-engineered is to reassess the control effectiveness of the process, meaning that the organization should evaluate whether the controls are still adequate, appropriate, and functioning as intended to mitigate the risks. Reassessing the control effectiveness can help to identify any gaps or weaknesses in the control environment, as well as to implement any necessary changes or improvements to the controls. References = Risk and Information Systems Control Study Manual, Chapter 5, Section 5.2.2, p. 229-230
Who is MOST appropriate to be assigned ownership of a control
Options:
The individual responsible for control operation
The individual informed of the control effectiveness
The individual responsible for resting the control
The individual accountable for monitoring control effectiveness
Answer:
DExplanation:
A control is a measure or action that is implemented to reduce the likelihood or impact of a risk event, or to enhance the benefits or opportunities of a risk event. A control owner is a person who is assigned the responsibility and authority for the design, implementation, operation, and maintenance of a control. The most appropriate person to be assigned ownership of a control is the individual accountable for monitoring control effectiveness, which is the process of measuring and evaluating the performance and compliance of the control. By assigning the control ownership to the individual accountable for monitoring control effectiveness, the organization can ensure that the control is aligned with the risk objectives, operates as intended, and delivers the expected results. References = 4
Which of the following is MOST important to consider when determining a recovery time objective (RTO)?
Options:
Time between backups for critical data
Sensitivity of business data involved
Cost of downtime due to a disaster
Maximum tolerable data loss after an incident
Answer:
CExplanation:
The Recovery Time Objective (RTO) is the maximum acceptable length of time that a system can be down after a failure or disaster. Determining the RTO involves assessing the cost of downtime and its impact on business operations to ensure that recovery strategies are cost-effective and aligned with business needs.
An organization has contracted with a cloud service provider to support the deployment of a new product. Of the following, who should own the associated risk?
Options:
The head of enterprise architecture (EA)
The IT risk manager
The information security manager
The product owner
Answer:
DExplanation:
The product owner should own the associated risk when contracting with a cloud service provider to support the deployment of a new product. The product owner is the person who has the authority and responsibility for defining the product vision, requirements, and priorities. The product owner also has the accountability for the business value and outcomes of the product. Therefore, the product owner should be the one who identifies, assesses, and manages the risks related to the cloud service provider, such as security, compliance, performance, and quality. The product owner should also collaborate with the other stakeholders, such as the head of EA, the IT risk manager, and the information security manager, to ensure that the cloud service provider meets the organization’s standards and expectations. References = Risk and Information Systems Control Study Manual, Chapter 5: IT Risk Mitigation, Section 5.3: IT Risk Mitigation Strategies and Approaches, Page 254; Best Practices to Manage Risks in the Cloud - ISACA.
An organization has restructured its business processes, and the business continuity plan (BCP) needs to be revised accordingly. Which of the following should be identified FIRST?
Options:
Variances in recovery times
Ownership assignment for controls
New potentially disruptive scenarios
Contractual changes with customers
Answer:
CExplanation:
When an organization restructures its business processes, the first step in revising the BCP is to identify new potentially disruptive scenarios that may affect the continuity of the critical functions and processes. This can be done by conducting a risk assessment or a business impact analysis (BIA) to determine the likelihood and impact of various threats and vulnerabilities onthe organization’s objectives and operations. By identifying new potentially disruptive scenarios, the organization can then update its recovery strategies, objectives, and plans accordingly.
Which of the following controls would BEST mitigate the risk of user passwords being compromised by a man in the middle technique?
Options:
Require users to select long passwords.
Implement a passwordless access mechanism.
Require users to change password as frequently as possible.
Block user sessions after short periods of inactivity.
Answer:
CWhich of the following process controls BEST mitigates the risk of an employee issuing fraudulent payments to a vendor?
Options:
Performing credit verification of third-party vendors prior to payment
Conducting system access reviews to ensure least privilege and appropriate access
Performing regular reconciliation of payments to the check registers
Enforcing segregation of duties between the vendor master file and invoicing
Answer:
DExplanation:
Enforcing segregation of duties between the vendor master file and invoicing is the best process control to mitigate the risk of an employee issuing fraudulent payments to a vendor. This is because segregation of duties is a key internal control that prevents or detects errors, fraud, orabuse by ensuring that no single person can perform incompatible or conflicting tasks. The vendor master file is a database that contains the information and settings for each vendor, such as name, address, bank account, payment terms, etc. Invoicing is the process of generating and sending bills to the vendors for the goods or services they provide. If the same person can access and modify the vendor master file and issue invoices, he or she could create fictitious vendors, alter vendor information, or generate false or duplicate invoices, and then divert the payments to his or her own account. By segregating these duties, the organization can reduce the opportunity and likelihood of such fraudulent activities. According to the CRISC Review Manual 2022, segregation of duties is one of the key IT control objectives and practices1. According to the web search results, segregation of duties between the vendor master file and invoicing is a common and recommended control to prevent vendor fraud
Which of the following BEST provides an early warning that network access of terminated employees is not being revoked in accordance with the service level agreement (SLA)?
Options:
Updating multi-factor authentication
Monitoring key access control performance indicators
Analyzing access control logs for suspicious activity
Revising the service level agreement (SLA)
Answer:
BExplanation:
According to the CRISC Review Manual (Digital Version), monitoring key access control performance indicators is the best way to provide an early warning that network access of terminated employees is not being revoked in accordance with the service level agreement (SLA), as it measures the effectiveness and efficiency of the access control process and its alignment with the SLA objectives and requirements. The SLA is a contract that defines the expectations and responsibilities of the service provider and the service recipient in terms of the quality, availability, and scope of the service. Monitoring key access control performance indicators helps to:
Evaluate the extent to which the access control process has met the SLA targets and standards
Identify and report any deviations, errors, or breaches in the access control process and its compliance with the SLA
Recommend and implement corrective actions or improvement measures to address the issues or findings in the access control process
Communicate and coordinate the monitoring results and recommendations with the relevant stakeholders, such as the service provider, the service recipient, and the senior management
References = CRISC Review Manual (Digital Version), Chapter 4: IT Risk Monitoring and Reporting, Section 4.1: IT Risk Monitoring, pp. 217-2181
A risk owner should be the person accountable for:
Options:
the risk management process
managing controls.
implementing actions.
the business process.
Answer:
DExplanation:
A risk owner should be the person accountable for the business process that is affected by the risk, as they have the authority, responsibility, and knowledge to manage the risk effectively. The risk owner should collaborate with the risk practitioner, who facilitates the risk management process, and the risk action owners, who implement the risk response actions. The risk owner should also ensure that the controls are adequate and functioning properly to mitigate the risk. The other options are not the best description of what a risk owner should be accountable for, as they are either too broad (the risk management process), too narrow (managing controls or implementing actions), or not directly related to the risk (the businessprocess). References = Why Assigning a Risk Owner is Important and How to Do It Right; Definition of Risk Owner; What Is a Risk Owner in Project Management?
An organization has asked an IT risk practitioner to conduct an operational risk assessment on an initiative to outsource the organization ' s customer service operations overseas. Which of the following would MOST significantly impact management ' s decision?
Options:
Time zone difference of the outsourcing location
Ongoing financial viability of the outsourcing company
Cross-border information transfer restrictions in the outsourcing country
Historical network latency between the organization and outsourcing location
Answer:
CExplanation:
The most significant factor that would impact management’s decision when conducting an operational risk assessment on an initiative to outsource the organization’s customer service operations overseas is the cross-border information transfer restrictions in the outsourcing country. Cross-border information transfer restrictions are the laws, regulations, standards, or contracts that govern the collection, processing, storage, or transmission of information across national or regional boundaries. Cross-border information transfer restrictions may affect the organization’s outsourcing initiative, because they may impose limitations, obligations, or penalties on the organization or the outsourcing company, such as requiring consent, notification, or authorization, or prohibiting or restricting certain types or categories of information. Cross-border information transfer restrictions may also create challenges or risks for the organization’s outsourcing initiative, such as compliance, legal, reputational, or operational risks, or conflicts orinconsistencies with the organization’s own policies, regulations, standards, or contracts. The other options are not as significant as the cross-border information transfer restrictions, although they may also pose some difficulties or limitations for the organization’s outsourcing initiative. Time zone difference of the outsourcing location, ongoing financial viability of the outsourcing company, and historical network latency between the organization and outsourcing location are all factors that could affect the efficiency and effectiveness of the outsourcing initiative, but they do not directly affect the legality or security of the outsourcing initiative. References = 3
Which of the following is MOST effective in continuous risk management process improvement?
Options:
Periodic assessments
Change management
Awareness training
Policy updates
Answer:
AExplanation:
Continuous risk management process improvement is the practice of evaluating and enhancing the risk management process on a regular basis, to ensure that it is effective, efficient, and aligned with the business objectives and strategy. Continuous risk management processimprovement can help identify and address the gaps, weaknesses, or opportunities for improvement in the risk management process, and ensure that the process is responsive and adaptable to the changing risk environment. The most effective method for continuous risk management process improvement is periodic assessments, which are systematic and objective evaluations of the risk management process, performed at predefined intervals or after significant events. Periodic assessments can help measure and monitor the performance and maturity of the risk management process, using criteria such as the risk management framework, standards, policies, procedures, methods, tools, roles, responsibilities, and results. Periodic assessments can also help identify and analyze the strengths, weaknesses, threats, and opportunities of the risk management process, and provide feedback and recommendations for improvement. Periodic assessments can also help communicate and report the status and progress of the risk management process to the stakeholders, and obtain their input and support for improvement actions. References = Continuous Risk Management Guidebook, p. 7-8, ISO 31000: riskmanagement and its continuous improvement, How Continuous Monitoring Drives Risk Management.
The BEST way to improve a risk register is to ensure the register:
Options:
is updated based upon significant events.
documents possible countermeasures.
contains the risk assessment completion date.
is regularly audited.
Answer:
AExplanation:
A risk register is a tool that records and tracks the identified risks, their causes, impacts, probabilities, responses, and owners. It is a living document that should be updated regularly to reflect the changes in therisk environment and the status of the risk responses12. The best way to improve a risk register is to ensure that it is updated based upon significant events, such as:
New risks are identified or existing risks are eliminated
Risk probabilities or impacts change due to internal or external factors
Risk responses are implemented or modified
Risk owners or stakeholders change
Risk incidents or issues occur
Risk thresholds or appetite change
Risk reporting or communication requirements change
Updating the risk register based upon significant events can help to:
Maintain the accuracy and relevance of the risk information
Enhance the risk awareness and accountability of the risk owners and stakeholders
Support the risk monitoring and reporting activities
Facilitate the risk evaluation and decision-making processes
Improve the risk management performance and maturity
References =
Risk Register - Project Management Knowledge
How to Create a Risk Register: A Step-by-Step Guide - ProjectManager.com
To mitigate the risk of using a spreadsheet to analyze financial data, IT has engaged a third-party vendor to deploy a standard application to automate the process. Which of the following parties should own the risk associated with calculation errors?
Options:
business owner
IT department
Risk manager
Third-party provider
Answer:
AExplanation:
According to the CRISC Review Manual1, the business owner is the person who has the authority and accountability for the achievement of the business objectives and the managementof the associated risks. The business owner is ultimately responsible for ensuring that the IT services and solutions support the business needs and goals, and for accepting or rejecting the residual risks after the implementation of risk responses. Therefore, the business owner should own the risk associated with calculation errors, as they are the ones who will be affected by the potential impact of the errors on the financial data and decisions. References = CRISC Review Manual1, page 194.
Which of the following provides The MOST useful information when determining a risk management program ' s maturity level?
Options:
Risk assessment results
A recently reviewed risk register
Key performance indicators (KPIs)
The organization ' s risk framework
Answer:
CExplanation:
Key performance indicators (KPIs) are measurable values that demonstrate how effectively an organization is achieving its key objectives. KPIs can be used to evaluate the progress and performance of a risk management program, as well as to identify the areas for improvement and alignment with the organization’s strategy. KPIs can provide the most useful information when determining a risk management program’s maturity level, because they can reflect the extent to which the program is integrated, consistent, proactive, and value-adding. KPIs can also be compared with industry benchmarks or best practices to assess the program’s maturity level relative to other organizations. The other options are not as useful as KPIs, because they do not provide a clear and comprehensive picture of the risk management program’s maturity level, but rather focus on specific aspects or outputs of the program. References = Risk and Information Systems Control Study Manual, Chapter 1, Section 1.3.2, page 18.
Which of the following should be the HIGHEST priority when developing a risk response?
Options:
The risk response addresses the risk with a holistic view.
The risk response is based on a cost-benefit analysis.
The risk response is accounted for in the budget.
The risk response aligns with the organization ' s risk appetite.
Answer:
DExplanation:
A risk response is the action or plan that is taken to address a specific risk that has been identified, analyzed, and evaluated. It can be one of the following types: mitigate, transfer, avoid, or accept.
The highest priority when developing a risk response is to ensure that it aligns with the organization’s risk appetite, which is the amount and type of risk that the organization is willing to accept in pursuit of its goals. The risk appetite is usually expressed as a range or a threshold, and it is aligned with the organization’s strategy and culture.
Aligning the risk response with the organization’s risk appetite ensures that the risk response is consistent, appropriate, and proportional to the level and nature of the risk, and that it supports the organization’s objectives and values. It also helps to optimize the balance between risk and return, and to create and protect value for the organization and its stakeholders.
The other options are not the highest priority when developing a risk response, because they do not address the fundamental question of whether the risk response is suitable and acceptable for the organization.
The risk response addresses the risk with a holistic view means that the risk response considers the interrelationships and dependencies among the risk sources, events, impacts, and responses, and the potential secondary and residual effects of the risk response. This is important to ensure that the risk response is comprehensive and effective, and that it does not create new or unintended risks, but it is not the highest priority when developing a risk response, because it does not indicate whether the risk response is aligned with the organization’s risk appetite.
The risk response is based on a cost-benefit analysis means that the risk response compares the expected costs and benefits of implementing the risk response, and selects the risk response that provides the most favorable net outcome. This is important to ensure that the risk response is efficient and economical, and that it maximizes the return on investment, but it is not the highest priority when developing a risk response, because it does not indicate whether the risk response is aligned with the organization’s risk appetite.
The risk response is accounted for in the budget means that the risk response is included in the financial plan and allocation of resources for the organization or the project. This is important toensure that the risk response is feasible and realistic, and that it has the necessary funding and support, but it is not the highest priority when developing a risk response, because it does not indicate whether the risk response is aligned with the organization’s risk appetite. References =
ISACA, CRISC Review Manual, 7th Edition, 2022, pp. 29-30, 34-35, 38-39, 44-45, 50-51, 54-55
ISACA, CRISC Review Questions, Answers & Explanations Database, 2022, QID 147
A risk assessment has revealed that the probability of a successful cybersecurity attack is increasing. The potential loss could exceed the organization ' s risk appetite. Which of the following ould be the MOST effective course of action?
Options:
Re-evaluate the organization ' s risk appetite.
Outsource the cybersecurity function.
Purchase cybersecurity insurance.
Review cybersecurity incident response procedures.
Answer:
DExplanation:
Cybersecurity incident response procedures are the plans and actions that an organization takes to respond to and recover from a cybersecurity attack. They include identifying the source and scope of the attack, containing and eradicating the threat, restoring normal operations, and analyzing the root cause and lessons learned. Reviewing cybersecurity incident response procedures is the most effective course of action when the probability of a successful cybersecurity attack is increasing and the potential loss could exceed the organization’s risk appetite, as it helps to prepare the organization for minimizing the impact and duration of the attack, as well as improving the resilience and security posture of the organization.
The risk associated with an asset after controls are applied can be expressed as:
Options:
a function of the cost and effectiveness of controls.
the likelihood of a given threat.
a function of the likelihood and impact.
the magnitude of an impact.
Answer:
CExplanation:
The risk associated with an asset after controls are applied can be expressed as a function of the likelihood and impact, as it helps to measure and quantify the residual risk level and exposure. Residual risk is the risk that remains after the implementation of controls or risk treatments. Residual risk can be calculated by multiplying the likelihood and impact of a risk event, where likelihood is the probability or frequency of the risk event occurring, and impact is the consequence or severity of the risk event on the asset or objective. Residual risk can be expressed as:
ResidualRisk=Likelihood×Impact
Expressing the risk associated with an asset after controls are applied as a function of the likelihood and impact helps to provide the following benefits:
It enables a data-driven and evidence-based approach to risk assessment and reporting, rather than relying on subjective or qualitative judgments.
It facilitates a consistent and standardized way of measuring and communicating risk levels and exposure across the organization and to the external stakeholders.
It supports the alignment of risk management and control activities with the organizational strategy and objectives, and helps to evaluate the achievement of the desired outcomes.
It helps to identify and prioritize the areas for improvement and enhancement of the risk management and control processes, and guide the development and implementation of corrective or preventive actions.
It provides feedback and learning opportunities for the risk management and control processes, and helps to foster a culture of continuous improvement and innovation.
The other options are not the best ways to express the risk associated with an asset after controls are applied. A function of the cost and effectiveness of controls is a measure of the inputs or outputs of therisk management and control processes, but it does not indicate the risk level or exposure. The likelihood of a given threat is a component of the risk calculation, but it does not reflect the impact or consequence of the threat. The magnitude of an impact is a component of the risk calculation, but it does not reflect the likelihood or probability of the risk event.References=Risk Assessment and Analysis Methods: Qualitative and Quantitative,IT Risk Resources | ISACA,Residual Risk: Definition, Formula & Management - Video & Lesson …
A risk practitioner learns of an urgent threat intelligence alert to patch a critical vulnerability identified in the organization ' s operating system. Which of the following should the risk practitioner do FIRST?
Options:
Patch the operating system immediately
Determine whether any active attacks are exploiting the vulnerability
Invoke the organization ' s incident response plan
Evaluate the threat in the context of the organization ' s IT environment
Answer:
DExplanation:
Before acting, the risk practitioner mustevaluate the threat in the organizational context. This includes checking system exposure, current mitigations, and potential business impact. Only then can an informed decision (such as patching or mitigation) be made.
Which of the following should be the PRIMARY input to determine risk tolerance?
Options:
Regulatory requirements
Organizational objectives
Annual loss expectancy (ALE)
Risk management costs
Answer:
BExplanation:
Organizational objectives should be the primary input to determine risk tolerance, as they define the desired outcomes and performance of the organization, and guide the selection of the acceptable level of risk that the organization is willing to take to achieve those objectives. Regulatory requirements, annual loss expectancy (ALE), and risk management costs are not the primary inputs, as they are more related to the external or internal constraints or factors that affect the risk tolerance, rather than the drivers or determinants of the risk tolerance. References = CRISC Review Manual, 7th Edition, page 109.
Which of the following is a risk practitioner ' s MOST important course of action after learning that an organization ' s industry peers have experienced an increase in ransomware attacks?
Options:
Recommend additional preventive controls to reduce residual risk.
Document this scenario as a risk event for further risk analysis.
Propose risk acceptance until the organization is directly affected.
Raise a security incident to proactively prevent similar attacks.
Answer:
AWhich of the following is the PRIMARY purpose for ensuring senior management understands the organization’s risk universe in relation to the IT risk management program?
Options:
To define effective enterprise IT risk appetite and tolerance levels
To execute the IT risk management strategy in support of business objectives
To establish business-aligned IT risk management organizational structures
To assess the capabilities and maturity of the organization’s IT risk management efforts
Answer:
AExplanation:
Ensuring senior management understands the organization’s risk universe in relation to the IT risk management program is primarily to define effective enterprise IT risk appetite andtolerance levels. This understanding is essential for setting the boundaries within which the organization is willing to operate regarding IT risks.
Defining Effective IT Risk Appetite and Tolerance Levels (Answer A):
Purpose: Senior management needs to understand the range and nature of IT risks to set appropriate risk appetite and tolerance levels.
Impact: This enables the organization to make informed decisions about which risks to accept, mitigate, transfer, or avoid.
Alignment: It ensures that the IT risk management strategy is aligned with the overall business objectives and risk posture of the organization.
Comparison with Other Options:
B. To execute the IT risk management strategy in support of business objectives:
Purpose: While important, it follows the definition of risk appetite and tolerance.
Limitation: Without understanding the risk universe, execution may be misaligned.
C. To establish business-aligned IT risk management organizational structures:
Purpose: Structural alignment is crucial but secondary to setting risk appetite and tolerance.
D. To assess the capabilities and maturity of the organization’s IT risk management efforts:
Purpose: This is part of the ongoing process but not the primary purpose of understanding the risk universe.
A business manager wants to leverage an existing approved vendor solution from another area within the organization. Which of the following is the risk practitioner ' s BEST course of action?
Options:
Recommend allowing the new usage based on prior approval.
Request a new third-party review.
Request revalidation of the original use case.
Assess the risk associated with the new use case.
Answer:
DExplanation:
A risk practitioner’s best course of action when a business manager wants to leverage an existing approved vendor solution from another area within the organization is to assess the risk associated with the new use case. This is because the new use case may introduce different or additional risks that were not considered or addressed in the original approval. For example, the new use case may involve different data types, volumes, or sensitivities; different business processes, functions, or objectives; different regulatory or contractual requirements; or different technical or operational dependencies. Therefore, the risk practitioner should perform a vendor risk assessment (VRA) to identify, evaluate, and mitigate the potential risks of the new use case and ensure that the vendor solution meets the organization’s riskappetite and tolerance12. Recommending allowing the new usage based on prior approval is not the best course of action, as it may overlook or underestimate the risks of the new use case and expose the organization to unacceptable levels of risk. Requesting a new third-party review is not the best course of action,as it may be unnecessary or redundant if the vendor solution has already been reviewed and approved for another use case within the organization. Requesting revalidation of the original use case is not the best course of action, as it may not address the specific risks of the new use case and may also delay or disrupt the existing use case. References = Risk and Information SystemsControl Study Manual, Chapter 4: Risk and Control Monitoring and Reporting, Section 4.2: Risk Monitoring, pp. 189-191.
To minimize the risk of a potential acquisition being exposed externally, an organization has selected a few key employees to be engaged in the due diligence process. A member of the due diligence team realizes a close acquaintance is a high-ranking IT professional at a subsidiary of the company about to be acquired. What is the BEST course of action for this team member?
Options:
Enforce segregation of duties.
Disclose potential conflicts of interest.
Delegate responsibilities involving the acquaintance.
Notify the subsidiary ' s legal team.
Answer:
BExplanation:
A conflict of interest is a situation where a person’s personal or professional interests may interfere with their ability to act in the best interest of the organization or the project1. A conflict of interest can compromise the integrity, objectivity, and impartiality of the person, and create ethical or legal issues for the organization or the project2. In the context of due diligence, a conflict of interest can affect the quality and reliability of the information and analysis, and jeopardize the success and confidentiality of the acquisition3.
The best course of action for a member of the due diligence team who realizes a close acquaintance is a high-ranking IT professional at a subsidiary of the company about to be acquired is to disclose potential conflicts of interest. This means that the team member should inform the due diligence leader and the organization’s management about the relationship with the acquaintance, and explain how it may affect their role or responsibility in the due diligence process. By disclosing potential conflicts of interest, the team member can:
Demonstrate honesty and transparency, and uphold the ethical standards and values of the organization and the project4.
Enable the due diligence leader and the organization’s management to assess the situation and decide the appropriate course of action, such as reassigning the team member, implementing additional controls or safeguards, or obtaining consent or approval from the relevant parties5.
Avoid or minimize the negative consequences or risks that may arise from the conflict of interest, such as legal liability, reputational damage, or loss of trust and credibility6.
References =
Conflict of Interest - CIO Wiki
What is a Conflict of Interest? Give Me Some Examples - The Balance Careers
How to Avoid Conflicts of Interest in M & A Transactions - DealRoom
How to Handle Conflicts of Interest - Harvard Business Review
Conflict of Interest Policy - ISACA
Managing Conflicts of Interest in the Public Sector Toolkit - OECD
Which of the following is the MOST important consideration when implementing ethical remote work monitoring?
Options:
Monitoring is only conducted between official hours of business
Employees are informed of how they are bong monitored
Reporting on nonproductive employees is sent to management on a scheduled basis
Multiple data monitoring sources are integrated into security incident response procedures
Answer:
BExplanation:
The most important consideration when implementing ethical remote work monitoring is to inform the employees of how they are being monitored, because this respects their privacy rights and expectations, and ensures their consent and compliance with the monitoring policy. Informing the employees of how they are being monitored also helps to build trust and transparency between the employer and the employees, and reduces the potential legal or ethical issues that may arise from the monitoring activities. The other options are not the most important considerations, although they may also be relevant for ethical remote work monitoring. Monitoring only during official hours of business, reporting on nonproductive employees to management, and integrating multiple data monitoring sources into security incident response procedures are examples of operational or technical aspects of remote work monitoring,notethical aspects. References = CRISC: Certified in Risk & Information Systems Control Sample Questions
Options:
Accept the residual risk due to the low likelihood of occurrence.
Implement additional mitigation measures.
Determine whether residual risk is within risk appetite.
Adopt a new risk assessment method to avoid the residual risk.
Answer:
CExplanation:
When a risk treatment plan does not reduce residual risk as expected, the immediate next step is to evaluate whether the current level of residual risk remains within the organization ' s defined risk appetite. If the residual risk is acceptable per the risk appetite, it may be tolerable without further mitigation. If it exceeds risk appetite, additional measures should be considered. Changing the risk assessment method is not a direct response to residual risk management. Acceptance should only occur if the risk is within tolerance levels【5:230, 5:231†CRISC_SentenceinNOTE30.pptx】.
An organization is concerned that a change in its market situation may impact the current level of acceptable risk for senior management. As a result, which of the following is MOST important to reevaluate?
Options:
Risk classification
Risk policy
Risk strategy
Risk appetite
Answer:
BExplanation:
Risk Appetite:
Risk appetite is the amount and type of risk that an organization is willing to take in order to meet its objectives. It reflects the organization’s risk tolerance and guides decision-making at all levels.
Impact of Market Changes:
A change in the market situation can alter the risk landscape, potentially affecting the organization’s ability to achieve its objectives. This might necessitate a reassessment of what level of risk is acceptable.
Senior management needs to ensure that the risk appetite remains aligned with the new market conditions and organizational goals.
Reevaluation Process:
Reevaluating the risk appetite involves assessing the organization ' s capacity to bear risk and determining if the current acceptable risk levels are still appropriate.
This might involve more conservative or aggressive risk-taking strategies based on the new market dynamics.
Other Considerations:
Risk Classification:This categorizes risks but does not directly address changes in acceptable risk levels.
Risk Policy:While important, the policy outlines the approach to managing risk and is influenced by the risk appetite.
Risk Strategy:This defines how risks are managed but should be aligned with the risk appetite.
References:
The CRISC Review Manual emphasizes the importance of aligning risk appetite with the organization’s strategic objectives and market conditions (CRISC Review Manual, Chapter 1: Governance, Section 1.10 Risk Appetite, Tolerance, and Capacity) .
A vendor ' s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
Options:
IT infrastructure manager
Chief Risk Officer (CRO)
Business continuity manager
Business application owner
Answer:
DExplanation:
The business application owner is responsible for the operation and risk decisions related to the application. Since the loss of failover may impact business continuity, their approval is essential.
Which of the following is the BEST key control indicator (KCI) for a vulnerability management program?
Options:
Percentage of high-risk vulnerabilities missed
Number of high-risk vulnerabilities outstanding
Defined thresholds for high-risk vulnerabilities
Percentage of high-risk vulnerabilities addressed
Answer:
DExplanation:
A key control indicator (KCI) is a metric that measures the effectiveness of a control in mitigating a risk. A good KCI for a vulnerability management program should reflect how well the program is reducing the exposure to high-risk vulnerabilities. The percentage of high-risk vulnerabilities addressed is a KCI that shows the proportion of identified high-risk vulnerabilities that have been remediated or mitigated within a defined time frame. This KCI can help monitor the progress and performance of the vulnerability management program and identify areas for improvement.
The other options are not the best KCI for a vulnerability management program because they do not measure the effectiveness of the control. The percentage of high-risk vulnerabilities missed is a measure of the completeness of the vulnerability scanning process, not the control. The number of high-risk vulnerabilities outstanding is a measure of the current risk exposure, not the control. The defined thresholds for high-risk vulnerabilities are a measure of the risk appetite, not the control. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 3: IT Risk Assessment, Section 3.4: Risk Indicators, p. 133-134.
Which of the following approaches would BEST help to identify relevant risk scenarios?
Options:
Engage line management in risk assessment workshops.
Escalate the situation to risk leadership.
Engage internal audit for risk assessment workshops.
Review system and process documentation.
Answer:
AExplanation:
The best approach to identify relevant risk scenarios is to engage line management in risk assessment workshops. Risk scenarios are hypothetical situations that describe how a risk event could occur and what the consequences could be1. Identifying risk scenarios can help to understand and communicate the nature and impact of the risks, and to design and evaluate the risk responses2. To identify relevant risk scenarios, it is important to involve the people who are responsible for or affected by the risks, such as the line managers. Line managers are the managers who oversee the operational activities and processes of the organization, and whoreport to the senior or executive management3. By engaging line managers in risk assessment workshops, the organization can:
Leverage the line managers’ knowledge and experience of the operational environment, the business objectives, the stakeholder expectations, and the potential threats and opportunities4.
Encourage the line managers’ participation and collaboration in the risk identification and analysis process, and foster a risk-aware culture and mindset5.
Enhance the line managers’ ownership and accountability of the risks and the risk responses, and ensure their alignment and commitment to the risk management strategy and objectives6.
The other options are not the best approaches to identify relevant risk scenarios, because:
Escalating the situation to risk leadership is not an effective or efficient way to identify risk scenarios, as it may bypass or undermine the line managers’ role and responsibility in the risk management process. Risk leadership is the function or role that provides the vision, direction, andguidance for the risk management activities and initiatives of the organization7. Escalating the situation to risk leadership may imply that the line managers are not capable or willing to identify and manage the risks, or that the risk leadership is not aware or involved in the riskmanagement process. This may create confusion, conflict, or distrust among the risk management stakeholders, and reduce the quality and credibility of the risk scenarios.
Engaging internal audit for risk assessment workshops is not a suitable or appropriate way to identify risk scenarios, as it may violate the independence and objectivity of the internal audit function. Internal audit is an independent and objective assurance and consulting activity that evaluates and improves the effectiveness of the organization’s governance, risk management, and control processes8. Engaging internal audit for risk assessment workshops may compromise the internal audit’s role and mandate, as it may create a conflict of interest or a self-review threat. Internal auditshould not be involved in the risk identification and analysis process, but rather provide assurance or advice on the adequacy and reliability of the process.
Reviewing system and process documentation is not a sufficient or comprehensive way to identify risk scenarios, as it may overlook or miss some important or emerging risks. System and process documentation are the records or artifacts that describe the structure, functions, features, and requirements of the organization’s systems and processes. Reviewing system and process documentation can help to identify some risks that are related to the design, implementation, or operation of the systems and processes, but it cannot capture all the risks that may affect the organization. Some risks may arise from external or internal factors that are not reflected or updated in the system and process documentation, such as changes in the market, technology, regulation, or stakeholder expectations.
References =
Risk Scenarios Toolkit - ISACA
Risk Scenarios Starter Pack - ISACA
Line Manager - CIO Wiki
Engaging Line Managers in Risk Management - IRM
Risk Culture - CIO Wiki
Risk Ownership - CIO Wiki
Risk Leadership - CIO Wiki
Internal Audit - CIO Wiki
[System Documentation - CIO Wiki]
Which of the following is MOST important to review when an organization needs to transition the majority of its employees to remote work during a crisis?
Options:
Customer notification plans
Capacity management
Access management
Impacts on IT project delivery
Answer:
BExplanation:
Capacity management is crucial when transitioning employees to remote work during a crisis. It involves ensuring that the IT infrastructure can handle increased loads and that resources are available to support remote operations effectively.
Which of the following approaches to bring your own device (BYOD) service delivery provides the BEST protection from data loss?
Options:
Enable data wipe capabilities
Penetration testing and session timeouts
Implement remote monitoring
Enforce strong passwords and data encryption
Answer:
DExplanation:
The best approach to bring your own device (BYOD) service delivery that provides the best protection from data loss is to enforce strong passwords and data encryption. BYOD is a service delivery model that allows the users to use their own personal devices, such as smartphones, tablets, or laptops, to access the enterprise’s network, applications, or data. BYOD can provide various benefits, such as increased productivity, flexibility, and satisfaction of the users, as well as reduced costs and maintenance of the enterprise. However, BYOD also poses various risks, such as data loss, data breach, malware infection, or unauthorized access, as the personal devices may not have the same level of security and control as the enterprise-owned devices. Enforcing strong passwords and data encryption is the best approach to protect the data on the personal devices, as it helps to prevent or limit the unauthorized access, disclosure, or theft of the data, especially if the devices are lost, stolen, or compromised. Enforcing strong passwords and data encryption also helps to comply with the legal and regulatory requirements for data protection and privacy. Enabling data wipe capabilities, penetration testing and session timeouts, and implementing remote monitoring are also useful approaches, but they are not as effective as enforcing strong passwords and data encryption, as they are either reactive or detective measures, rather than proactive or preventive measures. References = CRISC Review Manual, 6th Edition, ISACA, 2015, page 217.
Which of the following is the MOST common concern associated with outsourcing to a service provider?
Options:
Lack of technical expertise
Combining incompatible duties
Unauthorized data usage
Denial of service attacks
Answer:
CExplanation:
The most common concern associated with outsourcing to a service provider is unauthorized data usage, which means the misuse, disclosure, or theft of the organization’s data by the service provider or its employees, contractors, or subcontractors1. Unauthorized data usage can pose significant risks to the organization, such as:
Data security and privacy breaches, which can compromise the confidentiality, integrity, and availability of the data, and expose the organization to legal liability, regulatory penalties, reputational damage, or loss of trust and credibility2.
Data quality and accuracy issues, which can affect the reliability and validity of the data, and impair the decision-making, reporting, or performance of the organization3.
Data ownership and control issues, which can limit the access and rights of the organization to its own data, and create dependency or lock-in with the service provider4.
The other options are not the most common concern associated with outsourcing to a service provider, because:
Lack of technical expertise is a potential but not prevalent concern associated with outsourcing to a service provider, as it may affect the quality and efficiency of the services provided by the service provider, and the compatibility and integration of the services with the organization’s systems and processes5. However, most service providers have sufficient technical expertise in their domain or field, and they can offer specialized skills or resources that the organization may not have internally6.
Combining incompatible duties is a possible but not frequent concern associated with outsourcing to a service provider, as it may create conflicts of interest or segregation of duties issues for the service provider or the organization, and increase the risk of errors, fraud, or abuse7. However, most service providers have adequate governance and control mechanisms to prevent or mitigate such issues, and they can adhere to the organization’s policies and standards regarding the separation of duties8.
Denial of service attacks is a rare but not common concern associated with outsourcing to a service provider, as it may disrupt the availability or functionality of the services provided by the service provider, and affect the operations or continuity of the organization. However, most service providers have robust security measures and contingency plans to protect and recover from such attacks, and they can ensure the resilience and reliability of the services.
References =
Unauthorized Data Usage - CIO Wiki
What is outsourcing? Definitions, benefits, challenges, processes, advice | CIO
The Pros and Cons of Outsourcing in 2023 - GrowthForce
13 Common Problems of Outsourcing and How to Avoid Them - ENOU Labs
The Top 10 Problems with Outsourcing Implementation - SSON
10 problems with outsourcing (+ Solutions for each) - Time Doctor Blog
Segregation of Duties - CIO Wiki
Outsourcing Governance - CIO Wiki
[Denial-of-Service Attack - CIO Wiki]
[Business Continuity Planning - CIO Wiki]
A PRIMARY advantage of involving business management in evaluating and managing risk is that management:
Options:
better understands the system architecture.
is more objective than risk management.
can balance technical and business risk.
can make better-informed business decisions.
Answer:
DExplanation:
Involving business management in evaluating and managing risk is beneficial, as it enables management to have a comprehensive and holistic view of the risk environment and its impact on the organization’s objectives and strategy. By participating in the risk management process, management can make better-informed business decisions, as they can consider the risk factors and implications of their choices, and align their decisions with the organization’s risk appetite and tolerance. Involving business management in evaluating and managing risk can also enhance the risk culture and governance of the organization, and foster a proactive and collaborative approach to risk management. References = Most Asked CRISC Exam Questions and Answers. CRISC: Certified in Risk & Information Systems Control Sample Questions, Question 253. ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, Question 253. CRISC by Isaca Actual Free Exam Q & As, Question 9.
When reviewing a report on the performance of control processes, it is MOST important to verify whether the:
Options:
business process objectives have been met.
control adheres to regulatory standards.
residual risk objectives have been achieved.
control process is designed effectively.
Answer:
CExplanation:
When reviewing a report on the performance of control processes, it is most important to verify whether the residual risk objectives have been achieved, as this indicates the extent to which the control processes have reduced the risk to an acceptable level. Residual risk is the risk that remains after the implementation of controls, and it should be aligned with the risk appetite and tolerance of the enterprise. Business process objectives, regulatory standards, and control process design are not the most important factors to verify,as they do not directly measure the effectiveness and efficiency of the control processes in managing the risk. References = CRISCPractice Quiz and Exam Prep; CRISC: Certified in Risk & Information Systems Control Sample Questions, question 209.
An organization is implementing Internet of Things (IoT) technology to control temperature and lighting in its headquarters. Which of the following should be of GREATEST concern?
Options:
Insufficient network isolation
Lack of interoperability between sensors
Insecure data transmission protocols
Impact on network performance
Answer:
AExplanation:
IoT devices often lack strong built-in security, and CRISC stresses that the most serious risk isinsufficient network isolation, because it exposes the entire enterprise network. If IoT devices are placed on the same network as business systems, an attacker who compromises an IoT device can move laterally to critical assets. This significantly increases the risk of a major security incident. Insecure transmission protocols are a concern but can be mitigated with encryption layers. Sensor interoperability and performance issues are operational problems but do not pose major security threats. Proper segmentation, isolation, and VLAN separation are the most critical controls for IoT risk reduction.
When reviewing the business continuity plan (BCP) of an online sales order system, a risk practitioner notices that the recovery time objective (RTO) has a shorter lime than what is defined in the disaster recovery plan (DRP). Which of the following is the BEST way for the risk practitioner to address this concern?
Options:
Adopt the RTO defined in the BCR
Update the risk register to reflect the discrepancy.
Adopt the RTO defined in the DRP.
Communicate the discrepancy to the DR manager for follow-up.
Answer:
DExplanation:
A recovery time objective (RTO) is the maximum acceptable time that a business process or function can be disrupted or unavailable before it causes significant damage or loss to the organization. A business continuity plan (BCP) is a document that describes how the organization will resume its critical business operations in the event of a disaster or disruption. A disaster recovery plan (DRP) is a document that describes how the organization will restore its IT systems and infrastructure in the event of a disaster or disruption. The RTO defined in the BCP and the DRP should be consistent and aligned, as they both support the continuity and recovery of the business. If the RTO defined in the BCP is shorter than the RTO defined in the DRP, it means that the BCP expects the business process or function to be restored faster than the DRP can provide. This can create a gap or a conflict between the BCP and the DRP, and can compromise the effectiveness and efficiency of the continuity and recovery efforts. Therefore, the best way for the risk practitioner to address this concern is to communicate the discrepancy to the DR manager for follow-up, meaning that the risk practitioner should report the issue and its implications to the DR manager, who is responsible for developing and maintaining the DRP. The DR manager should review the discrepancy and determine whether it is justified or not, and whether it requires any adjustment or alignment of the RTOs in the BCP and the DRP. References = Risk and Information Systems Control Study Manual, Chapter 4, Section 4.4.2, p. 206-207
The BEST criteria when selecting a risk response is the:
Options:
capability to implement the response
importance of IT risk within the enterprise
effectiveness of risk response options
alignment of response to industry standards
Answer:
CExplanation:
The effectiveness of risk response options is the best criteria when selecting a risk response, because it reflects the degree to which the response can reduce the impact or likelihood of the risk, or enhance the benefit or opportunity of the risk. The effectiveness of risk response options can be evaluated by considering factors such as cost, feasibility, timeliness, and alignment with the organization’s objectives and risk appetite. The other options are not as good as the effectiveness of risk response options, because they do not measure the outcome or value of the response, but rather focus on the input or process of the response, as explained below:
A. Capability to implement the response is a criteria that considers the availability and adequacy of the resources, skills, and knowledge required to execute the response. While this is an important factor to consider, it does not indicate how well the response can address the risk or achieve the desired result.
B. Importance of IT risk within the enterprise is a criteria that considers the significance and priority of the risk in relation to the organization’s strategy, objectives, and operations. Whilethis is an important factor to consider, it does not indicate how well the response can address the risk or achieve the desired result.
D. Alignment of response to industry standards is a criteria that considers the compliance and conformity of the response with the best practices, norms, and expectations of the industry or sector. While this is an important factor to consider, it does not indicate how well the response can address the risk or achieve the desired result. References = Risk and Information Systems Control Study Manual, Chapter 2, Section 2.2.2, page 40. How to Select Your Risk Responses -Rebel’s Guide to Project Management, Risk Response Plan in Project Management: Key Strategies & Tips, Risk Responses - options for managing risk - Stakeholdermap.com
Key risk indicators (KRIs) BEST support risk treatment when they:
Options:
Set performance expectations for controls.
Align with key business objectives.
Indicate that the risk is approaching predefined thresholds.
Articulate likelihood and impact in quantitative terms.
Answer:
CExplanation:
KRIs are most effective when they signal that a risk is nearing or exceeding predefined thresholds. This early warning enables organizations to take proactive measures to mitigate risks before they materialize into significant issues.
A risk practitioner is performing a risk assessment of recent external advancements in quantum computing. Which of the following would pose the GREATEST concern for the risk practitioner?
Options:
The organization has incorporated blockchain technology in its operations.
The organization has not reviewed its encryption standards.
The organization has implemented heuristics on its network firewall.
The organization has not adopted Infrastructure as a Service (laaS) for its operations.
Answer:
BA risk practitioner is reporting on an increasing trend of ransomware attacks in the industry. Which of the following information is MOST important to include to enable an informed response decision by key stakeholders?
Options:
Methods of attack progression
Losses incurred by industry peers
Most recent antivirus scan reports
Potential impact of events
Answer:
DExplanation:
The potential impact of events is the estimated magnitude and likelihood of the consequences that may result from a risk scenario. The potential impact of events can help key stakeholders understand the severity and urgency of the risk, and prioritize the appropriate response actions. The potential impact of events can be expressed in quantitative or qualitative terms, such as financial loss, operational disruption, reputational damage, legal liability, etc. The potential impact of events is the most important information to include when reporting on an increasing trend of ransomware attacks in the industry, as it can help stakeholders assess the level of risk exposure and the adequacy of the existing controls. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Assessment, Section 2.3: Risk Analysis, p. 87-89.
What is the GREATEST concern with maintaining decentralized risk registers instead of a consolidated risk register?
Options:
Aggregated risk may exceed the enterprise ' s risk appetite and tolerance.
Duplicate resources may be used to manage risk registers.
Standardization of risk management practices may be difficult to enforce.
Risk analysis may be inconsistent due to non-uniform impact and likelihood scales.
Answer:
AExplanation:
A risk register is a tool that records and tracks the identified risks, their causes, impacts, likelihood, responses, and owners. A decentralized risk register is maintained by each business unit or function, while a consolidated risk register is maintained at the enterprise level. The greatest concern with maintainingdecentralized risk registers instead of a consolidated risk register is that the aggregated risk may exceed the enterprise’s risk appetite and tolerance. Risk appetite is the amount and type of risk that an enterprise is willing to accept in pursuit of its objectives, while risk tolerance is the acceptable level of variation around the objectives. If the risk registers are not consolidated, the enterprise may not have a holistic view of its risk profile and may not be able to prioritize and allocate resources effectively. The other options are also concerns, but they are not as significant as the potential misalignment between the aggregated risk and the enterprise’s risk appetite and tolerance. References = Risk and Information Systems Control Study Manual, 7th Edition, Chapter 1, Section 1.2.2.2, pp. 21-22.
Which of the following is the MOST important consideration when sharing risk management updates with executive management?
Options:
Using an aggregated view of organizational risk
Ensuring relevance to organizational goals
Relying on key risk indicator (KRI) data Including
Trend analysis of risk metrics
Answer:
BExplanation:
According to the CRISC Review Manual (Digital Version), the most important consideration when sharing risk management updates with executive management is ensuring relevance toorganizational goals, as this helps to align risk management with business strategy and performance. The risk management updates should:
Highlight the key risks that may affect the achievement of the organizational goals and objectives
Demonstrate the value and benefits of risk management in supporting decision making and enhancing business resilience
Provide clear and concise information on the current risk profile, risk appetite, risk tolerance and risk exposure of the organization
Recommend appropriate risk response actions and resource allocation to address the identified risks
Communicate the roles and responsibilities of executive management in overseeing and governing risk management
References = CRISC Review Manual (Digital Version), Chapter 4: IT Risk Monitoring and Reporting, Section 4.2: IT Risk Reporting, pp. 221-2221
Which of the following is the PRIMARY reason for conducting peer reviews of risk analysis?
Options:
To enhance compliance with standards
To minimize subjectivity of assessments
To increase consensus among peers
To provide assessments for benchmarking
Answer:
BExplanation:
According to the CRISC Review Manual1, peer reviews are the process of evaluating the quality and validity of risk analysis by independent experts or colleagues. Peer reviews are conducted to ensure that the risk analysis is consistent, objective, and reliable, and that it follows the established standards and methods. The primary reason for conducting peer reviews of risk analysis is to minimize subjectivity of assessments, as peer reviews can help to reduce personal biases, preferences, and assumptions that may affect the risk analysis outcomes. Peer reviews can also help to identify and correct any errors, gaps, or inconsistencies in the risk analysis, and to improve the risk analysis skills and knowledge of the reviewers and the reviewees. References = CRISC Review Manual1, page 209.
A recent risk workshop has identified risk owners and responses for newly identified risk scenarios. Which of the following should be the risk practitioner ' s NEXT step?
Options:
Develop a mechanism for monitoring residual risk.
Update the risk register with the results.
Prepare a business case for the response options.
Identify resources for implementing responses.
Answer:
BExplanation:
The next step for the risk practitioner after identifying risk owners and responses for newly identified risk scenarios is to update the risk register with the results. The risk register is a document that records the details of the risks, such as their sources, causes, consequences, likelihood, impact, and responses. By updating the risk register with the results of the risk workshop, the risk practitioner can ensure that the risk information is current, accurate, and complete, and that the risk owners and responses are clearly defined and communicated. Developing a mechanism for monitoring residual risk, preparing a business case for the response options, and identifying resources for implementing responses are possible steps that may follow the updating of the risk register, but they are not the next step. References = ISACA Certified in Risk and Information Systems Control (CRISC) Certification Exam Question and Answers, question 11; CRISC Review Manual, 6th Edition, page 144.
When an organization is having new software implemented under contract, which of the following is key to controlling escalating costs?
Options:
Risk management
Change management
Problem management
Quality management
Answer:
BExplanation:
The key to controlling escalating costs when an organization is having new software implemented under contract is change management, which is the process of identifying, evaluating, approving, and implementing changes to the project scope, schedule, budget, or quality1. Change management can help to control escalating costs by:
Establishing a clear and agreed-upon baseline for the project deliverables, requirements, and expectations, and ensuring that they are aligned with the contract terms and conditions2.
Defining and enforcing a formal and consistent change control process, which includes the roles and responsibilities, the criteria and methods, and the documentation and communication of the changes3.
Assessing and prioritizing the proposed changes, and determining their impact and feasibility, and their alignment with the project objectives and constraints4.
Obtaining the approval and authorization of the relevant stakeholders, such as the project sponsor, the project manager, the contractor, or the customer, before implementing the changes5.
Monitoring and measuring the performance and outcome of the changes, and ensuring that they are delivered within the agreed scope, schedule, budget, and quality6.
References =
Change Management - CIO Wiki
Project Scope Management - CIO Wiki
Change Control - CIO Wiki
Change Impact Analysis - CIO Wiki
Change Approval - CIO Wiki
Change Evaluation - CIO Wiki
Which of the following is the PRIMARY consideration when determining the impact to an organization after the discovery of malware on an endpoint device?
Options:
Asset criticality and sensitivity
Currency of anti-malware signatures
Availability of patches and security updates
Currency of the incident response plan
Answer:
AExplanation:
The correct answer isAbecause when malware is discovered on an endpoint device, the first consideration in determiningimpactis thecriticality and sensitivity of the affected asset. The business importance of the device, the data it stores or accesses, and the role it plays in operations determine how serious the incident is to the organization.
The other options are less important for determining impact:
B. Currency of anti-malware signaturesrelates to control effectiveness, not the primary measure of business impact.
C. Availability of patches and security updatesis relevant to remediation, but not the main factor in assessing impact.
D. Currency of the incident response planaffects preparedness, not the actual impact of the malware event.
Exact Extracts supporting the answer:
“IT risk is measured by its impact on business operations.”
“The primary reason risk professionals conduct risk assessments is to identify risk with the highest business impact.”
“The main outcome of a business impact analysis (BIA) is the criticality of business processes.”
“To determine the level of protection required for securing personally identifiable information a risk practitioner should PRIMARILY consider the sensitivity property of the information.”
“The criticality of an IT infrastructure element can be quantified based on dependencies.”
These extracts show that impact assessment is driven primarily by business criticality and information sensitivity. Therefore,asset criticality and sensitivityis the primary consideration.
===========
Which of the following is the BEST indication that an organization ' s IT asset life cycle is poorly managed?
Options:
Increased hardware maintenance costs
Sensitive data found on discarded devices
Lack of asset labeling
Inadequate employee training
Answer:
BExplanation:
The correct answer isBbecause findingsensitive data on discarded devicesis the clearest indication that the IT asset life cycle is poorly managed. This points to failure in end-of-life handling, media sanitization, disposal controls, ownership accountability, and policy enforcement. It is a direct indicator of life cycle control breakdown with significant security and compliance consequences.
The other options are less conclusive:
A. Increased hardware maintenance costsmay indicate inefficiency, but not necessarily poor life cycle control.
C. Lack of asset labelingis a weakness, but less severe and less direct than improper disposal of sensitive data.
D. Inadequate employee trainingmay contribute to problems, but it is not the strongest indicator by itself.
Exact Extracts supporting the answer:
“When data are no longer needed by a particular process they should be handled according to policy.”
“Information that is no longer required to support the main purpose of the enterprise from an information security perspective should be managed under the retention policy.”
“The data security control that BEST protects the confidentiality of data stored on backup media in transit to a third-party storage facility is encryption.”
“The BEST safeguard against a data breach is security awareness training.”
These extracts support that assets and the data on them must be handled according to policy throughout the life cycle, especially when no longer needed. Sensitive data remaining on discarded devices is therefore the strongest indication of poor asset life cycle management.
===========
All business units within an organization have the same risk response plan for creating local disaster recovery plans. In an effort to achieve cost effectiveness, the BEST course of action would be to:
Options:
select a provider to standardize the disaster recovery plans.
outsource disaster recovery to an external provider.
centralize the risk response function at the enterprise level.
evaluate opportunities to combine disaster recovery plans.
Answer:
DExplanation:
Disaster recovery plans are essential for ensuring the continuity and resilience of business operations in the event of a disruption or disaster. However, creating and maintaining separatedisaster recovery plans for each business unit may not be cost-effective or efficient, as it may result in duplication, inconsistency, or gaps in the plans. Therefore, the best course of action would be to evaluate opportunities to combine disaster recovery plans across the business units, where possible and appropriate. This would help to achieve economies of scale, standardization, and alignment of the plans, as well as reduce complexity and costs. However, this does not mean that all disaster recovery plans should be identical or centralized, as different business units may have different risk profiles, recovery objectives, and requirements. Therefore, the combined disaster recovery plans should still be tailored and customized to suit the specific needs and characteristics of each business unit. References = ISACA CRISC Review Manual, 7th Edition, Chapter 2, Section 2.3.2, page 71.
Which of the following is the PRIMARY reason for an organization to include an acceptable use banner when users log in?
Options:
To reduce the likelihood of insider threat
To eliminate the possibility of insider threat
To enable rapid discovery of insider threat
To reduce the impact of insider threat
Answer:
AExplanation:
The primary reason for an organization to include an acceptable use banner when users log in is to reduce the likelihood of insider threat, as it informs the users of the policies, rules, andexpectations for the use of the organization’s IT resources, and deters them from engaging in unauthorized or malicious activities. The other options are not the primary reasons, as they are more related to the detection, prevention, or mitigation of insider threat, respectively, rather than the reduction of the likelihood of insider threat. References = CRISC Review Manual, 7th Edition, page 155.
Which of the following is the BEST approach for performing a business impact analysis (BIA) of a supply-chain management application?
Options:
Reviewing the organization ' s policies and procedures
Interviewing groups of key stakeholders
Circulating questionnaires to key internal stakeholders
Accepting IT personnel s view of business issues
Answer:
BExplanation:
The best approach for performing a business impact analysis (BIA) of a supply-chain management application is to interview groups of key stakeholders, as this allows the risk practitioner to obtain direct and detailed information on the business processes, dependencies, resources, and requirements that are supported by the application. The risk practitioner can also clarify any doubts, address any concerns, and validate any assumptions during the interviews. The BIA is a process of identifying and analyzing the potential effects of disruptive events on the critical business functions and objectives. The BIA helps to determine the recovery priorities, strategies, and targets for the business continuity plan. The other options are not the bestapproaches for performing a BIA, although they may be useful or complementary methods. Reviewing the organization’s policies and procedures can provide some background and context for the BIA, but it may not reflect the current or accurate situation of the business processes and the application. Circulating questionnaires to key internal stakeholders can be a convenient and efficient way to collect some data for the BIA, but it may not capture the complexity and nuances of the business processes and the application. Accepting IT personnel’s view of business issues can be biased and incomplete, as they may not have the full understanding or perspective of the business needs and expectations. References = Risk and Information Systems Control Study Manual, Chapter 2: IT Risk Identification, page 58.
Which of the following is the PRIMARY reason for a risk practitioner to report changes and trends in the IT risk profile to senior management?
Options:
To ensure risk owners understand their responsibilities
To ensure IT risk is managed within acceptable limits
To ensure the organization complies with legal requirements
To ensure the IT risk awareness program is effective
Answer:
BExplanation:
The primary reason for a risk practitioner to report changes and trends in the IT risk profile to senior management is to ensure that IT risk is managed within acceptable limits, because it helps to inform and advise the senior management on the current state and direction of IT risk, and to support the risk-based decision making and prioritization. An IT risk profile is a summary of the key IT risks that an organization faces, and their implications for the organization’s objectives and strategy. An IT risk profile may change or evolve over time, due to factors such as newtechnologies, business initiatives, or external events. Reporting changes and trends in the IT risk profile to senior management is the primary reason, as it helps to ensure that the senior management is aware of and prepared for the IT risk challenges and opportunities, and that the IT risk is managed within the acceptable limits defined by the organization’s risk appetite and tolerance. To ensure risk owners understand their responsibilities, to ensure the organization complies with legal requirements, and to ensure the IT risk awareness program is effective are all possible reasons for reporting changes and trends in the IT risk profile, but they are not the primary reason, as they are not directly related to the management of IT risk within acceptable limits. References = Risk and Information Systems Control Study Manual, Chapter 3, Section 3.2.3, page 91

